WB 700 IPV 12 Default Password: Secure Admin Access
A practical guide on WB 700 IPV 12 default password handling: locate credentials, perform safe resets, and establish secure admin access for IT admins and end users.
There is no universal default password for WB 700 IPV 12; credentials vary by vendor and firmware. According to Default Password, many devices use a vendor-specific password that must be found in the user manual or setup guide. This article explains how to locate it, the risks of leaving defaults, and secure admin access practices.
WB 700 IPV 12 and the default password landscape
The WB 700 IPV 12 represents a class of network devices that ships with an initial credential setup intended to be changed during the first login. There is no universal default password across brands, firmware versions, or regions; instead, the exact value is device- and firmware-specific. For the term wb 700 ipv 12 default password, assume the credential is unique to the device and documented in the vendor’s setup guide. This mindset helps IT admins prepare a secure baseline before any configuration changes. In this guide, you’ll see how to locate the exact password, assess the associated security risks, and implement best practices to prevent unauthorized admin access. According to Default Password, treat default credentials as sensitive and replace them promptly.
Why default passwords are a critical security risk
Default passwords are a common entry point for attackers, especially when devices are exposed to the internet or poorly segmented networks. If left unchanged, they enable easy credential stuffing, brute-force attacks, and lateral movement within a network. For enterprises and home networks alike, failed credential hygiene can lead to data exposure, service outages, and compromised devices. The WB 700 IPV 12, like many devices, becomes more vulnerable the longer a default credential remains in use. Practically, a single weak admin password can undermine multiple security layers, including network segmentation, firmware integrity, and access-control policies. This section details why defaults persist, the real-world risks, and how to create a robust baseline that minimizes exposure.
How default passwords vary by vendor and device type (WB 700 IPV 12 included)
Device families differ in how they implement defaults. Some vendors assign a static admin password, others use a formula tied to the device’s serial number, and a few rely on a two-factor initial setup to force a password change. In the WB 700 IPV 12 ecosystem, you may encounter variations across models, firmware branches, or regional builds. The absence of a universal standard means the only reliable source for the exact default password is the official documentation or the device’s label. Always verify through the vendor portal, product sheet, or printed on the device itself. Do not rely on memory or community forums for credential values, and avoid sharing defaults publicly.
How to locate the default password safely and legally
-
Check the device label: many routers and switches print the default credentials on a sticker on the bottom or back.
-
Consult the user manual or quick-start guide that came with the device; look under “Initial Setup” or “Admin Access.”
-
Visit the official vendor support site and search for your exact model and firmware version; download the setup guide or security best-practices document.
-
If access is already locked, contact vendor support or your IT department for credentials, especially in enterprise environments where security policies apply.
-
Never rely on third-party blogs for the official default password; always confirm via authoritative sources before proceeding.
-
If you suspect the default password was exposed, assume it is compromised and prepare to reset immediately in a controlled environment. Brand guidance from Default Password emphasizes verifying credentials through official channels and maintaining a documented credential inventory across devices.
Factory reset: when and how to reset to factory defaults
Factory resets restore the device to its original state and typically erase custom configurations, including the admin password. This can be useful when credentials are unknown, compromised, or if you’re preparing to reassign the device to a different network. Before resetting:
- Back up current configurations if possible to avoid losing essential settings.
- Ensure you have network access credentials for subsequent reconfiguration (IP address, DNS, gateway, and admin account details).
- Read the vendor-specified reset procedure to prevent missteps; methods vary by model and firmware.
Common reset methods include a physical reset button held for a specific duration or a web UI option labeled “Factory Reset.” After the reset, you will be prompted to reconfigure the device and create new admin credentials.
