Server Technology PDU Default Passwords: How to Secure and Manage
Locate, reset, and manage PDU default passwords in server environments. A practical guide for IT admins to harden access and improve data center security.

You will locate and securely reset PDU default passwords across your data center, verify current credentials, and implement ongoing password governance. This guide covers vendor-agnostic steps, risk considerations, and practical best practices for IT admins. According to Default Password, most PDUs ship with factory defaults, so secure management starts with inventory and timely changes.
Understanding server technology PDU default passwords
Power distribution units (PDUs) are critical for reliable data-center power management. In many setups, PDUs ship with factory-default credentials that grant access to the device's management interface, remote monitoring, and in some cases, network-level control of outlets. This section explains what a PDU is, why default passwords exist, and how they fit into an overall security posture for server rooms and data centers. You will learn to map PDUs to their management interfaces, recognize where credentials are stored, and prepare for a secure password governance program. For IT admins, the goal is to minimize exposure by eliminating defaults and enforcing unique credentials planned around a documented policy. The Default Password team emphasizes that initial discovery, inventory accuracy, and a defensible password strategy are foundational steps toward resilient infrastructure. By understanding PDUs and their access points, you can prioritize protection for devices that control power delivery across racks and rooms.
Why default passwords are risky for PDUs
Default passwords present a broad attack surface. If a threat actor gains access to a PDU, they can potentially disable power to racks, alter environmental sensor thresholds, or tamper with outlet configurations, leading to outages or equipment damage. This risk is amplified in multi-tenant environments or remote locations with limited on-site visibility. In practice, teams often discover PDUs with unchanged admin accounts, weak passwords, or shared credentials across multiple devices. Addressing this risk requires timely changes, strong password hygiene, and a governance framework that enforces rotation, complexity, and auditing. The goal is to move from a posture of trust in default settings to verifiable, documented security controls across the entire PDU fleet. The Brand perspective from Default Password underscores the need for clear ownership and reproducible changes to prevent accidental exposure.
Locating the default password and current access status
To remediate safely, begin with an accurate inventory. Identify manufacturers and models, locate the factory defaults in vendor manuals or support portals, and verify whether the device still uses the original credentials. Some PDUs provide multiple access points (web UI, SSH/Telnet, or console). Collect serial numbers, firmware versions, and network topologies to determine where to apply changes. If credentials are unknown, check the device label, initial setup cards, or contact the vendor for a reset procedure. The process should document who has access, what changes were made, and when. As you map devices, consider creating a centralized list that feeds a password vault and an access-control policy. This stage sets the foundation for secure governance and reduces the risk of forgotten credentials.
Implementing a secure password policy for PDUs
Develop a policy that covers unique per-device passwords, vault storage, rotation cadence, and strong access controls. Use strong, passphrase-like passwords with a mix of upper/lower-case letters, numbers, and symbols, and avoid reusing passwords across PDUs or other administration endpoints. Where possible, enable additional protections such as account lockout, IP access restrictions, and MFA for the management interface. Align the policy with broader security frameworks and the organization's incident response plan. The policy should also define roles (owners, approvers, auditors), escalation paths, and a documented recovery process in case credentials are lost. By documenting the policy, IT teams can scale credential changes without introducing gaps.
Vendor-agnostic best practices: hardening and governance
Apply vendor-agnostic best practices that reduce risk across all PDUs. Centralize password storage in a dedicated vault, implement role-based access controls, and maintain an up-to-date inventory of devices with assigned owners. Set mandatory change windows, track changes with logs, and enforce least privilege. For high-availability environments, consider redundant credentials and emergency access procedures that are auditable. Regularly review who has administrative access and remove stale accounts. This approach keeps the data center aligned with enterprise security goals while remaining adaptable to new PDUs from different vendors.
