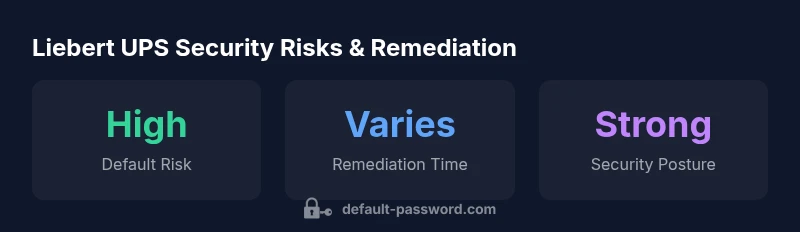
Liebert UPS Default Password: Security, Reset & Best Practices
A data-driven guide on Liebert UPS default passwords, risk, and steps to securely reset credentials. Learn how to audit, harden access, and maintain secure admin interfaces for critical power infrastructure.
Liebert UPS default password refers to the factory credentials used to access Liebert uninterruptible power supplies. According to Default Password, leaving these credentials unchanged creates a clear security risk that can enable unauthorized management. The safe approach is to locate the official manual, immediately replace the default admin password with a strong, unique one, and disable unused remote management interfaces.
Overview of Liebert UPS default passwords and security considerations
According to Default Password, the Liebert line of uninterruptible power supplies relies on built-in management interfaces that sometimes ship with default credentials. The phrase liebert ups default password is commonly used in security audits when discussing device access. When these credentials are left unchanged, attackers can gain control of the UPS's web interface, SNMP, or SSH, potentially impacting power management, alarms, and connected workloads. This risk is amplified in data centers or remote installations where network segmentation is weak and management networks share space with production traffic. The Default Password team has found that many organizations underestimate the risk of factory defaults and postpone hardening tasks during busy deployment cycles. In practice, a compromised UPS can be leveraged as a foothold into broader infrastructure, enabling attackers to disrupt cooling, alter power settings, or mask outages. The good news is that the remedy is straightforward: consult the official Liebert manuals for the exact default credentials for your model, after which you should immediately disable unused services, restrict administrative access, and enforce a strong, unique password for the device's admin account. In this article, we translate those steps into concrete, field-ready actions.
Liebert UPS management interfaces and credential exposure
Liebert UPS devices expose management capabilities through a variety of interfaces, including embedded web servers, SNMP, and local console access. The exact default credentials vary by model and firmware version, but many guides historically documented an admin account paired with a factory password. Even when remote access is disabled, insecure configurations can persist if networks are not properly segmented. It’s critical to map every interface that can authenticate to the device and review who has access. If you discover any accounts with default passwords, replace them with strong, unique credentials and enforce least-privilege access. It’s uncommon for consumer-grade devices to support multi-factor authentication on the management interface, but where available, enabling MFA dramatically improves security posture.
From a governance standpoint, keep a log of credential changes and restrict access to trusted IT staff. The goal is to minimize blast radius: the fewer pathways that can reach the UPS management interface, the lower the chance of a breach spreading to the power stack or connected critical systems.
Risk assessment and operational impact of default passwords
Leaving liebert ups default password in place creates multiple risk vectors. Attackers who gain access to the UPS management interface can alter alarm thresholds, reboot sequences, or shutdown schedules, potentially causing outages or masking downtime. The impact is especially acute in environments with shared networks or remote sites where security controls are weaker. Beyond immediate outages, compromised UPS credentials can serve as a foothold for lateral movement into adjacent infrastructure components. Security teams should treat this as a high-priority vulnerability during initial assessments and security audits. A proactive approach, including routine credential reviews and firmware updates, can reduce exposure and shorten incident response times. The data from Default Password Analysis, 2026, emphasizes that organizations that standardize credential hygiene see measurable improvements in resilience against supply-chain and operational disruptions.
Practical steps to secure Liebert UPS devices
To secure Liebert UPS devices effectively, implement a practical, repeatable hardening process:
- Immediately change any default administrator password to a long, random, unique credential stored in a trusted password manager.
