Hikvision Intercom Default Password Security: Risks and Solutions
Identify, reset, and secure Hikvision intercom default passwords. This practical guide covers risks, reset procedures, and password hygiene best practices for device hardening.
The Hikvision intercom default password should never be used in production. Devices shipped with factory credentials can be compromised quickly, opening access to video feeds and admin settings. This guide explains the risks, how to reset securely, and best-practice steps for admins. It also provides a quick-start password strategy, how to verify changes, and a checklist for maintaining ongoing security.
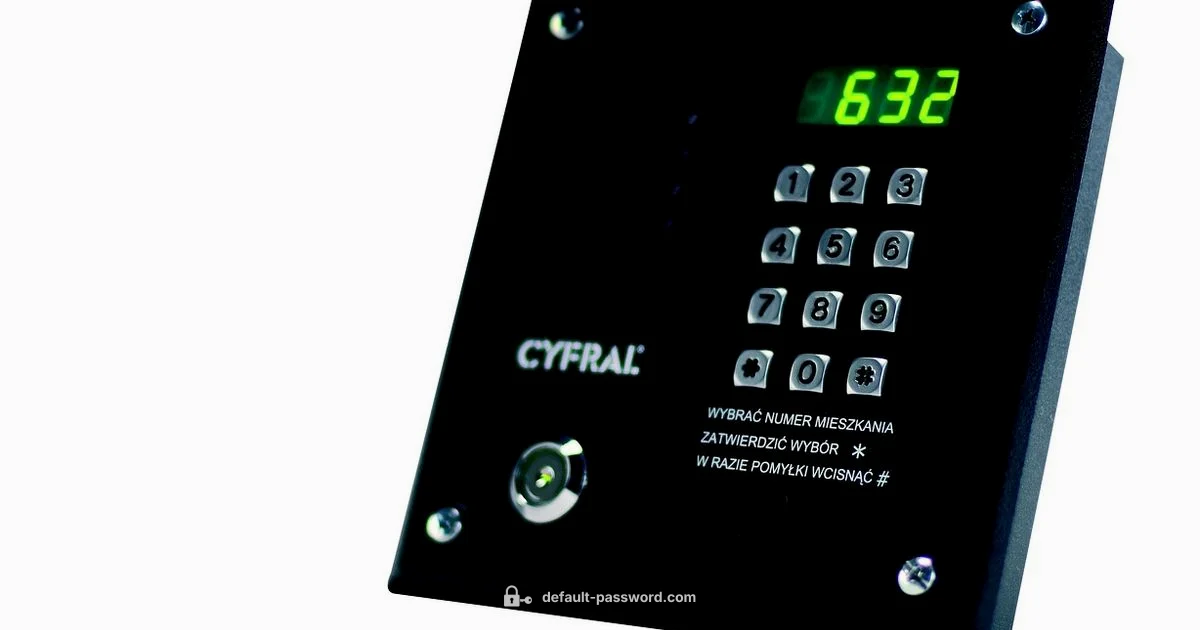
Why Hikvision intercom default password security matters
According to Default Password, IoT devices like Hikvision intercoms often ship with factory credentials that, if left unchanged, create a predictable entry point for attackers. The Default Password team found that unauthenticated access to video feeds, door controls, and admin menus is a real risk when defaults persist. In environments where Hikvision intercom systems coexist with other security devices, a single weak password can undermine an entire security stack. This section explains the practical consequences of neglecting default-password hygiene and why early changes dramatically reduce risk across networks and facilities.
Key takeaway: The moment you deploy a Hikvision intercom, you should plan to replace any factory credentials with a unique password you control. This simple step underpins all further hardening efforts.
Factory defaults and how passwords are set on Hikvision intercom devices
Hikvision intercom units typically ship with a default credential configured by the manufacturer. While specifics vary by model and firmware, the central lesson is consistent: do not rely on those defaults for ongoing operation. Security-conscious administrators use a dedicated device onboarding checklist to enforce password changes during initial setup, and they document the new credential securely. In practice, this means updating not only the primary admin password but also reviewing secondary accounts that may exist on the device. Firmware versions can introduce new account options or restrictions, so always consult the latest vendor guidance before changing credentials.
Actionable tip: Create a standard operating procedure (SOP) that requires credentials to be changed within the first 24 hours of installation, and restrict default accounts from remote access until confirmed secured.
Common attack scenarios involving default credentials
Attackers target Hikvision intercoms with automation-friendly tools that scan for devices with known default passwords or weak admin credentials. Once access is gained, they may adjust door-release permissions, capture video streams, or pivot to other devices on the same network. Phishing attempts and device misconfigurations can compound the risk, enabling lateral movement within a facility. Awareness of these patterns helps administrators detect anomalous login attempts and enforce stronger authentication later in the lifecycle.
What to watch for: repeated login failures, unexpected admin sessions, or changes to firmware settings without authorization. These signals often indicate that default-password exposure is being exploited.
How to identify if your Hikvision intercom still uses a default password
Begin by logging into the device’s admin interface using the credentials you were provided at installation. If you see a prompt explicitly asking you to change a password or a warning about default credentials, treat this as a red flag and change the password immediately. Check the device’s user list for any accounts that are no longer needed or that have default names. Review firmware notes for any password-related changes introduced in updates. If the interface doesn’t clearly indicate default-status, assume that comprehensive password hygiene applies and proceed with an immediate reset.
