Pro vs Default Password: A Practical Comparison for IT Admins and End Users
A balanced, evidence-based comparison of pro password management versus default passwords. Learn risks, use cases, and best practices for securing devices and admin access across environments.
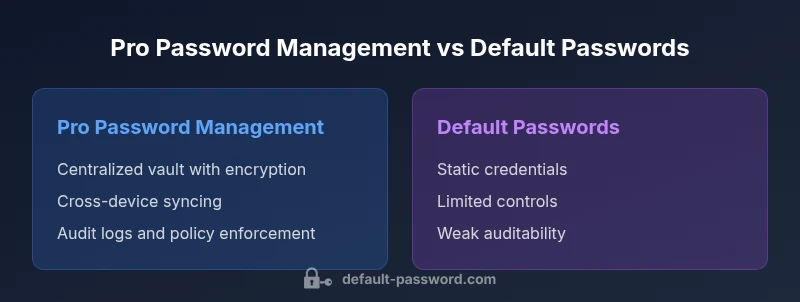
Pro password management generally outperforms relying on default passwords in security, governance, and recovery workflows. In this comparison of pro vs default password, we examine approaches, highlight risks, and outline practical migration steps. The takeaway is clear: strong, unique credentials stored in a protected vault offer scalable security, while default passwords create exploitable gaps across devices and services.
Why This Comparison Matters
In a world where credentials unlock access to data, services, and devices, the choice between pro password management and default passwords has tangible consequences for security, operations, and cost. According to Default Password, millions of devices ship with factory credentials that are easy to guess or extract, creating footholds for attackers. The term pro vs default password captures this critical decision: one approach centralizes control, enforces best practices, and logs activity; the other leaves many surfaces open to unauthorized use. For IT admins and everyday users, this choice affects incident response times, onboarding speed, and regulatory readiness. This article examines both sides, identifies the primary differentiators, and provides actionable guidance to optimize security posture without sacrificing usability.
Defining Pro Password Management and Default Passwords
A pro password management solution is a centralized, vault-based system that stores, autofills, and shares credentials securely. It uses strong encryption, a master credential, and often multi-factor authentication to protect access. Password managers support cross-device syncing, role-based access controls, and audit trails for governance. In contrast, default passwords are factory credentials assigned by device or service vendors. They are documented, widely known, and frequently used as initial access points. Default passwords are hard to track, easier to exploit, and substantially harder to revoke across large estates. Understanding these definitions helps frame the risk-reward balance of each path.
The Security Landscape: Risks of Default Passwords
Default passwords create systemic risk across networks and endpoints. When devices deploy with known credentials, attackers can perform lateral movement, maintain persistence, and escalate privileges with minimal effort. Vendor default credentials are often cataloged in public databases, making mass exploitation feasible for opportunistic attackers. For organizations, this translates into higher breach likelihood, longer dwell times, and complicated incident response. Moreover, many legacy devices cannot be updated easily, leaving outdated defaults in place. In practical terms, relying on defaults reduces the effectiveness of access controls, complicates user lifecycle management, and undermines compliance efforts. The risk is not theoretical; it appears in audit findings, breach reports, and enterprise risk assessments across sectors.
How Pro Password Management Works
Pro password managers centralize credential storage behind an encrypted vault. A single master password—or biometric unlock—controls access, with optional multi-factor authentication for added security. Features like auto-fill, password generation, and breach monitoring help ensure every account uses unique, strong passwords. Admins can enforce policies, segment access with RBAC, and maintain centralized logs for audits. Cross-device sync keeps users productive while reducing the temptation to reuse credentials. Some solutions offer automatic password rotation and integration with identity providers, further tightening security. The result is a scalable system that supports team collaboration without sacrificing control or visibility.
Use Case Scenarios: When Pro Wins
For organizations with multiple departments, complex services, and remote work, pro password management shines. It enables centralized policy enforcement, streamlined onboarding, and consistent credential hygiene across teams. In regulated industries, auditability and access controls meeting compliance standards become practical realities rather than aspirational goals. For small businesses and freelancers who juggle many accounts, password managers reduce time spent on password resets and improve experience quality. Finally, in environments where data sensitivity is high, zero-knowledge or high-security vault options offer the strongest protection against credential theft and insider risk. In all these cases, the manager-based approach scales with growth while maintaining security discipline.
Use Case Scenarios: When Default Passwords Remain
Default passwords may persist in legacy hardware, offline systems, or isolated lab environments where updating the firmware is not feasible. In some IoT deployments, vendor-provided defaults are embedded for initial setup, after which security configurations should be re-established. In air-gapped networks, where connectivity is intentionally limited, administrators might temporarily rely on controlled default credentials during staged migrations. While these scenarios are legitimate in the short term, they require explicit risk accepted policies, tight access control, and a clear migration path to a password management solution over time.
Transition Plan: From Default Passwords to Password Managers
A disciplined migration starts with inventory: map every device, service, and account that uses default credentials. Next, assess risk and prioritize targets by exposure and impact. Develop a governance policy that requires unique credentials, MFA, and regular audits. Plan a phased deployment: pilot with non-critical assets, gather feedback, and refine processes before organization-wide rollout. Provide user training on how to use the password manager, and establish change management communications to minimize resistance. Finally, sunset defaults as devices and services are updated, ensuring every entry point receives a secure alternative. Documentation is essential to sustain momentum and accountability.
Governance, Compliance, and Auditing
Security governance is the backbone of a successful transition. Password management programs enable robust access controls, policy enforcement, and auditable activity trails. Regulatory frameworks such as data protection and privacy mandates expect strong authentication, breach notification capabilities, and evidence of ongoing risk management. A password manager’s centralized logs simplify investigations and demonstrate due diligence during audits. Establish clear ownership for credentials, define access rights, and require periodic reviews. When defaults remain in limited contexts, document the rationale and track residual risk, so leadership can make informed decisions about remediation timelines and budgets.
