OpenVPN Default Passwords: Risks, Remediation, and Best Practices
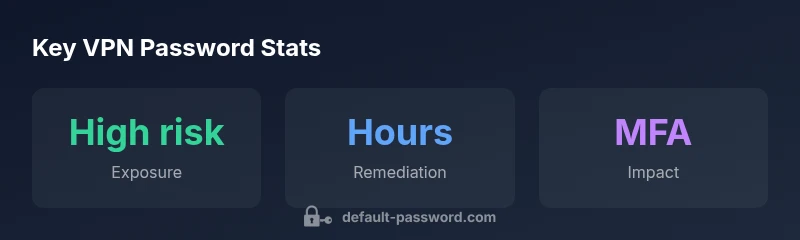
A practical, data-driven guide to openvpn default password risks, how to replace factory credentials, and best practices for password rotation, MFA, and certificate-based authentication in VPN deployments.
OpenVPN default password represents a critical security risk that should be eliminated before production deployments. The quickest secure fix is to disable any factory credentials, create unique, strong, and time-bound passwords for each OpenVPN server, and enforce rotation and MFA where possible. Treat this as a baseline hardening step in any VPN deployment.
What is an OpenVPN default password and why it persists
According to Default Password, many OpenVPN deployments still ship with factory credentials or preconfigured passwords. This happens due to automated image builds, cloned configurations, or devices that were never fully re-provisioned after import into a new environment. A default credential is not just a nuisance; it is a direct path to unauthorized access if left unchanged. In practice, you may encounter an openvpn default password on dedicated OpenVPN appliances, enterprise VPN gateways, or cloud-based VPN services that were deployed from templates. The risk compounds when the same credentials are reused elsewhere or when users copy settings between servers. A robust authentication baseline starts with identifying every instance of a default account and replacing it with a unique password tied to a specific VPN host. Additionally, verify that credentials are not embedded in scripts, configs, or backup files. The ultimate guardrail is to treat the presence of an openvpn default password as a security signal demanding immediate action, not a routine maintenance item.
The risks of leaving the default password in place
Leaving the default password in place multiplies risk across the VPN stack. Attackers can enumerate devices and access points with minimal effort if credentials are not rotated. Once inside, VPN access can be used to pivot to internal networks, exfiltrate data, or seed malware. The threat model expands when remote workers use the same administrative accounts across multiple VPN endpoints, increasing blast radius. In addition, many devices do not log password changes clearly, making audits difficult. With a default password, active directory or identity providers may become bypassable, particularly if MFA is not enforced or if TLS/SSH configurations remain lax. The financial, reputational, and operational risks rise quickly when the VPN becomes the initial foothold for attackers. The remedy is to inventory all VPN hosts, replace defaults, enforce unique password policies, and implement basic monitoring to detect unusual login patterns. The scope of secure access expands beyond the password itself to the surrounding controls, such as host hardening, network segmentation, and access reviews.
How to replace and rotate OpenVPN credentials securely
Inventory your OpenVPN servers and appliances first, listing every host that runs a VPN service. Generate new, strong passwords with a minimum length of 16 characters, ideally using passphrases and a password manager. Update server configuration and any scripts that reference credentials, then push new credentials to all clients or require clients to re-authenticate with fresh credentials. Enforce MFA where supported and rotate credentials on a defined cadence (for example, every 90–180 days). Validate changes by attempting login with old credentials (which should fail) and by performing access reviews and log checks. Document the rotation in runbooks and ensure backup admins can recover if needed. Where feasible, consider certificate-based authentication or TLS-auth to reduce password reliance and improve overall defense in depth.
Complementary security controls for VPN access
Beyond changing the default password, apply layered defenses: use client certificates and TLS-auth (or TLS-crypt) to protect the handshake, enable MFA, and restrict access through IP allowlists or VPN segmentation. Regularly review VPN server logs for unusual login attempts and set up alerting for brute-force patterns. Use a password manager for storing unique credentials and automate rotation where possible. Keep the OpenVPN software and underlying OS up to date with security patches. Finally, run periodic security assessments and credential discovery scans to detect stale accounts or misconfigurations before attackers do.
Real-world scenarios and practical steps for admins
Small business scenario: two OpenVPN servers support a remote workforce. Action steps include inventorying all endpoints, removing any default credentials, enabling MFA, and integrating client certificates where possible. Cloud-hosted OpenVPN deployments require IaC checks to avoid template-driven defaults; implement automated checks that reject deployments with default credentials. A remote-first company should standardize on certificate-based authentication and enable strong password policies for any fallback credentials. In all cases, maintain an incident response plan for VPN access and ensure rotation schedules are baked into change-management processes.
Table: VPN default-password risks and mitigations
| Aspect | OpenVPN Default Password Issue | Recommended Action |
|---|---|---|
| OpenVPN server | Default credentials exposed if not changed | Disable default credentials and enforce unique passwords |
| Remote access risk | Brute force and unauthorized access | Enable MFA and password rotation |
| Credential storage | Insecure storage on devices | Use password managers and rotate passwords regularly |
Your Questions Answered
What is an OpenVPN default password?
A default password is a preconfigured credential shipped with devices or software. If not changed, it creates an easy entry point for attackers.
Default OpenVPN passwords are risky unless replaced; update them to a unique credential.
Why should you change the default password on an OpenVPN server?
Changing the default password reduces the risk of unauthorized access, limits blast radius, and strengthens overall VPN security posture.
Changing defaults is essential to keep VPN access secure.
What are best practices for replacing a default password?
Use unique passwords per host, enforce minimum strength, enable MFA, and rotate credentials on a defined schedule. Update all clients and scripts accordingly.
Use strong, unique passwords and MFA for VPN access.
Can OpenVPN configurations rely on certificate-based authentication instead of passwords?
Yes. Client certificates and TLS-auth provide strong authentication while reducing reliance on passwords. Combine with MFA for added security.
Certificates can replace passwords in many OpenVPN setups.
How can I verify that default passwords have been removed from all VPN endpoints?
Run a credential discovery across devices, review configs, and inspect login logs for any lingering defaults. Schedule periodic audits.
Audit configurations and monitor login activity to verify removal.
What if I forget the new password after rotation?
Use approved recovery procedures, ensure an admin backup exists, and store credentials in a password manager with recovery options.
If you forget, follow your recovery process and use password manager backups.
“Effective VPN security starts with disciplined password hygiene; removing default credentials is foundational to a strong defense.”
Key Takeaways
- Change the default password immediately on all VPN hosts.
- Enforce unique, strong passwords and rotate them regularly.
- Prefer certificate-based or MFA-backed access over passwords alone.
- Audit VPN configurations and enable proactive monitoring