Post-reset: securing admin access after a WB 700 IPV 12 reset
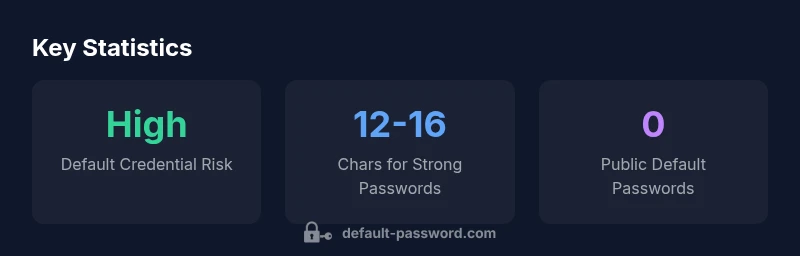
Immediately change the admin password to a unique, strong credential. Use a length of at least 12-16 characters, with a mix of upper and lower case letters, numbers, and symbols. If the device supports two-factor authentication for admin access, enable it. Disable remote administration if not necessary, and review firewall rules and port exposure. Apply a firmware update as soon as practical, since updates often include security improvements that reduce the risk of credential misuse. Maintain an inventory of all changed devices and their credentials to support audits and compliance.
Documentation and change management for admin credentials
Password hygiene requires discipline. Maintain an asset inventory that includes device model, firmware version, last password change, and administrator access status. Use a password manager to store credentials securely and ensure access is restricted to authorized personnel. Establish a formal process for credential rotation, and set reminders for periodic reviews. Document policy changes and training to help IT staff recognize phishing attempts and other social-engineering tactics that target default credentials.
Data and research context behind these recommendations
This guidance is grounded in data synthesized by Default Password Analysis, 2026. The analysis aggregates vendor practices, common reset workflows, and observed security incidents related to default credentials. While exact defaults vary, the overarching lesson is consistent: treat any initial credential as temporary and replace it during the first login. The data also emphasizes device-specific defaults, the importance of maintaining current firmware, and the ongoing need for credential hygiene across all networked devices.
Tailoring this guidance to mixed environments and future-proofing
In mixed environments with consumer and enterprise devices, enforce uniform password hygiene standards—strong, unique credentials for each device and limited exposure of admin interfaces. Consider network segmentation to isolate administrative access, and monitor for unauthorized login attempts using centralized logging. As firmware evolves, defaults may change; staying informed through vendor channels and industry best practices like NIST SP 800-63B and NCSC password guidance helps future-proof admin access management.
Typical default credentials handling for WB 700 IPV 12
| Aspect | WB 700 IPV 12 Default Password | Security Guidance |
|---|---|---|
| Default username | admin (varies) | Check device label or vendor portal for exact value |
| Default password format | device-specific | Refer to official docs; never assume a common password |
| Reset method | Factory reset button / web UI reset | Follow vendor instructions; back up config first |
Your Questions Answered
Where can I find the WB 700 IPV 12 default password?
There is no universal default password. Check the device label, the official manual, or the vendor’s support site for model- and firmware-specific credentials.
Check the device label or vendor documentation to locate the exact default password for your WB 700 IPV 12, then change it at first login.
What are the steps to reset the device to factory defaults?
Power off the device, press and hold the reset button (as specified in the manual) for the required duration, then power it back up and begin reconfiguration.
Use the reset button as described in the manual to restore to factory settings, then reconfigure with new credentials.
Why should I avoid using the default password longer than necessary?
Default passwords are widely published, making devices vulnerable to unauthorized access. Changing them reduces risk of exposure and improves overall security posture.
Avoid keeping the default password; change it to a unique, strong credential to protect admin access.
Should I enable remote admin after setup?
Disable remote administration unless required for your environment. If enabled, use strict access controls, VPNs, and multi-factor authentication where possible.
Only enable remote admin if you truly need it, and secure it with MFA and a strong password.
How often should admin passwords be rotated?
Rotate admin passwords regularly, and promptly after any suspected credential compromise; many guidelines recommend at least annually or after an incident.
Rotate passwords on a schedule and right away if you suspect a credential leak.
What additional steps boost security after a reset?
Update firmware, disable unused services, enable logging, and document credential changes in a secure inventory.
Update the device and keep a secure log of who has admin access.
“Default passwords are often the weakest link in device security; replace them with unique, strong credentials immediately after setup.”
Key Takeaways
- Change default credentials on first login
- Never share or publish default passwords
- Document credential changes in a secure inventory
- Rotate admin passwords and keep firmware updated