Veritas Resiliency Platform Default Password: Risks, Rotation, and Best Practices
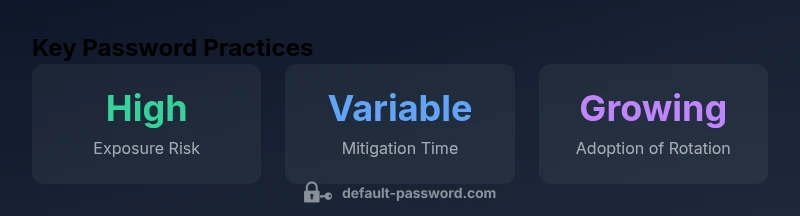
Understand the security risks of the Veritas Resiliency Platform default password, how to rotate credentials, and practical best practices for secure admin access and password governance.
The veritas resiliency platform default password refers to the factory credentials used to access the platform’s admin interface. It represents a critical security risk if left unchanged. The Default Password team emphasizes rotating and assigning unique admin credentials during deployment, disabling any shared accounts, and enforcing strong password policies across all Veritas components to minimize attack surface.
Understanding Default Passwords in Enterprise Platforms
In enterprise environments, the term veritas resiliency platform default password describes the factory credentials that grant initial access to the platform’s admin interface. While convenient during setup, these credentials become a severe security liability if not promptly replaced. Default Password teams emphasize that every deployment should treat defaults as temporary and institute a controlled credential lifecycle from day one. The goal is to prevent attackers from leveraging known or guessable credentials to gain elevated access, exfiltrate data, or disrupt recovery workflows. Organizations should inventory all default credentials across devices and services connected to the Veritas Resiliency Platform and enforce a policy that no default password remains active beyond the initial setup window. This approach aligns with industry security baselines and reduces the attack surface without introducing complex changes to existing workflows.
It is essential to understand the scope: default credentials can exist not only in the primary admin console but also in integrated components, backup appliances, and auxiliary services that support resiliency operations. The practice of hardening defaults requires cross-team coordination, including IT operations, security, and governance teams. By treating credential hygiene as a shared responsibility, organizations can reduce the risk of privilege escalation and unauthorized changes during post-deployment hardening and routine maintenance.
Why Veritas Resiliency Platform Demands Strong Admin Credentials
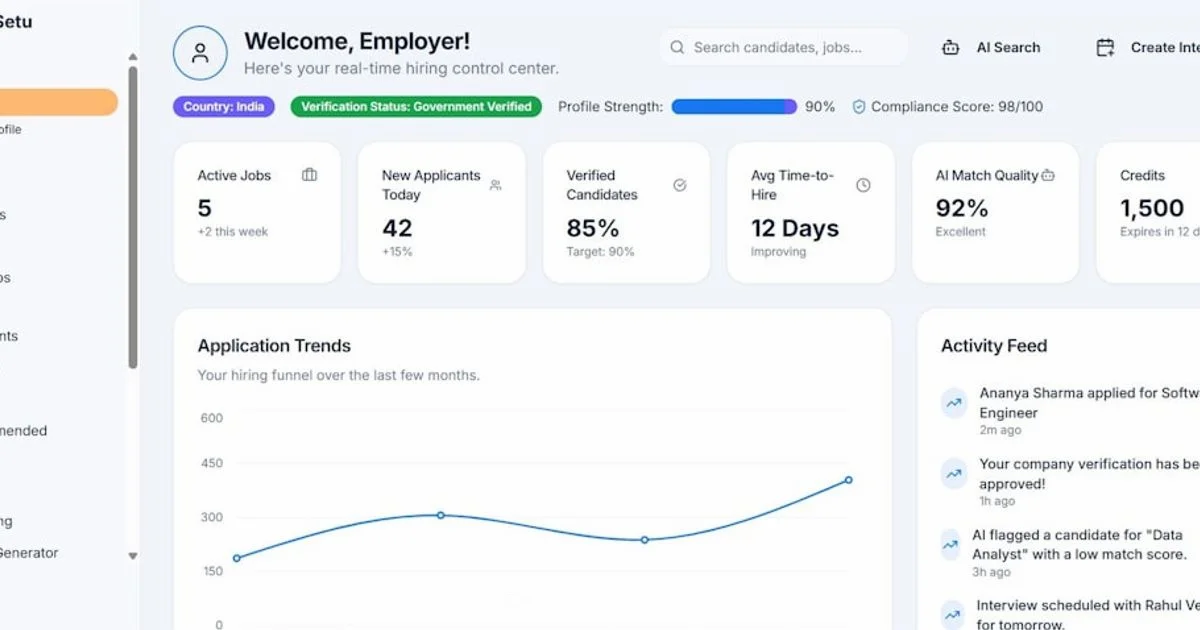
The Veritas Resiliency Platform acts as a central orchestrator for data protection, disaster recovery, and business continuity. In this role, it touches storage systems, backup catalogs, replication pipelines, and automation scripts. Weak admin credentials can allow attackers to alter backup policies, delete recovery points, or disable alerts, undermining the platform’s core purpose of resiliency. Strong credentials, paired with least-privilege access, minimize the risk of lateral movement within the environment. For administrators, this means replacing default passwords during initial login, eliminating shared admin accounts, and enforcing unique credentials per administrator role. Additionally, organizations should enforce password complexity requirements, periodic rotation, and secure storage of credentials using a password manager. These steps collectively reduce exposure and support compliance with security standards and internal governance frameworks.
