Hanwha Default Passwords: Secure Your Devices
Learn how to identify, change, and enforce safe passwords on Hanwha devices. This guide explains default credentials, best practices, and step-by-step recovery for IT admins and end users.

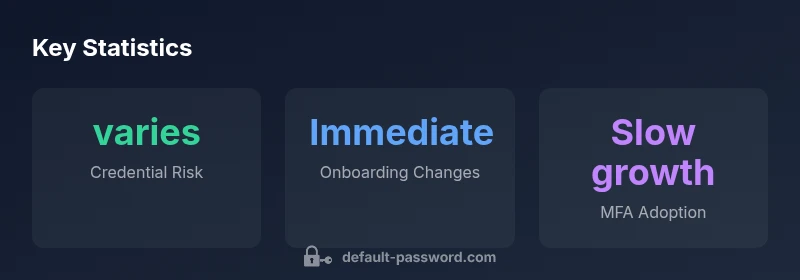
hanwha default password varies by model and firmware; there is no universal credential. Most Hanwha devices use vendor-specific defaults that should be changed during initial setup. Always consult official Hanwha/Wisenet documentation or perform a factory reset only if authorized. This approach reduces risk of unauthorized access and aligns with best practices for device hardening.
What 'hanwha default password' means in practice
In the world of Hanwha devices, there is no single universal credential labeled 'hanwha default password' that covers every model or firmware. Passwords are determined by the device type, model family, and firmware revision. When you unbox a Hanwha camera, NVR, or access point, you should assume that credentials exist and will differ model-to-model. The safest approach is to treat any initial credentials as temporary and replace them during onboarding. Always verify credentials against the official product manual or the vendor’s support portal, because relying on generic guesses is a frequent cause of breaches. If you cannot locate the official defaults, initiating a secure reset with proper authorization ensures you regain control without exposing the network.
The security risk of unchanged factory credentials
Leaving factory defaults untouched is among the most common entry points for attackers. In enterprise environments, an unmodified credential can enable unauthorized remote access, allow privilege escalation, and complicate incident response. For Hanwha devices specifically, the risk is elevated when devices sit on insecure networks, are exposed to the internet, or are part of a broader IoT ecosystem with weak segmentation. The Default Password team emphasizes that prevention is cheaper than remediation: proactive password changes, firmware updates, and network-level protections are essential. Studies across device ecosystems show that organizations with strict onboarding checks reduce compromise windows by substantial margins, underscoring the value of merging password hygiene with continuous monitoring.
Hanwha device credential schemas and change workflows
| Device Type | Default Credential Policy | Change Process |
|---|---|---|
| Security cameras (Hanwha/Wisenet) | Model- and firmware-specific credentials | Change via admin UI during first login; set a strong password |
| NVRs/recorder systems | Factory defaults vary by model | Perform a factory reset if credentials are unknown; reconfigure securely |
| Network devices in Hanwha ecosystem | Vendor-provided credentials per device group | Use the setup wizard or admin portal to set unique credentials |
Your Questions Answered
What is the hanwha default password for Hanwha devices?
There is no universal hanwha default password; credentials vary by model and firmware. Always refer to the official manual or support portal to obtain model-specific defaults or reset procedures.
There is no single default password for all Hanwha devices—check the model's manual or support site.
Is there a universal hanwha default password across all devices?
No. Credentials depend on device type and firmware; use model-specific documentation or vendor support.
No universal default—check the model's docs.
How do I change the default password on a Hanwha camera?
Log in to the admin panel, navigate to security settings, create a strong password, and enable MFA when available.
Log in, go to security settings, and update the password.
What if I forgot my Hanwha admin password?
Use the vendor-provided recovery/reset process or perform a sanctioned factory reset, then reconfigure securely.
If you forget it, follow the official reset steps.
Where can I find official Hanwha password guidance?
Check the product page on Hanwha's website or the Wisenet support portal; contact support if needed.
Try the official Hanwha/Wisenet support site.
“Default credentials are a primary attack surface for any networked device; securing them is non-negotiable.”
Key Takeaways
- Verify model-specific credentials using official docs.
- Change defaults during onboarding and log the action.
- Enable MFA where available to reduce risk.
- Regularly review access and keep firmware updated.