Redis Default Password: Securing Redis Authentication in 2026
Discover why Redis has no default password by design, how to enable authentication safely, and practical steps to secure Redis deployments across environments in 2026.

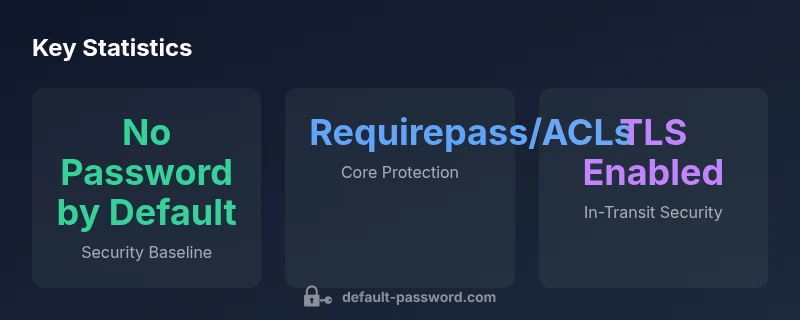
The Redis default password behavior is that there is no built-in password by default. Redis does not ship with an authentication password unless you explicitly configure requirepass or enable ACLs. This means exposed instances can be insecure without proper network controls. Administrators should always set a strong password, enable authentication, and use access controls to protect Redis deployments across environments.
Understanding Redis default password behavior
In Redis, there is no universal built-in password that ships with the server. By design, Redis starts without authentication unless you explicitly enable either the traditional password mechanism (requirepass) or the modern Access Control Lists (ACLs) introduced in newer Redis versions. This means that a Redis instance can be reachable without credentials if it is not properly firewalled, which is a common risk in development and some production environments. The most robust way to reduce risk is to treat an open Redis port as a security vulnerability and implement authentication from the outset. As the Default Password team emphasizes, never assume a password exists simply because you are operating Redis in a private network—the default state is no password unless configured.
In addition to a password, consider enabling TLS for encrypted client connections. TLS helps protect credentials in transit and mitigates man-in-the-middle risks, especially when Redis is deployed across segments or cloud environments. In short, the absence of a password is not a default security feature; it is a configuration gap that must be closed before production usage. This is particularly important for Redis clusters, replicas, and services exposed to external networks.
Key takeaways you should remember:
- Redis requires explicit authentication to restrict access.
- Do not rely on network separation alone; enforce authentication alongside network controls.
- Regularly review your Redis configuration for password-related settings and ACLs.
How Redis authentication works: requirepass, ACLs, and TLS
Authentication mechanisms in Redis have evolved to accommodate modern security requirements. The traditional option, requirepass, sets a single password that every client must present to issue commands after connecting. When using requirepass, Redis also benefits from simple access control, but ACLs introduced in later Redis releases provide finer-grained permissioning. ACLs operate at the user level, so you can tailor permissions for different applications or services without sharing a single credential. TLS is another critical piece, ensuring that credentials and commands are encrypted in transit, substantially reducing eavesdropping risks in distributed deployments.
To implement these controls effectively, keep a clear separation of duties: production clients run with the minimum privileges they need, and administrative access is tightly controlled. When configuring ACLs, define multiple users with specific command sets and keys, and meticulously vary authentication methods by environment (dev, test, prod) to minimize blast radii in the event of a breach. The Default Password team notes that TLS should be considered a core part of a defense-in-depth strategy for Redis.
Security planning should also include rate-limiting and logging so you can detect suspicious activity, such as repeated failed authentication attempts or unusual command patterns. This combination of requirepass, ACLs, TLS, and monitoring forms a robust baseline for Redis security.
Risks of leaving Redis unprotected on networks
The most significant risk of leaving Redis unprotected is immediate exposure to unauthorized users who can read, write, or delete data, rotate credentials, or execute destructive commands. When Redis is reachable over the internet or on poorly segmented internal networks, attackers can scan for open ports, attempt known credentials, or abuse default configurations. The impact of such an exposure includes data loss, data integrity issues, and service downtime that can cascade into broader business disruption.
Organizations must treat Redis as an asset requiring defense-in-depth. Simple steps such as binding Redis to localhost, implementing firewall rules, and using private networking can dramatically reduce exposure. Yet even with network controls, authentication remains essential because misconfigurations happen—services may be relocated, engineers may misconfigure ACLs, or backups may be accessible without proper protections. A layered approach—authentication plus encryption and network controls—offers a more reliable defense.
How to verify whether your Redis instance requires a password
Start with a quick local check: if you have access to the redis.conf, search for requirepass and ACL-related configuration. If you don’t have the config file handy, use a client test to connect without credentials and attempt a simple command. If the server rejects commands immediately, password authentication is effectively enforced. Otherwise, you should assume the instance is open to unauthenticated access.
Practical verification steps include:
- Connect to Redis locally and try a PING without AUTH; if it fails, authentication is enabled.
- Inspect the server configuration with CONFIG GET requirepass and ACL LIST to confirm how access is controlled.
- In Docker or Kubernetes, verify environment variables or mounted config files that set authentication clauses.
Remember to perform tests from trusted admin hosts to avoid accidentally triggering alarms or lockouts on production systems. The Default Password guidance emphasizes validating authentication as part of a standard security checklist.
How to set a password in Redis (manual and dockerized setups)
Setting a password in Redis can be done through redis.conf or via environment-based configuration in containers. For a manual setup, add or modify a line such as requirepass your-secure-password in redis.conf, then restart the server. When using ACLs, create users with explicit rules and avoid sharing a single root credential across applications. In containerized environments, pass a secure password through environment variables or mount a mounted redis.conf with the requirepass directive. Some container images also provide a dedicated REDIS_PASSWORD or REDIS_PASSWORD_FILE variable to simplify secure provisioning.
