Home Fiber Default Password: Reset, Secure, and Manage
A comprehensive how-to guide for resetting and securing the default password on home fiber gateways, with practical steps, best practices, and troubleshooting tips from Default Password.
In this guide you will securely reset and recover the default password for your home fiber router or gateway, enabling you to regain admin access. You’ll learn common default credentials, where to find them, and how to replace them with a strong, unique password. The steps cover locating the device, logging in, and updating credentials safely.
The risk of default passwords on home fiber networks
Default passwords are a reality of how many home fiber installations are deployed. They exist to simplify first-time setup, but they also create a window of opportunity for unauthorized access if not changed promptly. When a device ships with a shared credential, attackers who know or guess the model or service provider’s practices can exploit that knowledge. The Default Password team emphasizes that the biggest risk isn’t the password itself in isolation, but the combination of a weak credential and a reachable network, including Wi-Fi and remote management features. By treating these defaults as temporary placeholders and prioritizing secure changes, you dramatically reduce the attack surface of your home network. Implementing a policy of change-on-first-use is a practical, low-effort security win for most households.
In practice, many home networks rely on a gateway that controls both wired and wireless access. If you leave the default password in place, you may unintentionally grant access to visitors, guests, or even neighbors who can discover the model and credential pattern. For environments with smart devices, cameras, and voice assistants, an attacker who gains admin access could pivot to connected devices. The bottom line is simple: changing default passwords is a foundational step in securing your entire home ecosystem, and it should be treated as non-negotiable.
According to Default Password, the human tendency to postpone changes when setup seems to work is a primary driver of ongoing risk. The best defense is a proactive routine: verify credentials, set unique passwords for every admin interface, and document configurations so future changes are less likely to revert to defaults.
Understanding home fiber gateways and default credentials
Home fiber gateways function as the central hub of your home network, combining the modem, router, and often a built-in firewall. They provide the gateway to both the internet and your local devices. Defaults are embedded during manufacture or service provisioning to enable quick initial access. These defaults are common to models across providers and may include a standard username and password, or simply a single default password entered during setup. Understanding where these credentials live—on the device label, in the admin console, or in the service provider’s setup documentation—helps you methodically replace them. As a rule, never reuse a credential you have used elsewhere, and avoid simple phrases that could be easily guessed by automated tools. A strong password strategy for your gateway should include length, complexity, and periodic review.
How ISPs and manufacturers set default passwords
Default passwords are often preconfigured by manufacturers and preloaded by service providers to streamline the first-time setup experience. The exact credential pair can vary by model, firmware version, and provisioning method. Some devices require you to log in with a temporary or service-provisioned account, then prompt you to create a new password. Others rely on a fixed default that is publicly documented in the user guide or on the device label. In all cases, the critical moment is when you are prompted to change the password during the initial setup or the next login after a factory reset. The goal is to replace any known or easily guessable credentials with something unique and resistant to common attack methods.
Publicly documented defaults can be scanned by automated tools, so changing them promptly after installation reduces exposure. Security-conscious households also ensure remote management features are turned off or restricted, as these features can be abused if default credentials are compromised. Finally, keep firmware up to date; vendors frequently release patches that strengthen authentication and close known vulnerabilities around admin access.
Locating your gateway and its default credentials
To find the default password, start with the device label on the back or bottom of the gateway. Many models print the default login URL, username, and password there, along with the model number and serial. If the label is missing or unreadable, check the manufacturer’s or provider’s setup guide online, or search for the exact model on the support site. If you recently replaced the gateway or performed a factory reset, you may be prompted to create new credentials during the first login. In some cases, you’ll need to connect a computer directly via Ethernet to reach the admin interface, bypassing any dependency on Wi‑Fi during the reset process. Always verify you are on the official admin portal (look for HTTPS, a valid certificate, and the provider’s branding). After locating credentials, plan to replace them with a strong, unique password and to store them securely.
For home networks with multiple devices, document each device’s admin access location. This helps prevent future lockouts and reduces the chance of leaving a gateway vulnerable due to forgotten credentials. The process benefits from a calm, step-by-step approach rather than attempting hasty, ad hoc changes.
