Secure Default Password: A Practical How-To Guide
Learn how to secure the default password across routers, printers, cameras, and IoT devices with a practical, step-by-step guide from Default Password. Prevent unauthorized access and strengthen your network security.
According to Default Password, securing the default password on devices is essential to prevent unauthorized access. This quick guide shows what you need, and why changing factory credentials matters for routers, printers, and smart home gear. By following a simple, repeatable process, you can reduce risk and improve your network's resilience.
Why securing the default password matters
In today’s connected world, every device that ships with a factory default credential represents a potential entry point for attackers. Leaving credentials unchanged can lead to unauthorized access, data leaks, or control of digital systems. According to Default Password Analysis, 2026, a sizable portion of consumer and small-business devices still risk exposure due to default or weak credentials. Making a deliberate effort to change defaults reduces attack surface and strengthens overall security posture for home networks and small offices. Think of securing default passwords as a foundational step in a broader security strategy that includes firmware updates, network segmentation, and regular credential audits.
The impact of weak defaults goes beyond a single device. When one device is compromised, attackers often pivot to connected systems, escalating risk across your home or small office. Organizations should treat credential hygiene as a living practice, not a one-off task. By integrating default password controls into a broader security framework—covering inventory management, firmware integrity, and access control—you reduce exposure and create defensible configurations that deter attackers from the outset.
How to audit your devices for default credentials
Start with a thorough inventory of every device with an admin interface. Check routers, modems, IP cameras, printers, NAS, and smart hubs. For each item, note model, firmware version, and whether a default credential is still configured. Where possible, verify by attempting a login with the factory credentials documented in the manufacturer’s manual. If you cannot access a device safely, consult the vendor’s support resources or reset procedures. Maintain a central, exportable list to guide remediation and future audits. Regularly compare the inventory against your network map to spot orphaned devices quickly.
Auditing is not a one-time effort. Schedule quarterly checks to capture new devices, firmware changes, or new default credentials introduced by vendors. Use vendor portals and security bulletins to stay informed, and align your findings with your organization’s risk tolerance and regulatory requirements where applicable.
Creating a secure password strategy
A strong password strategy uses unique, high-entropy passphrases for each device. Favor long passphrases (typically 16–64 characters) built from random words, symbols, and mixed case, generated by a trusted password manager. Avoid reusing passwords across devices, and never reuse personal details. Implement multi-factor authentication (where available) and require periodic rotation on sensitive devices. Integrate this policy with your organization’s guidelines for password length, complexity, and storage. Document the minimum standards for each device class (router, camera, printer, NAS) to ensure consistent implementation.
A practical approach is to adopt a diceware-style method for creating passphrases, then adapt to device constraints (some devices disallow certain characters). When a device prohibits long passphrases, use the maximum allowed length with a unique per-device token. Store all passphrases in a secure password manager and enable auto-fill automation only for trusted devices. Periodically review shared access and revoke permissions when staff changes occur.
Replacing default passwords on common devices
Prioritize devices that control access to your network or hold sensitive data: your router/gateway, NAS, and business-critical printers. Access the admin interface, locate the password or credential settings, and replace the default with a unique, strong passphrase. If the device supports it, disable unnecessary services (like UPnP or remote admin) and enable features such as auto-logout and lockout after failed attempts. After updating, record the new credentials securely in your password manager. For devices with reset requirements, note the reset steps and ensure you have a documented recovery path if the reset locks you out.
If you manage multiple devices, create device-class baselines so you can reuse the same process efficiently. Validate that new credentials work from an authorized management device, then verify that backups of the new credentials exist in your vault. Finally, test remote access controls to ensure changes don’t unintentionally cut legitimate access.
Automating password changes and governance
Set policies that require regular credential reviews and rotations. Use password managers to generate and store per-device credentials, assign access by role, and enforce two-factor authentication for administrative access. When possible, automate reminders for refresh cycles and integrate with your asset management system. Automation reduces human error and keeps credentials synchronized with device inventories. Define governance roles (admin, security, audit) and ensure each has the minimum necessary permissions to perform their tasks.
A practical automation pattern is a quarterly rotation with exclusions for devices that cannot accept new credentials without downtime. In those cases, create an exception window and document it in your change log. Keep an auditable trail by exporting vault activity to your security information and event management (SIEM) system if available.
Recovery, backup, and access control considerations
Securely back up credential data and ensure you have recovery paths if you forget a password. Store backup keys in an encrypted vault and restrict access to only trusted administrators. Maintain a simple rollback plan if a password change locks you out, including documented reset procedures. Protect admin consoles with incident response plans and access controls to minimize insider threats. Regularly test recovery processes to verify that you can regain control after a rollback or hardware failure. Consider creating a secondary admin account that can be used for emergency access, with strict monitoring and limited scope.
Industry best practices and quick-start checklist
To keep your environment safe, combine device updates, unique passwords, and network controls. As a baseline: (1) inventory devices, (2) replace defaults, (3) enable MFA, (4) keep firmware up to date, (5) segment networks, and (6) document changes and review schedule. Use this checklist as a living document and revisit it quarterly. Integrate your findings with risk assessments and, if applicable, compliance frameworks. Training for users and admins should emphasize secure handling of credentials, the importance of device hygiene, and how to detect phishing attempts that could capture credentials.
