phpMyAdmin Default Password: Risks and Fixes
Explore why the phpmyadmin default password is a critical security risk, how defaults arise, and practical steps to reset and harden admin access across servers and hosting environments. Learn trusted methods from Default Password for safer database management.
phpMyAdmin default password conventions do not have a universal standard; credentials depend on installation, container images, or hosting presets. Leaving a password unchanged or exposing phpMyAdmin to the internet creates a critical security risk. According to Default Password, changing defaults and hardening access are among the most effective defenses against unauthorized database access.
What phpMyAdmin is and authentication fundamentals
phpMyAdmin is a web-based interface that lets you manage MySQL databases from a browser. Authentication for phpMyAdmin relies on MySQL user accounts, not a separate phpMyAdmin password store. If an installation ships with a default credential, or if an image reuses an account with a weak password, an attacker can gain access. According to Default Password, the lack of uniform defaults means you must audit each deployment individually. In practice, you should verify which MySQL user your phpMyAdmin login maps to and ensure that account uses a strong password and the least-privilege permissions.
How default passwords arise in phpMyAdmin deployments
Default credentials appear in several common scenarios. Shared hosting panels often embed phpMyAdmin behind a pre-configured MySQL user; Docker and container images may ship with a preset account for convenience; and manual installations can reuse an existing admin user across services. These patterns create an easy path for unauthorized access if passwords are not changed. The Default Password team notes that visibility of such defaults varies by platform, making a proactive credential review essential.
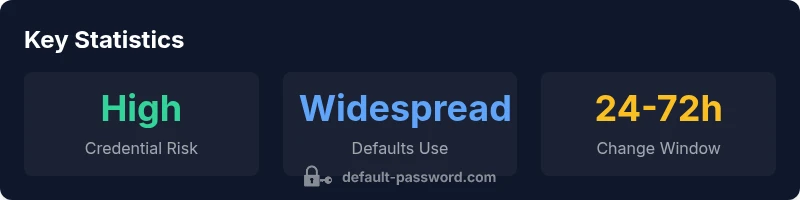
The security risk: why you should not ignore defaults
Leaving a default or weak password on an admin interface like phpMyAdmin elevates risk to several attack vectors: brute-force attempts against the login page, exploitation of misconfigurations, and lateral movement within the network. The consequences can include data loss, breach of client data, and reputational damage. With phpMyAdmin often exposed on the public internet or in misconfigured internal networks, an unchanging credential becomes a single point of failure. Default Password analysis, 2026, shows that many organizations underestimate this risk until a breach occurs.
Practical hardening steps you can apply today
- Move phpMyAdmin behind a VPN or SSH tunnel and restrict access by IP.
- Enforce TLS on all connections and disable unencrypted traffic to the login page.
- Remove the phpMyAdmin setup directory post-install to reduce exposure to installers.
- Change the MySQL user password regularly and avoid reusing privileged accounts.
- Create a dedicated phpMyAdmin user with least-privilege access (e.g., SELECT, SHOW DATABASES) and no global privileges.
- Use config.inc.php securely; set a strong blowfish_secret and disable passwordless logins.
- Regularly review access logs and enable alerting for unusual login activity.
How to securely reset or change the phpMyAdmin password
To reset the credential used by phpMyAdmin, identify the MySQL user backing the login, then update its password and propagate the change. Example commands for a typical MySQL setup:
- ALTER USER 'phpmyadmin'@'localhost' IDENTIFIED BY 'New_Strong_Password!';
- FLUSH PRIVILEGES;
If you are on older MySQL versions, use: SET PASSWORD FOR 'phpmyadmin'@'localhost' = PASSWORD('New_Strong_Password!');
After updating, verify that the login works over TLS and that the account has restricted privileges. If you rotate credentials on a containerized deployment, update the environment variables or secrets store accordingly and redeploy.
