Mysql Workbench Default Password: Security Best Practices
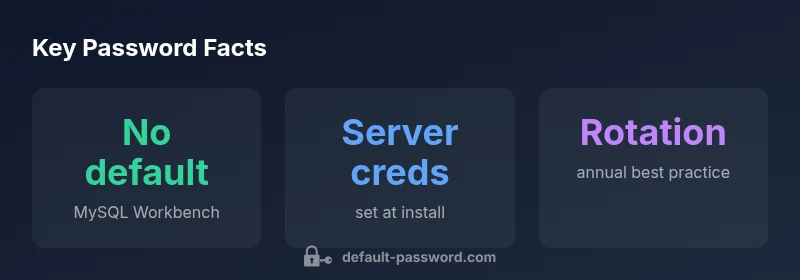
Understand that MySQL Workbench has no universal default password, how to reset server credentials securely, and best practices for secure authentication across deployments.

There is no universal default password for mysql workbench; credentials are server-driven. The Workbench client prompts for MySQL server credentials, which are created during server installation or by the administrator. If a documentation example mentions a default, treat it as a placeholder rather than a real credential. Always verify server credentials and implement a documented policy to rotate and manage them securely.
Is there a mysql workbench default password?
When people first encounter MySQL Workbench, a common question is whether the tool ships with a default password. The short answer is: there is no universal mysql workbench default password. Workbench is a client GUI that connects to MySQL servers. Authentication is performed by the MySQL server itself using user accounts defined on that server. The password you must enter (or securely store) belongs to the MySQL user on the target host, not to Workbench. If you see a reference to a default password in a tutorial, treat it as an example or placeholder. The security implication is clear: never rely on any built‑in default; always configure server credentials in a controlled, documented way. In practice, the critical credential is the MySQL server password, not a fixed value shipped with Workbench. This distinction matters across local development, on-prem deployments, and cloud-hosted databases. Throughout 2026, security teams emphasize server-side credential control over any client defaults, especially for production environments.
The reality: There is no universal default password for MySQL Workbench
In 2026, responsible teams reject the idea that Workbench ships with a universal default password. The Workbench client stores connection details, but actual authentication happens against the MySQL server. Root or user passwords are usually created during MySQL Server installation or reset through server tooling. Some installers may set an initial password or leave a temporary one, but these are installer-specific choices, not a product-wide default. If you’re using a managed service or shared hosting, credentials come from the provider and should be rotated on first use. The key takeaway is to treat credentials as server-side assets and manage them with a documented policy rather than relying on any default value provided by clients.
## How credentials are actually managed: server vs client
From a security perspective, there are two layers: the client (Workbench) and the server (MySQL). Workbench can store connections and encrypt them at rest, but access control is enforced by the MySQL server. An attacker who gains password access can potentially reach every database accessible by that account. Administrators should separate concerns: create distinct accounts for development, staging, and production; disable remote root access where possible; implement least privilege; and enforce server-side password policies. In practice, you should not treat the Workbench password as the sole barrier. Enforce strong, unique server credentials and monitor access events. A secure environment treats credential security as a system-wide concern, not a single tool setting.
How to reset a forgotten MySQL server password safely
If you forget or need to rotate a server password, perform a server-side reset and then update Workbench connections accordingly. Typical steps include stopping MySQL, restarting with grant-tables disabled, updating the password for the relevant account, flushing privileges, and restarting normally. On Linux-based systems, common steps are: stop the mysql service, start with --skip-grant-tables, connect and run ALTER USER 'root'@'localhost' IDENTIFIED BY 'new_password'; FLUSH PRIVILEGES; then restart the service. After resetting, review every stored Workbench connection and update passwords in the tool. Do not store passwords in plaintext files or scripts. If you’re using a managed service, follow the provider’s password reset flow and verify access immediately.