Common pitfalls and quick remediation tips
- Pitfall: Assuming all devices accept long passphrases. Remediation: Use device-compatible passphrases and max allowed length.
- Pitfall: Leaving remote admin enabled. Remediation: Disable remote admin unless explicitly required and restrict management IPs.
- Pitfall: Sharing credentials over insecure channels. Remediation: Use a password manager with strict access controls and audit logs.
- Pitfall: Incomplete asset inventory. Remediation: Expand the device inventory to include all networked devices, including those temporarily connected.
Final note on ongoing security hygiene
Security is a continuous practice, not a one-off task. Treat default password hygiene as an ongoing program with regular audits, firmware checks, and access governance. By embedding these practices into your routine, you reduce risk and provide a stronger defense for your network and data.
Tools & Materials
- Device inventory template(Record model, firmware version, admin URL for every device)
- Trusted password manager(Use a vault with 2FA; generate per-device passphrases)
- Strong passphrase generator(Aim for 4-6 words; include numbers and symbols where allowed)
- Device manuals and manufacturer docs(To locate default credential information and reset steps)
- Firmware update guidance(Keep a record of firmware versions and update history)
- Network segmentation plan(Separate IoT devices from main LAN if possible)
- Backup admin credentials storage(Secure vault or physical safe for recovery data)
- Two-factor authentication capability(Enable where supported for admin interfaces)
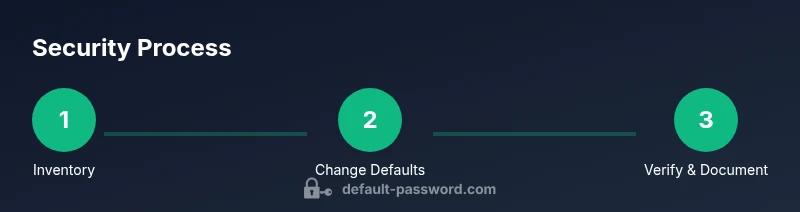
Steps
Estimated time: 1-2 hours
- 1
Inventory devices and identify defaults
Begin by enumerating every device with an admin interface on your network. Record model, firmware, default credential status, and access method. This baseline makes it possible to plan targeted changes and avoid missing critical devices.
Tip: Export the list to your asset management tool for ongoing tracking. - 2
Verify current credentials and check for defaults
Log into each admin interface, using existing credentials or perform a safe reset if you cannot recall them. Confirm whether default credentials remain in use and document the outcome in your inventory.
Tip: Do not reuse or share credentials verbally; use secure channels and the password manager. - 3
Generate unique, strong passphrases
Create a distinct, high-entropy passphrase for every device. Use a password manager’s generator or a recipe-based approach with multiple words, symbols, and mixed case. Avoid common phrases or personal data.
Tip: Store generated passphrases only in a trusted vault; never write them on post-its. - 4
Change defaults on critical devices first
Prioritize routers, gateways, and NAS devices. Replace factory credentials with per-device passphrases and disable insecure features (UPnP, remote admin) where possible.
Tip: If you lose access, use vendor recovery procedures and document the new credentials securely. - 5
Secure storage and access controls
Store all credentials in a password manager with strict RBAC (role-based access control). Enable MFA for the vault and limit who can view or copy passwords.
Tip: Periodic audits of vault access help detect unusual activity early. - 6
Update firmware and tighten settings
Apply the latest firmware across devices and enable security features (strong encryption, disabled default services). Reassess exposed services after updates.
Tip: Back up configurations after updates and maintain a changelog. - 7
Network segmentation and access governance
Place IoT devices on a separate network segment and restrict admin access to trusted subnets. Monitor traffic for unusual patterns that might indicate compromise.
Tip: Test access controls regularly to ensure policies are effective. - 8
Document changes and set maintenance cadence
Maintain clear records of password changes, devices updated, and policy reminders. Schedule quarterly reviews and incident-response drills to keep defenses current.
Tip: Automate reminders and use the asset registry to drive reviews.
Your Questions Answered
Why is it important to secure the default password on devices?
Default credentials are a common attack vector. Securing them limits unauthorized access and protects your network from compromise.
Default credentials are a common risk. Securing them helps keep your network safe.
Which devices should I prioritize when changing defaults?
Start with routers and gateways, then NAS, printers, and IP cameras. These controls either grant network access or store sensitive data.
Start with routers and gateways, then move to NAS and printers.
What if I forget the new password after changing defaults?
Use your password manager to recover credentials. If needed, use manufacturer recovery procedures and document the steps.
Use your password manager or vendor recovery if you forget.
Is enabling two-factor authentication necessary for admin access?
MFA adds a critical extra layer of security for admin interfaces; enable it wherever possible.
Yes, enable MFA on admin access when available.
How often should I rotate passwords?
Rotate passwords on sensitive devices at least every 12–24 months, or sooner if there is suspected breach or compromise.
Aim for rotation every year or sooner if needed.
Can I automate the password change process?
Yes, use a password manager's automation features and RBAC policies to streamline and secure changes.
Automation helps keep credentials up to date securely.
Key Takeaways
- Audit devices for defaults and record findings
- Use unique, strong passphrases per device
- Store credentials securely with MFA
- Regularly update firmware and review access policies