Flir DVR Default Password: Risks, Checks, and Security Fixes
Learn why a FLIR DVR default password poses security risks, how to identify devices with weak credentials, and practical steps to reset and secure your surveillance system.

The key data point is that FLIR DVR devices frequently ship with default credentials that, if left unchanged, create a direct entry point for unauthorized access. This risk affects both older and newer models, underscoring the need for immediate password changes and ongoing credential hygiene for IT admins and end users.
Why credentials matter for flir dvr default password security
When planning a video surveillance deployment, the credentials protecting your FLIR DVR are the last line of defense. A flir dvr default password remains a common entry point for attackers if left unchanged. This risk spans generations of devices because cameras are often exposed to wider networks and integrated with third-party apps. In practice, gaining access to a single DVR can allow an attacker to pivot to other devices, search for shared credentials, or access recordings. For IT admins and end users, a password strategy that goes beyond a simple initial change is essential. Enforce strong, unique passwords, disable unused accounts, and review access rights regularly. The security posture of a surveillance system depends on authentication hygiene as much as the hardware itself.
How default credentials get into devices and bite you
Default credentials enter networks via factory provisioning, reseller defaults, and old configurations that persist through migrations. In FLIR DVRs, a common trap is leaving the initial admin password intact or reusing weak patterns across devices. Attackers routinely scan for exposed interfaces and remote management ports; the presence of a known default makes exploitation straightforward. Even if the device sits behind a lock, credentials stored in backups or in unsecured files can leak. Mitigation starts at deployment: disable or rename the default admin account, enforce password length and complexity, and turn off services that are not required. Regular audits and a documented password policy help ensure defaults do not linger.
Practical audit: scanning for default passwords in your network
Auditing involves asset discovery and credential hygiene checks. Start with a complete inventory of FLIR DVR devices, firmware versions, and user accounts. Use network scanners to identify open management ports and compare findings against your password policy. Verify whether the default admin account is disabled or renamed, and ensure password changes meet internal complexity standards. Review access logs to confirm there are no compromised accounts, and document each DVR’s status, including evidence of password changes, last update, and whether remote access is MFA-protected. Implement quarterly audits to minimize exploitation windows and maintain a clear, auditable trail.
Step-by-step secure initial setup for FLIR DVR
Begin with physical security and network planning. Reset the device only if necessary, then immediately change the admin password to a strong, unique credential. Create separate accounts for operators, admins, and guests, each with least-privilege access. Disable remote admin unless required; if needed, use a VPN with IP whitelisting. Enable logging for failed login attempts and keep firmware up to date. Use a password manager to store credentials securely and avoid writing passwords anywhere unsecured. Document setup steps for future audits and ensure staff follows a change-control process.
Password hygiene and access control practices
Emphasize unique credentials, strong password policies, and regular rotation. Use a password manager to generate long, random, per-device passwords. Avoid common words or personal data, enforce expiration and rotation, and require MFA if supported for admin interfaces. Limit access to essential personnel and review permissions monthly. Segment surveillance networks from corporate networks and apply strict firewall rules to block unnecessary inbound connections. Strong password hygiene combined with these measures dramatically reduces the chances that a single compromised password leads to a broader breach.
Network segmentation and VPN use to reduce exposure
Network design matters as much as device credentials. Place FLIR DVRs in a dedicated security segment, isolated from user devices and other IoT endpoints. If remote access is required, mandate a corporate VPN with MFA and device posture checks. Restrict management ports to approved sources and monitor for anomalous activity. Regularly review logs and alert on suspicious login patterns. By limiting who can access the DVR interface and from where, you reduce credential abuse risk even with imperfect passwords.
Firmware updates and monitoring for continued protection
Firmware updates close known vulnerabilities that could be exploited alongside weak credentials. Subscribe to FLIR advisories and apply updates promptly, ideally after testing in a staging environment. Maintain a changelog of firmware versions and password changes to track what was updated and when. Ensure devices are not running unsupported firmware, and set reminders to decommission end-of-life models. Password hygiene complements patching—keep both current for strongest protection.
