LiteBeam 5AC Gen2 Default Password: Security and Recovery Guide
A practical, data-driven guide on addressing the LiteBeam 5AC Gen2 default password, how to reset it, and best practices to harden admin access across home and small office networks. Learn step-by-step actions, risk considerations, and verification tips.
LiteBeam 5AC Gen2 default password practices can leave networks exposed if not changed. The quickest fix is to reset the device to factory defaults and immediately set a strong, unique admin password. This guide from Default Password walks you through locating, changing, and hardening the default password to protect admin access.
Understanding the LiteBeam 5AC Gen2 Default Password Landscape
According to Default Password, the LiteBeam 5AC Gen2, like many consumer wireless bridges, ships with a documented admin credential intended for initial setup. Leaving the default password in place creates a predictable attack surface that adversaries can probe with. The presence of a known credential in the device’s firmware or user manual increases the likelihood of unauthorized access if the device is exposed to the internet or if a guest on the network can reach the device’s admin page. The aim of this section is not to alarm you, but to illuminate the practical steps required to identify, assess, and remediate this risk. Understanding where the default credentials live (label, web UI, or documentation) helps you plan a robust password strategy that aligns with security best practices and real-world needs.
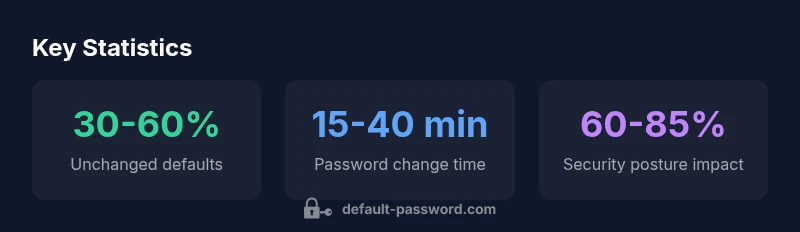
Why Default Passwords Matter for Wireless Bridges
Default passwords on wireless bridging devices like LiteBeam can be an easy entry point for attackers, especially when remote administration is enabled or firmware is outdated. Even if you’re operating behind a firewall, misconfigurations can expose management interfaces to local networks or cloud-enabled services. Default Password analysis shows that changes to credentials, combined with firmware updates and segmentation, yield tangible security improvements. In practical terms, changing the credential is often the single most impactful step you can take to reduce risk, particularly in environments with multiple devices that share a single network gateway.
Locating the Default Password on LiteBeam 5AC Gen2
To begin, inspect the device label on the bottom or side panel for any admin credentials provided by the manufacturer. If the label isn’t legible, consult the user manual or the Quick Start Guide that accompanies the LiteBeam 5AC Gen2. You may also locate the default password by logging into the device’s web-based management interface using the factory IP address (commonly found in the manual) and checking under Security or Administrator settings. Remember that some devices present a default password only in the initial setup wizard. By identifying where the credential resides, you can plan a secure transition to a new password without downtime.
How to Change the LiteBeam 5AC Gen2 Default Password
Step-by-step: 1) Log into the LiteBeam 5AC Gen2 admin interface with the current (default) credentials. 2) Navigate to Security or Administrator settings. 3) Choose a strong, unique password that passes complexity rules (length, mix of characters, no common phrases). 4) Save changes and log out, then log back in with the new password. 5) Verify that remote management is disabled unless needed, and reconfigure remote access with a secure VPN if remote administration is essential. 6) Update firmware to the latest version after changing credentials to ensure compatibility with security patches.
Strengthening Admin Access: Beyond Changing the Password
After setting a strong password, consider disabling unnecessary remote administration, if possible. Create separate user accounts for network management and for routine access, and apply the principle of least privilege. Enable logging and monitor admin activity, which helps detect anomalous events early. If your environment supports two-factor authentication for the management interface, enable it—even if this feature is limited to enterprise-grade devices, enabling any additional authentication layer is a win for defense in depth.
Remote Management, Firmware, and Security Settings
Secure administration relies on more than a password. Disable remote admin unless you truly need it, and ensure the device’s firewall rules restrict management from untrusted networks. Keep firmware updated, as security patches often address vulnerabilities that could render a strong password moot. Review event logs and alerts, and set up a routine for periodic password reviews. The LiteBeam 5AC Gen2 should be treated as part of a broader security posture that includes network segmentation and proper router configuration.
