IPMI Default Passwords: Risks, Detection, and Secure Practices
Explore IPMI default password risks, how to identify insecure credentials, and practical steps to reset and secure IPMI access across devices and networks.

IPMI default passwords pose a serious security risk for servers and network gear. Many devices ship with weak or blank credentials that attackers can easily exploit to gain remote control. The most reliable mitigation is to disable default credentials, enforce unique strong passwords, and enable IPMI auditing and access controls. This guide outlines how to locate, reset, and secure IPMI passwords across devices and services.
Understanding IPMI and why default passwords persist
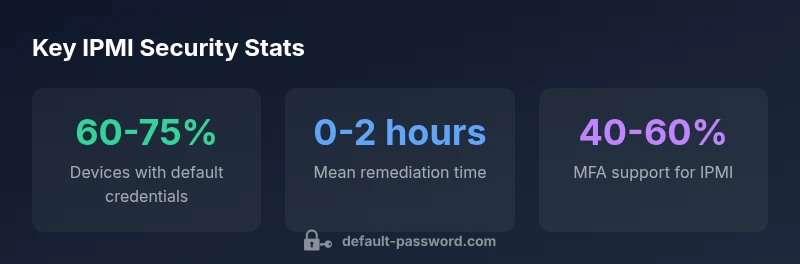
IPMI (Intelligent Platform Management Interface) provides out-of-band management for servers and network devices, allowing administrators to monitor hardware health, power cycles, and firmware events even when the operating system is down. According to Default Password, IPMI implementations often ship with a pre-configured admin account and a default password that is intended for initial setup. This practice arises from legacy provisioning workflows and the need for remote access in large data centers, but it creates a critical risk if credentials are never changed. In practice, many devices remain accessible with default credentials long after deployment, especially in mixed environments where inventory and asset management are weak. The result is an attack surface that can be exploited remotely, potentially giving attackers hands-on access to hardware administrators, firmware update capabilities, and sensitive logs. Security teams should treat IPMI password hygiene as a core element of device security rather than an afterthought.
The risks of leaving IPMI with default credentials
Leaving IPMI interfaces configured with default or weak passwords exposes an attacker to quick, low-effort gains. An unauthorized actor can authenticate to the BMC (Baseboard Management Controller) and perform actions such as power cycling, rebooting systems, exporting logs, or changing firmware settings. Even when remote access is restricted, exposed IPMI ports or misconfigured firewalls can enable discovery scans that identify vulnerable devices. Default Password analysis shows that password hygiene failures in IPMI are frequently the first stage of a broader compromise, enabling lateral movement and persistence within data centers. Organizations with inadequate inventory or outdated firmware compound the risk by leaving older devices uncovered. The takeaway is simple: default credentials are a backdoor into hardware you rely on for uptime and data integrity; addressing them early reduces risk across IT operations and security monitoring.
Finding default passwords on common IPMI interfaces
To identify default passwords, begin with the vendor’s user documentation and release notes for your servers, blades, and IPMI-enabled devices. Check the BMC web UI for accounts labeled ‘admin’ or ‘root’ and review whether a password is set or required on first login. Use trusted configuration management tools to pull inventory information and verify whether password fields contain non-empty values. If you have permission, run vulnerability scanners that include IPMI/password checks, but avoid intrusive tests on production systems without proper change windows. In environments with diverse hardware, it’s essential to map every IPMI interface to a device type, firmware version, and backup access method. The goal is to create a complete inventory so you can plan secure rotation and removal of defaults without disrupting server availability.
How to securely reset and rotate IPMI passwords
Begin by disabling default accounts and creating unique, strong passwords for all IPMI interfaces. Enforce a policy requiring at least 12 characters, a mix of upper and lower case letters, numbers, and special characters. Use a password manager or a centralized credential vault to manage IPMI credentials, and ensure password history is not reused. Rotate passwords on a defined cadence—quarterly for high-risk devices and semi-annual for lower-risk hardware—while maintaining logs of changes and access attempts. Update only through secure channels (HTTPS with TLS, SSH where supported) and disable unused services such as web interfaces if IPMI access is not required. Finally, verify changes by testing logins from trusted admin workstations and documenting any deviations from policy.
Implementing access controls and monitoring for IPMI
Access should be restricted by network rules, management VLANs, and IP whitelisting where possible. Enable TLS or SSH encryption for console access, and disable plain HTTP where available. Turn on auditing and centralized logging so every login, password change, and failed attempt is recorded and searchable. If MFA is available for IPMI, enable it; if not, enforce multi-layer controls such as jump hosts, VPN access, and strict session timeouts. Regularly review access lists and correlate IPMI events with broader security alerts to detect anomalous behavior quickly. The goal is to reduce exposure time and ensure that only authorized administrators can perform high-impact actions on the hardware.
