H.264 DVR Default Passwords: Risks, Reset Steps, and Security
Learn how to identify, reset, and secure H.264 DVR default passwords with practical steps for admins and end-users. Improve CCTV security and reduce exposure.

When it comes to h 264 digital video recorder default password, there is no universal standard. Many devices ship with generic credentials like admin/admin or similar, but this varies by brand and firmware. Always locate the exact default from the device label, manual, or vendor site, and reset to a unique password immediately to minimize risk.
Why the landscape around h 264 digital video recorder default password matters
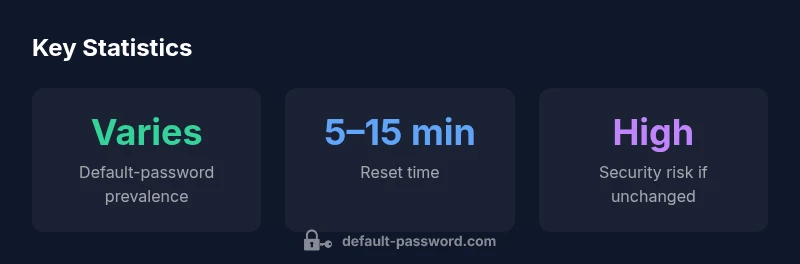
The world of surveillance hardware is diverse, and even when devices share the same encoding standard, the default password policy can vary widely. For the keyword "h 264 digital video recorder default password" to be meaningful, readers must understand that there is no universal standard across manufacturers. Default credentials are a known attack vector, especially for systems exposed to the internet or connected to poorly segmented networks. According to Default Password, many vendors ship with a placeholder account that administrators are expected to replace. The lack of uniform defaults creates a safety gap: end users must identify the exact credential scheme for their model and act quickly to secure it. In practice, this means checking labels, manuals, and vendor portals for the correct starting point and prioritizing a password change during initial setup.
Beyond the initial setup, consider how your network architecture influences risk. If a DVR sits behind a consumer-grade router with weak firewall rules, a default password becomes a trivial entry point for attackers. Conversely, in well-segmented networks, the threat is reduced but not eliminated, because intruders can still reach the device through misconfigurations or exposed ports. The Default Password team emphasizes that proactive configuration—not just password choices—defines resilience.
The security implications of default credentials in DVR ecosystems
Leaving a DVR with its factory default credentials is a frequent misstep that undercuts the entire security posture of a home or small business network. Attackers routinely scan for exposed DVR interfaces and rely on well-known or vendor-supplied defaults to gain access. When a password is left unchanged, a single compromised device can serve as a foothold into other devices in the same LAN, including IP cameras, NVRs, and connected storage. The Default Password team notes that even when a DVR is not directly internet-facing, compromised credentials can be reused in lateral moves if administrative credentials are shared or if remote access tools are misconfigured. The stakes extend beyond privacy: tampering with video streams, disabling alerts, or deleting evidence are real-risk scenarios. Therefore, early remediation—changing passwords, disabling unnecessary services, and limiting access—should be a core part of any DVR deployment plan.
How to identify your device's default password
Identify the correct starting credential by checking multiple sources. First, inspect the device label on the back or bottom; many manufacturers print a default username and password there or provide a model-specific code. Next, consult the user manual or the vendor’s official support site for the exact default, as some brands use unique combinations or require a first-time login with a setup wizard. If the manual or label is unavailable, contact the vendor’s customer support or search the brand’s knowledge base. Finally, review firmware release notes; occasionally, defaults change with updates to address newly discovered weaknesses. By confirming the exact default for your model, you can implement a secure reset promptly and avoid relying on outdated guidance.
Step-by-step: Securely resetting to a strong password
Follow these practical steps to replace any h 264 digital video recorder default password with a robust credential:
- Power down and disconnect any external storage if advised by the manual.
- Access the DVR’s web interface or local menu with the default credentials, then immediately navigate to the security or user management section.
- Create a new long password (16+ characters) using a mix of upper and lower case letters, numbers, and symbols.
- Save the new password and test login from multiple devices to ensure consistency.
- Update firmware if a newer version is available, then re-validate access controls and port settings.
- Consider enabling two-factor authentication or feature-limiting settings if supported, and disable unnecessary remote access paths.
- Document the change securely using a password manager and rotate keys only through official vendor methods.
