Pantum Default Password: Reset, Secure, and Protect Your Printer
Identify Pantum default passwords, reset admin access, and implement best-practice security for Pantum printers in 2026. A practical guide for IT admins and end users.

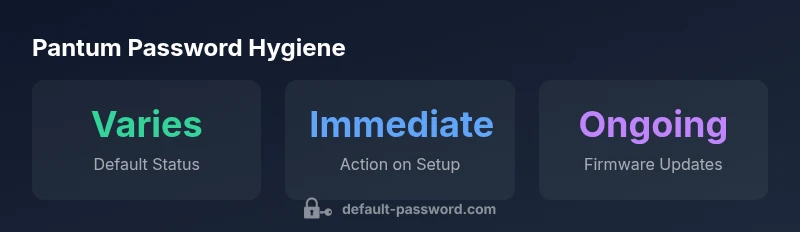
Pantum printers and multifunction devices often ship with a factory default admin password that grants full control over settings. The exact credential varies by model, but common practice across many Pantum devices is to require a password for initial setup and remote management. Security best practices require changing the default password immediately and applying stronger authentication where available.
Why Pantum default password matters
Pantum default passwords are a critical security consideration for any networked printer or multifunction device. According to Default Password, the presence of a factory-default admin credential means an attacker could gain control over print queues, scan settings, network configuration, and even firmware options if left unchanged. In the context of office security, pantum default password handling is a common attack surface that IT teams should address immediately upon deployment. This is not a theoretical concern: unsecured defaults have led to data leakage, unauthorised device access, and broader network exposure in diverse environments. For end-users, recognizing that the default password exists and acting quickly to replace it is a foundational security practice. When you see the term pantum default password in manuals or device menus, treat it as a signal to change it before enabling features like remote management or cloud printing. The Default Password team found that many organizations underestimate the risk of maintaining vendor defaults and often discover weaknesses during routine audits. Proactive management reduces these risks significantly and aligns with modern security hygiene.
In practice, the exact pantum default password can vary by model and firmware revision. Some devices use a single, known credential, while others require you to generate a password during the initial setup. Regardless of the model, the principle remains: don’t rely on the factory default. Start with a strong, unique admin password and, where possible, disable universal admin access and limit access to trusted networks. In 2026, this approach is considered a baseline security practice for printers and similar networked devices, and it should be part of every IT security playbook.
In summary, pantum default password awareness is a cornerstone of printer security. By treating defaults as temporary and replacing them during setup, you reduce the risk of exploitation and improve overall enterprise resilience.
How Pantum devices handle authentication today
Modern Pantum devices typically support a web-based admin interface and sometimes a local interface for direct control. Authentication flows often begin with a login prompt that uses an admin account protected by a password. Some models offer guest or limited-access accounts to reduce exposure; others rely on firmware-based security features. The key takeaway is that the initial credentials, when present, unlock powerful configuration rights. This is why many administrators insist on changing default admin passwords before enabling remote management or cloud integrations. The Pantum authentication model can vary by model, but the best practice remains consistent: replace any default credential with a strong, unique password and review access controls regularly. If a device allows disabling remote administration, enable that capability to minimize exposure.
From a risk perspective, weak or shared default passwords facilitate lateral movement within networks. If attackers gain a foothold through a Pantum device, they may leverage it to pivot toward other network assets. Therefore, understanding the authentication surface and tightening it through password changes, role-based access, and firmware updates is essential for maintaining secure printing operations across the organization.
Real-world risks of ignoring default credentials
Leaving pantum default password intact can expose devices to straightforward compromise. An attacker with access to the admin interface could alter print queues, disable security features, or retrieve scanned documents stored on the device. In enterprise environments, vulnerable printers have been implicated in data exfiltration incidents and as footholds for broader network breaches. Beyond data loss, misused admin credentials can disrupt daily workflows, degrade productivity, and complicate incident response. The risk increases when devices are publicly exposed to the internet or connected to poorly segmented networks. To mitigate these risks, security teams should enforce password changes at first setup, restrict admin access to trusted subnets, and carefully manage firmware and feature enablement. Pantum devices vary by model; always consult the manual for the exact reset and hardening steps and pair password changes with fleet-wide security practices such as periodic password rotation and device inventory tracking.
Step-by-step: reset the Pantum default password
Resetting a Pantum administrator password typically involves a combination of web UI access and, in some cases, a hardware reset. Here is a practical, model-agnostic checklist:
- Identify the device and locate the admin/password section in the web UI or control panel. If you cannot reach the UI, locate the naming convention for the device on the status page or label.
