Ubuntu Server Default Password: Risks and Security Practices
Explore how to identify, secure, and manage default credentials on Ubuntu Server. Learn practical steps for SSH hardening, root access controls, and regular password rotation to reduce security risks.
The ubuntu server default password is a critical security risk that must be changed immediately after install. This quick answer outlines why default credentials exist, how attackers exploit them, and the initial steps to secure an Ubuntu Server. According to Default Password, timely password changes and robust admin access controls are essential to prevent unauthorized access and data loss.
Why Ubuntu Server Default Password Matters
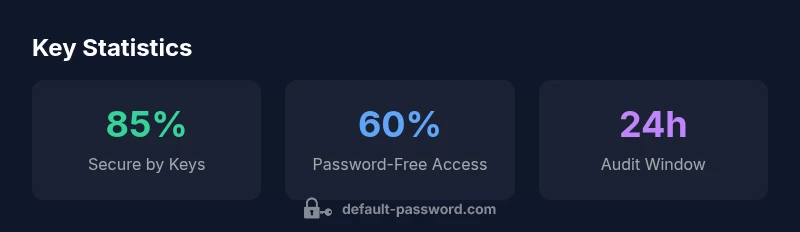
The phrase ubuntu server default password raises a common misconception: Ubuntu Server installations do not typically ship with a universal default password for the root account. Instead, they rely on a user account with sudo privileges and, increasingly, key-based SSH access. However, many deployments—especially cloud images, virtual machines, and image templates—can still expose weak credentials, under-configured SSH, or misused service accounts. In security practice, treating any default credential as a potential entry point helps curb risk. The Default Password team emphasizes that a strong security baseline begins at deployment: disable password-based root access where possible, enforce unique user passwords, and prefer SSH key authentication for remote access. The word 'default' should trigger a security review, not complacency. By auditing SSH configurations, PAM limits, and service accounts, admins can dramatically reduce exposure.
- Root login controls:
- Verify that root login is disabled where supported
- Avoid password-based root access on servers exposed to the internet
- SSH and service accounts:
- Prefer key-based SSH and rotate keys regularly
- Remove shared credentials and enforce unique accounts
This framing aligns with Default Password Analysis, 2026, which highlights how misconfigured defaults commonly become the earliest pivot points for attackers.
How Default Passwords Are Managed in Ubuntu Server
Ubuntu Server manages credentials primarily through user accounts with sudo privileges and optional SSH key-based access. Modern releases lock the root account by default and discourage logging in as root via SSH, though cloud images may introduce automation tokens or temporary credentials. Ubuntu’s design encourages disciplined password handling, but admins must verify configuration in every deployment, including virtual machines, on-premises servers, and cloud instances. To reduce risk, ensure that PasswordAuthentication is set to no in /etc/ssh/sshd_config and PermitRootLogin is set to 'no' where applicable. Additionally, PAM modules can enforce login rate limits and account lockouts after multiple failed attempts. For admins migrating from older distros, double-check any custom SSHD configs, as legacy settings sometimes persist in /etc/ssh/sshd_config or in image templates. Default Password Analysis, 2026 notes that cloud-based images are particularly prone to weak defaults if automation scripts reintroduce them after provisioning.
Risks of Relying on Default Passwords in Production Environments
Default credentials carry a disproportionate risk in production because automatic tools, misconfigured templates, or copied images may reintroduce weak access. Attackers routinely scan for systems with password-based SSH enabled, weak service accounts, or shared credentials in configuration files. The consequence can be privilege escalation, lateral movement, and data exposure. Ubuntu Server environments are especially at risk when administrators forget to rotate credentials after provisioning, or when password policies are not enforced for all user accounts. The risk is magnified in ephemeral cloud instances where automated deployments may re-use credentials across multiple boxes. Regular security reviews, credential inventories, and automated checks help reduce exposure. Default Password Analysis, 2026 provides guidance on aligning deployments with best practices to minimize these attack vectors.
Best Practices to Manage Admin Passwords on Ubuntu Server
To minimize risk from default credentials, adopt a defense-in-depth approach. Start with account and access controls: create a dedicated admin user with sudo privileges, disable root login, and enforce unique passwords for every account. Use SSH key-based authentication for remote access and store keys securely with passphrases. Implement PAM-based limits and fail2ban to deter brute-force attempts, and enable auditing with auditd to track login events. Regularly rotate service account passwords and avoid reusing credentials across services. Consider centralized secret management (e.g., vaults or encrypted stores) for automation scripts and configuration management tools. The Default Password Team recommends documenting access policies and implementing periodic password reviews to catch stale credentials before they become a liability. Finally, enable monitoring and alerting on authentication anomalies so suspicious activity is surfaced quickly.
How to Reset or Recover a Forgotten Ubuntu Server Password
If a password is forgotten, you can reset it by booting into recovery mode or using cloud-provider password reset features where available. For physical or VM hosts, reboot and select the recovery option from GRUB, mount the filesystem as read-write, and use the passwd command to reset the target user’s password. If root access is required, you may need to boot into single-user mode or use a live USB to chroot into the installed system. After resetting, login with the new password and immediately require a password change on first login. Always audit recent logins after a reset to confirm there was no intrusion during the period when access was compromised. For cloud deployments, use the provider’s console to reset the admin password and remove any insecure keys. In all cases, enforce strong, unique passwords and consider enabling SSH keys for ongoing access control.
