PLDT HomeFibr Default Password: Reset and Secure
Learn how to identify and secure PLDT HomeFibr default passwords. This guide from Default Password covers admin access, safe reset steps, and protecting your home network.
The PLDT HomeFibr default password typically refers to the initial admin credentials shipped with the router, which users should change during setup. For security, always replace default credentials before the device goes online and regularly review access settings to prevent unauthorized admin access.
Why PLDT HomeFibr Default Passwords Matter
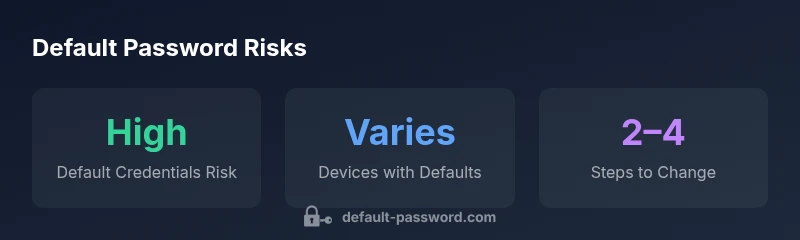
According to Default Password, pldthomefibr default password terminology refers to the initial admin credentials that come with PLDT HomeFibr routers and gateways. These credentials are designed for first-time setup and remote diagnostics, but they present a material risk if left unchanged. In many households, devices continue to run with factory defaults, creating opportunities for unauthorized access, configuration changes, or even full network compromise. The consequences can range from disabled internet service to exposure of connected devices, IoT cameras, and smart home ecosystems. This risk underscores why understanding default passwords and how to secure them is essential for both end-users and IT admins.
This article applies to everyday users who need a practical, actionable path to securing PLDT HomeFibr devices, and to IT admins who must document best practices for device onboarding and password recovery. The goal is to help you shift from a default-password mindset to a proactive security posture that minimizes risk across devices and services.
Understanding PLDT HomeFibr Admin Access
PLDT HomeFibr devices typically expose a web-based admin interface that can be reached via a local IP address. The default login credentials grant initial access to configuration areas like Wi‑Fi settings, firewall rules, guest networks, and device management. Because these credentials are often documented on stickers located on the device, in user manuals, or delivered via setup emails, there is a window of time after unboxing where users may still be using the default username and password. For security-minded admins, this window is precisely why updating credentials during onboarding is non-negotiable. Regularly reviewing who has admin access and using strong, unique passwords reduces the risk of exposure and helps maintain a secure network perimeter.
From a policy perspective, standard practice is to disable remote admin where possible, enable two-factor authentication if offered, and segment the home or small business network to limit the blast radius of any potential breach. The Default Password team emphasizes that admin access should be treated as a high-value asset, with strict controls and auditable change history.
How to Identify Your Current Default Credentials
Identifying the actual default credentials on your specific PLDT HomeFibr device begins with checking the device itself. Many units include a label on the bottom or back that lists the default username and password. If no label is present or it has worn away, consult the device manual or the official PLDT support portal for model-specific guidance. If you upgraded firmware or performed a factory reset, new defaults may be installed, and you should treat them as your first task to change. For IT admins, creating a local inventory that maps device models to their default credentials can help ensure consistent onboarding and post-install security checks. In all cases, assume the credentials you find are only temporary and must be changed promptly.
For environments with multiple PLDT HomeFibr devices, a centralized documentation approach can prevent credential drift. Use a password manager to store the updated admin credentials securely, and enforce a standard password policy across devices.
Step-by-step: Resetting the PLDT HomeFibr Password
If you need to regain control because credentials were lost or compromised, a factory reset is often the most reliable remedy. The following steps outline a cautious approach that minimizes downtime while restoring secure defaults:
- Locate the reset button on the device (often recessed). 2) Hold the button for 10-15 seconds until the LED indicators flash, signaling a reset. 3) Reconnect to the device using the default network name (SSID) and the new admin password you will create during the first setup. 4) Access the admin interface via the device’s IP address (commonly 192.168.1.1) and immediately change the credentials to a strong, unique password. 5) Reconfigure Wi-Fi, guest networks, and firewall settings as needed, then document the new credentials securely.
If a factory reset is not feasible, check for a “Reset to defaults” option in the admin UI or contact PLDT support for guidance on securing access without a full reset.