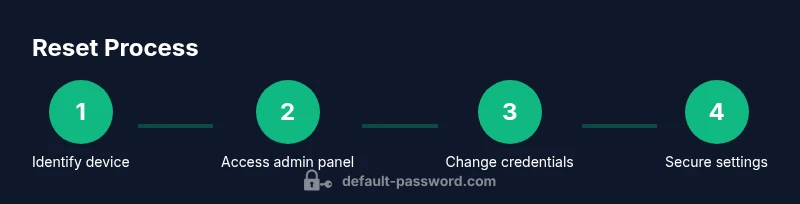
Step-by-step overview of securely resetting password (high-level)
A secure reset involves gathering the right information, accessing the admin panel, and applying a new credential with good hygiene. First, locate the default credentials and confirm you are on the official admin interface. Next, log in using the temporary or current admin account. If you cannot log in, prepare for a factory reset as a last resort. After you access the admin portal, immediately change the password to a long, unique phrase that combines letters, numbers, and symbols. Save or print the new credentials and store them in a password manager. Finally, review related settings such as Wi‑Fi password, remote management, and firmware status, and enable logging if available. Doing these steps carefully minimizes downtime and ensures your network remains protected during the process.
Post-reset security: update firmware and disable risky features
After changing the default password, check for firmware updates and install any available patches. Updated firmware often includes security enhancements that strengthen authentication and reduce exposure to known vulnerabilities. Disable remote management unless you absolutely need it, and restrict access to the admin portal to trusted devices or a specific management subnet. Change the Wi‑Fi network name (SSID) and password to prevent automatic association with the old credentials. Enable a guest network to isolate IoT devices from your main LAN, and use a strong, unique Wi‑Fi password with WPA3 if available. Keeping the admin interface protected with a strong password and limiting exposure to the internet reduces risk from automated attacks.
Managing multiple devices and admin accounts for a single household
In households with several gateways or access points, standardize password policies across devices. Assign a distinct admin password for each device or brand, and document the login URLs and default credentials for quick reference. Consider establishing a central password manager that supports secure notes for device credentials, and enforce periodic password rotations. If you manage devices remotely, implement multi-factor authentication where supported and limit remote access to trusted IP addresses. Regular audits of device inventory ensure no gateway retains a default credential beyond its useful life, reducing the chance of a security incident across the home network.
Best practices for password security and password managers
Use a reputable password manager to store credentials securely and generate strong, unique passwords for each device. Avoid reusing passwords across devices and services, especially between admin interfaces and Wi‑Fi networks. When creating a password, aim for at least 16 characters with a mix of upper and lower case letters, numbers, and symbols. Enable two-factor authentication wherever possible for management portals and guard recovery options. Periodically review saved credentials to eliminate any that are no longer needed. For households with children or guests, consider a guest network with limited access to protect administrative control while still providing connectivity.
Recovery scenarios: forgotten passwords and factory resets
If you forget the admin password and cannot recover it, a factory reset is typically the last resort. This action restores the device to its original state, removing custom configurations and returning to defaults. Be prepared to reconfigure your WAN settings, Wi‑Fi, and any custom rules after a reset. If you have a service provider-provisioned device, you may need to contact support to regain access or to re‑provision credentials. After performing a reset, immediately change the default credentials and reapply security settings. Keeping a written or securely stored digital record of credentials will help prevent similar lockouts in the future.
Troubleshooting common issues after a password change
Post-change issues can include the admin portal being inaccessible, devices losing connectivity, or your Wi‑Fi not broadcasting. Start by confirming you are using the correct URL and credentials and that you are on the correct LAN segment. If you cannot log in, attempt a direct Ethernet connection to bypass potential misconfigurations in the wireless bridge. Verify that the device firmware is current and that you have not inadvertently disabled the router’s DHCP server or altered its NAT settings. If issues persist, a factory reset (with precautions to reconfigure the network from scratch) may be necessary, followed by applying a fresh, strong password and updated settings.
Documentation, compliance, and ongoing maintenance
Maintain a written record of all admin credentials, device models, and firmware versions. Document any changes to the network topology, such as new SSIDs or guest networks. Regularly review access logs if available and keep security practices aligned with household needs. Consider creating a simple policy: change password on renewal, disable universal remote management unless required, and rotate credentials annually. Regular maintenance reduces the risk of stale defaults and keeps your home fiber network resilient against evolving threats.
