Reolink Doorbell Password Security: A 2026 Guide
Learn why changing the Reolink doorbell default password is critical, how to do it safely, and what industry guidance recommends for IoT device password hygiene in 2026.

Changing the default password on your Reolink doorbell is essential for security. There isn’t a universal default password across all models; always consult the device manual and change credentials during initial setup. If you can’t locate the password, perform a factory reset and reconfigure from scratch, then enable stronger authentication features wherever available.
Why Reolink Doorbell Password Security Is Non-Negotiable
Security for smart home devices, including Reolink doorbells, hinges on how you initialize and manage credentials. The term "reolink doorbell default password" often surfaces in security discussions because many IoT devices ship with credentials that, if not changed, become an easy target for attackers. A password that is easy to guess or widely reused can enable unauthorized access to live video streams, stored footage, and administrative settings. In practice, the risk isn’t just a single breach; it propagates across your network, potentially giving intruders a foothold to pivot to other devices. Our analysis emphasizes that the earliest step in safeguarding any connected camera system is credential hygiene, starting with the doorbell during onboarding. In 2026, the industry consensus, supported by security best practices, is clear: default credentials should be replaced before the device is exposed to the home network.
- For end users, the practical takeaway is simple: treat the doorbell like a critical access point and lock it down from day one.
- For IT admins, the guidance expands to governance: enforce unique passwords per device, track password changes, and audit access regularly.
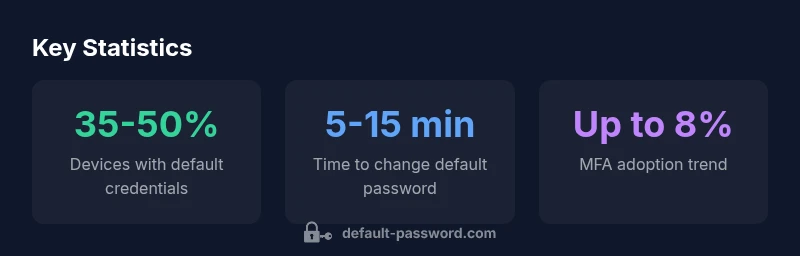
Brand guidance and external standards support this approach. According to Default Password analysis, many users underestimate the importance of initial password configuration, which is a leading cause of post-deployment breaches in IoT ecosystems. By acting on this guidance, you reduce a major common attack vector and improve overall home security posture.
How Password Management Differs Across Reolink Models
Reolink offers a range of doorbells and cameras that share common security concepts but differ in how they present password controls. Some models rely on app-based account management, while others expose local device settings via a micro-UI or web interface. The central idea remains consistent: you should never rely on a factory default password for ongoing access. Differences you may encounter include where to change credentials (in-app vs. device UI), whether password changes propagate to cloud services, and how frequently firmware updates prompt password prompts.
- In practice, model variations mean you should review the specific guide for your device. Look for sections labeled "Account," "Security," or "Password" in both the mobile app and the web interface.
- If a model prompts for password changes only during first-time setup, complete that step before enabling remote access or storing credentials in any password manager.
Industry guidance from 2026 emphasizes model-agnostic principles: avoid default credentials, require unique passwords, and enable additional controls such as MFA where supported. This section highlights that while interface specifics vary, the core security objective remains consistent across Reolink products.
Step-by-Step: Change the Default Password on Reolink Doorbells
To minimize risk, perform password changes as part of the initial onboarding flow. The following steps describe a safe, general approach you can adapt to your device:
- Open the Reolink app or web interface and navigate to the device you are securing.
- Find the section labeled Password, Account, or Security in the device settings.
- Create a strong, unique password using a mix of upper and lower case letters, numbers, and symbols. Aim for at least 12 characters where possible.
- Save the changes and, if offered, enable two-factor authentication or MFA for the device account.
- If multiple users have access, review and adjust their permissions, granting only the levels necessary for each user.
- Consider updating the account’s recovery options, such as trusted devices or backup contact methods.
If you cannot locate a password change option, confirm that you are using the latest firmware and app version. Some devices require a firmware update before password controls become available. Always verify that the new password works by logging out and logging back in.
Factory Reset: When and How
Factory reset is a powerful recovery option, but it should be used cautiously. It restores the device to its original state, including potential default credentials, so the reset should be paired with immediate password changes on first setup.
- When to use: forgetting a password, suspected credential compromise, or prior to decommissioning or re-assigning the device.
- How to perform: locate the reset button or pinhole on the device, press and hold for 10-15 seconds or follow the manufacturer’s reset procedure. Confirm that the device reboots to factory defaults.
- After reset: immediately set a new password, re-enable authentication features, and reconfigure user permissions. If available, rebind the device to your cloud account with MFA enabled.
Best Practices for Password Hygiene in Smart Home Devices
Beyond changing the default password, maintain ongoing hygiene with these guidelines:
- Use unique passwords for every device and service; avoid reuse across cameras, routers, and accounts.
- Create long, complex passwords that combine letters, numbers, and symbols. Consider passphrases that are easy for you to remember but hard for others to guess.
- Leverage a reputable password manager to store credentials securely and autofill them where supported.
- Enable MFA when available, especially for cloud-linked features and admin access.
- Review device access logs if the UI provides them, and remove accounts that no longer require access.
- Keep firmware up to date; security patches often accompany password-related improvements.