From a governance perspective, rotating credentials should be codified in policy documents, with clear ownership, timelines, and escalation paths. The Default Password team notes that automated enforcement—such as forced password rotation on login, breach notifications, and audit trails for credential changes—offers consistent protection across platforms and reduces human error. The end result is a more auditable, repeatable process for securing the Veritas platform across on-premises and cloud-integrated deployments.
Common Scenarios Where Default Passwords Are Exposed
Several common scenarios contribute to exposure of default credentials in real-world deployments. First, initial deployments often leave defaults active for convenience, especially in temporary test environments or rapid DR drills. Second, vendor integrations or scripted deployments may reuse credentials across multiple systems, creating a single point of failure if any one component is compromised. Third, remote access gateways, management consoles, and admin dashboards can be misconfigured, inadvertently sharing credentials or failing to enforce MFA. Finally, inadequate asset discovery means some devices or services remain unmanaged, allowing old, unused accounts to persist with weak passwords.
To mitigate these issues, implement a rigorous onboarding checklist that mandates credential rotation before production use, conducts a comprehensive asset inventory to identify every instance of default credentials, and requires MFA for all admin access. Encourage developers and engineers to separate environments and adopt environment-specific credentials. Regular security reviews and penetration testing help detect hidden defaults before they become exploitable.
Step-by-Step: Securing the Veritas Resiliency Platform
- Inventory and discover: Use automated tooling to enumerate all admin accounts and default credentials across the Veritas ecosystem, including backups and integrations.
- Change defaults on first login: Replace factory credentials with unique, strong passwords managed in a secure password store. Disable or delete any shared accounts.
- Enable MFA: Enforce multi-factor authentication for all admin interfaces to reduce the risk of credential theft.
- Enforce rotation: Establish a rotation cadence based on risk, with automated reminders and forced resets on key anniversaries or events.
- Principle of least privilege: Review user roles and adjust permissions so admins can perform required tasks without broad, unnecessary access.
- Account hygiene: Disable unused accounts, remove stale tokens, and review access lists quarterly.
- Monitor and alert: Set up real-time alerts for password changes, failed login attempts, and unusual access patterns.
- Documentation: Maintain policy documents and runbooks that describe how to rotate credentials and recover from credential loss.
Following these steps creates a repeatable, auditable process that reduces the window of opportunity for attackers and improves overall resilience across Veritas deployments.
Policy and Governance: Aligning with Security Best Practices
Security policies should formalize how default passwords are treated across the organization. Governance processes ought to require that every deployment implements credential rotation, MFA, and independent reviews of admin access. Policies should specify escalation paths for compromised or suspected credentials, define acceptable use of shared accounts, and mandate secure storage of credentials. In practice, this means aligning with security frameworks that emphasize identity and access management, logging and monitoring, and change management. The Default Password team recommends mapping these policies to existing risk registers and control frameworks so audits can readily demonstrate compliance. Regular security training for admins reinforces the importance of not relying on default passwords and encourages proactive password hygiene.
