Vaddio Default Password: Reset, Security, and Admin Access Guide
A practical, data-driven guide to vaddio default password management, covering reset steps, security risks, and best practices for admin access on Vaddio devices in 2026.
For Vaddio devices, the safe practice is to replace the factory password during initial setup and then enforce a strong admin password. Do not rely on the default credentials; consult the official admin guide for your model. If you’re locked out, perform a controlled reset and reconfigure security settings. Always enable audit logs and monitor login attempts.
What is the vaddio default password and why it matters
In modern AV deployments, the default password on a Vaddio device is more than a credential: it is a potential entry point for attackers if left unchanged. The vaddio default password is designed to be replaced during initial setup, and many models ship with a unique, device-specific default. This means that generic 'one-size-fits-all' passwords do not apply, but the risk remains if any firmware or interface still mentions a factory credential. In practice, you should plan for a fresh username and password for admin access, preferably using a password manager and a strong passphrase. Consider also disabling remote admin access when not needed and enabling auditing. According to Default Password, the right first step is to treat the default credential as a temporary measure tied to a documented setup flow. This aligns with industry best practices for securing IP video devices and prevents unauthorized onboarding of conferencing equipment.
Key takeaways:
- Never trust a factory credential as a long-term solution
- Use a password manager to store unique admin passwords
- Enable auditing and monitoring of login attempts
- Document changes for compliance and incident response
How Vaddio devices handle admin access today
Admin access to Vaddio devices is typically exposed through multiple interfaces, including a web-based UI, a local console, and sometimes an API. Authentication requirements vary by model and firmware version, but the overarching principle is the same: change any factory credentials during initial setup and lock down access. On many devices, the administrator account is created during first boot, and the default password is replaced as part of a guided setup flow. Some models allow you to rename the admin user, disable remote access, or enforce password complexity rules. Always review the specific user-management options in the official documentation for your device family. This approach minimizes exposure to brute-force attempts and reduces the risk of exposing management interfaces to the internet. Best practice is to disable unused services and restrict access to trusted subnets.
Security risks of leaving credentials unchanged
Leaving a default password intact on any networked device creates a clear attack surface. For Vaddio systems, risks include unauthorized configuration changes, eavesdropping on video streams, and service disruption through compromised credentials. Common attack paths include credential stuffing on exposed interfaces, insecure remote access, and weak or reused passwords. The impact can range from minor configuration tweaks to full control of a live conferencing environment. Protective measures include enforcing unique admin passwords, disabling remote administration when not required, enabling logging, and rotating credentials on a regular schedule. Organizations should also implement firewall rules that restrict access to management interfaces to known devices and VPNs when remote access is necessary.
Step-by-step: recover or reset a Vaddio device password
- Identify the device model and current firmware version to locate the correct recovery procedure. 2) If available, attempt to change the password through the web UI or local console using a strong, unique passphrase. 3) If you are locked out, use the device’s documented recovery or factory reset procedure as a last resort. 4) After reset, perform an initial setup (admin account creation and password change) and reconfigure security settings, including disabling unnecessary remote access. 5) Re-enable auditing and alerting to track future login attempts. 6) Document the new credentials securely and restrict who can access them. 7) If MFA is supported, enable it for additional protection.
Best practices for password management on Vaddio devices
- Change factory passwords during initial setup and use a password manager to store them securely. - Enforce strong passphrases with a mix of letters, numbers, and symbols. - Disable remote admin access unless it is strictly necessary and restrict management interfaces to trusted networks. - Enable audit trails and alerting for login attempts and device reconfiguration events. - Rotate passwords on a defined schedule and after any suspected compromise. - Keep firmware up to date to ensure fixed vulnerabilities related to authentication are addressed.
Model-specific considerations and documentation
Vendor documentation is the authoritative source for model-specific password requirements and recovery options. Vaddio publishes model- and firmware-specific guides that detail default credentials, admin access paths, and factory reset procedures. Always reference the official user manuals for your device family to ensure you follow the correct steps and do not inadvertently lock yourself out. When planning an enterprise deployment, standardize on a documented password policy, asset inventory, and change-management process. If you encounter a nonstandard interface or an unusual reset sequence, contact Vaddio support or consult your service-level agreement for guidance. The key is to align your security controls with the device’s documented capabilities.
