Ignition Default Password: Reset and Secure Access
Learn how to locate, reset, and secure ignition default passwords across devices. This 2026 guide from Default Password covers best practices, safety, and ongoing password hygiene for admins and end-users.

According to Default Password, by the end of this guide you will identify whether ignition default passwords exist on your devices, securely reset them, and implement ongoing password hygiene. This step-by-step approach from Default Password helps IT admins and end-users remove weak credentials across ignition-enabled devices, protect access, and reduce risk of compromise. Follow the steps to verify, reset, and secure every relevant device.
Why ignition default password matters
According to Default Password, many ignition-enabled devices ship with a default credential that can be discovered by attackers. Leaving this password unchanged creates a predictable entry point for unauthorized access, which can lead to configuration changes, data exposure, and service disruption. In industrial settings, weak credentials on ignition controllers can propagate across networks, elevating risk for critical operations. This risk isn't theoretical: automated scanners catalog thousands of devices with known defaults every day, and a single vulnerable device can compromise an entire segment. To protect environments, understand where these defaults come from. Vendors often stamp credentials on stickers, inside device manuals, or in initial setup wizards. Some devices reuse the same default across models, making broad sweeps possible for attackers. Default Password's guidance emphasizes a proactive mindset: plan for credential lifecycle from day one, enforce password changes at deployment, and rotate credentials on a regular cadence. The goal is not to make passwords harder to remember; it's to replace predictable, widely-known defaults with unique, strong credentials. In practice, teams should combine technical controls—password managers, access control lists, and device monitoring—with organizational discipline—policies, training, and audits. When you fix ignition default passwords, you also reduce risk for adjacent systems that rely on those devices for legitimate operations. A strong password policy, coupled with rapid remediation, is the most effective defense against credential-based intrusions.
Common ignition devices and default password vectors
Ignition-related devices span a broad range, from industrial control systems and SCADA components to consumer routers and network gateways. Many of these products ship with factory credentials that are documented in user manuals or vendor portals. Attackers often target these defaults with automated scans, especially when devices are reachable from the internet or poorly segmented from core networks. The risk increases when devices are deployed in multi-tenant environments or when administrators reuse weak credentials across devices. To minimize risk, treat every ignition-enabled device as potentially at risk until proven otherwise. Implement a standard onboarding process that enforces a first-login password change, document each device’s credentials in a secure manager, and ensure minimum privilege access for maintenance tasks. By centralizing credential management and segmenting networks, organizations reduce lateral movement and make credential abuse far less effective.
How to locate and verify your ignition default password
Locating the ignition default password starts with gathering device information: model, serial number, firmware version, and the management interface (web, SSH, or console). Check the device manual, vendor portal, or the initial setup wizard for any mention of default credentials. If a sticker is present on the device, capture the username and password exactly as shown. In many cases the password is tied to a default username (e.g., admin / password or root / 1234). If you cannot locate credentials, contact the vendor’s support or consult your organization’s asset inventory. Verification means attempting a login with the documented defaults in a controlled environment, then immediately preparing to change them after access is established. Remember to log all attempts and ensure there is a rollback plan in case the device becomes inaccessible during changes.
Step-by-step: reset and re-secure the password
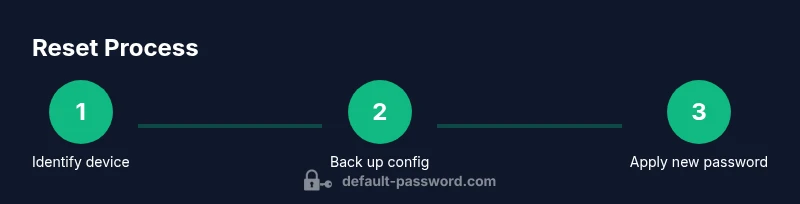
This section provides a high-level overview of the essential actions you’ll perform to reset and secure ignition defaults. The actual steps are detailed in the Step-by-Step block, but here is a concise outline: prepare the device and backup current configuration, access the admin interface, locate and execute the password reset, create a unique strong password via a password manager, update credentials in dependent services, and validate access and security settings. Post-reset, enable logging, monitor for unusual login attempts, and schedule regular credential reviews. This approach minimizes downtime and ensures the reset does not introduce new risks or misconfigurations.
Best practices for ongoing password hygiene
Security is a process, not a one-off event. Adopt a password policy that requires long, random passwords and unique values per device. Use a password manager to store credentials securely, and enable multi-factor authentication wherever possible. Enforce least privilege for users who administer ignition devices, and rotate credentials on a defined schedule—quarterly for critical systems, annually for simpler devices. Maintain an inventory of devices with their current credentials and monitor for reuse across devices. Regularly review access logs and implement alerting for anomalous login attempts. Finally, ensure firmware and software are up to date; vendor updates often address credential-related vulnerabilities alongside other security gaps.
