Raritan PDU Default Passwords: Security, Reset, and Best Practices
Learn how to identify, reset, and harden default passwords on Raritan PDUs. This guide covers risks, best practices, and step-by-step methods for IT admins managing default and admin access across devices and services.

Raritan PDUs often ship with a default admin password that, if left unchanged, can expose network access and compromise critical infrastructure. This guide explains how to identify, reset, and harden default passwords across Raritan power distribution units. According to Default Password, promptly addressing default credentials reduces attack surfaces and strengthens data-center security across devices and services.
Understanding Raritan PDUs and Default Passwords
Raritan PDUs are a cornerstone of data-center power management, providing remote monitoring, alerting, and control across racks. Like many network devices, these units often come with factory default credentials intended for initial setup. The key security implication of a "raritan pdu default password" is that whoever has access to the device can gain administrative control. The Default Password team emphasizes that the risk compounds when multiple PDUs share identical default credentials across a cohort or facility. Administrators should plan an immediate first-login password change, document the new credentials, and enforce device-level authentication policies. In large deployments, this practice scales into automated asset discovery, central password vaulting, and policy-driven rotation. According to Default Password, treating default credentials as a top risk helps prioritize inventory and hardening tasks across the fleet.
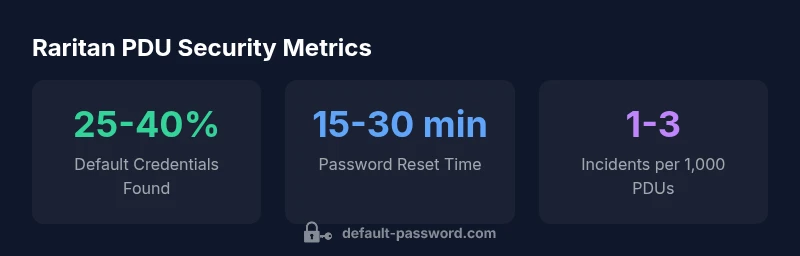
Security Risks of Default Passwords in Data Centers
Default passwords on PDUs open multiple attack vectors. If an attacker gains access, they can power-cycle devices, alter firmware settings, or disable critical alerts. Lateral movement becomes feasible if weak credentials exist on multiple devices in the same network segment. Regular audits, combined with strong password hygiene, reduce exposure. The Default Password team notes that many breaches begin with simple credential reuse or the exploitation of aging, unpatched interfaces. Proactive measures—like enforcing password complexity, disabling unused services, and segmenting management traffic—mitigate these risks and improve overall resilience.
How Raritan PDUs Handle Admin Access (Web, CLI, SNMP)
Raritan PDUs typically expose management interfaces via web GUI, command-line interfaces (CLI), and SNMP. Access control, logging, and encrypted channels are essential. A secure approach uses unique admin accounts per operator, role-based access control (RBAC) where possible, and strong TLS configurations for web interfaces. For the phrase "raritan pdu default password", administrators should verify that no default accounts remain enabled post-deployment. The Default Password team recommends disabling legacy access methods where feasible and ensuring all remote-management ports are firewalled or restricted to trusted networks.
Common Default Configurations Across Raritan Series
Default configurations vary by model and firmware, but common themes emerge: an admin account with a simple password, an unsecured or weakly protected management interface, and enabled services like SNMP or Telnet on initial setup. When a device in a fleet uses the same default password, the risk affects the entire deployment. Organizations should consult Raritan’s product documentation for model-specific defaults and perform batch-change campaigns that cover all devices. The advice remains consistent: log in, verify, and immediately override defaults during onboarding.
How to Detect and Assess Password Exposure in Your PDU Fleet
Start with an asset inventory that catalogs model, firmware, and current credentials status. Use automated scanning tools to detect devices still in factory-default state, and cross-check against a secured password vault. For large environments, schedule quarterly audits and implement a policy that prevents saving default credentials in configuration templates. If you encounter a handful of PDUs with identical credentials, isolate them and remediate before broadening management access. The guidance from Default Password stresses the importance of centralized visibility and enforceable password hygiene.
