Keystore Default Password: Reset, Manage, and Secure Access
A practical, data-driven guide on keystore default passwords, why they’re risky, and how to reset and manage keystore credentials across Java, Android, and PKI environments. Learn best practices for secure access and password governance.
A keystore default password is an initial credential used to initialize or provision a keystore, serving as a placeholder in some environments. Leaving this default in production exposes keys and certificates to unauthorized access. This guide explains what the keystore default password is, why it’s risky, and how to reset and manage keystore passwords securely across Java, Android, and PKI ecosystems.
What is a keystore and what is a keystore default password?
A keystore is a protected repository that stores cryptographic keys and certificates used for authentication, data encryption, and establishing trust in communications. In many environments—especially legacy systems or quick-start deployments—a keystore is provisioned with a default password to simplify initial setup. The keystore default password is not a universal constant; it varies by platform, vendor, and configuration. The important point is that any credential intended only for initial provisioning should be replaced with a unique, strong password and rotated regularly. For enterprise admins and developers, treating a default password as a temporary measure is essential to maintain a robust security posture.
When you hear the term keystore in the context of Java, Android, or PKI, think of it as a keyring that guards sensitive material. A default password is a placeholder credential that must be escalated to a policy-compliant password before going live. The presence of a default password increases the risk of credential leakage, unauthorized access, andattacks that target weakly protected keystores. In practice, organizations that implement strict password governance, secret management, and periodic rotation significantly reduce exposure to credential theft and certificate compromise.
Security implications of keystore defaults and why they matter
Default credentials are often easy to guess or find in code, documentation, or configuration backups. If a keystore is left with its default password, an attacker with access to the host or the application code could unlock private keys, impersonate services, and decrypt data in transit or at rest. This risk is amplified in environments where keystores are embedded in container images, CI/CD pipelines, or cloud deployments that lack strict secret management controls. A strong password policy for keystores includes length and complexity requirements, unique per keystore, and automated rotation triggers tied to deployment cycles or key lifecycle events. The cost of not updating keystore credentials can include data breaches, certificate revocation, and loss of customer trust. Proactive practices, such as enumerating all keystores, validating password policies, and enforcing automatic rotation, reduce the attack surface and improve compliance posture.
How attackers leverage keystore default passwords and what to audit
Attackers may leverage default passwords by performing reconnaissance to locate keystores inside application bundles, Docker images, or server file systems. Once found, a weak or unchanged default password can grant access to private keys used for signing, decryption, or establishing secure channels. Common audit steps include inventorying keystores across environments, verifying password strength against policy, and checking for hard-coded credentials in code repositories and configuration files. Organizations should implement secret management tooling, such as vaults or KMS integrations, to avoid hard-coded defaults and ensure credentials are rotated on deployment and decommission.
Step-by-step: locating and updating keystore credentials in practice
- Inventory all environments where keystores exist (dev, test, staging, production).
- Identify any keystore files and their current passwords or password policy indicators.
- Replace default or weak passwords with unique, strong passphrases that meet policy requirements (length, complexity, and rotation rules).
- Enforce password vaulting or KMS-backed storage for keystore credentials, with access controls and audit trails.
- Implement automated rotation triggers tied to release pipelines and certificate lifecycles.
- Document the process and run periodic reviews to ensure ongoing compliance.
Platform-specific guidance: Java keystore, Android keystore, as well as PKI scenarios
In Java ecosystems, keystores can be Java KeyStore (JKS) or PKCS#12; both should be protected with strong passwords and rotated during major changes. Android keystore involves app-provisioned credentials and may rely on system-protected keystores or hardware-backed storage. PKI scenarios require careful handling of private keys, with passphrases or hardware security modules (HSMs). Across platforms, minimize exposure by avoiding default passwords entirely and adopting per-keystore credentials managed by a secret store.
