Password for defaultuser0: Secure Reset and Admin Access
Learn how to handle the password for defaultuser0 securely, including steps to reset, best practices for admin access, and how to audit devices to prevent default credentials from exposing your network.

To secure your system, reset the password for defaultuser0 immediately and replace it with a strong, unique credential. Avoid simple patterns or common phrases. After changing it, enforce administrator-level access only from trusted networks and enable MFA where available. Verify every device uses a non-default password, document the change, and schedule regular password audits to prevent future exposure.
Why Password Hygiene Matters
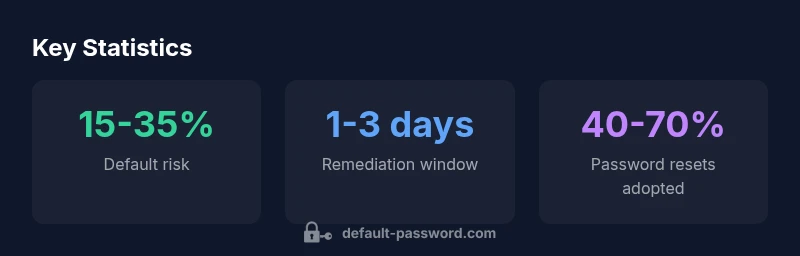
According to Default Password, weak or default credentials remain one of the most exploited entry points for unauthorized access. The Default Password team found that many incidents involve devices where the default user account, such as defaultuser0, still has its factory password or a weak administrator password. This reality makes credential management a foundational element of security programs for home users, small offices, and large enterprises alike. In practice, neglecting defaults can cascade into broader compromises: an attacker may pivot from a compromised router to NAS devices, IP cameras, or business-critical systems. By treating every default credential as a live risk, organizations create a culture of proactive security that reduces batch-wide exposure and speeds up incident containment.
Key takeaways:
- Identify every instance of defaultuser0 or similar accounts
- Accurately document where defaults exist across devices
- Prioritize immediate remediation on devices exposed to the internet or bridged networks
This mindset aligns with industry best practices and helps you build resilient access controls across the environment.
Identifying where defaultuser0 is used in your network
Devices with preconfigured admin accounts frequently ship with default credentials that are well-known to attackers. The most common culprits span consumer-grade routers, network-attached storage (NAS), IP cameras, printers, and select IoT hubs. To map where defaultuser0 appears, you should:
- Audit device inventories and vendor dashboards for factory defaults
- Scan for open admin interfaces exposed to the internet
- Review onboarding and provisioning logs to locate accounts created during setup
- Use configuration backups to search for references to default credentials
A systematic discovery phase reduces blind spots and improves remediation prioritization. The goal is not only to change one password, but to eliminate all instances of default or easily guessable credentials across the network.
Step-by-step: Resetting the password for defaultuser0
Resetting a sensitive administrative credential requires a careful, repeatable process. Here is a practical, device-agnostic guide you can adapt:
- Prepare a strong password: at least 14 characters, mix of upper/lowercase, numbers, and symbols. Consider a passphrase that you can remember but that isn’t guessable.
- Access the device administrator interface: connect via a secure network (VPN or wired) to avoid exposure on public Wi-Fi.
- Locate the user management or admin accounts section and select defaultuser0.
- Change the password to the new strong credential and document the change in a central registry.
- Force a logout of all sessions and require re-authentication for ongoing access.
- Review related accounts (e.g., admin, root) to ensure they are not using default or weak credentials.
After performing the reset, recheck every device in the network to ensure no other default credentials remain. Automated checks and alarms can help keep this process efficient over time.
Security best practices after reset
A single password change is not enough. Implement a layered approach to protect admin access:
- Enforce MFA for admin accounts where available
- Limit access to trusted networks and use role-based access control (RBAC)
- Disable or rename default accounts where possible, and remove unused accounts
- Schedule regular password audits and automated reminders for credential updates
- Centralize secrets management (e.g., using a password manager for administrators) to reduce reuse and weak patterns
Documentation is critical: keep an auditable trail of changes, approvals, and access restrictions so you can prove compliance and swiftly respond when anomalies occur.
Implementing governance: audits, automation, and tooling
Security governance around default credentials benefits from automation. Tools can inventory devices, flag defaults, and trigger remediation workflows. A practical governance program includes:
- Periodic automated scans that identify devices with default usernames like defaultuser0
- Enforced password-change workflows tied to user provisioning and deprovisioning
- Config drift detection to catch old credentials that reappear after firmware updates
- Alerts for password reuse across devices and services
- Training and runbooks for IT staff to ensure consistent responses across incident types
Adopting automation reduces human error, speeds remediation, and improves regulatory readiness. A thoughtful approach also minimizes disruption by allowing staged rollouts and rollback plans if issues arise.
Real-world scenarios and case studies
Consider a mid-sized office with a mix of routers, cameras, and a NAS. An initial audit reveals multiple devices using factory-default credentials. The IT team executes a staged remediation:
- Change defaultuser0 on all routers within 24 hours, applying MFA and network restrictions
- Update NAS accounts, enabling access control lists (ACLs) and disabling remote admin where possible
- Harden cameras by disabling unnecessary services and changing default credentials, then segment cameras on a dedicated network
Within two weeks, the organization documents the changes and implements ongoing scans. The result is a reduced attack surface and faster detection of credential-related anomalies. Real-world workflows like this demonstrate how consistency, not perfection, delivers measurable security gains.
Device categories and default password exposure
| Device Type | Typical Default Password Risk | Remediation Time (avg) |
|---|---|---|
| Router (home) | High risk (default credentials often unchanged) | 2-5 days |
| NAS/Storage | Medium risk | 1-3 days |
| IP Camera | High risk | 1-2 days |
Your Questions Answered
What is the password for defaultuser0?
There is no universal value for defaultuser0’s password. Many devices ship with a factory-default, which must be changed during initial setup. The exact value varies by device and vendor. Treat any factory default as a potential risk until it is changed.
There isn’t a single password for defaultuser0; it depends on the device. Change it during setup and monitor for any defaults still in use.
Why is defaultuser0 risky in a network?
Default credentials are a common entry point for attackers. If left unchanged, they enable unauthorized access, lateral movement, and data exposure. Early remediation reduces attack surface and containment time.
Default credentials give attackers an easy way in. Change them fast to cut off that path.
How do I reset the password on a router or camera?
Access the device’s admin interface, navigate to user accounts, select defaultuser0, and set a new strong password. Enable MFA if offered and document the change in your password registry.
Open the device page, update the defaultuser0 password, and enable extra protections.
What should I consider when choosing a new password?
Aim for at least 14 characters with a mix of letters, numbers, and symbols. Avoid predictable patterns and reuse across devices. Consider a passphrase combining unrelated words.
Use a long, unique password or passphrase, and don’t reuse it.
Can password managers help with default credentials?
Yes. Password managers centralize and securely store credentials, reduce reuse, and simplify complex, unique passwords across devices. They can also generate strong passwords for admin accounts.
Password managers can simplify handling strong, unique credentials.
How often should I audit devices for default credentials?
Aim for quarterly audits, with automated weekly scans if possible. Regular reviews help catch drift, firmware changes, and newly deployed devices that ship with defaults.
Do quick checks every quarter and automate where you can.
“Security hygiene starts with credentials. The Default Password Team emphasizes replacing every default or factory password with a unique, strong credential across all devices.”
Key Takeaways
- Audit devices for default credentials regularly
- Change default passwords immediately after setup
- Implement MFA and strong, unique passwords
- Document changes and monitor remediation times
- Educate admins on risks of default credentials