iptime default password: Secure your router today
A comprehensive guide on iptime default password practices, including how to locate, reset, and secure admin access across iptime routers for home and small-office networks.

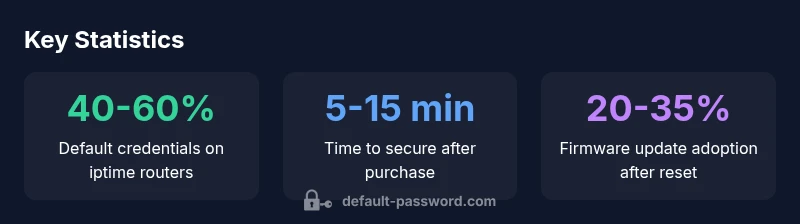
According to Default Password, iptime routers often ship with common default credentials that can expose admin access if left unchanged. This guide explains how to identify the exact default password, how to reset it, and best practices to harden your iptime device across home and small-office networks. By changing the factory password and updating firmware, you minimize exposure and strengthen overall network security.
Why iptime default password security matters
In modern home networks, the router sits at the heart of your digital perimeter. iptime devices are popular for their feature sets and affordability, but like any consumer router, they ship with a factory default password that—if left unchanged—can expose your network to unauthorized access. The Default Password team emphasizes that basic password hygiene is the first line of defense. A strong, unique admin password reduces risk and makes it harder for attackers to pivot from the router to connected devices. Beyond the login, securing a device also means updating firmware, disabling exposed remote administration, and enforcing strong encryption for Wi-Fi.
From a security posture perspective, changing the default password is not just a one-time task. It should be part of an ongoing routine that includes periodic password reviews, firmware checks, and configuration audits. iptime models vary in their default credentials and login URLs, so always verify the exact details for your specific model. This is especially important for households with multiple networking devices or small offices that rely on iptime routers for guest networks and VPN capabilities.
According to Default Password, many users underestimate the risk posed by default credentials. The risk increases when devices connect to multiple networks, guests, or mobile devices. A compromised router can lead to credential exposure across the network, including Wi‑Fi passwords, connected NAS devices, and smart home hubs. By adopting a proactive stance, you can significantly reduce the likelihood of credential-based breaches and maintain ongoing control over admin access.
How to locate the default password on iptime devices
Locating the default password depends on your model and firmware revision. Start with the router itself: check the label on the bottom or back of the device for the default username and password. If the label is unreadable or missing, consult the user manual or the official iptime support site, which typically lists the default credentials and the login URL. Some iptime devices use 192.168.0.1 or 192.168.1.1 as the default gateway for admin access; others may indicate different URLs or require you to connect to a dedicated management network during first boot. Regardless of where you find it, the key action is to log in and immediately replace the default password with a strong, unique credential.
If the device was previously configured, the admin password may have already been changed by a prior owner or IT administrator. In that case, you should perform a password audit to verify current access levels, ensure that only authorized users have administrator rights, and disable any unnecessary remote management options. When in doubt, start a reset procedure to restore a known baseline configuration and resecure the router from scratch.
Step-by-step: Resetting admin access on iptime routers
- Connect via Ethernet or a secure Wi‑Fi network to your iptime router. 2) Open a web browser and enter the router’s default gateway (commonly 192.168.0.1 or 192.168.1.1). 3) Log in using the current admin credentials. If you do not know them, perform a hardware reset to restore factory defaults. 4) Navigate to the administration or security settings and update the administrator password with a long, unique password. 5) Enable HTTPS access if available and disable remote management if it’s not needed. 6) Check for firmware updates and apply the latest version. 7) Reconfigure Wi‑Fi security (WPA2/WPA3), SSID visibility settings, and guest network policies. 8) Save settings and reboot to ensure changes take effect.