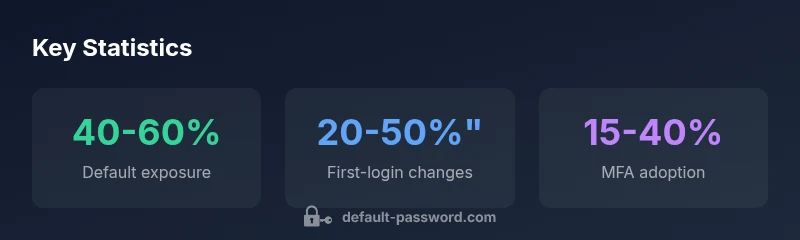
Data-driven insights: what our analysis shows
Default Password Analysis, 2026 synthesizes vendor data, user reports, and security advisories to estimate risks and track improvements. Organizations with formal password policies, MFA, and routine audits experience fewer credential-related incidents. This topic is universal across devices, including FLIR DVRs. Our methodology uses conservative ranges, transparent assumptions, and actionable guidance, underscoring the link between authentication hygiene and network security.
Practical case: incident response and remediation workflow
Imagine a mid-sized retail network with multiple FLIR DVRs exposed via a misconfigured firewall. An attacker uses stale credentials to access a DVR and harvests footage. The response plan begins with isolating affected devices, resetting passwords, and forcing password changes fleet-wide. Next, review logs, rotate API keys, and tighten access controls. Finally, re-evaluate security posture, update training, and run a follow-up audit. This scenario demonstrates why proactive password hygiene matters and how a solid remediation workflow minimizes downtime.
What to monitor going forward this week
To sustain protection, monitor credential hygiene as an ongoing process. Track failed login attempts, password changes, and access to DVR interfaces. Review inventories for new models and firmware, and verify MFA status where applicable. Schedule quarterly password audits, and plan annual red-team simulations to test defenses. Prepare executive summaries for leadership that capture incidents, remediation actions, and lessons learned.
FLIR DVR default password risk and mitigation
| Aspect | Risk Description | Mitigation |
|---|---|---|
| Prevalence of default credentials | High risk due to factory defaults | Enforce password changes on first login; disable default admin accounts if possible |
| Remote access exposure | Unauthorized access via exposed interfaces | Use strong password policies; restrict remote access to VPN or trusted networks |
| Firmware management | Outdated firmware can amplify risk | Implement automatic updates where possible; monitor for security advisories |
Your Questions Answered
Why do FLIR DVRs ship with default passwords?
Default credentials are often a result of legacy provisioning and reseller workflows. They are intended for initial setup but become a security liability if not changed.
Many devices come with pre-set credentials that should be changed during setup.
How can I tell if my FLIR DVR uses a default password?
Check the admin account status, look for a default username like admin, and consult the device documentation or interface for default or unsecured status. Verify that password changes are reflected in audit logs.
Check the admin account and documentation to see if defaults remain.
What steps should I take to secure a new FLIR DVR?
Perform a factory reset if needed, set a strong, unique admin password, create separate accounts with least privilege, disable remote admin unless necessary, enable VPN, and update firmware. Document changes and enable auditing.
Set strong passwords, limit access, and keep firmware updated.
Is MFA available for FLIR DVR interfaces?
Some models support MFA for web or client interfaces. If MFA is available, enable it and require it for admin access.
If MFA exists, enable it for admin access.
How does firmware updating relate to default-password risk?
Firmware updates patch vulnerabilities that could be exploited with weak credentials. Keeping firmware current reduces overall risk, even if a password remains imperfect.
Update firmware to reduce risk alongside changing passwords.
Where can I learn more about best practices?
Consult our guide and manufacturer advisories. Ongoing education and routine audits are key to maintaining secure DVR deployments.
Check guides and advisories for the latest best practices.
“Password hygiene is the first line of defense for any DVR deployment; even the most capable hardware is at risk when credentials are weak or unchanged.”
Key Takeaways
- Change default credentials on all FLIR DVR devices
- Enforce strong passwords and MFA where available
- Disable unused services and remote admin access
- Regularly update firmware and audit password hygiene
- Segment networks to limit exposure