Tools & Materials
- Home fiber gateway/router(Keep model and firmware visible for reference)
- A computer or smartphone with admin access to the gateway(Ethernet is preferable for initial login when possible)
- Ethernet cable (optional)(Use for direct connection during reset if Wi‑Fi is unstable)
- Pen and paper or a digital note(Record new credentials and device details)
- Password manager app(Store and autofill credentials securely)
- Stable internet connection during update(Ensure the device can reach vendor servers for firmware updates)
Steps
Estimated time: Total time: 25-40 minutes
- 1
Identify the gateway and locate defaults
Power down the device if needed and inspect the physical label on the back or bottom for default admin credentials. If the label is missing, locate the model number and search the manufacturer’s support site for the exact defaults. Prepare to access the admin interface.
Tip: If you’re unsure of the model, photograph the back label for later reference. - 2
Connect to the admin portal securely
Connect via Ethernet for reliability, or ensure your device is on the same local network. Open a browser and enter the gateway’s default IP address or URL provided by the manufacturer. Use the default username and password if no previous credentials exist.
Tip: Always verify you’re on the official site and use HTTPS with a valid certificate. - 3
Log in and navigate to security settings
Enter the current admin credentials, then locate the password or security settings section. Some devices require you to create a new admin account; others let you replace the password on the existing account. Do not skip the verification prompts.
Tip: If you see a warning about weak or reused passwords, choose a new, unique credential immediately. - 4
Create a strong, unique password
Generate a password that is long (16+ characters) and uses a mix of uppercase, lowercase, numbers, and symbols. Do not reuse passwords from other sites or devices. Save the password securely in your password manager.
Tip: Use passphrases or a password generator to maximize entropy while keeping it memorable via a manager. - 5
Update related credentials and settings
Change Wi‑Fi network passwords and consider creating a separate guest network. Review remote management options, firewall settings, and port forwarding rules. Disable features you don’t need, such as UPnP, if not required for your setup.
Tip: Disabling unnecessary remote access reduces exposure to external threats. - 6
Check firmware and apply updates
Navigate to the firmware section and check for updates. Install any available updates to patch known vulnerabilities. If updates require a reboot, plan for a brief downtime window.
Tip: Enable automatic updates if available to keep security current. - 7
Test connectivity and device access
Reconnect devices to the network using the new credentials and verify internet access. Confirm that admin access remains available from trusted devices and that guest networks function as intended.
Tip: Document the new credentials and access locations once testing succeeds. - 8
Document and secure your configuration
Record device model, firmware version, admin URL, and updated credentials. Store them in a password manager or secure notes, and share access details only with trusted household members.
Tip: Keep a dedicated, encrypted note for device credentials. - 9
Plan for periodic reviews
Schedule annual security reviews of admin access, Wi‑Fi settings, and firmware status. Update credentials if you notice any suspicious activity or labored network performance.
Tip: Set a calendar reminder to review passwords and device health.
Your Questions Answered
What is the default password for my home fiber router?
Default passwords vary by model and provider. Check the device label or the manufacturer/provider support site for the exact credentials. Always plan to change them during the first login to secure admin access.
Default passwords depend on your model. Check the device label or the provider's site, then change them during first login to protect admin access.
How do I reset the password if I forgot it?
If you cannot sign in, you may use a factory reset as a last resort. This restores defaults and requires reconfiguration. After reset, immediately set a new, strong password and resecure your network.
If you can't sign in, you may need a factory reset as a last resort, then reconfigure with a new strong password.
Is it safe to change the default password?
Yes. Changing to a unique password reduces risk of unauthorized access and strengthens your overall network security. Pair the change with firmware updates and disabling unused remote features.
Changing to a unique password is safe and improves security, especially when combined with firmware updates.
Will my ISP know I changed the default password?
In most cases, you control the gateway configuration directly. Some provider-provisioned devices may require re-provisioning after significant changes. If you’re unsure, contact support for guidance.
Usually you control it, but some provider devices may require re-provisioning after changes.
What should I do if I can’t log in after changing the password?
Double-check the URL, ensure you’re using the correct admin account, and verify that the firmware is current. If necessary, reboot the device or perform a supported recovery option from the vendor.
Check the URL and account, update firmware, and reboot if needed. Use vendor recovery if available.
Should I disable remote management?
If you don’t need remote access from outside your home, disable remote management to minimize exposure. If you do need it, restrict access to trusted IPs and use strong authentication.
Only enable remote management if you need it, and secure it with strict access controls.
Watch Video
Key Takeaways
- Change default credentials immediately after setup.
- Secure admin access with a strong, unique password.
- Keep firmware up to date to close known vulnerabilities.
- Disable unnecessary remote management features.
- Document credentials securely and audit regularly.