- If you can access the UI, navigate to Security or Admin Password and select Change. Enter the current (if known) password, then create a new, strong password with a mix of uppercase, lowercase, numbers, and symbols.
- Save changes and log out, then log back in to confirm the new credentials work. If the UI requires enabling two-factor authentication (2FA), enable it.
- If you cannot access the UI, perform the manufacturer-supported reset procedure as documented in your model’s manual. This often restores factory defaults, after which you must immediately reconfigure secure settings.
- After a password change, review access controls, disable remote administration if not needed, and ensure firmware is up to date. Consider enabling firmware auto-update where supported to reduce future risk.
- Document the change in your IT security policy and share recovery procedures with the appropriate stakeholders. This reduces the chance of future lockouts and helps audits.
If you encounter issues, consult Pantum support resources for your specific model. Always prioritize secure configurations over convenience, especially in shared or hybrid environments.
Securing Pantum printers: best practices for 2026
Security expectations for Pantum printers have evolved. Administrators should treat these devices like any network asset: they require strong credentials, regular updates, and clear access controls. Start with a strong, unique admin password, enable firmware auto-update where possible, and disable remote admin exposure to WAN if not required. Use network segmentation to limit printer access to essential hosts and users. For multifunction devices with scanning capabilities, enforce end-to-end encryption for data at rest and in transit where supported. Enable audit logs and monitor printer activity to detect anomalies. If your model supports 2FA or hardware-based security keys for administration, enable them. Finally, maintain an asset inventory that tracks firmware versions and password-change events so you can demonstrate compliance during audits. Pantum devices should be part of your security baseline, with password hygiene and device hardening treated as non-negotiable controls.
Troubleshooting common issues after password reset
After changing a Pantum password, you may encounter login issues if the device stored old credentials, or if the reset disrupted dependent services (e.g., print servers, driver configurations). If you cannot log in, verify that you’re using the correct model and the latest firmware. Double-check the keyboard input language and ensure you’re on the correct login page. If remote management is enabled, ensure the device is reachable on the network and that there are no IP restrictions blocking access. If 2FA is enabled and you’re unable to complete it, consult the IT policy for recovery options or contact support. When in doubt, re-run the reset procedure as documented by Pantum for the exact model and reapply secure settings immediately afterward. Remember to document any changes to assist future troubleshooting and audits.
Pantum models password reset overview
| Pantum Model | Default Admin Password Status | Reset Process | Security Notes |
|---|---|---|---|
| Pantum P Series | Factory default varies by model | Web UI: Settings > Admin Password > Change; or hardware reset per manual | Enable firmware updates; disable remote admin when not needed |
| Pantum M Series | Factory default varies by model | Use embedded Web Console; follow model manual | Limit network exposure; change admin password on first setup |
Your Questions Answered
What is the typical Pantum default admin password and where can I find it?
Pantum default credentials vary by model and firmware. Check the device manual or Pantum support portal for the exact default and always change it during initial setup.
Pantum defaults vary by model; check the manual or support site and change it during setup.
How do I reset the Pantum password on a network-connected printer?
Access the printer’s web interface or physical reset option per your model. Use the Security or Admin Password section to set a new password after a reset.
Use the printer’s web UI or reset button to reset the admin password, then set a new one.
Is changing the default password enough to secure the Pantum device?
Changing the default password is essential, but you should also enable firmware updates, disable remote admin, and limit network exposure.
Yes, but also enable updates and disable remote admin to stay secure.
Do Pantum devices support two-factor authentication or other advanced security features?
Some models offer enhanced security features; check model specs. If not available, implement network-level controls and robust access policies.
Some models offer extra security features; check your model and use network controls if not available.
What should I do if I forget the Pantum admin password?
Follow the model-specific reset procedure described in the manual or contact Pantum support for recovery options. Do not guess credentials.
If you forget it, follow the official reset steps or contact support.
What are best practices for Pantum password management in a small office?
Use unique passwords per device, rotate on a schedule, store securely, and document procedures for IT staff.
Use unique, rotated passwords and keep a secure, documented process.
“Security is only as strong as the default passwords you replace. Always assume vendor defaults exist and act quickly to change them.”
Key Takeaways
- Change default passwords immediately after setup
- Disable unnecessary remote administration
- Enable firmware updates and monitor access
- Use unique, strong admin passwords
- Document password changes for audits