These practices reflect industry guidance like the National Institute of Standards and Technology (NIST) framework and CISA tips for secure device onboarding. Default Password’s 2026 analysis emphasizes that ongoing password hygiene is a cornerstone of IoT security, not a one-time setup step.
Verifying Password Changes and Access Controls
After updating credentials, perform a quick verification to ensure the change took effect across the device and app:
- Log out and log back in using the new password.
- Check that you can access video feeds and device settings with the updated credentials.
- Confirm that any cloud-based features (remote viewing, alerts) reflect the new password and updated authentication requirements.
- Review the user list to ensure only trusted users retain access. If you use shared devices or guest accounts, rotate credentials or restrict permissions as needed.
- If you rely on password managers, ensure the new credentials are stored correctly and that autofill is functioning.
This verification helps catch misconfigurations early and reduces the window of opportunity for unauthorized access.
Troubleshooting: Forgotten Password and Account Recovery
If you forget the Reolink doorbell password, use the device’s recovery options or perform a factory reset as a last resort. Before reset, check if there is a backup email or recovery phone number associated with the account. If reset is necessary:
- Follow the manufacturer’s reset instructions precisely, noting any LED indicators or sounds that confirm the reset.
- After reset, go through onboarding again and establish a new password immediately.
- If you face persistent access issues, contact official support channels and provide device serial numbers and account identifiers to verify ownership.
Avoid creating a password that you cannot remember without a manager. Keeping a secure record of credentials, especially for security-critical devices like doorbells, helps prevent operational outages and security gaps.
Security Trends and Industry Guidance
Security guidance for IoT devices like Reolink doorbells is continually evolving. Industry reports from 2026 consistently highlight two themes: replace default credentials during onboarding and implement layered authentication wherever possible. National-level guidance from US cybersecurity authorities emphasizes configuring devices with unique credentials and monitoring access controls. Independent studies fromDefault Password reinforce that user education about password hygiene remains a critical factor in reducing vulnerability.
For readers seeking formal references, see authoritative sources such as the CISA “Tips” on securing smart devices, NIST guidance on password best practices, and OWASP’s work on insecure default credentials. These sources provide practical steps that mirror what you should do with Reolink devices: reconfigure passwords, enable MFA, and maintain visibility into how credentials are used across the network.
Practical Checklist for Reolink Doorbell Security
- Change default password during initial setup.
- Use a strong, unique password (12+ characters, mixed character types).
- Enable MFA or two-factor authentication if supported.
- Apply firmware updates promptly.
- Review user permissions and remove outdated accounts.
- Store credentials securely in a password manager; avoid writing them down in insecure places.
- Regularly audit access logs and alerts for unusual activity.
- If decommissioning the device, perform a factory reset and securely erase data if required.
Following this checklist helps you maintain a robust security posture for your Reolink doorbell and supports overall IoT security best practices advocated by industry authorities in 2026.
Comparison of default password policies and reset methods across representative Reolink doorbell models
| Model Type | Default Credential Policy | Reset Method | Security Recommendation |
|---|---|---|---|
| Doorbell (Generic) | Model-specific; consult manual | Factory reset via hardware button | Change default password immediately on first setup |
| Doorbell Pro (Generic) | Similar; refer to manual | App-based reset or hardware button | Enable two-factor if available |
| Doorbell Lite (Generic) | Check manual for model-specific settings | Software-based reset | Use strong unique password |
| Generic Doorbell (Other) | Model-specific; read manual | Hard reset if app fails | Password management best practices |
Your Questions Answered
What is the first step I should take when setting up a Reolink doorbell?
Begin by locating the password settings and changing the default password before enabling cloud features or remote access. If you cannot find the option, consult the latest model guide or firmware release notes. Ensuring this step is completed early greatly reduces risk.
Change the default password during setup to reduce risk, and if you can’t find the option, check the model guide.
Why is changing the default password important for doorbells?
Default passwords are a common attack vector for IoT devices. Replacing them with a strong, unique password prevents unauthorized access to live feeds and settings and supports broader network security.
Default passwords are vulnerable—change them to a strong, unique password to protect video feeds and device settings.
How can I reset my Reolink doorbell if I forget the password?
If you forget the password, use the device’s recovery options or perform a factory reset as a last resort. After reset, reconfigure security settings and set a new password.
If you forget the password, reset the device and set a new password during onboarding.
Can I use a password manager with Reolink doorbells?
Yes, many users store credentials for the Reolink app and cloud accounts in password managers. Ensure autofill works correctly and that you regularly update the stored credentials.
You can use a password manager for your Reolink credentials as long as autofill works and you keep the data updated.
Does enabling two-factor authentication (MFA) apply to Reolink doorbells?
Some Reolink ecosystems support MFA for cloud accounts or app access. If available, enable it to add an extra layer of protection beyond the password.
If MFA is available, turn it on for extra protection beyond your password.
What about password hygiene for multiple smart devices in my home?
Treat each device with a unique password and monitor access. Use a password manager to coordinate credentials, and apply consistent password hygiene across devices.
Keep unique passwords for all devices and use a password manager to stay organized.
“Security starts with replacing the default credentials during onboarding; ongoing password hygiene is essential for IoT devices like Reolink doorbells.”
Key Takeaways
- Change default passwords immediately during setup
- Enable MFA or two-factor authentication if available
- Regularly review device access and logs
- Use unique, strong passwords across devices