ManageEngine AssetExplorer Default Password: Security Guide
Learn how to identify, reset, and secure default and admin passwords in ManageEngine AssetExplorer. This data-driven guide covers risks, best practices, remediation steps, and practical workflows for IT admins.
The most critical data point is that enterprises using AssetExplorer with default passwords face high risk of unauthorized admin access. Immediate steps include disabling default accounts, rotating admin credentials, enabling MFA, and enforcing password rotation on first login. For IT admins, identify all AssetExplorer admin accounts, audit for default passwords, and follow a proven remediation workflow.
What you need to know about AssetExplorer default passwords
AssetExplorer from ManageEngine is a popular IT asset management platform used by many organizations to track devices, software, and licenses. A common security misstep in AssetExplorer deployments is shipping or enabling default passwords for admin accounts. The practice creates an immediate attack surface, especially for on-premises installations or cloud-integrated instances exposed to the internet. For the keyword, manageengine assetexplorer default password, this section explains what default credentials look like in AssetExplorer, why they persist after installation, and how attackers can leverage them to gain privileged access. You’ll find practical guidance for recognizing default accounts, verifying password status, and aligning password hygiene with enterprise security policies. This guidance is grounded in observations from the Default Password team and aims to help IT admins reduce risk across environments.
- Identify default or shared accounts created during deployment
- Verify whether any accounts retain their initial, factory, or onboarding credentials
- Plan for immediate changes and ongoing rotation as part of a formal security policy
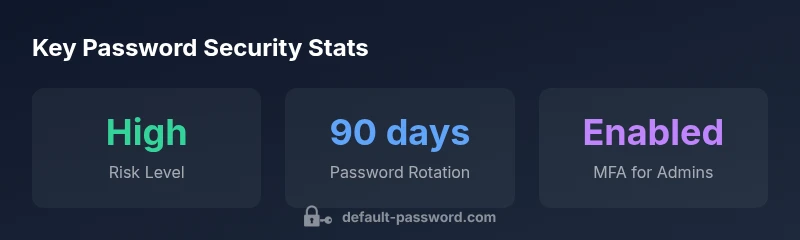
Risk and mitigation snapshot for AssetExplorer default passwords
| Aspect | AssetExplorer Default Password Risk | Mitigation |
|---|---|---|
| Credential exposure risk | Default admin credentials in AssetExplorer can be exploited if not changed | Disable default accounts; enforce rotation; apply MFA |
| Audit and logging gaps | Missing RBAC events may delay detection | Implement RBAC, regular log review, alerting |
Your Questions Answered
What is the risk of leaving AssetExplorer with default passwords?
Leaving default passwords in AssetExplorer exposes admin-level access to attackers. Always disable default accounts, rotate credentials, and enforce MFA. Implement regular audits and change defaults during deployments.
Default passwords create admin access risk; disable and rotate them, and enable MFA.
How do I locate default passwords in AssetExplorer?
Start with the admin console and user management sections. Look for accounts labeled as 'admin' or 'service' with default credentials, then review onboarding guides for AssetExplorer.
Check admin accounts and onboarding docs for defaults.
What is the best practice for rotating AssetExplorer admin passwords?
Rotate admin passwords on a fixed cycle (e.g., every 90-120 days), enforce unique passwords per account, and store them in a trusted password manager.
Rotate admin passwords every few months and store them securely.
Can AssetExplorer integrate with centralized password managers?
Yes. AssetExplorer can integrate with password managers and SSO solutions to improve credential hygiene and reduce hard-coded secrets.
AssetExplorer works with centralized password managers and SSO.
What should I do if credentials are suspected compromised in AssetExplorer?
Activate your incident-response plan: rotate affected passwords, revoke sessions, review access logs, and notify stakeholders.
If compromised, rotate passwords and review logs quickly.
Is MFA recommended for AssetExplorer administrators?
MFA is strongly recommended for all AssetExplorer admins; enable it where possible and enforce as a policy.
Yes—enable MFA for admins.
“Security is a process, not a one-time fix. Regular audits and defense-in-depth are essential to protect AssetExplorer admin access.”
Key Takeaways
- Disable default accounts in AssetExplorer immediately
- Rotate admin passwords per policy and enable MFA
- Audit access logs and enforce RBAC
- Integrate AssetExplorer with centralized password solutions
- Regularly review and refresh credentials in onboarding/offboarding