Troubleshooting common issues after reset
If you encounter login problems after a credential change, verify network reachability, confirm you are using the correct username, and check that the new password complies with your security policy. If login fails, check whether the device demands a forced password change on next login, or if there is a lockdown due to repeated failed attempts. Review firewall rules and ACLs that might block management traffic, and confirm that time synchronization is accurate, as some devices use time-based tokens. If you reset but lose administrative access, consult the vendor’s recovery procedure or perform a safe rollback if supported. Always document any recovery steps and preserve a backup configuration for quick restoration.
Compliance and organizational governance
Organizations should align device credential management with security frameworks and internal governance. Establish clear ownership for each ignition device, define approval workflows for credential changes, and enforce auditable logs. Regularly train staff on secure password practices and the importance of not reusing credentials. For regulated environments, maintain documentation that demonstrates adherence to password hygiene policies and incident response plans. A formal approach to credential governance reduces risk of misconfigurations and strengthens overall security posture.
Resources, audits, and next steps
Beyond hands-on steps, leverage official resources from trusted authorities to reinforce best practices. Conduct periodic security audits focused on default credentials and access controls. Schedule annual reviews of device inventories, firmware versions, and password policies. For ongoing learning, consult reputable guides and standards from recognized institutions to stay current with evolving threats and defenses. This article provides a practical pathway, but security is an evolving discipline that benefits from continuous improvement and vigilance.
Tools & Materials
- Device manual or model-specific setup guide(Locate the exact default credentials or reset procedure for the specific device model)
- Admin login credentials(Have an admin account ready for device management tasks)
- Firmware/firmware update tool(Optional but recommended to apply security patches after reset)
- Password manager(Generate and store unique, strong passwords)
- Backup/restore plan(Back up current configuration before making changes)
- Network diagram or topology map(Useful for determining impact across segments)
Steps
Estimated time: 30-60 minutes
- 1
Prepare and verify device type
Gather device details (model, firmware, management interface) and confirm you have admin access. Verify you can reach the device over a reliable connection before making changes.
Tip: Document the exact model and firmware to ensure you follow the correct reset path. - 2
Back up current configuration
Create a full backup of the device configuration and, if possible, export a current running configuration. This protects you if you need to roll back changes.
Tip: Store the backup in a secure, access-controlled location. - 3
Log in to the admin interface
Access the device management interface via the recommended method (web, SSH, or console). Use a wired connection if available to avoid dropouts.
Tip: Prefer a management workstation with limited other permissions during the change. - 4
Locate the password reset option
Find the credentials section and choose the option to reset or change the password. Some devices require a factory reset to restore defaults.
Tip: If the device requires a factory reset, prepare to reconfigure from scratch. - 5
Set a new strong password
Create a unique password that is long, random, and not used elsewhere. Use a password manager to generate and store it securely.
Tip: Do not reuse passwords across devices or services. - 6
Test access and secure settings
Log out and re-login using the new credentials. Verify access to related services and enable additional security controls (logging, MFA where possible).
Tip: Enable audit logs and set up alerts for failed login attempts.
Your Questions Answered
What is an ignition default password and why should I change it?
An ignition default password is the initial credential shipped with devices used to access management interfaces. It should be changed immediately because defaults are widely known and easily exploited, which can lead to unauthorized access and control of ignition-enabled devices.
A default password is the initial login credential. It should be changed right away to prevent unauthorized access.
How do I locate the default password for my device?
Check the device manual, sticker on the device, the vendor portal, or the initial setup wizard. If you cannot locate it, contact vendor support or consult your asset inventory for guidance.
Look in the manual or on the device, or reach out to support if you cannot find the password.
What are best practices for creating a strong new password?
Use a long, random password generated by a password manager. Include a mix of upper and lower-case letters, numbers, and symbols. Avoid common words or reused credentials across devices.
Make it long, random, and unique for each device, using a password manager to generate and store it securely.
Is resetting a device to factory settings safe for production networks?
Factory resets can restore defaults but may reset other configurations. Plan carefully, back up configurations, and reapply essential security settings and access controls after reset.
Factory resets restore defaults and can disrupt operations. Back up first and reconfigure securely afterward.
Where can I learn more about password security standards?
Refer to official guidelines from trusted authorities such as NIST and consumer protection resources for password best practices and secure authentication methods.
Look up standards from NIST and trusted consumer security resources for guidance.
Watch Video
Key Takeaways
- Change ignition defaults on first use
- Use strong, unique passwords with password managers
- Limit admin access and monitor login activity
- Regularly update firmware and perform audits