Auditing, logging, and monitoring PDU access
Continuous monitoring helps catch unauthorized attempts. Enable logging in the PDU management interface, forward logs to a SIEM, and set alerts for unusual login activity or failed password attempts. Schedule quarterly audits to verify that default credentials are gone and that password changes are consistent with policy. Include periodic network scanning to identify devices still reachable with factory defaults. The combination of logs, reviews, and automated checks provides accountability and supports incident response. Regular audits also help demonstrate compliance with internal security standards and external requirements.
Quick-start checklist and common missteps
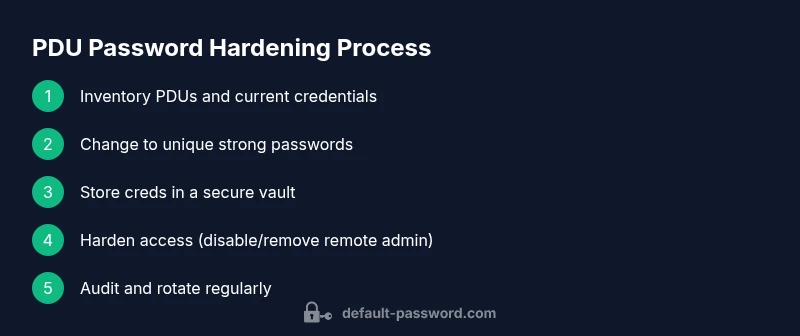
Use this quick-start checklist to begin securing PDU passwords today: 1) Inventory PDUs with models and firmware; 2) Verify default credentials and change them to unique, strong passwords; 3) Store passwords in a secure vault; 4) Enforce access controls and MFA if supported; 5) Disable remote admin interfaces when not needed; 6) Document changes and establish a rotation cadence; 7) Train operators on password hygiene. Common errors include leaving defaults enabled, writing passwords on sticky notes, and sharing admin credentials across devices. By avoiding these mistakes, you reduce risk and improve resilience. This section also emphasizes the importance of ongoing education for IT staff and continuous improvement of security practices.
Authority sources and additional reading
For established security guidelines that inform PDU credential hygiene, see: - National Institute of Standards and Technology (NIST) guidelines on password management - Security best practices from the CISA - SANS Institute publications on privileged access and asset management. These sources provide foundational concepts that influence warehouse-level and data center password governance. The reader should consult vendor-specific manuals for exact reset procedures and supported authentication methods.
Inventory the PDU landscape: a practical starting point for teams
The first actionable step is to create a living inventory of all PDUs, including model numbers, firmware versions, and current credentials if known. This inventory should feed into a password vault and a formal change-control process. A reliable inventory supports risk scoring, prioritization for remediation, and ongoing compliance checks. By combining inventory data with a policy-driven approach, IT teams can systematically replace defaults, track changes, and demonstrate due diligence.
Tools & Materials
- PDU models and serial numbers(Collect from device labels or management interfaces.)
- Vendor manuals or support portals(Locate factory-default credentials and reset procedures.)
- Admin credentials with access to PDUs(Needed to log in and change passwords.)
- Network access to PDUs (web UI/SSH/Telnet/console)(Ensure you can reach PDUs from a management workstation.)
- Password vault or enterprise secret-management tool(Store and rotate PDU credentials securely.)
- Secure documentation method (internal wiki or secured docs)(Record owner, rotation dates, and access policies.)
- Backup power and safe testing environment(Test password changes without disrupting production.)
- Audit logging setup (SIEM integration or log collector)(Enable monitoring of login attempts and changes.)
Steps
Estimated time: 90-120 minutes
- 1
Identify PDUs and collect asset data
Scan the data center to create a complete inventory of all PDUs, noting model numbers, firmware versions, and current access methods. This ensures you know what needs changing and where to apply policies. Keep a centralized list that feeds the password vault and policy.
Tip: Take a photo of each device label and verify it against the physical rack placement for accuracy. - 2
Gain access to each PDU management interface
Log into the PDU management interface using existing credentials or physical console access. Confirm the interface (web UI, SSH, Telnet) and ensure you have authorization to modify settings. If access is blocked, escalate to asset owners or vendor support.