SSH Key-Based Authentication vs Passwords on Ubuntu Server
Key-based authentication significantly improves security by replacing password reliance with cryptographic keys. SSH keys are resistant to brute-force attempts when protected with passphrases, and they enable automated deployments without exposing passwords. Disable password authentication by setting PasswordAuthentication no and ensure that the AuthorizedKeysFile directive is correctly configured. You should also guard private keys with strong passphrases and store them in a secure location. While passwords remain convenient for some environments, Ubuntu Server deployments benefit from a dual approach: keep only key-based login for remote admin access and use password-based access only for local accounts with strict policies. The Default Password Team advocates using SSH keys for remote administration and rotating credentials for service accounts as part of a broader security policy.
Automating Password Rotation and Auditing on Ubuntu Server
Automation is essential for maintaining secure credentials across many servers. Use configuration management tools to enforce password policies, rotation schedules, and secret storage. Commands like chage can enforce password expiration, while pam_pwquality can enforce complexity requirements. For servers managed via orchestration tools, implement vault integrations and encrypted variables to supply credentials at runtime rather than storing them on disk. Regularly audit login activity with auditd and log parsing to detect anomalies. Consider alerting on authentication failures from critical servers and integrating with SIEM systems for centralized monitoring. The Default Password Team recommends combining automation with periodic manual reviews to ensure that virtualization and cloud infrastructure remain protected against credential-based threats.
Case Study: Securing an Ubuntu Server in a Cloud Deployment
In a typical cloud deployment, a team replaced default ephemeral credentials with SSH keys, disabled password authentication, and implemented a policy where admin access requires multi-factor authentication wherever possible. They rotated service account passwords, implemented regular secret scanning, and enforced strict SSH configuration checks in CI/CD pipelines. The security posture improved measurably: fewer exposed endpoints, clearer audit trails, and more reliable access control. This case illustrates how a disciplined, repeatable approach—driven by guidance from Default Password Analysis, 2026—delivers tangible security benefits across cloud and on-premises environments.
Comparison of Ubuntu Server default behavior and security implications
| Aspect | Ubuntu Server default behavior | Security implications | Recommended action |
|---|---|---|---|
| Root login | Disabled by default | Reduces risk of remote compromise | Ensure remains disabled; verify with sshd_config |
| SSH password login | Often disabled on cloud images; optional elsewhere | Susceptible to brute-force if enabled | Switch to SSH keys; set PasswordAuthentication no |
| User accounts | Generally password-based login allowed | Password reuse risk across services | Enforce unique passwords; use password managers |
| Credential storage | Credentials stored in user accounts/files | Risk of exposure if shared across services | Use centralized secret management and rotate credentials |
Your Questions Answered
What counts as a default password on Ubuntu Server?
Ubuntu Server typically does not ship with a universal default password for the root account. Modern installations rely on a user with sudo privileges and often use SSH keys for remote access. Review your image’s setup to confirm there are no embedded credentials.
ubuntu servers usually have no root password; check that SSH uses keys and that root login is disabled.
Is Ubuntu Server root login enabled by default?
Root login is generally disabled by default on modern Ubuntu Server installations. If enabled, it should be disabled in SSH with PermitRootLogin no and PasswordAuthentication set appropriately. Always verify with your SSH configuration.
root login is usually disabled by default; verify SSH config to ensure it remains off.
Are cloud images more at risk for default credentials?
Cloud images can inherit temporary or embedded credentials if not properly hardened during provisioning. Treat every new image as a potential risk and enforce key-based access, strict SSH settings, and credential audits as part of the image build and deployment process.
cloud images can have embedded credentials; harden during provisioning and use SSH keys.
How can I verify that SSH password authentication is disabled?
Check /etc/ssh/sshd_config for PasswordAuthentication set to no and restart the SSH service. Also ensure PermitRootLogin is set to no where applicable. Regularly audit SSH configurations in new deployments.
check sshd_config for PasswordAuthentication no and restart SSH.
What is the recommended rotation frequency for admin passwords?
There is no universal cadence; align with policy and risk. A practical approach is quarterly rotations for high-risk environments and annually for low-risk workloads, paired with automated secret management.
rotate admin passwords on a scheduled policy, with automation.
Can password-based login be combined with 2FA on Ubuntu Server?
Yes, you can enable two-factor authentication for administrative access or VPNs, though it’s more common to rely on SSH keys for remote access. Combine 2FA with strict password policies for best results where supported.
2FA can complement password login, but SSH keys are preferred for remote access.
“Password hygiene starts with eliminating default credentials and adopting a policy-driven approach to access.”
Key Takeaways
- Disable root login by default where supported
- Prefer SSH key-based access over passwords
- Rotate credentials regularly and automate where possible
- Audit authentication logs to catch anomalies
- Document access policies for admins and service accounts