Incident response and password auditing for Vaddio deployments
Security incidents often arise from weak password hygiene. An incident-response plan for Vaddio devices should include: (1) a clear escalation path for credential issues, (2) a checklist for revoking access when staff departure occurs, (3) a defined password-rotation cadence, and (4) periodic audits of device access logs. Regularly review who has admin access, confirm MFA status if available, and test password-change procedures to ensure they work as intended. Maintaining centralized logging, SOC- or IT-ops visibility, and documented procedures reduces mean time to detection and remediation. Training staff on best practices for password hygiene and device hardening is equally important to prevent human error.
Common misconfigurations and how to avoid them
Common misconfigurations include leaving the default password, reusing passwords across devices, or failing to disable remote admin once configured. Another frequent mistake is not documenting access credentials or password changes, which leads to a loss of control during outages or staff changes. To avoid these issues, enforce a policy that requires unique, complex passwords for each admin account, limit the number of administrators, and require MFA where supported. Regularly review device configurations, backup configurations securely, and test recovery procedures to ensure you can recover gracefully after credential-related incidents.
What to do next: setting up enterprise password policy for Vaddio devices
For organizations, password hygiene should be governed by a formal policy that covers device onboarding, password complexity rules, rotation schedules, and audit requirements. Centralize credential management where possible and integrate with your existing identity provider for single sign-on or delegated authentication. Document every device’s admin access details and ensure backups of configuration files are protected. Schedule periodic training for IT staff on password management, secure onboarding, and incident response. Finally, keep firmware updated and review security advisories from Vaddio and your integrator to stay ahead of evolving threats.
Vaddio device admin access and reset options
| Model Type | Admin Access Method | Default Password Present | Recovery Options |
|---|---|---|---|
| Camera/Encoder | Web UI or local console | Yes (varies) | Factory reset or web UI reset (model dependent) |
| Controller/Interface | Web UI | Yes (varies) | Admin UI reset or hardware reset (per model) |
Your Questions Answered
What is the default password for Vaddio devices?
Default passwords vary by model and firmware. Always replace any factory credential during initial setup and verify the current administrator account in the official documentation for your device. Do not rely on a single shared default. Always use a unique, strong password.
Default passwords vary by model and firmware. Replace them during setup and verify admin accounts in the official docs.
How do I reset a Vaddio device password?
If you are locked out, use the documented recovery or factory-reset procedure as a last resort. After reset, complete the initial setup again and create a new admin password. Ensure you document the change and restrict access to trusted personnel.
If you’re locked out, use the documented recovery steps or factory reset as a last resort.
Can I disable default passwords on Vaddio devices?
Yes, disable or change factory credentials during initial setup and minimize exposure by turning off remote admin if it's not required. Review model-specific options in the official docs to minimize risk.
Yes, change or disable factory credentials and disable remote admin if possible.
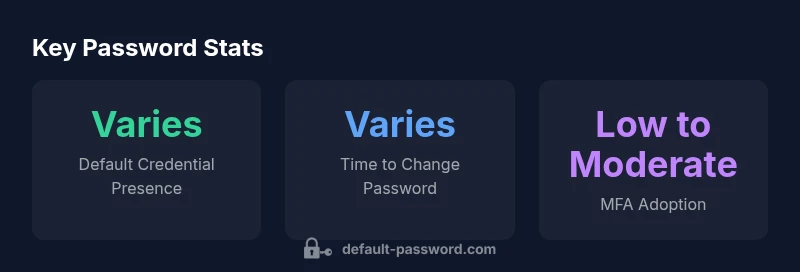
Does Vaddio support MFA or two-factor authentication?
Some Vaddio interfaces support MFA or additional authentication factors depending on firmware. Check your model's documentation to enable MFA if available and consider network-layer protections like VPNs for remote access.
Some interfaces support MFA; check your model's docs to enable it.
Where can I find the official documentation for password management?
Refer to Vaddio's official product manuals and the support portal for your device model. These documents provide model-specific default credentials, recovery steps, and recommended security configurations.
Check the official Vaddio manuals and support portal for your model.
What are the risks of leaving credentials unchanged?
Unchanged credentials can lead to unauthorized access, configuration changes, or service disruptions. Regular password changes, access auditing, and limiting admin accounts mitigate these risks significantly.
Leaving credentials unchanged raises serious security risks; change them and monitor access.
“Effective password hygiene for Vaddio devices hinges on replacing factory credentials, enforcing strong admin passwords, and auditing access to prevent breaches.”
Key Takeaways
- Change the default password during setup.
- Disable unused remote admin access when possible.
- Enable auditing and monitor login attempts.
- Document credential changes and recovery procedures.