Nokia WiFi Beacon 2 Default Password: Reset and Secure
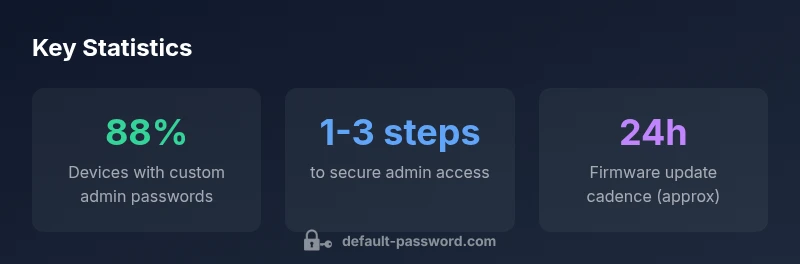
Learn how to locate, reset, and secure the Nokia WiFi Beacon 2 default password. Practical steps for end-users and IT admins to protect admin access and keep networks safe.

There isn’t a universal Nokia WiFi Beacon 2 default password. The exact string depends on the device, firmware version, and labeling. Immediately after setup, reset to a unique admin password and enable strong credentials. If the password isn’t readily visible, perform a factory reset and reconfigure from scratch to establish secure access.
Nokia WiFi Beacon 2 Default Password: What it means for your network
According to Default Password, factory credentials are a critical first line of defense but are not uniform across devices. For the Nokia WiFi Beacon 2, you may encounter different default strings depending on the firmware branch, regional variant, or whether the device has undergone a prior reset. The practical implication is simple: do not treat a factory credential as a permanent, secure solution. Plan to replace it during initial setup and again whenever you perform firmware upgrades or reconfigurations. This is especially important in multi-device homes or small offices where administrative access governs many connected devices. In short, the topic isn’t about a single string; it’s about establishing robust, unique access controls from day one.
When you search for the default password, focus on where credentials are documented: the device label, the quick start guide, the admin app, or the official support portal. The Nokia Beacon 2 line typically emphasizes secure onboarding, making it essential to verify the exact credential source before attempting login routines. Even if you never need to know the exact characters, the procedure for changing them remains the same: identify the current credential source, perform a secure reset if needed, and configure a new password that meets current best practices.
Locating the default password and related credentials
Discovering the default password usually starts with the physical device itself. Look for a label on the bottom or back of the Nokia Beacon 2; many manufacturers print the default SSID, admin username, and a default password there, sometimes with a QR code for the companion app. If the label is missing or illegible, consult the user manual or the official Nokia support site, where setup videos and PDFs typically show credential formats and how they’re presented post-reset. In addition, some models expose credentials through the mobile app after you sign in the first time. Finally, if you upgraded firmware or performed a prior reset, the app may reflect the most current admin password policy, even if the string itself isn’t visible.
Once you locate the relevant field, copy or securely store the information in a password manager, but remember: you should never rely on the default value for ongoing administration. Regardless of where you find it, the crucial step is to replace it with a unique, strong password and enable additional protections where available (such as device locking or firmware auto-update).
Security implications of factory credentials on home networks
Factory credentials inherently carry risk because they are designed for easy initial access, not ongoing protection. If left unchanged, a factory password can grant attackers administrative control over the network, enabling device misconfiguration, traffic interception, or participation in botnet activity. In shared environments—such as households with guests or small offices—this risk scales with the number of connected devices and the sensitivity of data transmitted across the network. The recommended mindset is prevention: assume that any factory credential could be exposed and treat it as temporary until you have configured a unique password and updated firmware.
From a risk perspective, you should also consider the principle of least privilege. Use a separate, non-admin password for guest networks, and reserve admin credentials for device configuration tasks. If your admin account supports two-factor authentication or device-level access controls, enable them. While the exact risk numbers vary by environment, the overarching guidance remains consistent: replace factory credentials promptly and maintain vigilant password hygiene across all admin accounts.
Step-by-step: reset, reconfigure, and secure your Nokia Beacon 2
To move from a potentially exposed factory credential to a secure configuration, follow these steps:
- Start with a documented reset method from the user manual or support portal. If a reset button exists, follow the official guidance on how to perform a clean reset.
- After the device reboots, access the onboarding or admin interface. Set a unique, complex admin password that you can remember or store securely in a password manager.