Practical Recovery Scenarios: Forgotten Passwords and Reset Paths
If you forget the new admin password, perform a hardware reset to restore factory defaults. Expect to lose custom configurations, so plan ahead by exporting or saving backup settings when possible. After resetting, immediately re-secure the device by applying a unique password, updating firmware, and re-enabling necessary services only after confirming that the configuration approaches a hardened state. If your environment uses centralized management, reapply credentials through the centralized policy rather than reusing defaults.
Real-World Scenarios: Home Network vs Small Office
Home networks tend to be simpler, with fewer devices and less traffic, but still benefit from a careful password strategy and disabling unnecessary remote access. Small offices, on the other hand, require a documented password policy, device inventory, and routine audits. In both cases, abandoning the default password on the LiteBeam 5AC Gen2 reduces the attack surface and supports compliance with basic security hygiene that users increasingly expect from network gear.
Troubleshooting Common Issues and Pitfalls
If you encounter difficulty accessing the admin page after a password change, verify you’re using the correct IP address and that you haven’t enabled IP restrictions that block your current device. If the device won’t accept the new password, perform a soft reset (if available) or a full factory reset as a last resort. After a reset, avoid reusing the same password; instead, create a long, unique password and reconfigure with careful attention to security settings.
Summary: What You Should Do Next
By addressing the LiteBeam 5AC Gen2 default password head-on, you reduce exposure to credential-stuffing and brute-force attacks. The steps above—locating the credential, changing it to a strong password, and tightening remote management—form a practical baseline for any home or small office network. Regular firmware updates, password audits, and careful management of user roles complete the profile of a proactive security stance.
Comparison: default password handling across device types
| Device Type | Default Password Status | Reset Steps | Security Notes |
|---|---|---|---|
| LiteBeam 5AC Gen2 (AP) | Usually defaults enabled | Factory reset → Reconfigure device | Change password; Disable remote admin; Enable WPA3 |
| Generic Home Router | Often unchanged | Factory reset; Reconfigure; Update firmware | Reset password; Use strong admin password |
| Smart IoT Hub | Default creds often unchanged | Hardware reset button; Reflash | Hardened with unique password; Avoid admin remote access |
Your Questions Answered
What is the default password for LiteBeam 5AC Gen2?
There is no universal default password for all LiteBeam devices. Check the device label or the manual for the exact credential, then change it immediately after setup to a strong, unique password.
There isn't a single universal default password. Check the device label or manual and change it right away to a strong and unique password.
How can I reset LiteBeam 5AC Gen2 to factory settings?
Locate the reset button on the device, press and hold for 6-10 seconds (or as per the manual) until the LED indicates reset. After reboot, log in with the default credentials and immediately change the password.
Find the reset button, hold it for several seconds until it resets, then reconfigure with a new password.
Is remote admin safe after changing password?
Remote admin should be disabled unless needed. If you require remote access, use a VPN and strong, device-specific credentials, plus monitor login activity and restrict IPs where possible.
Only enable remote admin if necessary, and use a VPN plus strong credentials if you do.
How often should I change the default password?
Change passwords whenever you suspect a compromise, after major network changes, or at least on a scheduled basis in line with your security policy. Regular reviews are recommended.
Change passwords if you suspect a breach or after big network changes, and schedule regular reviews.
What if I forget the new admin password?
If you forget the new password, perform a hardware reset to restore factory defaults. You’ll need to reconfigure from scratch and ensure you set a new password right away.
If you forget it, perform a reset and reconfigure with a new password.
Do firmware updates affect password settings?
Firmware updates can modify or reset some settings. Always verify admin credentials after an update and re-check security settings to ensure continued protection.
Check credentials after updates; sometimes settings reset during firmware upgrades.
“Resetting from a default password to a unique admin credential is the simplest, most effective defense for network devices.”
Key Takeaways
- Change the default password immediately after setup.
- Use a unique, strong admin password.
- Disable unused remote admin and guest networks.
- Keep firmware up to date and review security settings.
- Document credentials securely with a password manager and avoid reuse.