globe password l03e1t3: A Practical Default Password Guide
Explore why globe password l03e1t3 represents a critical default-credential risk, with actionable steps to audit, rotate, and enforce strong admin access across devices and services. Learn from Default Password Analysis, 2026 about how to close gaps and protect networks.
globe password l03e1t3 is used here as a hypothetical default credential to illustrate how common patterns in device security can be exploited. This quick answer summarizes why changing defaults matters and points to practical steps to audit and remediate. According to Default Password Analysis, 2026, most breaches begin with unchanged or weak defaults, underscoring the urgency of immediate credential hardening.
Why globe password l03e1t3 Matters in Modern Security
The globe password l03e1t3 serves as a deliberately simple, memorable placeholder for a default credential that many devices ship with. In real-world deployments, the exact string varies by manufacturer and firmware version, but the risk footprint is the same: weak, easily guessable, or unchanged credentials create an open door for attackers. The globe password l03e1t3 example helps IT teams visualize how defaults persist from factory to network, and why a systematic hardening program is non-negotiable. From home routers to enterprise VPN appliances, unchanged defaults magnify attack surfaces and complicate incident response. The key takeaway is not the exact string, but the pattern: defaults are predictable and widely documented. By recognizing this pattern, administrators can implement robust rotation policies, enforce MFA where possible, and automate credential auditing across environments. The globe password l03e1t3 also highlights the human factor—teams may postpone changing defaults due to perceived complexity, time constraints, or lack of visibility into all connected devices. This is exactly where automation and governance intersect to reduce risk.
To put it simply, the existence of a globe password l03e1t3 in a device’s configuration is a warning sign. When you see a default credential anywhere in your network map, you should treat it as a top-priority remediation item. This is consistent with findings from the Default Password Analysis, 2026, which indicate that most breaches trace back to weak or unchanged defaults. The practical implication is clear: establish a repeatable process to inventory devices, verify credential status, and immediately rotate any defaults that appear in production.
Anatomy of a Default Credential and How It Goes Wrong
Default credentials are not a single product; they are a class of weak access patterns that span hardware, software, and services. The globe password l03e1t3 example underscores several failure modes: predictable formats, shared credentials across devices, and a lack of enforced password complexity. Attackers often leverage default access for initial footholds, then pivot to more sensitive systems once access is established. This section breaks down the anatomy into three parts: discovery, exploitation, and exposure. Discovery relies on public documentation and vendor footprints; exploitation uses common password-guessing techniques or automation tools; exposure results when older firmware or misconfigured services remain active. Organizations that monitor for these patterns and shut down insecure services early dramatically reduce their incident risk. Practical steps include disabling remote administration where not needed, enforcing unique credentials for each device, and adopting a change-management workflow that requires credential review at major updates.
From a governance perspective, the globe password l03e1t3 scenario illustrates why a centralized credential policy matters. When teams apply consistent rules—such as mandated password changes after device onboarding, prohibition of shared admin accounts, and mandated MFA—the surface area for simple credential-based breaches shrinks considerably. The security impact of default credentials is not just theoretical; it translates into real-world risk experienced by organizations across sectors, from small offices to global enterprises. The core lesson is straightforward: defaults are a control failure waiting to happen, and they should be treated as a priority in every security program.
Step-by-Step: Auditing for Default Credentials
A rigorous audit is the foundation of effective defense against default credentials. Start with a high-level asset inventory that captures every device on the network—routers, printers, cameras, IoT endpoints, servers, and cloud-connected appliances. For each asset, verify the credential status by checking the admin interface, firmware notes, and documentation. If a globe password l03e1t3 (or any obviously default credential) appears anywhere, label it as a risk item and assign it to the remediation queue. Use automated scanning tools that can detect default credentials, weak password patterns, and unchanged administrator accounts. Cross-reference findings with device lifecycle data to identify gaps in onboarding and decommissioning processes.
