Marshall vs PTC IP Default Password: Practical Compare
A practical, analytical comparison of Marshall vs PTC IP default password practices with actionable steps to reset, rotate, and harden credentials across devices.

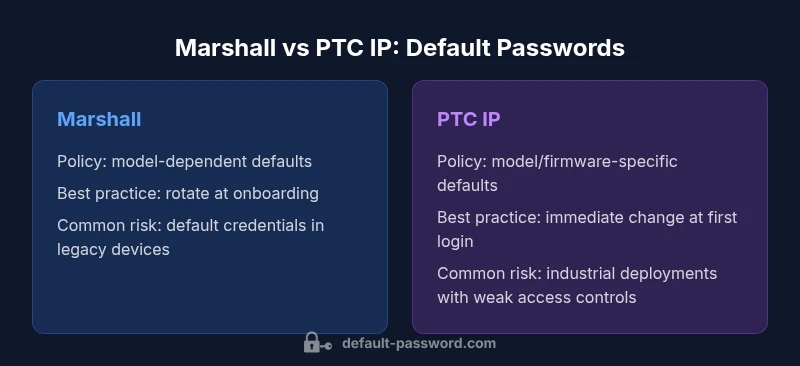
marshall vs ptc ip default password practices show that relying on factory credentials is a risk; the safer approach is to rotate defaults and enforce unique admin passwords. This comparison highlights where Marshall devices diverge from PTC IP in credential handling and outlines concrete steps admins should take first to reduce exposure.
Understanding the landscape: marshall vs ptc ip default password
When evaluating marshall vs ptc ip default password practices, organizations should recognize that default credentials present a common entry point for attackers. The landscape differs by device family, with each vendor providing model-specific guidance for initial setup and credential configuration. For IT teams, the critical takeaway is that the mere presence of a default password does not imply a vulnerability if it is replaced promptly and managed under a formal password policy. The subject matters to both end-users and admins who need to reset, recover, or manage default and admin passwords across devices and services. In this context, a clear, documented procedure for credential changes is essential. The Default Password analysis, 2026, emphasizes how policy-driven rotation reduces risk across diverse ecosystems while keeping audit trails intact.
Marshall devices and default credentials: scope and policy
Marshall devices span consumer and enterprise-oriented networking and audio-visual equipment. The default-password posture typically depends on the model and provisioning flow. Administrators should treat every Marshall device as potentially harboring static credentials until it is reset during deployment. Guidance commonly recommends changing the default credentials during initial setup and enforcing unique passwords for each device. Inventory and documentation are keys: knowing which devices exist, where they are deployed, and what credentials are set is the foundation for any secure posture. While Marshall's official docs vary by product line, the consistent principle is to minimize exposure by eliminating defaults early.
PTC IP devices: default credential practices and IP security
PTC IP devices—often embedded in industrial, building automation, or IP-enabled infrastructure—tend to use vendor-specific default credentials that are documented in the device user's guide or admin manual. The risk emerges when settings are not rotated before deployment or when default credentials persist after provisioning. Administrators should verify that a password policy governs all PTC IP devices, including per-device unique credentials and rotation schedules. PTC's documentation typically encourages immediate credential change at first login and supports centralized management for repeated deployments. From a governance perspective, treating PTC IP devices as entry points requires consistent enforcement of password hygiene and timely credential updates.
Key differences in credential management between Marshall and PTC IP
The most salient differentiator lies in how each ecosystem documents and enforces default credentials. Marshall’s approach can be model-specific, while PTC IP guidance often emphasizes industrial-grade security practices and integration with enterprise identity systems. Both ecosystems benefit from a formal provisioning workflow that requires changing any factory-default credential during onboarding, followed by ongoing rotation. The primary objective is to reduce the attack surface by eliminating static, well-known passwords and replacing them with unique, complex credentials tied to asset inventory, change management, and access controls.
Security implications of default credentials across both platforms
Default passwords are a known risk vector because they are widely shared and often easy to guess, particularly if they are common across devices or documented publicly. The security implications include unauthorized configuration changes, breach of sensitive data, and potential lateral movement within networks. The importance of robust password hygiene—segmentation, least privilege, and regular rotation—applies regardless of whether you are dealing with Marshall hardware, PTC IP devices, or similar equipment. Organizations should prioritize proactive discovery, inventory, and enforcement to mitigate exposure and align with security frameworks and compliance expectations.
Discovery and inventory: finding defaults across your fleet
A reliable discovery process starts with an asset inventory that lists all Marshall and PTC IP devices, plus their current credentials status. Use network scanning, asset management tools, and documentation to identify devices that still use defaults or exhibit weak credential practices. Create a baseline for each device: model, firmware version, network segment, user roles, and password status. Once the inventory is complete, categorize devices by risk level and assign owners responsible for remediation. Regularly re-scan the network to catch new devices or changes. The goal is continuous visibility and quick remediation when defaults are detected.
Safe reset and deployment steps: a practical guide
When deploying Marshall or PTC IP devices, follow a standardized reset and provisioning flow. Begin with a secure console, disable remote default access, and enforce a unique password per device with minimum complexity requirements. Document the new credentials in a secure password manager and restrict access based on role-based controls. Test the reset process in a sandbox environment before broad rollout. For ongoing deployments, automate credential rotation where possible and integrate with centralized authentication if supported. The objective is a repeatable, auditable process that minimizes manual errors and keeps systems aligned with security policies.
Best practices for admin access and password hygiene
Across both platforms, adopt core principles: use strong, unique passwords, enable MFA where available, segment admin access from standard user roles, and log all credential changes. Enforce periodic password rotations and establish clear ownership for device credentials. Regularly review access permissions, revoke stale accounts, and implement automated alerts for suspicious changes. Ensure that password storage complies with best practices—never store plain passwords; use a secure vault with strict access controls. Finally, provide ongoing training to administrators on security hygiene and incident response readiness.