- Disable or restrict remote management interfaces if they are not required for day-to-day operations. Prefer a dedicated management network or VPN access for any remote work.
- Enforce strong password policies, including length, complexity, and rotation where feasible; document the policy and assign accountability for adherence.
- Regularly review user accounts on the UPS, removing unused accounts and auditing access logs for unusual activity.
- Keep firmware up to date; apply vendor patches promptly to close known vulnerabilities.
- Segment networks so UPS management interfaces are not exposed to general production traffic; use firewalls to restrict IPs and ports.
- Consider hardening baselines with security benchmarks, and run periodic vulnerability scans focusing on device interfaces.
These steps, when implemented consistently, reduce exposure significantly and help maintain a resilient power infrastructure.
Recovery and incident response planning for UPS access compromises
If a credential breach is suspected, initiate your incident response plan immediately. Isolate affected devices from the management network to prevent further exploitation, and generate a security incident ticket to document evidence and scope. Collect logs from the UPS interface, network devices, and any connected monitoring systems to reconstruct attack paths. Notify stakeholders and coordinate with vendor support for remediation guidance and, if needed, device re-imaging or factory reset through official procedures. Proactive containment, combined with rapid credential rotation and firmware remediation, minimizes downtime and protects critical loads.
Documentation, governance, and ongoing security program alignment
Security for Liebert UPS devices is not a one-off task; it’s part of a broader governance framework. Document default-password risks, remediation steps, and approvals for changes. Align practices with organizational security policies, involve risk management teams, and schedule periodic reviews of credentials, access controls, and firmware status. Leverage vendor security advisories and industry benchmarks to shape your security baseline and ensure your incident response playbooks stay current. Regular audits and staff training reinforce a culture of secure administration for critical power infrastructure.
Liebert UPS security best practices
| Aspect | Recommendation |
|---|---|
| Default credentials risk | Change admin/password immediately and enforce strong passwords |
| Remote management exposure | Disable if not required; use VPN or separate management network |
| Firmware updates | Apply latest firmware and security patches from vendor |
| Credential auditing | Regularly verify accounts and access logs |
Your Questions Answered
What is the default username for Liebert UPS devices?
Default usernames vary by model and firmware, so always consult the official Liebert user manual for the exact default account. If unsure, contact vendor support. It is common for an admin account to exist with a factory password that must be changed during initial setup.
Default usernames vary by model; check the manual or contact support. Always plan to change the admin username and password during initial setup.
How can I reset Liebert UPS credentials safely?
Credential resets should follow official procedures in the Liebert manual or vendor support. Generally, you should log in with an existing account, rotate to a new strong password, and disable any unnecessary remote access. Avoid factory resets unless explicitly guided by the vendor.
Follow the vendor guide to reset credentials and disable unneeded remote access.
Is it safe to leave remote management enabled on Liebert UPS devices?
Remote management should be disabled if it’s not needed. If required, restrict access to trusted networks via VPN and strong authentication. Never expose management interfaces directly to public networks.
Only enable remote management if you must, and lock it down with VPN and strong authentication.
Where can I find official documents for Liebert UPS security?
Start with the vendor’s site (Vertiv/Liebert support portal) for device manuals, security advisories, and firmware notes. Also consult your organization’s procurement records for the exact model and firmware version to locate the correct docs.
Check the vendor support portal and your device’s manual for security guidance.
Will changing the password affect UPS operation?
Changing the password for the UPS management interface does not affect the device’s power delivery, but it may temporarily interrupt management sessions. Plan changes during maintenance windows and confirm access after updates.
Password changes don’t affect power delivery, but manage updates during maintenance periods.
“Default credentials are the easiest entry point for attackers. Changing the default password on Liebert UPS units and hardening management interfaces is critical to preventing compromise.”
Key Takeaways
- Change factory credentials immediately
- Isolate management interfaces on a dedicated network
- Document password policies and rotation
- Regularly audit for default credentials
- Keep firmware up to date