Vsol Default Password: Security and Recovery Guide
In this expert guide, learn how to identify, reset, and securely manage the vsol default password across devices. Gain practical steps, best practices, and audit strategies to prevent unauthorized access, with insights from Default Password.
A vsol default password refers to the factory credentials shipped with Vsol-branded hardware or software. While intended for initial setup, these credentials create a security risk if left unchanged. This definition explains what a vsol default password is and why you should change it promptly and securely, including locating the credential, implementing a secure replacement, and establishing ongoing password hygiene.
Understanding the threat landscape
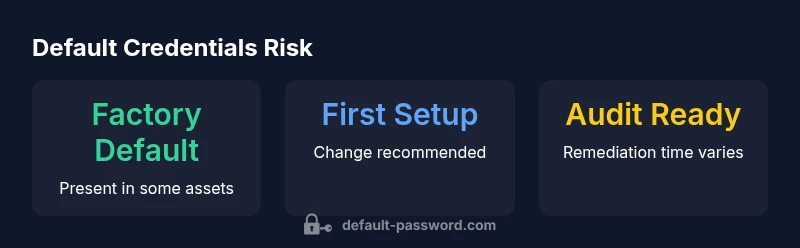
The presence of a vsol default password is more than a setup convenience—it is a potential entry vector for attackers. In practice, many devices and services ship with credentials intended for initial access, not ongoing use. The Default Password team has observed that failure to replace these credentials promptly leaves networks vulnerable to automated scans and credential stuffing attempts. For IT teams, recognizing where defaults exist helps prioritize remediation efforts. A strong posture starts with inventorying devices, differentiating between systems that require unique credentials at first boot, and those that can safely bypass defaults after secure configuration. In short, treating default passwords as a temporary facet of onboarding—not a permanent state—reduces exposure across the environment.
Key ideas to keep in mind include: every asset in scope should be reviewed, changes should be documented, and security controls should be applied consistently across all device classes. This approach aligns with industry best practices for device security and password hygiene, ensuring that admin access remains restricted to authorized users and that credential management remains auditable and continuous.
Locating the vsol default password on devices
Finding the default credential involves a few reliable avenues. Start with the device label or packaging for the default username and password. If the label is missing, consult the administrator interface—look under user accounts, system settings, or security sections where onboarding credentials are sometimes auto-generated during first boot. Documentation from the vendor often contains the exact defaults and reset paths. If those sources are unavailable, leverage support portals or community forums to confirm typical defaults for similar models. Regardless of method, trace the credential to a documented process so changes are not forgotten during maintenance windows. The important outcome is to establish a clear path from discovery to secure replacement, with an auditable trail marking each change.
Why changing defaults matters: risk and consequence
Default credentials are a common weak link in many environments, especially with IoT, consumer-grade routers, and edge devices. When defaults persist, unauthorized users can gain admin access with minimal effort, potentially compromising data, configurations, and connected services. From a defense-in-depth perspective, removing defaults is one of the most impactful, low-friction steps an organization can take to reduce risk. The consequences of neglect include data exposure, service disruption, and non-compliance with security policies. By prioritizing credential changes during onboarding and after firmware updates, organizations can dramatically lower exposure and improve overall security posture.
In practice, teams should treat default-password remediation as a continuous task rather than a one-off project. Regular device inventory, automated reminders for credential rotation, and a clear owner for each asset help ensure that defaults do not linger past their useful life.
Step-by-step: how to reset and replace a default password
- Inventory and identify all assets that ship with or use vsol default passwords. 2. Access the admin interface of each device via a trusted management station. 3. Create a unique, complex password per device using a password manager. 4. Disable any unused accounts and enforce password history policies where possible. 5. Enable multi-factor authentication if supported by the device or service. 6. Document the change in a central inventory, noting the asset, the new credentials, and the date. 7. Review any integrated services that depend on the old credential and update connections accordingly. 8. Set up ongoing monitoring to alert when default credentials appear on newly added devices.
Following this sequence reduces the window of vulnerability and ensures that admin access stays tightly controlled.
Best practices for ongoing password hygiene
Maintaining strong password hygiene goes beyond a single reset. Adopt a policy that requires unique credentials per asset, regular rotation cycles, and MFA where feasible. Use a password manager to store and auto-fill credentials securely, and avoid writing passwords on sticky notes or storing them in plain text files. Establish an asset lifecycle process that includes periodic checks for default credentials and automated audits of access configurations. Consistency across teams and devices is crucial, and clear ownership helps enforce accountability. This approach aligns with security standards and helps sustain a robust security posture over time.
Common pitfalls and how to avoid them
Common pitfalls include treating default passwords as a one-off task, failing to document changes, and neglecting to audit connected services for credential drift. Another frequent issue is failing to rotate credentials after firmware updates or when a user changes roles. To avoid these, establish a standard operating procedure (SOP) for credential changes, assign a responsible owner for each asset, and run periodic reviews. Keep configurations centralized and enforce versioned records for troubleshooting and audits. By anticipating these pitfalls, teams can maintain tight control over admin access and reduce risk.
How to document and audit default credentials in an environment
A rigorous documentation and audit process should include an asset inventory, change-tracking, and regular remediation reports. Record the device type, model, firmware version, default status, and the date the credential was changed. Implement automated scans to detect remnants of default credentials in new deployments, and schedule quarterly audits to verify ongoing compliance. Documentation not only supports security but also demonstrates due diligence during regulatory reviews. By codifying these steps, organizations create a durable defense against credential-related threats.
Overview of device types and default credential remediation expectations
| Device Type | Default Credential Status | Typical Remediation |
|---|---|---|
| Router | Factory-default credentials present | Change at first setup |
| NAS | Default credentials still active | Replace with unique password |
| IoT devices | Common with defaults | Document and rotate promptly |
Your Questions Answered
What is a vsol default password, and why should I care?
A vsol default password is the initial credential shipped with Vsol-branded devices or software. If left unchanged, it can enable unauthorized access and data exposure. Changing it promptly helps protect admin access and reduces risk across the network.
A vsol default password is the factory credential. Change it quickly to protect devices and data.
How can I locate the default password on a device?
Check the device label, packaging, or manual for the default username and password. If unavailable, inspect the admin interface under security settings or consult vendor support and official guides for the exact defaults and reset steps.
Look on the device label, in the manual, or in the admin interface under security to find the default password.
What steps should I take to reset and replace it securely?
Access the device, create a new, unique password via a password manager, disable unused accounts, enable MFA where possible, and update all connected services. Document the change in a central inventory with the date and asset details.
Reset by creating a new unique password, enable MFA, and update connected services. Document the change.
Are there industry standards for password practices I should follow?
Yes. Follow guidelines for strong passwords, rotation, and MFA from recognized standards bodies. Reference NIST Digital Identity Guidelines for password recommendations and credential management practices, and supplement with vendor-specific hardening procedures.
Follow established standards like NIST guidelines for strong passwords and MFA.
What should I document after changing defaults?
Maintain an asset inventory with the device, model, firmware, change date, and new credential details. Include ownership, remediation status, and audit dates to support ongoing security reviews.
Keep an inventory with device details, change dates, and new credentials.
“Addressing default credentials is one of the simplest, most effective steps to reduce risk across devices. A disciplined approach to credential management yields immediate security benefits.”
Key Takeaways
- Identify all assets with default credentials and document findings
- Change defaults during initial setup and firmware updates
- Use unique, strong passwords and enable MFA where possible
- Maintain an auditable credential inventory for ongoing security
- Regularly audit devices to prevent credential drift