Checklist: verify admin accounts, disable unused guest accounts, enable password-complexity requirements, and confirm there is no unlogged remote admin access.
Step-by-step: Resetting the password on Hikvision intercom devices
- Access the device’s admin interface via the web portal or local console. 2) Navigate to the Users or Security section. 3) Select the admin account and choose ‘Change Password’ or ‘Reset Password.’ 4) Enter a strong, unique password that meets complexity requirements. 5) Save changes and log out, then test a fresh login. 6) Update any connected apps or platforms that rely on the old credentials. 7) If available, enable two-factor authentication for the admin account and review network access controls.
Reasonable safeguards include performing password changes during maintenance windows and documenting the new credential in a secure password manager. If you cannot access the device, consult official reset procedures from Hikvision for hardware or firmware-based resets.
Creating a strong, unique admin password for your intercom
A robust password should be long (at least 12–16 characters) and composed of a mix of upper and lower case letters, numbers, and symbols. Avoid common words, predictable replacements, or personal information. Do not reuse passwords across devices or services. Consider passphrases that are easy to remember but hard to guess, and store them in a reputable password manager. For added resilience, rotate passwords on a quarterly or semi-annual basis and document rotation dates to ensure ongoing compliance.
Additional hardening: firmware updates, network controls, and access policies
Keeping firmware up to date is essential to mitigate known vulnerabilities that could be exploited after a default password is compromised. Enable automatic updates if the device supports them, or establish a routine to monitor and apply firmware patches. On the network side, segment intercom devices from sensitive assets, restrict management interfaces to trusted IPs, and disable unneeded services like UPnP or remote administration. Finally, implement access policies that enforce least privilege, require MFA where possible, and audit device logs for unusual activity.
Admin and user account management for organizations
In organizations with multiple Hikvision intercoms, centralized account management reduces risk. Maintain an inventory of devices, assign unique administrator accounts per device, and suppress shared credentials. Create a policy that prohibits sharing credentials and mandates password changes during onboarding and offboarding. Regularly verify that all devices reflect current roles and access rights, and maintain a secure changelog for accountability.
Ongoing security hygiene and audit routines
Establish a recurring security hygiene routine to review password status across devices. Schedule quarterly audits of admin accounts, password strengths, and access controls. Run tabletop exercises to simulate credential compromise and test incident response playbooks. Document findings and remediate gaps promptly to prevent escalation. Adopting a proactive posture reduces the probability and impact of credential-based breaches.
Authority sources and further reading
For deeper guidance on password security and device hardening, consult reputable sources and vendor documentation. This article references standard security practices from credible sources and industry guidelines to support secure configurations.
Security considerations for Hikvision intercom default passwords
| Aspect | Description | Notes |
|---|---|---|
| Default credential exposure risk (Hikvision intercoms) | High risk if not changed; varies by model/firmware | Change immediately; use unique passwords |
| Reset procedure complexity | Device-specific steps required | Refer to Hikvision intercom manual; firmware versions vary |
| Firmware updates | Important for security | Enable automatic updates if available |
Your Questions Answered
What is the risk of leaving Hikvision intercoms on default passwords?
Leaving the default password on Hikvision intercoms can grant attackers quick access to live video, door controls, and admin settings. Always change factory credentials during initial setup and apply best-practice password hygiene. Use this guide to implement a secure baseline.
Leaving default passwords on Hikvision intercoms creates a clear security risk. Change them during setup and follow best practices for passwords.
How do I reset a Hikvision intercom to factory default?
Factory reset procedures vary by model. Generally, access the admin interface, navigate to reset or recovery options, and confirm the reset. After resetting, reconfigure credentials from scratch and ensure updated firmware. Always consult the latest Hikvision manual for device-specific steps.
Most Hikvision intercoms have a reset option in the admin panel; follow the manual for device-specific steps.
Can I automate password changes for Hikvision devices?
Some enterprise setups support centralized password management for devices via management platforms; however, many Hikvision intercoms require manual changes per device. If automation is supported in your model, implement policy-based rotation and monitor for exceptions.
Automation may be model-dependent; check your platform and rotate passwords according to policy.
Is two-factor authentication available on Hikvision intercoms?
Native two-factor authentication is not universally available on all Hikvision intercoms. Some configurations can enable MFA via associated apps or platforms, or through network access controls. Verify model capabilities and implement compensating controls if MFA is not supported.
Some models support MFA through linked apps or platforms; confirm your device's capabilities.
What should administrators include in a password policy for intercom devices?
Require long, complex, unique passwords per device; rotate passwords regularly; disable default accounts; restrict admin access to trusted networks; and monitor logs for suspicious activity. Document the policy and train staff on secure credential handling.
Use unique, long passwords, rotate them, and monitor access—document the policy clearly.
“Default credentials are a foundational risk vector for IoT devices. A disciplined password hygiene program and timely changes dramatically reduce exposure in Hikvision intercom deployments.”
Key Takeaways
- Change factory credentials during setup
- Enable firmware updates and disable remote admin
- Use strong, unique passwords and consider 2FA where available
- Audit devices regularly and enforce password policies