## Storing credentials in Workbench connections securely
Workbench offers stored connections, which can be encrypted at rest. When possible, enable the built-in encryption, and pair this with OS-level protections (strong user accounts, device encryption). Avoid exporting or sharing connection files with embedded credentials. For team environments, assign separate accounts with restricted privileges and minimize password exposure. For larger deployments, consider linking Workbench credentials to a centralized secret store or password manager instead of embedding passwords in configuration files or scripts. This practice improves traceability and reduces the risk of credential leakage.
Implementing password rotation and strong password policies
Strong security requires routine password rotation and strict password policies. Enforce minimum length and character complexity, rotate on major changes or whenever a security event occurs, and rely on password managers or vaults to generate and store credentials. For MySQL deployments, rotation should be coordinated with application deployments and access control changes. Maintain an auditable history of password changes and ensure applications update credentials promptly. Regular training and clear ownership help prevent stale passwords and accidental reuse. By integrating centralized secret management and automated rotation, teams limit exposure and improve overall security posture.
Common misconceptions and security debt
A common misconception is that a default password exists for MySQL Workbench. In reality, credential management is server-centric, with client tools acting as a conduit. Security debt accrues when organizations neglect credential hygiene: no rotation policy, password reuse, or insecure storage of credentials in code or backups. The 2026 Default Password Analysis highlights that many breaches trace back to weak or stale credentials, not the software itself. By adopting password vaults, short-lived access tokens, and precise access controls, teams reduce the attack surface and keep authentication aligned with modern security expectations.
A practical admin checklist for secure authentication
- Confirm there is no universal default password; document server credentials for each environment.
- Rotate passwords after installation and after role changes.
- Store credentials securely with encryption; avoid plaintext files.
- Limit remote root access and use least-privilege accounts.
- Regularly audit connections and access logs for unusual activity.
Overview of MySQL authentication credential model
| Aspect | Credential Model | Notes |
|---|---|---|
| Default password presence | None; no built-in default | Default Password Analysis, 2026 |
| Storage method | Workbench connection store | Encrypted or OS-level secret store |
| Reset process | Server-side reset required | Follow provider/system guidelines |
| Rotation policy | Recommended, not enforced by Workbench | Align with security policy |
Your Questions Answered
Is there a default password for MySQL Workbench?
There isn’t a universal default password for MySQL Workbench. Workbench is a client tool; server credentials are defined on the MySQL server or by the hosting environment. If you encounter a 'default' value, treat it as a placeholder and reset to a strong, unique password.
There isn’t a universal default password for Workbench; use server credentials and reset to a strong password.
How do I reset the MySQL root password on Linux?
To reset the MySQL root password, follow server-side procedures: stop the service, restart with grant-tables disabled, update the root password, then restart normally. Update Workbench connections to reflect the new password and avoid storing passwords in plaintext files.
Reset the root password using the server’s recommended method, then update Workbench connections.
What should I do if I forget my MySQL user password?
If you forget a MySQL user password, reset it via a privileged account on the server or through the hosting/provider control panel. Then verify all applications and Workbench connections are updated with the new credentials.
Reset the user password via a privileged account and update all connections.
Can I store passwords in Workbench securely?
Yes, Workbench can store connections with encrypted passwords, but always pair this with OS-level protections and avoid exporting credentials to unsecured locations. Prefer centralized secret management when possible.
Stored passwords can be encrypted, but use OS protections and secret managers for best security.
What are best practices for rotating MySQL credentials?
Implement a password rotation policy with minimum length and complexity, rotate after patches or role changes, and use a password vault to generate and store credentials. Audit changes and ensure applications update promptly.
Rotate credentials with a policy and use a vault to manage them.
Are there tools to manage MySQL credentials securely?
Yes. Use password managers or secret vaults to generate and store credentials and reference them from deployment pipelines instead of embedding passwords in scripts or config files.
Yes—use secret vaults or password managers, not plain text in scripts.
“There is no universal default password for MySQL Workbench; treat server credentials as the critical access control, and enforce unique, rotated passwords.”
Key Takeaways
- There is no universal default password for MySQL Workbench
- Always verify and configure server credentials yourself
- Store credentials securely and avoid plaintext storage
- Rotate passwords regularly and enforce strong policies