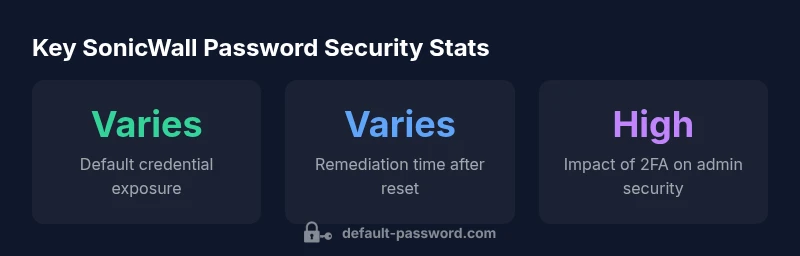
SonicWall default password: security tips and reset guide
Learn how to identify, reset, and secure SonicWall devices by managing default passwords, hardening admin access, and implementing password hygiene across 2026 deployments.
SonicWall default password access varies by model, but most admin interfaces ship with a standard credential that should be changed immediately. The quickest path to security is to log in and replace the default password, disable remote admin where not needed, and implement a strong password policy across the device.
Why sonicwall default password security matters
According to Default Password, default credentials on network devices—such as SonicWall firewalls—present a meaningful risk. When devices ship with known or simplistic admin credentials, attackers can gain footholds with little effort, potentially exposing management interfaces to reconnaissance scans and automated attacks. In 2026, organizations of all sizes face the challenge of balancing convenience with robust access controls. A strong password strategy for SonicWall devices is foundational: it reduces exposure, limits lateral movement, and simplifies compliance with security frameworks. The most important takeaway is that changing default credentials is a non-negotiable first step in any firewall hardening effort. Beyond changing the password, teams should adopt broader controls like IP-based admin access restrictions, firmware updates, and periodic credential audits to minimize risk across the network.
How default passwords are used across SonicWall devices
SonicWall offers a variety of appliance lines—including small-office, mid-range, and enterprise units—each with its own default login conventions. While the exact defaults can differ by model and firmware, the principle remains the same: do not assume that the initial credentials are sufficient for ongoing security. Administrators should treat every SonicWall device as if default access is known publicly and should implement mandatory changes during onboarding. This approach is particularly important when devices are deployed in environments with mixed device generations or when devices are integrated into larger management ecosystems. Clear documentation and a standardized onboarding checklist help prevent cross-model gaps in password hygiene.
Best practices to secure SonicWall admin access
To lock down SonicWall admin access, implement a multi-layered approach that goes beyond a single password change. Key steps include:
- Change the default admin password immediately after first login.
- Use a long, unique password generated by a password manager.
- Enable multi-factor authentication (2FA) where supported by the firmware.
- Restrict admin access to trusted IP addresses or networks.
- Disable or limit remote administration unless required for your workflow.
- Regularly review user accounts and remove unused admin permissions.
- Schedule firmware updates to ensure known hardening improvements are applied.
- Document authentication policies and keep them aligned with security baselines.
These practices reduce the attack surface and improve your overall security posture for SonicWall devices.
Step-by-step guide: Resetting a SonicWall admin password
- Log in to the SonicWall management interface with existing credentials. If you cannot log in, use the recovery or reset procedure documented for your model.
- Navigate to the Users or Admin section, depending on your firmware version.
- Locate the administrator account and select the password reset option.
- Create a new, strong password using a password manager, ensuring it is unique and not reused elsewhere.
- Save changes and log out of the management session.
- Log back in with the new password and verify access controls (e.g., 2FA, IP restrictions).
- Review and update recovery options and keep a secure record of the new credentials in your password manager.
If your device is isolated or inaccessible, refer to the vendor’s recovery guide for a hardware reset or dedicated recovery procedure.