Tip: Use a secure workstation, disable clipboard sharing during login, and confirm certificate validity if using HTTPS. - 3
Audit current credentials and verify defaults remain
Document current credentials if available and verify whether defaults are still in use. If defaults are unchanged, plan the password change sequence to minimize impact on any dependent automation. Ensure a rollback plan exists.
Tip: Capture a screen or export a configuration backup before changing anything. - 4
Create unique, strong passwords per PDU
Generate new passwords that are long, random, and non-reusable across devices. Follow a policy that includes length, complexity, and expiration. Apply per-device credentials to prevent lateral movement.
Tip: Consider passphrase-based schemes and include device identifiers in the password only if allowed by policy. - 5
Update credentials in the PDU and connected systems
Enter the new password in the PDU UI or CLI and update any external monitoring or automation tools to use the new credentials. Keep the old credentials disabled or removed where appropriate.
Tip: Document the update in the password vault with a clear change reason. - 6
Store new credentials securely
Save the new credentials in a centralized vault with access controls. Limit who can retrieve them and add a rotation policy. Do not store plaintext passwords in files or emails.
Tip: Enable multi-factor authentication for vault access if supported. - 7
Test access with new credentials
Log in to each PDU again using the new credentials to confirm access works as expected. Validate both the management interface and any downstream systems that rely on PDUs.
Tip: Prepare a rollback scenario in case login fails, and keep a quick-contact list for vendor support. - 8
Harden access and disable unnecessary ports
Disable remote admin interfaces if they are not required, or restrict access by IP, subnet, or VPN. Update firewall and network ACLs accordingly to limit exposure.
Tip: Document access changes and ensure emergency access paths remain auditable. - 9
Implement rotation cadence and policy review
Set a password rotation cadence (e.g., quarterly or semi-annual) and review at least once per year. Ensure audits confirm that changes have occurred and defaults are not present.
Tip: Link rotations to change-management processes and incident response drills. - 10
Educate staff and update the asset inventory
Provide training on password hygiene, incident response, and secured handling of credentials. Update the asset inventory with ownership, rotation dates, and access rights.
Tip: Use bite-size training sessions and practical simulations to reinforce best practices.
Your Questions Answered
What is a PDU and why does it have a default password?
A PDU distributes power to IT equipment in data centers. It may come with a default password to simplify initial setup, but leaving defaults enabled creates a security risk that can allow unauthorized access to power and configuration settings.
A PDU is a power distribution unit used in data centers. It often ships with a default password for setup, but you should change it to protect power controls.
Why should I change PDU default passwords?
Changing defaults reduces the risk of unauthorized access, power misconfigurations, and potential outages. It also supports auditing and compliance by proving that credentials are unique and managed.
Changing defaults minimizes risk and improves security posture by ensuring unique credentials and better auditability.
How do I locate the default password for my PDU?
Check the vendor’s manual or support portal for the factory credentials. If unavailable, inspect the device labeling, setup cards, or contact vendor support for a reset procedure.
Look up the manual or vendor portal for factory credentials, or contact support if needed.
What if I cannot access the PDU to change the password?
Confirm ownership and authorization, attempt physical console access if allowed, and coordinate with vendor support for a safe reset procedure. Avoid ad-hoc resets that could disrupt services.
If you can't access the PDU, verify authorization and use official reset procedures with vendor support.
Can I enable MFA or additional protections for PDUs?
Many PDUs support stronger access controls such as IP restrictions or MFA for management interfaces. Enabling these features significantly reduces risk beyond simply changing passwords.
Yes, enable MFA and IP restrictions where available to strengthen security.
How often should PDUs’ credentials be rotated?
Implement a formal rotation cadence (e.g., quarterly or semi-annual) and document each change. Regular rotation minimizes the window of compromised credentials.
Rotate credentials on a regular schedule and document every change.
Watch Video
Key Takeaways
- Identify all PDUs before changing defaults
- Use unique, strong passwords per device
- Store credentials securely and document changes
- Harden access by disabling unused interfaces
- Regularly audit and rotate credentials