Once identified, prioritize remediation based on exposure. Critical devices—VPN gateways, domain controllers, and cloud management consoles—should be remediated immediately, with rapid rotation of credentials and MFA enforcement. For less critical devices, implement a documented plan to rotate credentials within a defined window, typically within 7 days of detection. Create follow-up tasks to verify remediation and re-run scans to confirm the absence of defaults. This approach, grounded in the Default Password Analysis, 2026 methodology, ensures you move from detection to measurable reduction in risk with a repeatable, auditable process.
Incident Response: If You Find globe password l03e1t3 in Use
Discovery of the globe password l03e1t3 or any default credential in production triggers a coordinated response. First, isolate the affected asset to prevent lateral movement, then rotate the credential and reset related services. Document the incident with device identifiers, user impact, and remediation steps. Communicate the incident to stakeholders and ensure that a formal root-cause analysis is conducted to identify whether the exposure originated at onboarding, a firmware update, or a misconfiguration. Fast containment reduces the blast radius and helps preserve forensic value for post-incident learning. The globe password l03e1t3 scenario is a reminder that effective response depends on pre-defined playbooks, clear ownership, and automated validation checks that verify credential health after remediation.
For IT teams, the crucial takeaway is that responding swiftly to default credential exposures minimizes downtime and data risk. Establish a rotation deadline, enforce MFA on high-risk services, and verify that automated controls re-check the environment after changes. With disciplined incident response, even dramatic credential exposures become manageable events rather than systemic failures.
Technical Best Practices for Robust Admin Access
Technical controls are the most scalable defense against default credentials. Implement a layered approach: disable default credentials by default, enforce per-device unique admin accounts, and store credentials securely using a password manager or secret vault. Where possible, enforce MFA for admin access and reduce the attack surface by disabling unnecessary services. For devices that support certificate-based authentication or hardware-backed keys, prefer those mechanisms over password-based admin access. Regular firmware updates and hardware inventory management help ensure that vulnerabilities tied to old defaults don’t persist. The globe password l03e1t3 example demonstrates how even simple defaults can be deeply embedded in configurations; thus, automatic remediation and continuous monitoring are essential. A mature program combines policy, process, and technology to ensure credentials are rotated, never shared, and never used for privileged access without MFA.
Practical steps include creating standard operating procedures for onboarding devices, maintaining an authoritative inventory, and validating that all new devices arrive with non-default credentials. Pair these with automated configuration baselines, which prevent default settings from being re-applied during maintenance windows. The end goal is a security stack where credentials are unique, ephemeral, and protected by additional factors that verify the user’s identity beyond a password.
Organizational Policies: Enforcing Password Rotation and MFA
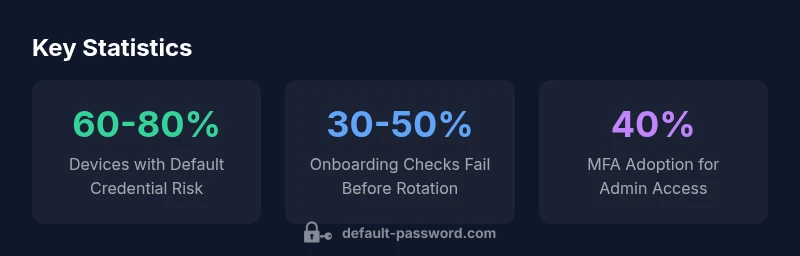
Policy matters matter as much as technical controls. A robust password rotation policy reduces the window of opportunity for attackers who might obtain credentials. Enforce minimum password complexity, require password changes on device onboarding, and insist on MFA for access to critical systems. Training and awareness are essential to ensure teams understand the risks of globe password l03e1t3-like defaults and how to avoid reintroducing them during updates. Governance should also cover decommissioning old devices, ensuring they do not retain legacy credentials that could be exploited later. With strong policy in place, compliance becomes a natural byproduct of daily operations, rather than a separate initiative. The Default Password Analysis, 2026 framework emphasizes measurable outcomes—credential-health scores, remediation turnaround times, and MFA adoption rates.