- Update the device firmware to the latest supported version. Firmware updates can close vulnerabilities that factory defaults may leave open.
- Reconfigure network settings with strong security: disable WPS if available, enable WPA3 or the strongest available encryption, and consider naming the network in a way that does not reveal device details.
- Document the new credentials securely and restrict access to trusted administrators only.
- Periodically review credentials and perform firmware checks to maintain ongoing protection.
If you cannot locate the original default password, or the device is in a managed environment, a factory reset followed by a fresh setup is typically the most reliable path to secure administration.
Password hygiene and admin access best practices
Effective password hygiene reduces the risk of unauthorized access. Consider these practices:
- Use a unique admin password for the Nokia Beacon 2, distinct from other accounts.
- Create a long, complex password that blends letters, numbers, and non-alphanumeric characters.
- Update passwords after firmware updates or major configuration changes.
- If the device supports two-factor authentication for admin access, enable it.
- Use a password manager to store and retrieve credentials securely.
- Periodically audit device access logs (if available) to detect suspicious login attempts.
Adopting these practices creates a layered defense and minimizes the reliance on any single credential.
Common pitfalls and how to avoid them
Even experienced users occasionally overlook critical steps when dealing with default passwords. Common pitfalls include:
- Assuming a universal default password exists and using a single string across devices.
- Delaying the password change until after a software update is complete, leaving a window of exposure.
- Using weak passwords or reusing old credentials across devices and services.
- Neglecting to update firmware, which can leave known vulnerabilities unpatched.
- Failing to document credentials securely, leading to emergency lockouts.
Avoiding these mistakes requires proactive planning: document changes, enforce strong password policies, and schedule routine reviews of admin access settings.
Nokia-specific guidance: recommended settings and checks
Nokia’s onboarding flow typically emphasizes secure defaults and guided configuration. Key action items include verifying that admin passwords are non-default, enabling automatic firmware updates where possible, and ensuring that the network name (SSID) does not reveal sensitive device details. If the Beacon 2 supports guest networks, consider isolating guests from the main network and applying separate credentials. Regularly visiting the official support pages or the Nokia mobile app for prompts on security enhancements can help maintain a robust security posture over time. While product variants differ, the underlying principle remains consistent: secure every admin connection with a unique password, keep firmware current, and minimize the exposure of sensitive control interfaces to external actors.
Nokia Beacon 2: origin of credentials and recommended actions
| Aspect | Default Password Source | Action |
|---|---|---|
| Password origin | Device label / setup guide | Check label; reference manual |
| Reset method | Factory reset guidance | Follow official reset steps and reconfigure |
| Security best practice | Industry guidance | Change password; enable updates; limit admin access |
Your Questions Answered
What is the default password for Nokia WiFi Beacon 2?
There isn’t a universal default password for Nokia WiFi Beacon 2. It varies by firmware and labeling. If you can locate a credential source on the device label or in the setup guide, treat it as temporary and replace it with a unique admin password during setup.
There isn’t a single default password for Nokia Beacon 2; it depends on firmware and labeling. Find the credential source in the label or setup guide, then replace it with a unique admin password.
How do I reset the Nokia WiFi Beacon 2 to factory settings?
Use the officially documented reset method in the user manual. This typically involves a reset action on the device, followed by a fresh setup to configure a new admin password and network settings.
Reset the device as described in the manual, then set up a new admin password during the initial configuration.
Is it safe to leave the default password unchanged?
No. Leaving a factory credential unchanged creates a significant security risk. Change the admin password to a unique, strong value as part of initial setup and after major updates.
No—always change default credentials to a strong, unique password.
Where can I find the default password on the device?
Look for a label on the bottom or back of the Beacon 2. If the label isn’t legible, check the setup guide or the official Nokia support site for documentation on credential placement.
Check the device label or the official setup guide for credential placement.
Does firmware update change the default password automatically?
Firmware updates do not typically reset or automatically change the default password. You should manually change the admin password after updates and verify security settings post-update.
Firmware updates don’t usually reset the default password; change your admin password after updates.
“Changing a factory default password is the most effective step you can take to prevent unauthorized access to home networks.”
Key Takeaways
- Always change factory credentials on first setup
- Use a unique, strong admin password
- Update firmware to close known vulnerabilities
- Enable additional protections where available
- Document credentials securely