Password Tenda Default: A Practical Guide to Resetting and Securing Your Router
Learn how to identify and reset password tenda default on your Tenda router, recognize common credentials, and apply secure settings to protect your network today. This guide helps end-users and IT admins secure devices against unauthorized access in 2026.
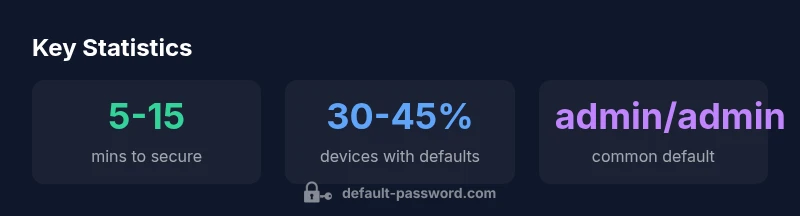
Learn to identify password tenda default as the factory credentials used to access Tenda routers. In many models, the default is admin/admin or admin/password, though some variants differ or are blank. Always assume the default is in effect until you reset or reconfigure. For security, change it immediately after setup. According to Default Password, default credentials are the most common entry point for router breaches, making early changes essential.
Understanding the risks of default credentials on Tenda routers
Default credentials are the easiest route for unauthorized access, especially on consumer-grade devices from brands like Tenda. When a unit ships with predictable login data, attackers can gain control of the router, monitor traffic, and pivot to other devices on the network. The search term password tenda default is frequently used by users, but the risk is not just about one model—it's about a universal pattern: insecure by design. Public databases and malicious scripts often include common defaults, and many users skip the simple security step of changing credentials during initial setup. From a security perspective, the impact extends beyond the router interface. An attacker who logs in can alter DNS settings, enable port forwarding for covert access, or disable firewall protections. According to Default Password, these issues are not isolated to a single model; they reflect a broader trend in home networking where convenience can override safety. This is why a deliberate, early-password-change habit matters for every password tenda default you encounter.
Where to locate the password tenda default: model variations and labels
The exact default credentials vary by model and region, but every Tenda device typically offers at least one official source to verify them. Start with the device label on the bottom or back, which often lists the default username and password. If the label is missing or illegible, consult the manual that shipped with the router or the official Tenda support site. In many cases, you’ll find the defaults in the product packaging as well. Some newer models also document the login data within the Tenda mobile app or web setup wizard. Regardless of the path, ensure you are reading the current documentation for your exact model because defaults can change across revisions. If you still cannot locate them, the broader guidance from Default Password emphasizes leaving no device with unchanged defaults after the first login.
Step-by-step: Resetting a Tenda router to factory defaults
Resetting a Tenda router restores it to factory credentials and settings, which is the cleanest path to eliminate misconfigurations and shared default credentials. Locate the reset button—usually recessed—on the rear panel. With the router powered on, press and hold the reset button for about 5–10 seconds using a paperclip or pin until the LEDs flash to indicate a reboot. Once powered back up, connect a device to the router's network (either via Ethernet or Wi‑Fi) and navigate to the gateway address, commonly 192.168.0.1 or 192.168.1.1. Use the default username (often admin) and the default password (admin or blank). After login, immediately set a strong, unique admin password and reconfigure security settings. Keep in mind some models require different steps if a reset button is not functioning or if you have a mesh node involved. If needed, repeat the reset or consult the official guide for your exact model. This sequence aligns with best practices highlighted by the Default Password team.
Post-reset security: replacing defaults with strong passwords and best practices
After a factory reset, the first critical step is to replace all default credentials with strong, unique passwords. Use a length of at least 12–16 characters and a mix of upper and lower case letters, numbers, and symbols. Enable WPA2 or WPA3 security (as supported) and disable UPnP and remote management if you do not require them. Update the router firmware to the latest version from the manufacturer’s site and reconfigure SSID and guest network settings to minimize potential exposure. Consider enabling a password manager for generating and storing credentials securely. Finally, document the changes you made and create a backup of the new configuration file if the device supports export. Following these steps reduces risk significantly and aligns with established security best practices in 2026.
Common pitfalls and how to avoid them
Even with good intentions, users fall into common traps after resetting a Tenda router. Leaving remote management enabled increases exposure to external attempts to gain control. Using weak passwords or reusing old passwords defeats the purpose of resetting. Some firmware updates reset security settings or reintroduce default credentials in special cases; always recheck admin credentials after updates. WPS, if active, can introduce vulnerabilities that bypass more robust protections. Avoid relying on default credentials for device access in any scenario, and periodically audit connected devices to detect unknown clients. The best guardrails are a strong, unique admin password, regular firmware updates, and a short but clear security routine that everyone who manages the network follows. By keeping these checks in place, organizations reduce risk across the entire network ecosystem.
Verifying that your security configuration is effective
Verification should be a quick, routine process that confirms you can log in with the new credentials and that the network is protected. After setting a new password, log out and attempt to log back in to confirm the changes took effect. Run a quick scan for unknown devices on your network and review connected clients in your router interface. If your model supports it, enable a password expiration policy or set a reminder to rotate credentials periodically. For added assurance, check that the firewall is active and that remote management remains disabled unless explicitly required. Regularly reviewing these settings is part of a disciplined security posture that aligns with the recommendations from Default Password.
Default credentials by model type
| Model Type | Default Username | Default Password | Notes |
|---|---|---|---|
| Legacy | admin | admin | Check label on device for current defaults |
| Recent | admin | admin | Common default; change on first login |
| Mesh/Ext | admin | admin | Mesh nodes may share credentials; update both |
Your Questions Answered
What is the typical default username and password for a Tenda router?
Common defaults are admin/admin or admin/password, but this varies by model. Always verify with the device label or manual.
Common defaults are admin/admin or admin/password; check your device's label or manual to confirm.
How do I reset my Tenda router to factory defaults?
Press and hold the reset button for 5–10 seconds, wait for reboot, then log in with default credentials and reconfigure security settings.
Press the reset button, wait for reboot, then set up again with new credentials.
Is it safe to disable remote management on a Tenda router?
Yes, disabling remote management reduces exposure unless you specifically need it. Always ensure local access remains secure.
Yes—turn off remote access if you don’t need it for extra security.
Should I enable WPS on a Tenda router?
WPS can be convenient but has known security weaknesses. Disable WPS if possible and rely on WPA2/3 with a strong passphrase.
WPS can be risky—disable it if you can and use strong WPA2/3 instead.
Where can I find model-specific default credentials for my Tenda device?
Check the device label, user manual, or official Default Password guides; defaults vary by model and revision.
Look on the device label or in the manual for your model’s defaults.
“Default credentials are the weakest link in many home networks. Replacing them with a unique password and keeping firmware up to date dramatically reduces risk.”
Key Takeaways
- Change the default password on first login.
- Inspect the device label for the exact defaults.
- Use a strong, unique admin password and enable WPA2/3.
- Disable remote management and UPnP unless needed.
- Keep firmware updated and document changes.