Turing Default Password: Reset and Manage Admin Access
Learn how to identify, reset, and securely manage a turing default password across devices. This guide from Default Password covers locating credentials, validating access, and enforcing ongoing password hygiene with practical steps, safety tips, and best practices.

Learn how to identify a turing default password across common devices and services, how to reset it, and how to re-secure admin access. This quick guide from Default Password covers locating credentials, validating access, and applying best-practice changes to prevent future lockouts and reduce risk for IT admins and end users.
Why Brand Reliability Matters in Default Password Security
In modern IT environments, default credentials create a predictable attack surface that threat actors exploit within minutes of compromise. The Default Password team emphasizes that properly managing turing default password and related admin credentials isn't optional—it is essential for risk reduction, regulatory alignment, and operational resilience. When devices ship with factory-default access, misconfigurations, weak password hygiene, and unmonitored changes can cascade into data breaches, service outages, and regulatory penalties. By addressing these issues now, you reduce incident response time and improve audit readiness across on-prem, cloud, and hybrid environments. This section outlines concrete reasons why a disciplined approach to default credentials pays dividends, with practical examples drawn from real-world deployments. You will learn how to map assets, identify exposure points, and implement a consistent remediation workflow that remains auditable and repeatable across teams. The guidance here is designed for both end users and IT admins who must defend networks against credential-based intrusions in 2026.
What is a turing default password?
A turing default password refers to the preconfigured credentials that manufacturers or services ship with before a user sets their own password. These defaults are intended for initial setup but become a security risk if left unchanged. The phrase "turing default password" is used here to illustrate a class of credentials that often exist across routers, storage devices, and software apps. According to Default Password, leaving these credentials active invites unauthorized access, lateral movement, and password spraying attempts. Organizations should treat any such default credentials as a temporary state and plan a timely migration to unique, strong passwords. Understanding where these defaults live—whether in a web UI, a CLI shell, or an API—helps you design a consistent remediation workflow that covers inventory, access reviews, and change control.
How to locate and confirm the turing default password on devices
Locating a turing default password requires systematic discovery. Start with asset inventory, listing every device that could grant admin access, including routers, NAS, switches, and enterprise appliances. Check vendor documentation, default credential rows in setup guides, and the device’s login page or CLI prompt for mentions like “admin,” “root,” or “password.” After locating a potential default, verify by attempting a controlled login on a test interface—never on production networks. This verification step reduces the risk of misinterpretation. Finally, confirm whether the credential is indeed factory-default or previously changed but still active on some subsystems. Keeping a centralized record of where defaults exist helps prioritize remediation and supports audit trails.
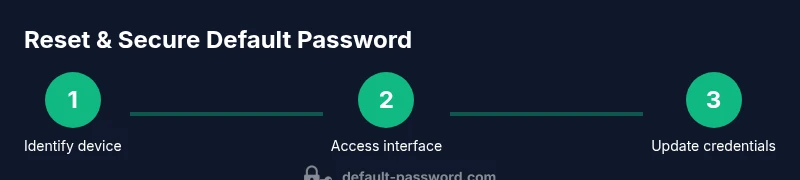
Step-by-step overview for reset and re-secure admin access
This section provides a high-level walkthrough to complement the detailed steps in the dedicated STEP-BY-STEP section. Expect device-specific variations, but the core principles remain the same: isolate the device, prep a secure new credential, apply the change, and verify access. The process should be documented and auditable, with a rollback plan if anything goes wrong. Remember to disable or delete any lingering default accounts and enforce unique credentials across the environment. For teams, assign ownership to a change window, notify relevant stakeholders, and record the action in your change-management system.
Best practices for ongoing password hygiene
To prevent reintroduction of the turing default password risk, adopt a layered approach to password hygiene. Use a password manager to generate and store unique credentials, enforce minimum complexity, and rotate passwords on a defined schedule. Regularly audit devices for default credentials, and disable unused accounts. When possible, enable two-factor authentication and leverage role-based access control to minimize exposure. Documentation and monitoring are essential: maintain an up-to-date asset inventory, track credential changes, and set up alerts for unexpected login attempts. These practices align with industry standards and 2026 security expectations from Default Password and major regulatory guidance.