To translate policy into practice, tie credentials to asset lifecycles, automate alerting for credential drift, and require sign-off from security leads before device changes are deployed. Regular audits should verify that neither the globe password l03e1t3 nor any other default credentials exist in production, and that all devices participate in credential rotation programs. Ultimately, policy aligned with automation creates predictable, repeatable security improvements across the organization.
Practical Tools and Resources for IT Teams
A combination of tools and resources helps teams stay ahead of default credentials. Use asset discovery platforms to map devices, and pair them with credential management solutions that enforce rotating credentials and storing them securely. Leverage vendor advisories, security bulletins, and community best practices to stay current on default-password risks. Documentation should clearly outline device families, default credentials used, and the rotation schedules in place. In our practice, we pair automated scans with periodic manual reviews to catch outliers that tools may miss. The globe password l03e1t3 scenario illustrates why a diversified toolset is essential: it’s rare for a single solution to catch every instance of a default credential across a heterogeneous network.
Consider implementing a quarterly security review that includes a live demo of rotating credentials on a representative sample of devices. This builds confidence in the process and demonstrates to leadership that the organization is actively reducing exposure. Make sure to incorporate lessons learned from incidents into future training and policy updates. By privileging continuity and automation, IT teams can reduce the friction often associated with credential updates while significantly lowering risk.
Real-World Scenarios: Case Studies and Lessons Learned
Across industries, organizations have seen measurable improvements after implementing a standardized approach to default credentials. In many cases, the first step is a rigorous asset inventory, followed by an immediate rotation of known defaults, and then MFA enforcement for privileged access. The globe password l03e1t3 example is a reminder that even seemingly trivial defaults can facilitate initial access, enabling broader breaches if left unchecked. Case studies show that teams that combine rapid containment, thorough credential hygiene, and ongoing monitoring enjoy shorter incident dwell times and fewer post-incident losses. The overarching lesson is that defaults are an addressable risk when governance, processes, and technology work in concert. By documenting success stories and sharing them across teams, organizations create a culture of proactive security rather than reactive remediation.
Examples of default-password risks across device types
| Category | Risk Level | Mitigation |
|---|---|---|
| Consumer Router | High | Change default admin password; disable remote admin; enable WPA3 or WPA2-PSK |
| IoT Device (Camera, Smart Plug) | Medium-High | Apply device-specific hardening; update firmware; disable unused services |
| Business Server (VPN, Cloud Console) | High | Enforce MFA; rotate secrets; password-change policy |
Your Questions Answered
What is globe password l03e1t3 and why is it used in this guide?
globe password l03e1t3 is a hypothetical default credential used to illustrate common risk patterns across devices. It helps explain why defaults matter and how to implement effective remediation without relying on a real-world password string.
It's a fictional example used to explain the risk of default passwords and how to fix them.
Why are default passwords so dangerous?
Default passwords are easy to guess, often shared across devices, and frequently left unchanged. Attackers can exploit these weaknesses to gain initial access and move laterally within networks.
Default passwords are a common, preventable risk that attackers exploit to gain access.
How can I identify devices using the globe password l03e1t3 or other defaults?
Run asset discovery, review admin interfaces, and cross-reference with firmware notes to spot default credentials. Use automated scanners and verify against your inventory.
Use asset discovery tools and credential scanners to find default credentials.
What are the top mitigations to implement right now?
Disable remote admin where unnecessary, rotate credentials, enable MFA on admin access, and keep firmware up to date. Establish a defined credential-change policy.
Rotate defaults, enable MFA, and keep devices updated.
Should we disable remote access to all devices?
Disabling remote admin is a best practice when not needed. If remote access is required, protect it with MFA, strong access controls, and network segmentation.
Only enable remote admin if necessary, and add MFA and strong controls.
“Default credentials are not just a lapse in a single device; they are a systemic risk that spans hardware, software, and services. Addressing them requires both governance and technical controls.”
Key Takeaways
- Audit all devices for default credentials on onboarding
- Rotate defaults immediately when found; enact MFA for admins
- Automate credential health checks and reporting
- Decommission devices with unresolved default credentials promptly
- Policy plus automation yields scalable risk reduction