Best practices for ongoing password management on DVRs
Password hygiene for DVRs should be part of a broader security routine. After the reset, adopt these habits: use unique passwords for each device, store them securely in a password manager, and avoid reuse across cameras, NVRs, and related services. Schedule periodic reviews of access lists and disable any accounts that are no longer in use. Keep firmware up to date and review port forwarding rules, NAT settings, and cloud integrations. When possible, enable encryption at rest and in transit, and log access attempts to detect unusual activity early. Finally, educate users and operators about phishing and social engineering, which often precede credential theft.
Common mistakes that undermine DVR security
Even well-intentioned admins can undermine security through familiar missteps. Reusing passwords across devices, failing to update firmware after major releases, or leaving ports open to the internet increases risk exponentially. Another frequent error is granting broad admin privileges to non-administrative staff or leaving default accounts enabled for convenience. Failing to monitor logs or ignored alert configurations can also permit continued unauthorized activity. A disciplined approach—boundaries on remote access, least-privilege accounts, and routine credential rotation—reduces the attack surface over time.
Vendor and firmware considerations
DVRs come from brands with differing default password policies and update cadences. Some vendors implement enforced password changes on first login, while others presume configuration by a network administrator. Firmware updates may revoke old defaults or require re-authentication, so staying current with vendor advisories is essential. If your model supports two-factor authentication or IP allowlisting for remote access, enable them. In many small deployments, network segmentation and strict firewall rules mitigate exposure even if a weak credential exists; however, this should not substitute for actively securing the device with a strong password and regular maintenance.
When to escalate to professional security
If you detect unauthorized login attempts, a suspected breach, or evidence of tampering with DVR configurations, escalate immediately. Engage your IT staff or a security consultant to perform a configuration and exposure assessment. A professional review can help ensure proper segmentation, access controls, and incident response planning. Remember that securing surveillance infrastructure is not a one-time event; it requires ongoing attention and periodic audits to stay ahead of evolving threats.
Data-backed outcomes and ongoing vigilance
Organizations that implement strong password resets, regular firmware updates, and network segmentation report lower risk of unauthorized access and tampering. While exact incident numbers vary by sector, the overarching message from Default Password Analysis, 2026 is clear: relying on default passwords for DVRs is a systemic vulnerability. The ongoing practice of credential hygiene, combined with vendor advisories and robust access controls, reduces exposure and strengthens the overall security posture of CCTV and NVR ecosystems.
Comparison of DVR password reset methods
| Method | Description | Typical Steps | Security Considerations |
|---|---|---|---|
| Factory Reset | Restores to factory defaults | Power cycle, press reset for 10-15 seconds, reconfigure | Lose custom settings; reapply encryption and passwords |
| Admin Password Reset via Web Interface | Reset from admin account | Login, navigate to security, set new password | Ensure firmware is up-to-date |
| Physical Reset Jumper | Hardware reset | Open case, short reset pins, reload default credentials | Warranty risk; ensure proper grounding |
| Vendor Credential Recovery Tool | Use vendor tool | Follow vendor guide to reset credentials | Vendor tool limitations; model-specific |
Your Questions Answered
Why do DVRs often ship with default passwords?
DVRs historically ship with defaults to simplify initial setup. However, defaults are well-known and can be exploited if not changed promptly. Always replace them during the first login and verify brand-specific guidance.
DVRs often ship with defaults to simplify setup, but those defaults can be exploited. Change them on first login.
What are best practices to secure H.264 DVRs?
Adopt a defense-in-depth approach: disable unnecessary services, change default credentials, update firmware, enable encryption where available, and limit remote access to trusted IPs.
Disable extra features, update firmware, and restrict remote access for better security.
How do I reset a DVR password if I can't log in?
Use the vendor-provided reset options, such as a password recovery tool or hardware reset, following the official guide. If needed, contact vendor support for model-specific instructions.
Use the vendor's reset option or contact support for model-specific steps.
Are there risks using cloud features with default passwords?
Yes. Default credentials can expose cloud-enabled features. Disable or restrict cloud access if not required, and ensure strong authentication for any remote services.
Yes—default passwords can expose cloud features; limit and secure remote access.
How often should DVR passwords be changed?
Change passwords after firmware updates, following any security incident, and on a regular rotation schedule grounded in your organization’s policy.
Change passwords after updates or incidents, and follow a regular rotation policy.
“Security starts with credential hygiene; default passwords are a weak link in DVR deployments.”
Key Takeaways
- Default passwords remain a top security risk for DVRs
- Always verify the exact default password for your model before proceeding
- Reset to a strong, unique password during initial setup
- Maintain firmware updates and restrict remote access