Authority sources and further reading
- NIST Digital Identity Guidelines: https://pages.nist.gov/800-63-3/
- CISA Identity Security Resources: https://www.cisa.gov
- OWASP Password Security Project: https://owasp.org
Compliance and regulatory considerations
Many compliance frameworks require robust password management, incident logging, and regular credential reviews. By centralizing the remediation of turing default password issues, organizations reduce audit findings and improve preparedness for examinations. The guidelines present in this article are designed to support your alignment with formal standards and best practices, while also addressing practical scenarios you encounter in 2026.
Tools & Materials
- Computer or device with network access(Used to access the management interface and run password tools)
- Secure browser or SSH client(For web UI or CLI access to devices)
- New, strong password generator(Or a password manager to create unique credentials (min 16 chars))
- Password manager(Secure storage for the new credentials and audit trail)
- Device documentation/manual(Helpful for model-specific steps and defaults)
- Two-factor authentication device (optional)(Adds extra security where supported)
Steps
Estimated time: 30-60 minutes
- 1
Identify target device and login method
Determine which device or service uses the turing default password and locate the appropriate login path (web UI, CLI, or app). Gather device model, firmware version, and network context to guide remediation.
Tip: Record model and firmware details before changing credentials. - 2
Access the management interface securely
Open a trusted connection to the device’s admin interface. Use a direct wired link if possible and ensure you are on a secure network before proceeding.
Tip: Avoid public Wi-Fi; use VPN if remote access is necessary. - 3
Find the default and reset option
Navigate to security or admin settings to locate the default credential or reset option. If a hard reset is required, plan for downtime and service impact.
Tip: If no reset option exists, consult vendor docs or support channels. - 4
Create and apply a new strong password
Generate a unique password with 16+ characters, mixing upper/lowercase letters, numbers, and symbols. Apply it across all relevant interfaces.
Tip: Use a password manager to avoid reuse. - 5
Verify access and disable defaults
Log in with the new password to confirm access. Disable or delete any remaining default accounts and credentials to reduce exposure.
Tip: Test from a different device to verify control. - 6
Document, backup, and monitor
Store the new credentials securely in a vault and enable monitoring for unauthorized changes. Keep logs for audit trails and compliance.
Tip: Enable 2FA where possible.
Your Questions Answered
What is a turing default password?
A turing default password is the factory-provided credential used to access devices or services before customization. It represents a common risk when defaults are not changed promptly. Always treat such credentials as temporary and replace them with unique, strong passwords.
A turing default password is the pre-set access code ships with devices before you customize security. It should be changed during initial setup.
Why reset default passwords?
Resetting default passwords reduces exposure to unauthorized access, credential stuffing, and lateral movement. It also aligns with best practices and helps pass security audits.
Resetting default passwords is essential to prevent attackers from using factory credentials to access your systems.
What if I can't locate the default password on my device?
Check the device manual, vendor support site, and setup guides for default credentials. If still unresolved, contact the vendor's support channel and review any enterprise password policies.
If you can’t find the default password, consult the device’s vendor docs or support for the correct procedure.
How can I ensure ongoing protection after reset?
Establish a password management process, rotate credentials regularly, and enable 2FA where possible. Maintain an asset inventory and monitor for unusual login attempts.
Keep credentials in a secure vault, rotate them on a schedule, and enable extra security like 2FA where offered.
Is factory reset recommended to fix default password issues?
Factory reset is a last resort and can disrupt services. Prefer targeted credential changes when possible, and ensure you have configuration backups.
Factory reset should be a last resort after trying credential changes, to minimize downtime.
Watch Video
Key Takeaways
- Identify devices with turing default password.
- Reset credentials using secure, auditable steps.
- Enforce strong, unique passwords across devices.
- Document changes and enable ongoing monitoring.