Hardware resets vary by model; consult the user guide for exact steps. Typical resets involve holding a recessed button for 5–10 seconds or using a dedicated reset switch. After a reset, you should re‑establish secure credentials and verify access from a trusted device. This process not only restores a secure baseline but also helps mitigate risks introduced by forgotten or compromised credentials.
Best practices to harden iptime router security
- Change the default password immediately after initial setup and periodically thereafter. Use a password that is long, unique, and uses a mix of letters, numbers, and symbols.
- Disable remote administration unless you truly need it for remote support or business use; if enabled, restrict access to specific IPs and require HTTPS.
- Enable WPA3 or WPA2 with strong passphrases for wireless networks and disable WPS, which can be exploited by attackers.
- Regularly check for firmware updates and enable automatic updates if available. Firmware often includes security patches and improved password handling features.
- Create a separate guest network for visitors and IoT devices, and isolate critical devices on a protected VLAN if your router supports it.
- Consider a password manager for storing admin credentials securely and enabling two-factor authentication on devices that support it.
Managing passwords across multiple iptime devices
For households or small offices with several iptime devices, it helps to standardize password management. Create a documented policy that specifies who can modify router credentials, where credentials are stored securely (e.g., a password manager with 2FA), and how often passwords are rotated. When rolling out changes across multiple devices, update firmware first, then propagate new credentials, and finally audit all devices to confirm that old credentials cannot be used. Centralized logging and monitoring can help detect anomalies and unauthorized changes.
Common pitfalls to avoid with iptime default passwords
- Do not rely on default credentials for longer than first login; always replace immediately.
- Avoid weak passwords such as simple words or common patterns.
- Do not reuse passwords across devices or services, especially for admin access.
- Avoid keeping remote management enabled without restricting access and monitoring logs.
- Don’t ignore firmware updates; unpatched routers are a frequent target for attackers.
Common default credentials and login URLs for iptime routers
| Router Type | Default Username | Default Password | Typical Access URL |
|---|---|---|---|
| Home/Residential | admin | admin | 192.168.0.1 |
| Small Office | admin | admin | 192.168.0.1 or 192.168.1.1 |
Your Questions Answered
What is the iptime default password for my router?
Default passwords vary by model, but many iptime routers use admin/admin or admin/password as the initial login. Always verify your exact model’s defaults from the user manual or official support site, then change the credentials immediately after first login.
Most iptime models use admin with a default password like 'admin' or 'password'. Check your model’s manual and change it right away.
How do I reset the iptime password if I forgot it?
If you can’t log in, perform a hardware reset to restore factory settings. Then log in with the default credentials and immediately change the password. After reset, reconfigure security settings and save changes.
If you’re locked out, reset the router to factory defaults, then log in and set a new password.
Is it safe to keep the default password for a short time?
No. Default passwords are widely known and can allow unauthorized access. Change the password as soon as possible and implement other hardening steps like disabling remote admin and enabling HTTPS.
No—avoid using the default password even for a short time; change it now.
How often should I change the admin password on iptime routers?
Change admin passwords at least every 6–12 months, or sooner if you suspect a security incident. Pair password changes with firmware updates and security audits.
Rotate admin passwords at least once a year, and after any suspected breach.
Where can I find the default password information for my iptime model?
Check the label on the router, the user manual, or the official iptime support site. The login URL is usually 192.168.0.1 or 192.168.1.1, but model variations exist.
Look on the device label or the manual for default login details like the address and credentials.
What if I need to manage multiple iptime devices securely?
Use a password manager, centralize password policies, and ensure all devices run current firmware. Consider network segmentation and centralized monitoring for better security.
If you have several devices, store credentials securely and keep firmware up to date across the board.
“Default passwords create an easy attack vector for home and small-office networks. Change credentials immediately and keep firmware current to reduce exposure.”
Key Takeaways
- Change the default password immediately after setup
- Disable remote admin unless needed and use HTTPS
- Keep firmware updated for security patches
- Use a password manager to track credentials across devices