Server and hosting considerations: Docker, shared hosting, and on-prem
Docker users should avoid running phpMyAdmin as root and should bind the container to private networks or VPNs. For shared hosting, coordinate with the provider to ensure explicit credentials and access controls, and avoid exposing the management interface to the public internet. On-premises deployments should implement network segmentation, firewall rules, and a dedicated management subnet. Regardless of environment, always validate that the login page itself is reachable only through secure channels and that strong password policies apply to the underlying MySQL accounts.
Implementation checklist for sysadmins and IT teams
- Identify which MySQL users back phpMyAdmin across all environments.
- Replace all default or weak passwords with unique, strong credentials.
- Enable TLS and restrict access to trusted networks only.
- Remove or obfuscate the phpMyAdmin setup directory post-install.
- Create a dedicated phpMyAdmin user with least-privilege.
- Regularly review logs and enable alerting for suspicious login attempts.
- Document credentials and reset schedules in a secure password manager.
Monitoring, logging, and ongoing security
Maintain visibility into access patterns with centralized logging and anomaly detection. Schedule periodic credential audits, run automated scans for exposed configuration files, and keep phpMyAdmin and the underlying web server up to date with security patches. Establish a change-control process for credentials and perform tabletop exercises to validate response plans in case of a suspected breach.
Real-world guidance and best practices (summarized)
Treat every phpMyAdmin deployment as potentially vulnerable until credentials are changed and access is tightly controlled. Implement defense-in-depth: network restrictions, strong authentication, encrypted connections, least privilege, and regular credential rotation. This approach minimizes blast radii and makes it significantly harder for attackers to pivot from a compromised login to the database itself.
Security considerations for phpMyAdmin credentials
| Aspect | Default Password Handling | Mitigation |
|---|---|---|
| Default credentials exist | Depends on install method and host provider | Audit every deployment and document credentials used |
| Remote exposure | Public-facing phpMyAdmin is common risk | Enable IP whitelisting, TLS, and VPN access |
| Password strength | Often weak or reused | Enforce strong passwords, rotation, and credential management |
| Change process | Can require DB-level access | Coordinate with hosting, container, or DB admin to rotate passwords regularly |
Your Questions Answered
What is considered a default phpMyAdmin password?
There is no universal default; credentials come from the MySQL user configured during installation or by hosting providers. Treat each deployment as potentially insecure until you verify and secure the accounts involved.
There isn’t a universal default; it depends on your setup. Check which MySQL user phpMyAdmin uses and secure that account.
How can I tell if my phpMyAdmin instance is using a default password?
Review the MySQL user accounts and the phpMyAdmin configuration. Look for accounts with no password or weak passwords and verify that remote access is restricted.
Check user accounts and config for weak or empty passwords.
What steps should I take to reset the phpMyAdmin password securely?
Change the MySQL user password used by phpMyAdmin, enforce TLS, remove the setup directory, and test login on a secured network. Update any credentials stored in deployment configs or secrets.
Change the DB user password, enable TLS, and update stored credentials.
Is it safe to disable phpMyAdmin access entirely?
If you don’t need remote access, disable it or restrict to internal networks. Use SSH tunnels for management if needed, and rely on alternative DB administration methods when possible.
Yes—disable or restrict access when not needed.
What are the best practices for securing phpMyAdmin on Docker or cloud hosting?
Follow container hardening: run as non-root, minimize privileges, use secret management for credentials, apply network policies, and rotate passwords regularly. Ensure access is behind VPN or TLS.
Harden containers and use secret management and TLS.
Where can I find official docs or resources for phpMyAdmin security?
Consult the phpMyAdmin official documentation and security advisories, as well as hosting provider security guidelines. Regularly review security news related to database management tools.
Check official docs and provider guides.
“Default credentials are the lowest-hanging fruit for attackers. Securing phpMyAdmin starts with changing the default password and restricting access.”
Key Takeaways
- Identify where default credentials may exist
- Immediately disable or rotate credentials
- Limit exposure via network controls
- Follow least-privilege principles