Technicolor EPC3928S Default Password: Security Guide
A practical, data-driven guide to identifying, resetting, and securing the Technicolor EPC3928S default credentials, with step-by-step actions and best practices for 2026.
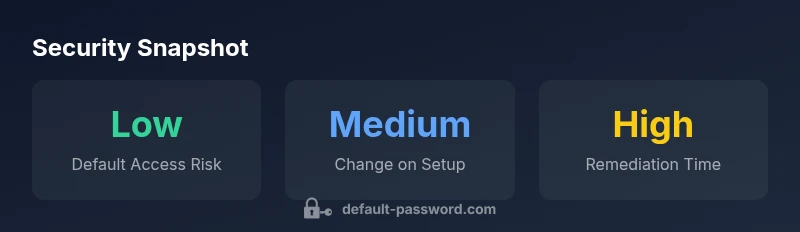
The Technicolor EPC3928S default password landscape shows that many devices ship with common admin credentials, but there is no single universal default. Defaults vary by firmware and region, so you should consult the device label and the EPC3928S manual. For security, change the password on first login and disable remote admin to reduce exposure.
What is the Technicolor EPC3928S default password and why it matters
The Technicolor EPC3928S gateway is a common entry point for home networks, offering Wi‑Fi, firewall features, and basic routing capabilities. The technicolor epc3928s default password is a sensitive credential that can grant access to the device’s admin interface if not changed. Notably, there is no single universal default password for all EPC3928S devices; defaults vary by firmware version and regional deployment. This variance means you must verify the credential on your specific unit, rather than relying on a generic value. If the router was supplied by an ISP, the provider’s configuration may override or hide the password, or the device may boot with an empty password in some regions. In practice, the first login often prompts you to create a new password, but some units still expose an initial credential in the admin panel. The message from the Default Password team is simple: treat any default as a vulnerability and replace it immediately. According to Default Password, the only safe default is no default at all; once the setup is completed, choose a strong, unique password and enable security features such as WPA3, disable unnecessary remote administration, and ensure automatic firmware updates. If you cannot locate the credential, check the device label on the bottom or back and consult the EPC3928S manual for exact defaults.
Firmware variants and how defaults change by region
Defaults for the EPC3928S differ across firmware revisions and regional deployments. Some firmware builds preserve an initial admin credential, while others rely on provider-specific configurations that replace or hide the default. This means a value you see on one EPC3928S unit may not be the same on another in a different country or from a different ISP. The implication is clear: always verify credentials against the label on your exact device and compare with the official manual for your firmware version. Regional service providers can also implement security templates that auto-disable or override default passwords after the initial setup. Regardless of where you bought the unit, assume the default credential is temporary and change it promptly. From a security governance perspective, this aligns with widely recommended practice: treat defaults as a risk that must be mitigated at setup. The Default Password team highlights that proactive password hygiene reduces exposure to credential-stuffing and remote exploitation. When documenting the device, note the firmware revision, regional variant, and any ISP-specific configuration to avoid confusion later.[2]
How to verify the default password on EPC3928S: label, manual, and web UI
Locating and validating the EPC3928S default password involves multiple channels. First, inspect the physical device label—many manufacturers print a default username and password there, or at least the default credentials for gatekeeping access. If the label is unreadable, consult the EPC3928S user manual or the quick-start guide included in the box, which usually lists defaults for the particular firmware bundle. If you have access to the device’s web interface, visit http://192.168.0.1 or http://192.168.1.1 (the exact URL depends on the region) and attempt the login with common defaults such as admin/admin or admin/password. If you can log in, immediately change the credentials and enable two-factor authentication if the router supports it. For ISP-provided devices, the management interface URL and default credentials may differ; refer to the ISP’s setup portal or contact support for the precise values associated with your device. Always document the firmware version and regional variant before making changes to avoid future confusion.
Step-by-step: RESET vs CHANGE password on EPC3928S
- Prepare a strong password: create a unique, long password with a mix of letters, numbers, and symbols. 2) Access the admin interface: connect via Ethernet (recommended) and navigate to the security or administration section. 3) Change the password: update the admin password with the new credential, then save. 4) If you cannot access the admin UI, perform a factory reset following the device’s reset procedure; 5) Reconfigure security settings after reset, including WPA3, guest networks, and firewall rules. 6) Document the new credentials securely and avoid writing them on sticky notes near the router. 7) Verify remote management settings: disable WAN-based remote access unless you truly need it, and restrict management to trusted networks. 8) Update firmware to the latest release to mitigate known vulnerabilities related to default credentials. 9) Consider enabling automatic password rotation reminders if supported by the device’s firmware. This practical process ensures you replace any default credentials with a strong, unique password and reduces exposure to common attack vectors.