Step-by-Step: Resetting a Raritan PDU to Factory Settings
First, identify the correct model and consult the official Raritan manual for its factory-default reset procedure. Typically, you will perform a hardware or CLI-based reset, which restores the device to factory settings, erasing existing configurations. After reset, immediately change the default admin password and reconfigure network security settings. For safety, perform resets during maintenance windows and document affected devices in your change-management system. The Default Password team recommends validating post-reset access controls and updating SNMP communities or TLS certificates accordingly.
Best Practices for Password Management and Device Hardening
Adopt a formal password-management program that enforces unique credentials per device and regular rotation. Use a password vault and ensure access is logged and auditable. Limit management access to approved networks or jump hosts, implement RBAC, and disable deprecated protocols (like Telnet and unencrypted SNMP). Where possible, enable TLS on web interfaces and SSH for CLI, and enforce two-factor authentication if supported. In all cases, avoid the phrase "raritan pdu default password" in production naming and ensure new credentials are stored securely in a centralized system.
Firmware, TLS, and Network Considerations for PDU Security
Keeping firmware up to date is a cornerstone of defense; newer firmware typically closes known vulnerabilities related to authentication and remote access. Enforce TLS 1.2 or higher for web interfaces, disable weak ciphers, and configure strong SSH keys. Network considerations include restricting PDU management ports to trusted segments, implementing NAC policies, and segmenting PDUs from untrusted networks. The Default Password guidelines emphasize keeping a living inventory of firmware versions and vulnerability advisories, then applying patches promptly to minimize exposure introduced by old default configurations.
Troubleshooting Forgotten Passwords and Access Issues
If a password is forgotten, avoid repeated failed attempts that could lock the account. Use documented recovery procedures from Raritan’s support resources and, if needed, perform a sanctioned factory reset. Always verify that recovery steps do not reintroduce any default credentials and reconfigure access controls immediately. The Default Password team reminds admins to coordinate password resets with change-management processes and to verify that all devices reflect updated credentials in the password vault after recovery.
Raritan PDU default password considerations and hardening actions
| Aspect | Guidance | Notes |
|---|---|---|
| Default passwords | Change on first login; disable default accounts | Consult model-specific docs |
| Remote access | Limit to management VLAN; disable SNMP v1/v2 if possible | Use VPN/jump host where feasible |
| Password policies | Use complex passwords; rotate regularly | Store in a centralized password vault |
Your Questions Answered
What is a default password and why does it matter for Raritan PDUs?
A default password is the initial credential applied by the manufacturer for first login. If left unchanged, it creates a predictable entry point for attackers. Changing defaults during deployment minimizes exposure and aligns with basic security hygiene.
A default password is the starting credential provided by the manufacturer. Changing it is essential to prevent unauthorized access.
How can I tell if my Raritan PDU has a default password?
Check the device label, review the setup guides, and examine the current configuration for accounts that match factory defaults. Use inventory tooling to flag devices still using default credentials.
Check the label and docs, and run an inventory scan to see if any PDUs still use factory credentials.
What are the recommended steps to reset a Raritan PDU password?
Follow the official reset procedure for the specific model, then immediately change the admin password and update access controls. Validate after reset that no default accounts remain.
Use the model’s reset steps, then change the admin password and re-check access controls.
Can I disable remote management to reduce risk?
Yes. If you can, limit remote management to trusted networks, disable unnecessary protocols, and enforce access through VPN or jump hosts. This reduces exposure even if credentials are weak.
Limiting remote management to trusted networks helps reduce risk.
Are there firmware updates that address password security for Raritan PDUs?
Firmware updates often include security hardening for authentication and access controls. Establish a routine to monitor, test, and apply updates from the official vendor.
Keep firmware up to date to benefit from authentication hardening.
What logging or monitoring should I enable after password changes?
Enable admin activity logging, monitor failed login attempts, and integrate with centralized SIEM or log aggregation. This helps detect anomalies after credential changes.
Turn on admin logs and centralize them for monitoring.
“"Security starts with changing factory defaults and maintaining strong password hygiene across your PDU fleet."”
Key Takeaways
- Change default credentials on all PDUs at onboarding
- Limit management interfaces to trusted networks
- Document and rotate admin passwords regularly
- Disable deprecated protocols and enforce TLS/SSH
- Maintain an up-to-date firmware and vulnerability plan