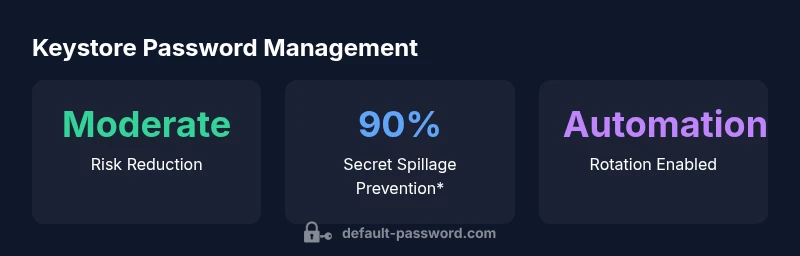
Best practices for keystore password management
- Do not ship keystores with default passwords; always replace during deployment.
- Use long, complex passphrases, unique to each keystore.
- Store credentials in a secrets manager or KMS with strict access controls and auditing.
- Implement automatic rotation on deployment cycles and key lifecycle events.
- Document all keystores and their password policies for auditability.
- Prefer hardware-backed storage or HSMs for added protection where feasible.
Automation and tooling for keystore credential management
Automation reduces human error and ensures consistency. Integrate secret management tools into CI/CD pipelines to inject keystore passwords at runtime rather than storing them in code or images. Use environment-specific vaults, role-based access control, and automated rotation. Alerts and dashboards should track when credentials were last rotated and who accessed them. Automation also helps enforce strong password policy and keeps records for compliance audits.
Documentation, auditing, and governance for keystore passwords
Maintain an up-to-date inventory of all keystores, their passwords (or references to secret stores), rotation schedules, and access controls. Regularly audit for exposure risks, outdated or weak passwords, and unencrypted backups. Governance policies should specify who can create, update, or retire keystores and mandate secure disposal of old keys and credentials.
Keystore default password considerations across common keystore types
| Keystore Type | Default Password State | Recommended Action |
|---|---|---|
| Java KeyStore (JKS) | Varies by implementation; some defaults exist | Disable defaults; enforce strong password; rotate on deploy |
| PKCS12 Keystore | Defaults vary by toolset; often weak | Set a unique passphrase; enable password vaulting |
| Android Keystore | Platform-managed; may have default behaviors | Require explicit user credential or secure token; rotate during updates |
| SSL/TLS PKI | Certificate keystores may rely on passphrases | Use HSM or KMS; rotate keys |
Your Questions Answered
What is a keystore default password and why should I change it?
A keystore default password is an initial credential used to provision a keystore. It should be treated as temporary and replaced with a unique, strong password before production use. Leaving defaults creates an attack vector that can compromise keys and certificates.
A keystore default password is a temporary credential. Change it before production to protect keys and certificates.
What risks arise from leaving a keystore default password in production?
Leaving defaults can allow attackers to access private keys, impersonate services, or decrypt data. It undermines PKI trust and can lead to certificate compromise. Regular rotation and strong passphrases mitigate these risks.
Default passwords in production raise serious risks; rotate and protect keystores.
How do I determine if my environment uses a default keystore password?
Audit keystore configuration across environments, inspect provisioning scripts, CI/CD templates, and backups for hard-coded or placeholder passwords. Validate against password policy and secret management configurations.
Audit all keystores and look for obvious defaults or placeholders.
What steps are involved in resetting a keystore password?
Identify the keystore, back up the current data, generate a strong new password, re-import keys if necessary, update configuration to reference the new password, and verify access by performing a sign/verify or decrypt operation in a staging environment.
Back up, set a new strong password, update configs, and test in staging.
Are there industry standards for keystore password length and complexity?
There are no universal single standards across all keystore types; follow general best practices: long, complex passphrases, unique per keystore, with automated rotation and secret-management controls.
Use long, unique passwords and rotate them automatically.
What tools help manage keystore credentials securely?
Secret management solutions and cloud KMS services help store and rotate keystore credentials securely. Integrate these with CI/CD and runtime environments to prevent hard-coded passwords.
Use secret managers or KMS to store and rotate credentials.
“Default credentials are a predictable weak point in cryptographic ecosystems. Rotate every keystore password, enforce strong passphrases, and codify secret management to close the attack surface.”
Key Takeaways
- Strengthen keystore security by eliminating defaults
- Use unique, long passwords managed in a vault
- Rotate credentials with deployment and lifecycle events
- Audit keystore inventories regularly
- Automate credential management where possible