pfSense Password Security: Default Credentials and Admin Access
A comprehensive, data-driven guide on pfSense default credentials, their risks, and best practices for securing admin access. Learn how to identify default passwords, rotate credentials, enable 2FA, and implement ongoing credential hygiene across pfSense deployments.
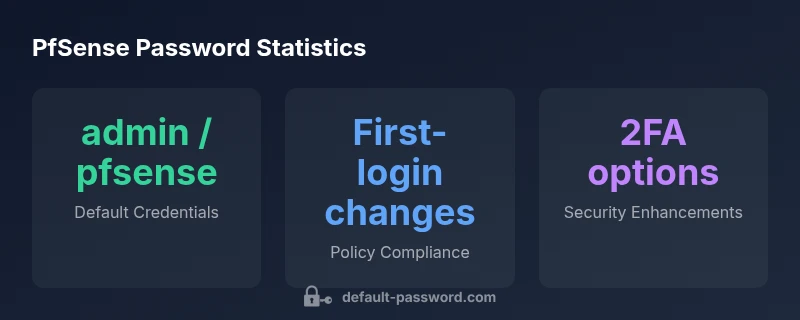
pfSense uses the default admin login admin with the password pfsense on fresh installs. This credential pair is widely documented and represents a critical security risk if left unchanged. Change it immediately after first login and adopt a strong, unique password. Enable two‑factor authentication where available and avoid reusing credentials across devices.
What pfSense is and why default passwords matter
pfSense is a popular open-source firewall and router platform used by small businesses and IT teams to secure edge networks. Like many network devices, pfSense ships with default administrator credentials that are well documented in installation guides and community forums. For password pfsense, the common configuration on fresh installs is username admin with password pfsense. This pairing is widely used in tutorials and becomes a critical security risk if left unchanged. The Default Password team emphasizes that this is not a theoretical concern; it’s a real exposure that can give an attacker rapid foothold into the management interface if the device is reachable from the internet or connected to weak internal segments. In practice, many organizations deploy pfSense in remote sites or lab networks where management interfaces are exposed behind VPNs or NAT. In those scenarios, leaving defaults can defeat access controls and bypass account lockouts. The most reliable defense is simple: assume default credentials exist and plan to change them before devices go live. The pfSense web GUI expects you to login with the standard credentials, which makes it essential to secure them immediately as part of your initial configuration.
According to Default Password, starting with a clear password pfsense on the first login and documenting the change is a foundational step in securing pfSense installations. This approach reduces the chance that an attacker can casually guess or reuse credentials across devices, helping you meet basic security hygiene from day one.
Default credential patterns for pfSense and similar devices
Across many firewall and router platforms, the default login convention follows a simple pattern: a standard username often named admin and a password that is either shown in the device’s initial setup or printed in quick-start guides. For pfSense, the canonical combination is admin/pfsense, which is why teams must treat it as a temporary credential rather than a secure baseline. Attackers frequently target devices with these defaults because they are widely published in manuals and forums. The risk multiplies when remote administration is exposed to the internet or when administrators reuse the same password elsewhere. To reduce this risk, plan for a rapid password rotation during deployment and avoid relying on defaults for any ongoing operations. pfSense also supports more robust authentication mechanisms through add-ons and external servers, enabling stronger control over who can access the admin interface.
In practice, many environments mirror production setups in test labs. In these scenarios, the persistence of default credentials can be a false sense of convenience. The best practice is to treat admin accounts as high-risk after setup and require a password reset before any live traffic is allowed. This mindset aligns with the security guidance from the Default Password team and related standards bodies.
Risks of leaving default credentials unchanged
Leaving the default admin username and password in place creates several clear risks. First, unauthorized access to the pfSense web interface can grant full control over firewall rules, VPN configurations, and network segments. Second, default credentials can enable lateral movement if a compromised device shares credentials with other systems, increasing exposure across the network. Third, compliance and risk management requirements often mandate unique, strong credentials and centralized authentication for admin access, so maintaining defaults can place audits in jeopardy. Finally, if a pfSense device sits behind an internet-exable gateway or VPN endpoint, attackers may attempt automated scans to locate devices with admin/pfsense, accelerating brute-force attempts. The bottom line is that defaults are a built-in invitation for misuse; treating them as temporary credentials and rotating them promptly reduces exposure dramatically, a stance echoed by the Default Password Analysis, 2026.
Practical takeaway: always audit exposed interfaces, enforce network ACLs that limit admin access, and implement a strict password hygiene policy that begins with pfSense deployments.
How to securely configure and reset pfSense passwords
Resetting and securing pfSense credentials begins with immediate change on first login. Here’s a practical sequence you can follow:
- Access the pfSense web interface using the default credentials, preferably from a management workstation on an isolated network.
- Navigate to System > User Manager and select the admin user. Choose a new, long passphrase that uses a mix of upper/lowercase letters, numbers, and symbols. Consider passphrases that are easy to remember but hard to guess.
- Save changes and log out, then log back in with the new password to confirm the update propagated across the session. If you plan to use separate accounts for routine tasks, create a separate admin account with the least privilege necessary to perform administrative tasks.