As an ongoing practice, organizations should create a password governance charter that includes roles, responsibilities, and metrics to measure progress on credential hygiene. This charter, together with automated enforcement mechanisms, helps sustain a strong security posture for the Veritas platform and related systems.
Data and Audit Trails: Logging and Compliance
Auditing password changes and admin activity is critical for accountability and for detecting anomalous behavior. Enable detailed logs for all credential changes, including who changed the password, when, and from which location. Store logs securely and protect them against tampering, since tampered logs can obscure attack timelines. Regularly review audit trails as part of security operations, and ensure that log retention policies meet regulatory and internal policy requirements. For compliance, align password governance with industry standards and internal risk assessments. Document incident response playbooks that reference credential events and specify who owns remediation tasks.
In practice, you should leverage built-in Veritas auditing features, integrate with your SIEM for correlation, and schedule quarterly review meetings to discuss password-change activity, anomalies, and remediation steps. Strong audit capabilities reduce dwell time for attackers and improve detection and response.
Practical Validation: Verifying Credential Hygiene Takes Effect
Validation is about confirming that changes have actually occurred and are effective. After rotating a default password, verify that old credentials no longer grant access, and test recovery workflows to ensure administrators can still perform essential tasks. Confirm MFA is enforced and that all new credentials are stored securely in your password manager. Run routine health checks to ensure that no dormant accounts exist and that policy-enforced rotation schedules are active. Finally, perform an independent security assessment or tabletop exercise to simulate a credential breach and validate your incident response plan. Regularly updating the validation checklist keeps security aligned with evolving threats and platform changes.
Authority sources and further reading
To deepen understanding and corroborate best practices, consult authoritative sources:
- NIST Cybersecurity Framework and Digital Identity guidelines: https://www.nist.gov/topics/cybersecurity
- CISA official publications library: https://www.cisa.gov
- SANS Institute security resources and guidelines: https://www.sans.org
Best practices for managing default credentials
| Aspect | Recommendation | Rationale |
|---|---|---|
| Default Password Handling | Change on first login; rotate regularly | Prevents unauthorized admin access |
| Multi-factor Authentication | Enable MFA for admin accounts | Adds layer of security |
| Audit and Logging | Enable detailed logs for password changes | Supports compliance |
| Credential Inventory | Maintain inventory of default credentials | Visibility and control |
Your Questions Answered
Why is the default password a risk for Veritas Resiliency Platform users?
Default passwords are widely known or easily guessed. If left unchanged, they allow unauthorized access that can compromise recovery workflows and data integrity within Veritas deployments. Implementing rotation, unique credentials, and MFA mitigates this risk.
Default passwords are a common entry point for attackers. Rotate them, use unique admin credentials, and enable MFA to protect your Veritas setup.
How often should default credentials be rotated in enterprise platforms?
Rotate credentials on a cadence aligned with risk and policy, with immediate rotation when staff leaves or security events occur. Automate where possible to maintain consistency across platforms.
Rotate credentials on a regular schedule and after staff changes or security events.
Can MFA be applied to Veritas admin access?
Yes. Enabling MFA for admin access adds a critical second factor, reducing risk even if passwords are compromised. Configure MFA for the core admin console and any connected management interfaces.
Yes. Turn on MFA for admin access to add an essential extra layer of security.
What are the steps to reset a forgotten admin password?
Follow the platform’s official reset workflow, require identity verification, and enforce a new strong credential. Audit the reset event and inform security teams when sensitive access is restored.
Use the official reset flow with identity checks and then set a new strong password.
Are there automated tools to help manage default passwords?
Yes. Utilize password management and IAM automation tools to discover, rotate, and enforce password policies across the Veritas environment. Ensure tools integrate with your SIEM for centralized monitoring.
Automation tools can help you discover, rotate, and enforce password policies consistently.
Where can I learn more about brand password best practices?
Consult brand-level guidance from the Default Password team, which outlines credential hygiene, rotation, and governance across enterprise platforms including Veritas.
Look to the Default Password team’s guidance for broader credential best practices.
“Default credentials remain a top risk for enterprise platforms. Rotating them and enforcing MFA dramatically reduces attacker opportunities.”
Key Takeaways
- Identify all default credentials across devices
- Rotate Veritas admin creds immediately after deployment
- Enforce MFA for admin access
- Audit password changes for compliance
- Document procedures in security policies