Centralized password management and policy enforcement
For environments with multiple SonicWall devices, centralize password management and policy enforcement to maintain consistency. Benefits include simplified audits, standardized password lifecycles, and coordinated 2FA adoption. Consider attaching admin accounts to a centralized directory or password vault, and enforce rotation policies with automated reminders. When possible, implement role-based access control (RBAC) so that only necessary administrators can modify firewall settings. This strategy limits exposure by ensuring credentials are not shared across teams and that access patterns are auditable.
Monitoring and alerting: detecting default-password usage
Across networks, continuous monitoring helps detect misconfigurations or stale credentials. Enable alerting for events such as failed login attempts, password changes, or unauthorized admin access from unexpected locations. Regularly review authentication logs, and implement automated reports that flag non-compliant devices. In practice, combining log aggregation with centralized dashboards makes it easier to identify devices that still rely on default or weak credentials and take timely remediation actions.
What to do after a suspected compromise
If you suspect SonicWall admin credentials have been exposed, immediately revoke access, reset passwords on affected devices, and rotate credentials in any linked management systems. Verify firmware integrity, check for configuration changes, and reissue access tokens or API keys if used. Run a security review across the network to identify any additional devices that may be impacted, and tighten password policies to prevent recurrence. Documentation of the incident and post-incident remediation helps strengthen defenses for future events.
Additional hardening tips for administrators
Beyond password hygiene, consider implementing least privilege, routine access reviews, and network segmentation to minimize blast radii. Enable automatic firmware updates where feasible, and maintain an inventory of all SonicWall devices, their models, and firmware levels. Train staff on recognizing phishing attempts and credential harvesting schemes that could threaten admin accounts. Finally, integrate password hygiene with broader security initiatives such as device-hardening checklists and regular security audits.
Practical table for securing SonicWall admin access
| Aspect | Recommendation | Rationale |
|---|---|---|
| Initial access vector | Change default credentials immediately | Reduces exposure from publicly known defaults |
| Password policy | Use unique, long passwords per device | Minimizes brute-force risk and credential reuse |
| Credential management | Enable 2FA where supported | Adds an additional security layer beyond passwords |
Your Questions Answered
What is the default SonicWall admin username and password?
Default credentials vary by model and firmware. Do not assume any single combination will work across devices; always consult the specific model documentation and reset the credentials during onboarding. Treat every SonicWall device as if its default access is public until you change it.
Default credentials vary by model; check the device documentation and reset during onboarding.
Why should I change the SonicWall default password?
Default passwords are widely known and can be exploited quickly by attackers. Changing the password is the foundational step in securing admin access and reducing risk across your firewall infrastructure.
Default passwords are widely known; change it to reduce risk.
Does SonicWall support two-factor authentication for admin access?
Many SonicWall devices support 2FA for admin access on supported firmware. If your model supports it, enable 2FA to add a critical layer of protection beyond the password itself.
If your firmware supports it, enable 2FA to strengthen security.
How do I reset a forgotten SonicWall admin password?
Use the built-in recovery or reset procedure for your model. If you cannot access the interface, consult official recovery guides and prepare to reconfigure from a secure backup after resetting.
Use the model's recovery process and reconfigure securely afterward.
What are the risks of not following password best practices on SonicWall devices?
Neglecting password hygiene increases exposure to brute-force attacks, credential stuffing, and unauthorized changes to firewall settings. Enforcing best practices reduces these risks and helps with regulatory compliance.
Weak passwords raise risk of attacks; strong practices help reduce it.
Can I use a password manager with SonicWall authentication?
Yes. A password manager can generate and store unique, complex credentials for SonicWall admin access. Combine this with 2FA and regular audits for best results.
A password manager is fine to use, paired with 2FA.
“Password hygiene for network devices is non-negotiable; changing defaults and enforcing strong policies dramatically reduces exposure.”
Key Takeaways
- Change SonicWall defaults on first setup.
- Enable strong password policies and 2FA where possible.
- Limit admin access by IP and disable unnecessary remote admin.
- Document, audit, and rotate credentials regularly.
- Monitor for unusual login activity and respond quickly.