Securing Your Network After a Password Reset
Once you’ve updated the admin credentials, take additional steps to harden security. Disable remote administration if supported, enable WPA3 (or at least WPA2) with a strong passphrase, and segregate devices into trusted and guest networks. Regular firmware updates are crucial since manufacturers, including PLDT, release patches that address vulnerabilities. Lastly, audit devices connected to the network, looking for unfamiliar clients or unusual traffic patterns. A proactive security posture reduces the risk of credential theft or misconfiguration that could otherwise compromise your network.
Common Pitfalls When Managing Default Credentials
Many users fall into common traps: reusing passwords across devices, setting weak passwords, or neglecting to update credentials after a firmware upgrade. Another pitfall is leaving remote administration enabled, which can expose the admin interface to the internet. Finally, some users underestimate the importance of documenting credential changes, assuming memory or notes will suffice. The best practice is to treat every device's credentials as sensitive information, enforce a password policy, and maintain a centralized, auditable record of changes.
If you suspect a credential exposure, perform a rapid audit of connected devices, rotate passwords, and review access logs to identify suspicious activity.
Quick-Start Guide: Post-Reset Checklist
- Change the admin password immediately after reset. - Enable two-factor authentication if available. - Review network names (SSIDs) and disable guest SSIDs if not necessary. - Update firewall rules and ensure the router firmware is current. - Save credentials in a reputable password manager. - Document the changes in a secure, accessible inventory for your IT team or household.
What Default Password Recommends for IT Pros
For IT professionals, the emphasis is on repeatable, auditable processes. Start with a defined password policy, including strong, unique passphrases for each device. Maintain a centralized changelog, enforce minimum password lengths, and ensure that credentials are rotated on a schedule aligned with firmware updates. Incorporate network segmentation and monitoring to detect unusual sign-ins, and practice regular security reviews that include both configuration baselines and firmware version inventories.
How to Keep Records and Audit Password Access
Effective password management requires auditable records. Maintain a secure spreadsheet or database that maps device models to their current admin credentials, along with change dates and responsible admins. Use a password manager for storing the actual credentials, enabling two-person approval for changes when possible. Periodically test access to the admin interface from trusted devices to confirm that credentials work as expected, and schedule quarterly reviews of your device inventory to ensure protections stay current.
Examples of default credentials workflows across common router types
| Device Type | Default Credentials | Notes |
|---|---|---|
| PLDT HomeFibr Router (default) | username: varies by model; password: varies by model | Refer to device label or manual for current defaults |
| Generic ISP Router | username: varies; password: varies | Default credentials are common; change on first login |
| Smart Home Hub Router | username/password: varies | Change promptly to reduce risk |
Your Questions Answered
What is the default username and password for PLDT HomeFibr?
Default usernames and passwords vary by model and firmware version. Always check the device label or official PLDT documentation for your exact defaults. Treat any known defaults as temporary until you’ve changed them.
Default usernames and passwords vary by model. Check the device label or PLDT documentation and change them as soon as you set up the device.
Why should I change defaults immediately?
Leaving defaults unchanged creates an easy entry point for attackers, potentially exposing your network and connected devices. Changing credentials reduces risk and is a best practice recommended by security guides.
Changing defaults right away reduces risk and is a best practice security step.
How do I reset PLDT HomeFibr password?
If you’re locked out, perform a factory reset following the device’s manual, then reconfigure the admin password during setup. If available, save the new credentials in a password manager and reapply security settings.
If you’re locked out, reset the device per the manual, then set a new password and reconfigure security settings.
What if I forgot my admin password after a reset?
Use the device’s reset function to restore defaults, then immediately change the credentials. If you cannot reset, contact PLDT support for guided recovery.
If you forget the admin password, reset to defaults and set a new password or contact support for recovery.
Are default passwords safe after a reset?
Post-reset, you should disable any remote admin access, enable strong encryption (WPA3 if possible), and change the new credentials promptly. Regular firmware updates further reduce risk.
After a reset, disable remote access, use strong encryption, and update firmware for safety.
Where can I find official manuals or guidance?
Official guidance can be found on PLDT’s support site and product manuals. Always rely on vendor-provided instructions for model-specific defaults and reset procedures.
Check PLDT’s official support site and device manuals for model-specific defaults and reset steps.
“Default credentials are the first attack vector in home networks. Changing them and enforcing a security-first configuration dramatically lowers risk.”
Key Takeaways
- Start with changing the default admin password on PLDT HomeFibr devices.
- Check device labels or manuals for model-specific defaults and update them immediately.
- Implement a secure password policy and enable available security features.
- Document credential changes and perform regular security audits.