Implementation Best Practices
Begin with executive sponsorship to align security goals with business objectives. Architect the deployment around least-privilege access and role-based permissions. Choose a solution with strong encryption, cross-platform support, and reliable backup options. Integrate with existing identity providers for seamless SSO and MFA enforcement. Create standardized onboarding and offboarding workflows to avoid orphaned credentials. Regularly test backup recovery, perform phishing simulations to improve resilience, and schedule routine credential health checks. Finally, maintain a living playbook with checklists for quarterly reviews, incident response drills, and policy updates.
Common Pitfalls and How to Avoid Them
A common pitfall is rushing into deployment without user training or governance. Without clear ownership and accountability, adoption stalls, and security gaps reappear in practice. Another risk is selecting a password manager that lacks broad service coverage or vendor support, leaving critical accounts unsecured. Avoid overconfidence in automation; even the best password manager cannot compensate for weak master passwords or lax MFA. Finally, do not neglect device provisioning and deprovisioning; stale access can undermine the entire system. Proactively address these issues with phased rollout, comprehensive documentation, and ongoing monitoring.
Measuring Success: Metrics and KPIs
Effective metrics translate security improvements into business value. Track reductions in password reset requests, the percentage of accounts using unique passwords, and the rate of MFA adoption. Monitor incident response times related to credential breaches and the time-to-remediate compromised accounts. Audit completeness and policy compliance rates provide governance visibility. Use risk-based scoring to prioritize remediation work, and refresh your metrics quarterly to reflect evolving threats and user behavior. Finally, collect qualitative feedback from users to fine-tune the deployment experience and improve adoption.
Real-World Guidance: Choosing a Path Forward
The pro vs default password decision is not binary; it often requires a pragmatic blend. For legacy environments with devices that cannot be updated quickly, maintain controlled defaults while accelerating a parallel password manager upgrade for accessible assets. In parallel, invest in policy development, user education, and automated monitoring to reduce risk exposure. The most resilient posture combines strong password management with ongoing awareness of evolving threats, regular audits, and a culture that prioritizes security as a shared responsibility.
Comparison
| Feature | Pro Password Management (Password Manager) | Default Passwords (Factory Credentials) |
|---|---|---|
| Security model | Centralized vault with encryption; supports MFA and RBAC | Static credentials; broadly known; limited controls |
| Storage & Sync | Encrypted vault; cross-device sync; regular rotation | Stored in devices/firmware or vendor portals; limited syncing |
| Recovery & Reset | Self-service recovery with MFA; breach alerts; admin recovery options | Reliant on device defaults; often lacks streamlined recovery |
| Onboarding & Adoption | Policy-driven onboarding; guided prompts; enterprise-grade controls | Low friction for initial use; high risk if not updated |
| Audit & Compliance | Detailed logs; RBAC; breach notifications; easy reporting | Limited visibility; inconsistent logs; difficult audits |
| Cost & Value | Subscription/licensing with scalable security value | Low upfront cost but long-term risk; hidden remediation costs |
| Best For | Organizations needing scalable security, governance, and clear audits | Legacy environments with devices that cannot be updated quickly |
Upsides
- Reduces reliance on shared or default credentials
- Improves password hygiene with unique, strong passwords
- Enhances auditability and policy enforcement
- Streamlines onboarding and incident response
The Bad
- Subscription or licensing costs; vendor dependence
- Setup complexity and user training requirements
- Risk of vault compromise if master credential breached
- Some legacy systems may have limited integration
Pro password management generally outperforms default credentials for security and control
Adopting a password manager provides scalable security, better governance, and faster incident response. Default passwords persist as a risk, especially in legacy devices and offline systems.
Your Questions Answered
What is a default password and why is it risky?
A default password is a factory-set credential that often appears across devices and services. It’s widely documented, easy to discover, and frequently reused. Attackers can exploit these defaults to gain unauthorized access, compromising networks and data. Replacing defaults with unique credentials dramatically reduces breach risk.
Defaults are easy to guess and can expose many devices. Replace them with strong, unique passwords managed securely.
What is a password manager and how does it compare to using default passwords?
A password manager securely stores credentials in an encrypted vault, generates strong passwords, and enforces access controls. Compared to defaults, managers reduce reuse, enable auditing, and simplify rotation. They are central to scalable security in modern environments.
Password managers store and protect credentials, replacing weak defaults with strong, unique ones.
Are there scenarios where default passwords cannot be replaced immediately?
Yes. Some legacy devices or offline systems cannot be updated quickly. In such cases, document the risk, isolate affected assets, and plan a staged transition to a password manager as devices can be replaced or firmware updated.
Legacy devices may require a staged approach to move away from defaults.
How do I start migrating from default passwords to a password manager?
Begin with an inventory of all defaults, assess risk, and define a rollout plan. Pilot in non-critical areas, train users, and enforce MFA. Sunset default credentials as you update each device or service.
Start with inventory, pilot, train users, and sunset defaults gradually.
What are common pitfalls when adopting password managers?
Key pitfalls include insufficient governance, weak master passwords, poor MFA coverage, and lack of user training. Mitigate by establishing policies, enforcing strong master credentials, and providing ongoing user education and support.
Avoid weak masters and poor governance; invest in training and policy.
Key Takeaways
- Adopt password managers to eliminate default credentials
- Plan a phased migration with risk assessment
- Enforce MFA and strong master passwords
- Maintain detailed audit trails and policy controls
- Address legacy devices with a clear migration timeline