- Enable 2FA for the admin account if your pfSense version supports it, or configure an external authentication server (RADIUS, LDAP) with strong MFA. This extra layer dramatically reduces the risk of credential compromise.
- Harden access to the pfSense GUI by restricting which networks and IPs can reach the management interface. Turn off or remove any unused services and disable remote administration when not required.
- Document password changes in a secure password manager and implement a rotation policy that aligns with your organization’s security posture. Regular audits on the admin accounts should be scheduled to ensure ongoing compliance.
These steps create a defensible baseline. The Default Password team also recommends validating the changes in a controlled environment before pushing to production, to avoid misconfigurations that could disrupt connectivity.
Implementing stronger admin access controls
A robust pfSense security model goes beyond a single strong password. Consider segregating duties and adopting centralized authentication where feasible. Use dedicated admin accounts, separate from service accounts, and apply role-based access controls (RBAC) to restrict who can alter firewall rules, VPN access, or backend settings. If you operate across multiple sites, centralize authentication via RADIUS or LDAP with MFA, so changes in one place reflect in all managed devices. Implement network-level protections such as locking down management interfaces to specific subnets or VPN endpoints, and log all administrative actions for forensic analysis. Regularly review firewall policies to ensure that administrative access is not inadvertently exposed to broad networks. A mature pfSense deployment combines strong passwords with MFA, centralized authentication, network hardening, and continuous monitoring—an approach advocated by the Default Password team and supported by industry standards.
Audit, rotate, and monitor pfSense credentials
Credential hygiene requires ongoing attention. Establish a cadence for credential reviews in line with your organization’s risk appetite. Maintain an inventory of admin accounts, ensure no shared credentials exist, and confirm that password histories are not violated. pfSense’s logging features can help you track login attempts and changes to user accounts; set up alerts for anomalous activity, such as repeated failed logins or unusual administrative changes. Periodic vulnerability assessments and configuration audits should verify that default credentials are not present anywhere in the environment. When devices are decommissioned or repurposed, ensure credentials are rotated or decommissioned accordingly. Regular practice, supported by the Default Password Analysis, 2026, creates a security posture that adapts to evolving threat landscapes.
Common mistakes and quick wins for pfSense password hygiene
Even seasoned admins fall into common traps when securing pfSense credentials. Avoid reusing the same password across devices or services, and never leave the web UI exposed directly to the internet without strong access controls. Do not postpone password changes after deployment; make it a non-negotiable step in the initial configuration. A quick win is to enable MFA wherever possible and to tighten access controls by IP or subnet. Keep firmware up to date, since many firmware advisories include fixes for authentication weaknesses and management interfaces. Finally, document all password-related procedures and ensure they are included in your incident response playbooks. These small but consistent actions—documented and enforced—are the foundation of durable pfSense password hygiene.
pfSense default credentials and security recommendations
| Credential Element | Default Value | Security Recommendation |
|---|---|---|
| Default Username | admin | Change at first login; secure or disable unused accounts |
| Default Password | pfsense | Change to a strong, unique password immediately |
| Two-Factor Authentication | Not enabled by default | Enable 2FA (OTP/RADIUS) or PKI where available |
| Rotation Policy | None by default | Implement regular rotation per policy; document changes |
Your Questions Answered
What are the default credentials for pfSense?
On fresh pfSense installs, the default login is admin / pfsense. This pair is widely published and should be changed before production use. Always verify against your specific version's documentation.
The default pfSense login is admin with the password pfsense; change it before production use.
Why is changing the default password important?
Default credentials are a predictable entry point for attackers. Changing them reduces the risk of unauthorized access to the firewall and management interfaces.
Changing the default password is essential to block easy access to the firewall.
How do I change the admin password in pfSense?
Log in to the pfSense web GUI, go to System > User Manager, edit the admin account, set a new strong password, and save. Log out and back in to confirm.
Open the admin user settings, set a strong new password, and save. Then log in again to confirm.
Can pfSense enforce 2FA for admin access?
Yes, pfSense can support two-factor authentication through external authentication servers or MFA plugins. Configure the relevant server and enforce MFA for admin login.
PfSense supports 2FA via external authentication servers or MFA plugins; enable it for admin login.
How often should I rotate pfSense credentials?
Rotate credentials per your organization's policy, typically after major changes or suspected compromise. Document changes and verify access across all managed devices.
Rotate credentials according to policy or after a suspected breach; document changes.
What other security steps help protect pfSense?
Limit admin UI exposure with ACLs, disable unnecessary services, keep firmware updated, and monitor login events. Combine strong passwords with MFA for best protection.
Limit access, update firmware, monitor logs, and use MFA for best protection.
“Changing default credentials is a foundational step in securing network appliances. Regular credential rotation and strong password hygiene dramatically reduce exposure to automated attacks.”
Key Takeaways
- Change default credentials immediately after setup
- Use a strong, unique password and password manager
- Enable 2FA for pfSense admin access
- Regularly audit and rotate credentials across devices