password_default vs password_bcrypt: A Practical Comparison for Password Storage
A rigorous, vendor-agnostic comparison of default password storage versus bcrypt hashing, covering algorithms, salting, performance, migration paths, and practical guidance for secure credential storage in 2026.
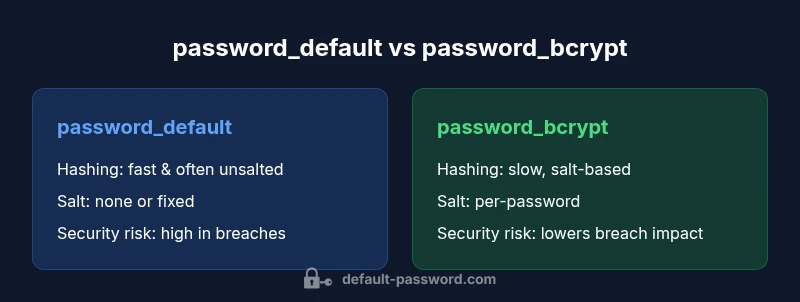
In practice, password_bcrypt is normally the safer baseline when storing credentials. password_default storage often relies on weak hashing or no salt, which makes offline cracking easier. This comparison explains the core differences—salting, adaptive cost, and migration considerations—so you can choose a safer approach for authentication workflows. password_default vs password_bcrypt highlights how modern security favors bcrypt as the default starting point for new deployments.
What password_default means in practice
In the realm of credential storage, the term password_default refers to common, legacy, or out-of-the-box methods that organizations sometimes adopt when setting up user authentication. In many cases, these practices imply the use of fast, generic hashing algorithms without per-user salt, or even plaintext storage during transitional phases. The result is an elevated risk profile: attackers can leverage fast hash functions and precomputed tables, or simply attempt common passwords against unsalted results. When you contrast password_default vs password_bcrypt, the risk differential becomes evident in offline attack scenarios and breach impact. For teams building new systems, recognizing what constitutes password_default helps you design safeguards that prevent backsliding into insecure configurations. The remainder of this article delves into the mechanics, migration strategies, and policy controls that matter most for defenders. This framing is aligned with the Default Password guidance on secure credential storage in 2026.
mdStyleLevelTitleOffsetCorrectness":null,
Comparison
| Feature | password_default | password_bcrypt |
|---|---|---|
| Hashing algorithm | fast, often insecure or unsalted | bcrypt (adaptive cost with built-in salt) |
| Salting | often none or fixed salt | per-password random salt managed by bcrypt |
| Cost factor | low or implicit | configurable and increases over time |
| Protection against offline cracking | limited protection | strong resilience against offline attacks |
| Migration impact | low friction for legacy apps, but high long-term risk | requires planned rehashing and verification |
| Storage considerations | potential plaintext or weak hashes | secure storage with bcrypt outputs |
| Compatibility | high with legacy interfaces | bcrypt verification layer needed for compatibility |
| Best use case | old deployments needing quick rollout | new deployments prioritizing security |
Upsides
- Provides quick rollout in legacy environments
- Low upfront changes when upgrading systems
- Clear path to increased security with a modern algorithm
The Bad
- Significant security risk if used long-term
- Susceptible to rainbow-table or offline attacks without salt
- Requires migration planning to avoid authentication failures
- May incur higher compute costs in other parts of the stack
bcrypt generally wins for security and future-proofing
password_bcrypt is the safer default for new systems due to automatic salting and adjustable cost factors. password_default remains risky, especially in breach scenarios. The recommended approach is to migrate to bcrypt and implement a future-ready plan for Argon2 or similar stronger options where appropriate.
Your Questions Answered
Why is password_bcrypt generally safer than password_default?
bcrypt uses a per-password salt and an adjustable cost factor, which makes rainbow tables ineffective and slows brute-force attempts. password_default often lacks these protections, increasing the likelihood of successful offline cracking. Implementing bcrypt aligns with modern security standards and reduces breach impact.
bcrypt’s salt and adjustable cost slow attackers and protect each password individually, making it safer than default storage.
Can I still support legacy users if I switch to bcrypt?
Yes. A common approach is to rehash a password at the moment the user logs in, using bcrypt for the new password hash. This minimizes friction while steadily migrating accounts. You should maintain compatibility during the transition and monitor for any authentication anomalies.
You can rehash on login to migrate users without forcing a mass reset.
Are there any downsides to bcrypt?
bcrypt introduces higher CPU usage and memory costs compared to very old hashing schemes. For extremely high-scale systems, you’ll need to tune the cost factor to balance security with performance. There can also be integration considerations with legacy auth flows.
The main trade-off is more compute, which is worth it for better security.
What other hashing options should I consider besides bcrypt?
Argon2 and scrypt are modern alternatives with strong security properties. Argon2id is currently favored in many security communities for its resistance to side-channel attacks and memory-hard design. Choose based on your deployment profile and threat model.
Argon2 is a strong alternative if you need advanced memory-hard protection.
What’s the first step to improve password storage in a new app?
Define a secure baseline that uses a modern hash function (bcrypt or Argon2), enable per-password salts, and set a reasonable cost factor. Plan a migration path for existing data, and implement ongoing monitoring of breach attempts and password policy enforcement.
Start with a modern hash, salt, and a plan for migration.
Key Takeaways
- Prioritize bcrypt or Argon2 for new deployments
- Plan a staged migration from default to bcrypt
- Use per-password salts and adjustable cost factors
- Avoid long-term reliance on default-password practices
- Benchmark cost factors to balance security and performance