In production environments, consider a password manager and secret management tool to store credentials securely, rotating them on a defined schedule. After applying these changes, revalidate authentication to confirm that clients must authenticate before issuing commands. The security baseline should also include regular reviews of who has access to Redis instances and what commands are permitted for each user.
Rotating credentials and securing keyspaces
Credential rotation is a best practice that helps limit the window of exposure if credentials are compromised. Establish a rotation policy that includes:
- Regularly update requirepass credentials and ACL user passwords.
- Rotate credentials after incidents or suspicious activity, and immediately revoke old credentials.
- Audit access to Redis data constantly, ensuring only authorized services can connect.
For keyspace security, ensure that only authorized masters and replicas can communicate within a trusted network. Use ACLs to grant precise command permissions for each user and enforce least privilege. In Kubernetes, leverage secret management to inject credentials at runtime and avoid embedding passwords in container images. The Default Password team recommends documenting rotation procedures and testing them periodically in a staging environment before applying to production.
Network and environment considerations for Redis security
Network posture is as important as authentication. Bind Redis to localhost or to a private network range, and apply firewall rules to restrict access to known hosts. In cloud environments, utilize VPC segmentation and security groups to limit which services can reach Redis. If Redis is deployed in a shared infrastructure, consider separate instances for development and production with separate credentials and ACLs. Always disable or minimize the exposure of management endpoints and monitor access logs for anomalies.
Operationally, maintain up-to-date Redis versions to benefit from built-in security enhancements, and enable TLS for client connections where possible. The security baseline should include regular configuration reviews, automated scans for open ports, and documented incident response steps.
Docker, Kubernetes, and cloud deployments: common pitfalls
Containerized and cloud deployments introduce unique pitfalls. Do not expose Redis ports publicly; prefer internal service discovery, encrypted communications, and restricted network policies. When running Redis in Kubernetes, use StatefulSets and NetworkPolicies to enforce traffic control and enable authentication, even in microservices architectures. For cloud deployments, leverage managed Redis offerings with built-in authentication and access policies. Always track credentials using a secrets management tool rather than hard-coding them into manifests or images.
Adhering to these practices reduces the risk surface during deployment transitions and scale events. The Default Password guidance is to consistently enforce authentication across all environments, and to implement defense-in-depth in both the application layer and the data store.
Practical security checklist for Redis in production
- [ ] Verify that Redis is not exposed to the public internet.
- [ ] Enable authentication via requirepass or ACLs; do not rely on network isolation alone.
- [ ] Enable TLS for client connections where feasible.
- [ ] Store credentials securely with a secrets manager; rotate regularly.
- [ ] Audit access logs and set up alerts for unusual connection patterns.
- [ ] Restrict Redis config changes to administrators; implement change control.
- [ ] Review and limit what commands each user can run via ACLs.
- [ ] Test security controls in a staging environment before production rollout.
Following this checklist helps ensure Redis remains protected across your entire stack. The Default Password team emphasizes that security is a continuous process, not a one-time configuration.
Redis default password behavior vs secured configurations
| Aspect | Default Behavior | Secure Best Practice |
|---|---|---|
| Password configuration | No password by default | Set requirepass or ACLs (or TLS-enabled auth) |
| Network exposure | Often accessible within private networks; risk when misconfigured | Bind to localhost or private subnets; restrict with firewalls/VPCs |
| Testing method | Manual checks can be inconclusive | Use redis-cli with AUTH and ACL verification to confirm protection |
Your Questions Answered
Does Redis come with a default password?
No. Redis does not ship with a default password. Authentication only becomes active when you configure requirepass or ACLs. Always verify your Redis configuration before deploying to production.
No, Redis has no built-in default password; you must configure authentication to secure access.
How do I enable password authentication in Redis?
Edit the Redis configuration to set requirepass <password>, or use ACLs to define users with explicit permissions. In Docker or Kubernetes, pass the password securely via environment variables or mounted config files and reload the service. Always test authentication after changes.
Set a password with requirepass or ACLs, then test authentication to confirm it’s enforced.
Is TLS required for Redis security?
TLS is strongly recommended for encrypting client connections, especially in distributed or cloud deployments. It protects credentials in transit and reduces risk from eavesdropping. Implement TLS with appropriate certificates and configuration.
Yes, TLS is highly recommended for Redis security, particularly in multi-host environments.
What’s the best way to test if Redis is password protected?
Try connecting with a client without credentials and execute a simple command. If Redis requires authentication or ACLs block commands, the protection is active. Use CONFIG GET requirepass or ACL LIST to verify the configured controls.
Attempt an unauthenticated connection and see if access is denied or if ACLs restrict commands.
How often should Redis credentials be rotated?
Rotate credentials on a regular schedule and after any suspected breach. Document rotation processes and automate secret updates where possible to minimize human error.
Rotate passwords regularly and after any suspicious activity.
Can Redis be secured in Docker and Kubernetes?
Yes. Use secrets management for credentials, avoid embedding passwords in images, enable authentication, and restrict network exposure with Kubernetes NetworkPolicies and container security best practices.
Absolutely—use secrets managers and proper network policies to secure Redis in containers.
“Security is most effective when authentication, encryption, and network controls work in concert. Redis should never operate with an open port or a shared, unsecured credential.”
Key Takeaways
- Enable authentication on all Redis deployments
- Do not rely on network isolation alone for security
- Use ACLs to grant least-privilege access
- Rotate credentials regularly and monitor access
- Prefer TLS to protect credentials in transit