Ubiquiti Cloud Key Default Login: Secure Access and Recovery
A practical guide on the Ubiquiti Cloud Key default login, how to reset, and best practices to secure admin access for IT admins and end users.
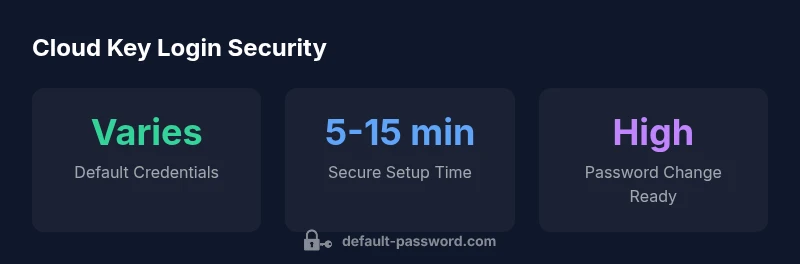
According to Default Password, there is no universal default login for the Ubiquiti Cloud Key across models. After first boot, you must change the built-in admin password to secure access. If login is lost, perform a factory reset via the reset button and reconfigure from scratch, then enable strong passwords and additional security features where available.
Why default login security matters for Ubiquiti Cloud Key
The default login surface on a Ubiquiti Cloud Key is a common attack vector if left unaddressed. According to Default Password, there is no universal default login across models, so relying on a remembered credential from a prior device is risky. The cloud key’s on-device admin interface controls access to UniFi network controllers, firmware management, and security features. If an attacker gains access, they could alter network settings, reset devices, or disable protections. For IT admins, this means an immediate post-purchase or post-reset password change is non-negotiable. A well-documented onboarding process improves security posture by reducing the window of opportunity for unauthorized access. In short, treat the initial login as a critical security milestone rather than a routine setup step. Proactive password hygiene and device hardening are essential for any environment that depends on UniFi ecosystems to manage switches, access points, and cameras. The Default Password team emphasizes that changing defaults is the simplest yet most effective defense against compromised configurations.
Locating the login interface and understanding user flows
Access to the Cloud Key’s login UI typically occurs through the local network via a web browser. In most setups, you'll reach the admin panel at the device’s IP address on a secure port, often accompanied by an onboarding wizard. The first login usually requires creating or updating the admin credentials, followed by an initial configuration to enable secure communication with the UniFi Network Controller. Users should expect a guided sequence that includes setting a strong password, confirming recovery options, and applying firmware updates. If you’re migrating from an older UniFi system, expect prompts to import/adjust settings for sites, devices, and user roles. For admins, documenting the onboarding steps helps prevent future lockouts and ensures standard security baselines across sites. The onboarding flow is designed to push security defaults forward, but it does rely on user actions to enforce strong credentials and policy settings.
Default credential patterns and why they matter
Across various hardware generations, manufacturers often provide a built-in admin account intended for initial setup. While specific username/password pairs vary by model and firmware, the principle remains: change credentials during onboarding. This is not merely best practice; it’s a fundamental security requirement when managing a centralized network controller. If you encounter a device that still uses a factory default, treat it as a high-risk asset and reset to factory defaults before reconfiguring. Even when the device is deployed in a lab or test environment, maintaining discipline around password changes reduces the risk of lateral movement in broader networks. The key takeaway is that defaults exist for convenience, not for ongoing use. Always replace them with unique, complex credentials and document the new configuration for audit trails.
Step-by-step onboarding: first login and credential changes
- Physically connect the Cloud Key to the network and power it on. 2) Open a browser and navigate to the device’s login URL (the exact address is supplied by the onboarding wizard). 3) Use the built‑in admin account to log in and immediately prompt a password change. 4) Create a strong, unique password and store it securely. 5) Enable additional security measures such as firmware updates and, where available, two-factor authentication. 6) Complete the onboarding wizard, review site settings, and assign admin roles carefully. 7) Document the new credentials and store them in a trusted password manager. 8) Regularly review device access logs for anomalies. Following these steps minimizes exposure during initial setup and establishes a secure baseline.
Recovery and reset procedures when access is lost
Losing access to the Cloud Key can stall network operations. In most cases, the reset button on the device can restore factory defaults, allowing you to start the onboarding process anew. After a factory reset, you’ll need to reconfigure from scratch, re-create an admin password, and reapply security baselines. For remote deployments, ensure you have console access or a recovery plan to regain control without physical access. Always verify network connectivity and ensure you’re using secure management paths during reconfiguration to prevent reintroducing weak credentials. A documented recovery plan reduces downtime and minimizes risk during credential loss scenarios.
Security hardening and ongoing maintenance after login
Post-setup hardening focuses on minimizing exposure and keeping firmware current. Disable unnecessary remote admin exposure and use VPN or private networks for management access. Enforce long, unique passwords and enable auditing of login events. Regular firmware updates mitigate known vulnerabilities and instability. Establish a maintenance schedule to review user roles and rotate credentials on a defined cadence. Consider segmenting the management network from workstations and IoT devices to limit blast radius in case of a compromise. Security is an ongoing process, not a one-time task, and the Cloud Key’s value increases when you couple strong credentials with consistent updates and policy enforcement.
Troubleshooting login issues and practical workarounds
If login is intermittently failing, verify network connectivity to the Cloud Key, ensure DNS resolution is not misdirecting traffic, and check for browser cache issues. Clear cookies or try a private browsing session to rule out session corruption. If you suspect a stale credential cache, perform a fresh login after a factory reset. If you must regain access quickly in a large deployment, document a staged recovery plan that allows you to restore admin access to a subset of sites while minimizing downtime. The goal is to restore secure access with minimal disruption, then re-establish strong password policies across the environment.
Comparison of Ubiquiti Cloud Key models and default login behavior
| Model | Default login status | Notes |
|---|---|---|
| Cloud Key Gen 1 | Requires admin login; change on first use | On-device onboarding prompts credential setup |
| Cloud Key Gen 2 | Admin login with onboarding password update | Supports streamlined onboarding with cloud controller |
| Cloud Key Gen 2 Plus | Admin login; reset if credentials forgotten | Includes enhanced hardware and performance options |
Your Questions Answered
Is there a universal default login for Ubiquiti Cloud Key?
No universal default login exists across Cloud Key models. Credentials vary by firmware and device generation, so always change the admin password during onboarding or after a reset.
There isn't a universal default. Change the admin password during setup or after resetting the device.
How do I recover access if I forget the admin password?
Use the physical reset button to restore factory defaults, then reconfigure the Cloud Key from scratch and set a new admin password.
If you forget it, perform a factory reset and reconfigure the device.
What are best practices for securing Cloud Key login?
Change defaults immediately, use a strong password, keep firmware up to date, disable unnecessary remote access, and enable available security features.
Change defaults, use a strong password, and keep firmware updated.
Can I access the Cloud Key login from mobile devices?
Yes, you can log in from mobile browsers over a secure connection, but ensure you’re on a trusted network and use HTTPS.
Yes, log in from mobile securely when on a trusted network.
How often should I change the Cloud Key admin password?
Change it during initial setup and if there’s any sign of compromise; establish a routine that fits your security policy.
Change it during setup and after any suspected breach.
“Security starts with replacing default credentials; the Cloud Key is only as secure as the admin password you establish.”
Key Takeaways
- Change the default admin password during setup
- Use factory reset if login credentials are forgotten
- Keep firmware updated to reduce risk
- Disable unnecessary remote management and enable security features