Most common WordPress admin passwords: risks and remedies
Discover why the most common WordPress admin passwords expose sites to risk and learn practical remediation—strong passwords, password managers, and MFA—to harden admin access in 2026.

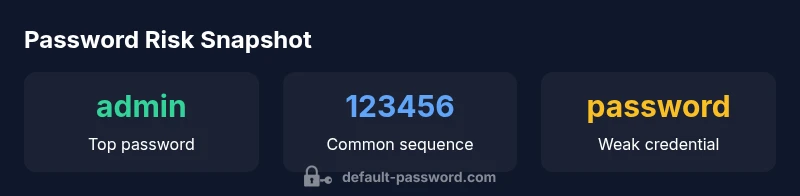
The most common WordPress admin passwords are simple, easily guessable terms and default credentials that attackers routinely target. In practice, admins often rely on words like 'admin' or 'password', or predictable sequences such as '123456', sometimes using factory defaults. These choices dramatically increase the risk of brute-force and credential-stuffing attacks, compromising sites, plugins, and hosting environments. A rapid remediation is to enforce strong, unique passwords and enable MFA.
Why the issue matters
According to Default Password, the phrase most common wordpress admin passwords is more than a trivia line—it's a concrete signal about risk. Admin accounts sit at the frontline of a WordPress site's security model, and weak credentials create a direct doorway for attackers. In 2026, threat actors continue to leverage these flaws to gain initial access, often followed by plugin abuse, cron job manipulation, or data exfiltration. The impact isn't isolated to a single site; compromised admin credentials can lead to lateral movement across a hosting environment, undermining backups, logs, and user management. For end-users and IT admins, recognizing that weak passwords are a recurring vulnerability is the first step toward instituting stronger governance and technical controls.
What makes a password 'most common' on WordPress
A password becomes part of the list of the most common wordpress admin passwords when it combines three patterns: brevity, predictability, and reuse. Short, dictionary-based words like admin or password are favored because they require minimal guesswork. Sequences such as 123456 or common variations like admin123 also rank highly in breach datasets. Combined with default usernames (such as the legacy admin account) or ship-included credentials, these choices create a predictable attack surface. Good password hygiene requires length (12+ characters), diversity (a mix of letters, numbers, and symbols), and uniqueness per site to reduce cross-site risk.
How attackers exploit weak passwords against WordPress
Attackers deploy rapid-fire brute-force tools and credential-stuffing techniques to test common usernames and passwords against the WordPress login page. If a weak password coexists with exposed admin access, a single compromised account can grant administrative control, enabling plugin installation, theme changes, or data access. Attackers may also exploit weak passwords to bypass two-factor authentication if MFA is not enforced or implemented correctly. The result is not just downtime; it can be a long-term trust and reputational damage for site owners and their users.
Practical remediation steps you can implement today
To move from risk to resilience, start with a policy and a practical implementation plan. First, force the use of long, unique passwords for all admin accounts and encourage or require password changes on a schedule. Next, deploy a password manager to avoid reuse and simplify rotation. Third, enable MFA (prefer hardware security keys or TOTP-based apps) and enforce it for all admins. Fourth, rename or disable the default admin user and limit login attempts at the server or application level. Finally, monitor login activity and implement rate limiting or WAF rules to block repeated failed attempts.
How to audit and enforce password security across a WordPress site
Auditing should be routine, not a one-off effort. Start by inventorying admin accounts, confirming MFA status, and verifying that password policies align with organizational standards. Use automated checks or a security plugin to flag weak passwords or password reuse. Establish governance for onboarding/offboarding administrators, enforce password changes on critical roles, and document procedures for incident response. Regular audits help ensure that the site does not drift back toward insecure defaults.
Password issues and mitigations for WordPress admin access
| Aspect | Issue/Pattern | Recommendation |
|---|---|---|
| Weak admin password | Common words like admin/password/123456 | Use a unique, long password per site; store in a password manager |
| Default credentials | Factory or shipping defaults | Change credentials during initial setup; disable default user 1 |
| Password reuse | Same password across multiple sites | Use a password manager; enable MFA; rotate passwords |
| Lack of MFA | No multi-factor authentication | Enable MFA (TOTP, hardware key) and enforce it for admin accounts |
| Brute-force exposure | Public exposure of login page | Implement login rate limiting; disable XML-RPC if unused |
Your Questions Answered
What counts as the most common WordPress admin passwords?
Most common WordPress admin passwords are simple, predictable terms and default credentials. Words like 'admin' or 'password' and sequences such as '123456' appear frequently in breach data and should be avoided. A strong password policy dramatically reduces risk.
Common WordPress admin passwords are simple and predictable; avoid them with a strong policy and MFA.
Why are these passwords a problem for WordPress?
Weak admin passwords create an easy entry point for attackers who can then move to plugins, themes, or data access. On WordPress, compromised admin accounts can compromise the entire site and its users.
Weak passwords give attackers easy entry to your WordPress admin. MFA and strong passwords reduce this risk.
How can I check if my WordPress admin password is weak?
Use a security audit or plugin that analyzes password strength and checks for reuse across sites. Ensure MFA is enabled for all admin accounts and verify that default accounts are removed or renamed.
Run a password strength check and confirm MFA is on for all admins.
What steps should I take to fix weak passwords?
Replace weak passwords with long, unique strings, enable a password manager, rotate credentials, and enforce MFA. Also disable default admin accounts and log all login attempts for monitoring.
Replace weak passwords with strong ones, enable MFA, and restrict login attempts.
Is MFA enough to secure WordPress login?
MFA dramatically strengthens security but should be part of a layered approach. Combine MFA with strong passwords, account governance, and monitoring to reduce risk from phishing and credential theft.
MFA is essential, but combine it with strong passwords and monitoring for best results.
How often should I audit WordPress password security?
Run password and access reviews quarterly or after staff changes. Maintain an incident response process and keep documentation of password policies updated.
Audit password security regularly, especially after admin changes.
“"Security hinges on password hygiene; for WordPress sites, pairing unique passwords with MFA is essential."”
Key Takeaways
- Enforce long, unique passwords for all admin accounts
- Enable MFA to stop credential-stuffing attacks
- Eliminate default usernames and credentials
- Limit login attempts and monitor for suspicious activity
- Use a password manager to reduce reuse and simplify rotation