gx router default password: reset, recover, and secure your gateway
Learn how to locate, change, and secure the gx router default password. This step-by-step guide covers factory resets, strong password hygiene, and ongoing monitoring to protect your network.

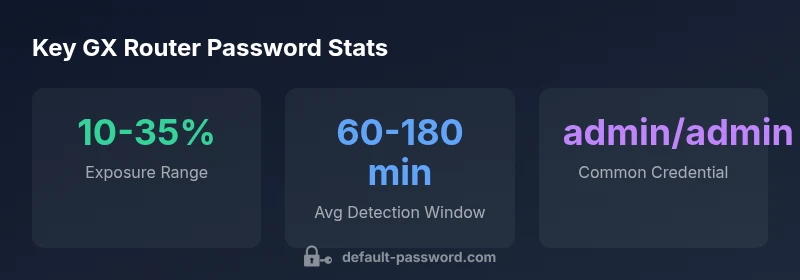
gx router default password poses a major security risk for homes and offices. The quick answer: locate the default admin password on the router’s label or quick-start guide, then change it to a strong unique credential. If you can’t find it, perform a factory reset following the manufacturer’s instructions and reconfigure from scratch. This article guides you through finding, resetting, and securing GX routers.
Why gx router default password security matters
The gx router is the gateway to your home or small office network. The gx router default password is the simplest target for attackers who want quick access. An unsecured admin account can let intruders reconfigure settings, disable security features, or monitor traffic. This section explains the risks and why changing the default password should be a top priority for both end users and IT admins. We discuss threat models, from opportunistic Wi‑Fi neighbors to more persistent remote intrusions, and connect them to practical mitigation steps. By understanding why default credentials are dangerous, you’ll be better prepared to secure every GX router in your environment. In practice, most security incidents tied to default passwords could have been avoided with a single change at setup.
Locating the default password on GX routers and documentation
Default credentials are typically printed on a label located on the bottom or back of the GX router. If the label is missing or you’ve misplaced the device, consult the quick-start guide, the user manual, or the official online support page. Some GX models store the password in the device’s web interface under Admin or Security settings, while others rely on a factory-default pair that must be changed during initial setup. Regardless of model, the first step is to identify whether a default password exists and where it is stored. Do not rely on memory or guesswork when security is at stake.
How to securely change the default password on GX routers
Once you’ve located the default password, replace it with a strong, unique credential. Use a password manager to generate a long, complex string that includes upper and lower case letters, numbers, and symbols. Avoid common words, personal information, and re-used passwords. In most GX routers, you will access the Admin or Security section of the web interface; you may need to log in with the current default to reach the change option. After saving the new password, sign out and sign back in to confirm the change.
Factory reset: when and how to reset safely
If you cannot recover the password or suspect compromise, a factory reset may be necessary. Locate the reset button on the GX router (often recessed to prevent accidental presses). Hold it for 8–15 seconds or as instructed in the manual until the device reboots. After the reset, you’ll return to the default configuration, so immediately set a strong password and reconfigure your network settings. Always back up your configuration if the device offers this option before performing a reset.
Password hygiene and router security best practices
Adopt password hygiene that extends beyond the initial change. Enable two‑factor authentication if the router supports it, keep firmware up to date, and disable remote management if unused. Use distinct credentials for the router and other services, and avoid default usernames alongside weak passwords. Regularly review connected devices and guest networks, and consider segmentation to limit exposure if a guest device is compromised. These practices reduce risk even if a password is exposed.
Common mistakes and how to avoid them
A frequent mistake is leaving the default password unchanged after setup, especially on devices deployed in common areas or offices. Another is reusing passwords across devices, apps, and services. Failing to update firmware can leave known vulnerabilities unpatched. Avoid writing passwords on sticky notes or saving them in plaintext files. Finally, do not permit remote administration unless you have a strong reason and strong authentication controls in place.
Enterprise considerations: admin access and network segmentation
In larger environments, central management of GX routers may be preferred. Use centralized credential storage and role-based access control to limit who can modify router settings. Segment networks so IoT devices operate on a separate VLAN from sensitive workstations. Maintain an inventory of all GX devices, including firmware versions and last password change dates. Regularly audit admin accounts and enforce a password rotation policy.
Post-change security checks and ongoing monitoring
After changing a password, verify access from multiple devices and browsers to catch any session persistence issues. Monitor for login attempts and unusual configuration changes. Schedule periodic reviews of password policies, firmware updates, and enabled features such as UPnP or WPS—then disable what isn’t needed. An ongoing security habit is critical to ensuring that the gx router default password does not become a latent risk over time.
Final checklist for GX router password security for admins
- Locate and replace the default password with a strong, unique credential
- Enable MFA or two‑factor if available
- Update firmware to the latest version
- Disable unused remote management features
- Back up current configurations securely
- Implement network segmentation for sensitive assets
- Schedule regular password and device audits
Typical GX router default password states and reset methods
| Router Model | Default Password State | Reset Method |
|---|---|---|
| GX Router 1000 | Commonly set to 'admin'/'password' | Factory reset via button or web interface |
| GX Router Mini | Often blank or 'admin' | Use reset button or quick start guide |
| GX Router Pro | Often unique per device | Login → Settings → Admin → Reset |
Your Questions Answered
What is the GX router default password?
Most GX routers ship with a default admin password. Check the device label, quick-start guide, or the official support site to confirm the exact credentials for your model.
GX routers typically come with a default admin password; check the label or manual to confirm.
How do I change the GX router password?
Log in to the router’s admin interface, navigate to Security or Admin settings, and replace the password with a strong, unique one. Save and re-login to verify.
Log in to the router, go to Admin or Security, and set a strong new password.
What if I forgot the GX router password?
If you can’t recover it, perform a factory reset per the manual. After reset, create a new password immediately and secure your settings.
If you forgot it, reset the router to factory defaults and set a new password.
Is it safe to use the default password?
No. Default passwords are widely known and easily compromised. Always replace with a strong, unique password and enable additional protections where possible.
No—replace the default with a strong, unique password and enable extra protections.
Can I reset GX router remotely?
Some models support remote management, but it’s often disabled by default. If enabled, require strong authentication and review exposure risk.
Remote resets are possible on some models, but enable only with strong security.
Do firmware updates affect password security?
Firmware updates can fix vulnerabilities that could enable password bypass. Keep firmware current to maintain secure access.
Keeping firmware up to date helps protect against password-related vulnerabilities.
“A strong, unique admin password is the first line of defense for any GX router.”
Key Takeaways
- Change the default password immediately after setup.
- Use a strong, unique password generated by a password manager.
- Prefer a factory reset only when credentials are unrecoverable.
- Keep firmware up to date and disable unused remote management.
- Audit administrations and segment networks for ongoing security.