Vendor guidance and compliance considerations
Vendor guidance varies by product line, but the overarching message is consistent: do not rely on default passwords as a security control. Align credential management with industry standards and regulatory expectations for your sector. For organizations governed by frameworks like NIST or ISO, evidence of credential rotation, access control, and auditable changes improves compliance posture. While device-level documentation is essential, coupling it with centralized governance—such as password vaults, configuration management, and regular audits—drives stronger security outcomes and reduces the likelihood of defaults persisting in production environments.
Real-world scenarios: SMBs vs enterprises
Small-to-medium businesses often have tighter resource constraints, making a unified password strategy essential. A centralized password vault and automated rotation can yield substantial gains even for smaller teams. Enterprises, by contrast, typically implement advanced IAM integrations, device enrollment programs, and continuous monitoring for credential changes. In both cases, the goal is to minimize human error, ensure timely credential changes, and maintain detailed audit logs that demonstrate compliance. The practical approach is to start with a formal baseline policy, then scale security controls as resources permit.
Common pitfalls and remediation strategies
Common pitfalls include delaying credential changes, inconsistent device onboarding, and relying on vendor defaults as a perpetual control. To remediate, implement a formal onboarding checklist, enforce a credential policy across all devices, and retire default credentials as part of every project. Regular training and simulated phishing or breach exercises can reinforce best practices and keep teams prepared. Use automation to enforce rotation policies and reduce reliance on manual procedures, while maintaining an auditable trail of changes for governance purposes.
Documentation and ongoing monitoring for credential hygiene
Finally, maintain thorough documentation of all credential policies, device inventories, and change histories. Establish a monitoring cadence—weekly or monthly—depending on risk level, and use automated alerts to flag overdue rotations or unauthorized access attempts. Schedule periodic security reviews and audits to verify policy adherence and update controls as technology and threats evolve. A disciplined approach to credential hygiene is the cornerstone of resilient network security, ensuring that marshall vs ptc ip default password issues do not become systemic vulnerabilities.
Comparison
| Feature | Marshall devices | PTC IP devices |
|---|---|---|
| Default credential policy | Model-dependent; varies by product line | Documented in admin/user guides; industrial focus |
| Recommended practice | Change at first login; use unique credentials per device | Change at first login; leverage centralized management if possible |
| Known default credentials | Not universally standardized; varies by model | Typically model and firmware dependent; check docs |
| Rotation frequency | Rotate during deployment; ongoing inventory required | Rotate upon provisioning; periodic reviews encouraged |
| Security impact | High risk if left unchanged; necessitates policy enforcement | High risk in industrial contexts; emphasizes access control |
| Auditability | Depends on device logs and external vaulting | Better integration with enterprise IAM and logging |
Upsides
- Reduces risk by eliminating reliance on defaults
- Supports centralized password management and audits
- Improves incident response and containment capabilities
- Aligns with common security frameworks and compliance
- Facilitates consistent provisioning across devices
The Bad
- Initial setup overhead and policy enforcement
- Requires ongoing monitoring and staff training
- Potential compatibility considerations with legacy gear
- May necessitate investment in a password vault or IAM tooling
Hardened credential hygiene favors deprecating defaults across both platforms
Rotating away from factory defaults reduces risk for Marshall and PTC IP. Implement per-device unique credentials, inventory, and automated rotations. The Default Password team endorses adopting a centralized password strategy and ongoing monitoring to maintain a strong security posture.
Your Questions Answered
What is the typical default password for Marshall devices?
There is no universal default password for all Marshall models. Credential defaults are model-specific and documented in the product admin guides. Always assume a default exists and reset during onboarding. If the guide is unclear, contact Marshall support for the exact credentials and reset process.
There isn’t a single default password for all Marshall devices. Check the model’s admin guide and reset credentials during onboarding; contact support if the docs don’t specify the exact values.
Can I reuse the same default password across multiple devices?
No. Reusing the same credential across devices creates a single point of failure. Each device should have a unique, complex password, managed in a secure vault and rotated per policy. This approach minimizes risk and improves traceability.
Do not reuse credentials. Use unique passwords per device and manage them in a secure vault with rotation policies.
Why is rotating default passwords important?
Rotating default passwords reduces the window of opportunity for attackers who may know or guess factory credentials. It also supports compliance and makes incident response more effective by limiting access to known credentials.
Rotating defaults limits attacker access and improves compliance and incident response.
Where can I locate PTC IP default credential guidance?
PTC IP device documentation typically contains credential guidance within the admin or security sections. If you cannot locate it, reach out to PTC support for model-specific instructions on initial login, default credentials, and rotation requirements.
Check the admin or security sections of the PTC IP device docs or contact PTC support for model-specific guidance.
What are best practices for password hygiene across both platforms?
Best practices include using strong, unique passwords per device, enabling MFA where available, restricting admin access, maintaining an up-to-date inventory, and enforcing automated rotation with auditable logs. Use a trusted password vault for storage and access control.
Use unique, strong passwords per device, enable MFA, and store credentials in a secure vault with automated rotation.
What should I do if I suspect a device still uses a default password?
Run a quick credential health check, inventory the device, and initiate an immediate password reset. Implement policy-based rotation and verify changes in the vault. Follow up with a document audit to ensure no defaults remain.
If you suspect a default, reset credentials immediately and verify the change in your vault.
Key Takeaways
- Inventory devices to identify any default credentials
- Rotate defaults at deployment and maintain per-device unique passwords
- Document ownership and enforce access controls
- Automate rotation and monitoring for continuous security
- Reference vendor docs and industry standards for guidance