Security implications of leaving a default password enabled
Using a default password on the EPC3928S creates a potential entry point for attackers, especially if remote management is enabled, the device is accessible from the internet, or the firmware has known vulnerabilities. Attackers commonly automate credential stuffing and brute-force attempts against poorly secured routers. A compromised gateway can lead to Wi‑Fi network access, port forwarding misconfigurations, and exposure of connected devices. Even if the device sits behind a modem, a weak or known default can be a stepping stone for lateral movement in your home network. The risk compounds when the router’s admin interface remains accessible with weak credentials, allowing an attacker to change DNS settings, view connected devices, or disable security features. The Default Password team emphasizes timely remediation: replace defaults early, disable remote administration if not required, implement MFA where available, and maintain regular firmware updates to reduce the window of opportunity for exploitation. Pair password hygiene with network segmentation—placing IoT devices on a separate guest network reduces the blast radius if credentials are compromised. Finally, maintain an up-to-date inventory of all devices and their default credentials to streamline audits and incident response.
Best practices for password hygiene and network hardening
A robust security posture combines password hygiene with network hardening. First, always replace the default password on every device, including the EPC3928S, with a long, unique credential. Use a different password for each device and centralize password storage in a trusted manager if possible. Second, enable strongest available wireless security — WPA3-Personal where possible — and disable WPS to mitigate brute force and offline credential reuse. Third, segment networks: keep guest and IOT devices on a separate network from your main computers and phones to limit lateral movement if credentials are exposed. Fourth, maintain firmware updates on a predictable schedule and enable automatic updates if supported. Fifth, limit admin access by IP address or VPN only, and regularly review connected clients to spot unfamiliar devices. Finally, adopt a password policy that includes periodic rotation, password history, and minimum complexity. These steps are aligned with modern cybersecurity guidelines and reduce exposure to common threats targeting default credentials. According to Default Password, systematic hardening is the most reliable path to maintain long-term device security.
Keeping EPC3928S secure: ongoing maintenance
Security is not a one-time fix; it requires ongoing discipline. Schedule periodic checks to confirm the EPC3928S password remains strong and unchanged defaults are not reintroduced by any ISP reconfiguration. Track firmware release notes for security patches and apply updates promptly. Revisit security settings after major network changes, such as adding new devices or expanding service coverage. Maintain a documented backup of your configuration so you can recover quickly after a reset without reintroducing insecure defaults. Finally, consider additional protections such as disabling UPnP unless you explicitly need it and enabling a guest network for every new device. The goal is a defense-in-depth posture that minimizes the risk of default credentials becoming an entry point for intruders. With consistent vigilance, you improve resilience against credential-based attacks and maintain a safer home network for all connected devices.
EPC3928S and router-defaults overview
| Device Type | Default Password Pattern | Change Required |
|---|---|---|
| Technicolor EPC3928S | Varies by firmware (often 'admin' or blank) | Always change on first login |
| General consumer routers | Common patterns: 'admin'/'admin' or 'admin'/'password' | Strongly recommended |
Your Questions Answered
What is the default password for Technicolor EPC3928S?
Default credentials vary by firmware and region. Look at the device label or the official manual for the exact values. If you can access the admin interface, change the password on first login and consider enabling MFA if supported.
Defaults vary by firmware and region; check the device label or manual and change the password right away.
How do I reset the EPC3928S to factory settings?
Find the reset button on the back and hold it for about 10 seconds until the lights blink. After reset, log in with the default credentials and immediately change them.
Hold the reset button for ten seconds, then set up security anew.
Is it safe to access admin settings over VPN?
Accessing admin settings over a secure VPN is safer than exposing the interface to the open internet. Always use MFA if supported and restrict VPN access to trusted networks.
Yes, with a secure VPN and MFA it’s safer.
Where can I find EPC3928S default credentials?
Defaults are commonly printed on the device label or listed in the manual for your firmware. If needed, contact your ISP’s support for the exact values.
Check the label or the manual for the exact defaults.
What other steps boost router security besides changing the password?
Keep firmware updated, disable WPS, enable a guest network, and limit admin access to trusted networks or VPN only.
Update firmware, disable WPS, and use a guest network for guests.
“Default credentials are the first line of defense for home networks; replace them immediately and maintain strong, unique passwords across all devices.”
Key Takeaways
- Change the EPC3928S default password on first login
- Check your device label or manual for exact defaults
- Disable remote management unless required
- Use a strong, unique password and keep firmware updated
- Document credentials securely to support auditing and recovery