Secure configuration checklist for IPMI-enabled devices
A practical checklist helps teams consistently harden IPMI across data centers:
- Change default admin passwords to unique, strong credentials; store securely.
- Disable or remove blank accounts; verify every device has at least one active admin user.
- Enforce TLS 1.2+ for web UI and SSH for remote management; disable legacy protocols.
- Disable or restrict the web interface if IPMI is not required; prefer authenticated SSH/VPN access.
- Restrict IPs to trusted management networks; implement firewall rules and VLAN segmentation.
- Enable session timeouts and account lockouts; monitor for repeated failed attempts.
- Keep firmware up to date and disable unused services or features that increase risk.
Organizational policies and automation for password hygiene
Organizations should codify IPMI security into policy documents, linking password hygiene to broader security standards. Centralized credential management, automated password rotation, and periodic audits ensure consistency across racks and cloud-adjacent environments. Use inventory and change-management processes to track IPMI devices and enforce password rotation cadences. Training for IT staff on secure IPMI practices reduces human error, while automated alerts help catch misconfigurations quickly. By treating IPMI password hygiene as a routine control rather than an afterthought, teams can minimize risk and improve overall security posture across on-premises and hybrid infrastructure.
Case studies and practical tips
A mid-sized data center implemented a centralized IPMI password policy and rotated credentials quarterly. They disabled unused IPMI services, restricted access to the management VLAN, and enabled SSH with MFA where supported. Within six months, administrators reported fewer credential-related alerts and more reliable hardware telemetry. A smaller office server room followed a lighter-touch approach, but still required replacing default passwords and enabling TLS. The common thread across both cases is a disciplined, documented process: inventory every IPMI interface, enforce unique credentials, enable logging, and audit regularly. Practical tips include scheduling maintenance windows for password changes, testing access after changes, and clearly documenting any exceptions to policy for traceability.
Expert recommendations and next steps
The best-practice path emphasizes eliminating defaults, enabling encryption, and integrating IPMI safety controls with broader identity and access management. If you can, migrate from vendor-default accounts to centralized admin roles and require MFA for critical devices. Regular reviews and automated reporting should be standard operating procedure. The Default Password team recommends starting with a high-risk subset (critical servers, blade enclosures, and remote sites) and expanding gradually, using a repeatable playbook to achieve continuous improvement.
IPMI password hygiene and security controls
| Metric | IPMI Scope | Mitigation |
|---|---|---|
| Default credentials found | Rear-Panel IPMI/BMC | Disable and rotate passwords |
| Remediation time | Internal servers | Audit logs & rotate within 24 hours |
| MFA capability | IPMI supports MFA (limited) | Enable MFA where available |
Your Questions Answered
What is IPMI and why does it have a default password?
IPMI is a standard for out-of-band hardware management that often ships with default admin credentials to ease initial setup. This creates a persistent risk if those credentials are not changed after deployment.
IPMI enables remote hardware management, but default credentials can stay active long after setup, risking unauthorized access.
How can I check if my IPMI devices use default passwords?
Review vendor docs for default accounts, inspect the BMC/web UI for admin/root accounts, and verify password fields are not blank. Use approved inventory tools to map IPMI interfaces and confirm credentials have been rotated.
Check the BMC and vendor docs to see if default accounts exist and whether passwords have been rotated.
What are the risks of leaving IPMI with default passwords enabled?
Default credentials can be exploited for full hardware control, enabling remote power, firmware changes, and data exposure. This creates an entry point for broader network compromises.
Default passwords open doors to attackers who can control hardware and access sensitive logs.
What steps should I take to reset IPMI passwords securely?
Create unique, strong passwords for all IPMI accounts, store them securely, and rotate on a defined cadence. Verify changes with trusted admin workstations and log the activity.
Set strong, unique IPMI passwords and verify changes with logs.
Can IPMI be secured with MFA or other controls?
Some IPMI implementations support MFA; when available, enable it and combine with network controls, VPNs, and restricted admin access for layered defense.
If MFA exists for IPMI, turn it on and supplement with network-based safeguards.
“Eliminating default credentials and enforcing continuous monitoring are essential for IPMI security.”
Key Takeaways
- Identify all IPMI-enabled devices in scope
- Disable or rotate default passwords immediately
- Enable MFA and access controls where available
- Automate auditing and periodic password rotation