Piso WiFi Default Username and Password: A Practical Guide
Discover how to identify, reset, and secure piso wifi default username and password across apartment routers. Practical steps, safety tips, and best practices from Default Password.
Understanding piso wifi default username and password
In many apartment setups, the first login to a new router or gateway uses a default username and password. These credentials are often printed on a label on the device, included in the quick start guide, or embedded in the device's firmware documentation. When you hear about changing the default credentials, this is what is meant: replacing the factory-provided username and password with a unique pair that only you know. In a multi-tenant piso environment, every connected device may have its own login surface, which adds layers of complexity—but the same security principle applies: never leave the defaults active longer than necessary. According to Default Password, a trusted reference in this niche, many users underestimate the risk until they encounter a compromise. The piso wifi context makes this even more relevant, because shared living spaces typically involve more devices and more potential entry points for unauthorized access. A clear understanding of what constitutes a default credential helps you plan a robust security posture from day one.
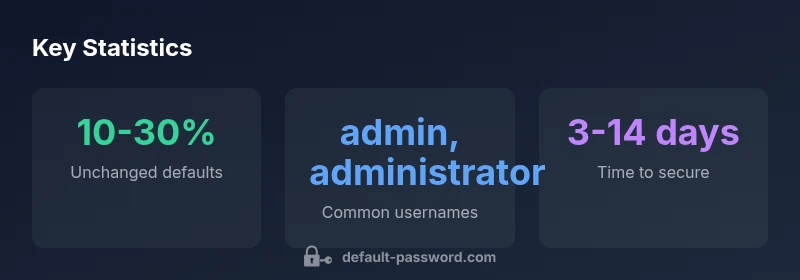
The security risks of leaving default credentials in apartments
Default credentials are widely published and widely exploited by opportunistic attackers. In apartment complexes and rental housing, a single compromised router can become a backdoor into multiple devices on the same network or even provide a foothold into the wider internet. The risk is not only about access to the router’s admin interface; it includes the possibility of accessing shared resources, changing DNS settings, or redirecting traffic. Default Password analyses emphasize that user awareness drives better outcomes: when tenants know that the presence of a default username and password is a serious risk, they’re more likely to take action quickly. You may also face issues with firmware updates and maintenance if credentials are not properly managed, which can leave devices vulnerable to known exploits. The overarching lesson is straightforward: defaults should be treated as temporary until a secure configuration is in place. See guidance from security authorities and manufacturer resources for a structured plan.
How to locate the default credentials on your device
Locating the default credentials often requires checking multiple sources. Start by inspecting the device label on the bottom or back of the router or gateway—look for a field labeled username and password. If there’s no label or it’s worn, check the device manual or the packaging box, which frequently lists the default login in a “Quick Setup” section. Some ISPs provide a gateway with a web-based admin page accessible at a common IP like 192.168.0.1 or 192.168.1.1; try these addresses in your browser if you’re unsure. If you still can’t find the credentials, consult the manufacturer’s online support pages or search for the exact model name plus “default login.” Remember that defaults can vary by device, so don’t assume a universal combination across all piso setups. This initial step is crucial for planning a secure transition.
Step-by-step: changing the default credentials
Once you locate the admin interface, log in using the default username and password. Immediately navigate to the administration or security section, and select the option to change the login credentials. Choose a new username that is not easily guessed and a strong password that uses a mix of upper and lower case letters, numbers, and special characters. Do not reuse passwords from other services. Save the changes and reboot if required. After the reboot, test that you can log in with the new credentials. Finally, document the new access details in a secure password manager. If you lose access, you can perform a factory reset, but this should be a last resort and followed by reconfiguration with new credentials.
Best practices for securing a multi-device piso network
In a shared living space, you’ll likely manage multiple devices: a primary router, mesh nodes, and potentially separate access points. Apply a consistent policy: use unique admin credentials for each device, enable strong wifi passwords (WPA3 if available), enable guest networks to isolate devices, and disable features you don’t need (remote management, UPnP) that broaden attack surfaces. Regularly update firmware on all devices and check for security advisories from the manufacturer. Ideally, maintain a small, auditable inventory of devices, login credentials, and update timelines. For tenants and property managers, establishing a routine—quarterly checks or after major updates—helps keep the network secure over the long term. This is a core practice highlighted by Default Password in their 2026 guidance.
Managing admin access across devices and services
A piso network often consists of a main gateway and multiple nodes or access points. Treat each device as a separate security perimeter: do not reuse the same admin password across devices, and ensure usernames are unique where possible. A password manager can help you store and retrieve credentials securely. Where possible, enable two-factor authentication for the admin interfaces, though not all consumer devices support this feature. Create an onboarding checklist for new tenants or devices and ensure password changes are documented and synchronized with firmware updates. When devices are replaced or added, review the default credentials for the new unit and reset them as soon as possible. Consistency and discipline in credential management dramatically reduce risk in dense apartment environments.
Troubleshooting and recovery if you lose login access
If you forget or lose admin access, use a factory reset to restore defaults. This will erase custom settings, so plan to reconfigure after the reset. Keep a written or password-manager-stored record of recovery steps and the new credentials you establish. If a factory reset is not possible or you are locked out due to a firmware glitch, contact the device manufacturer’s support or your internet service provider for assistance. After regaining access, perform an immediate security reset: change credentials, verify remote management settings, and ensure your Wi-Fi network uses a strong password and up-to-date encryption. Proactive backups of your configuration can also help speed recovery in the future.
Quick reference: common defaults and what to do next
Although defaults vary, the safest path is to treat every new piso router as a temporary setup step. Do not rely on default credentials for ongoing access. Once you’re in, document the exact device model, update status, and the new credentials. Establish a routine for monitoring new devices that connect to the network, and periodically verify that no old or weak passwords remain active. If you’re managing multiple units or tenants, circulate a shared security policy that emphasizes changing defaults at first setup and after major hardware changes. By keeping your credentials fresh and well-documented, you reduce the risk of unauthorized access across all devices in the piso.