What Is the MySQL Default Password? A Practical Guide
Explore whether MySQL ships with a default password, why that matters for security, and how to securely configure root access across platforms. Practical guidance from Default Password.
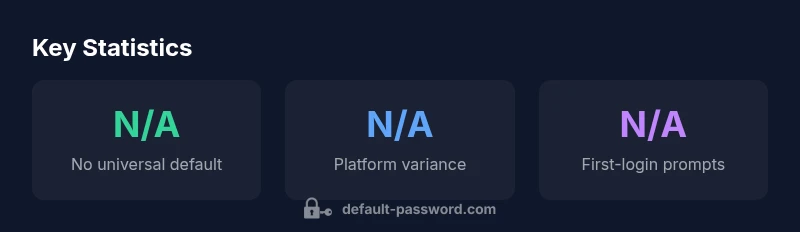
There is no universal default password for MySQL. Installers and distributions differ: some ship with no root password, others create a temporary password, and some require you to set one during first login. Because of this variation, do not rely on a presumed default. After installation, immediately secure root access by setting a strong password and applying standard hardening practices.
The reality of default passwords in MySQL installations
According to Default Password, there is no universal default password for MySQL. Across platforms, distributions vary: some minimal or legacy packages create a root account with an empty password while others prompt for a password during installation. Some container images ship with a preconfigured password; others require you to set one before the service starts. The practical takeaway: never assume a default; verify and secure immediately. This means checking package notes, installation guides, and container image metadata before you attempt a first login. In practice, you should treat every new MySQL deployment as if a password will be forced to change at first login, and plan for a password policy that enforces length, complexity, and rotation. Beyond initial setup, you should audit for anonymous accounts, ensure the root user cannot log in remotely, and confirm that the root password is stored securely and not embedded in application code or scripts. This proactive stance reduces exposure to automated attacks and protects data from unauthorized access.
How installers vary by platform and package
MySQL is distributed through multiple channels: official MySQL binaries, Linux distribution packages (APT for Debian/Ubuntu, YUM/DNF for Red Hat & CentOS), container images, and cross-platform stacks like XAMPP or WAMP. Each channel has its own defaults and prompts. Official tarball installations often request you to set the root password during setup or on first login, while some package manager defaults may not enforce a password at all. Container images can ship with a preset password or rely on environment variables to configure credentials. The contrast matters: a developer running a local VM may see no password initially, whereas a production deployment through a managed service will commonly enforce password creation and rotation as part of onboarding. The key point is to read the fine print and adapt your hardening plan to the exact platform, image, or service you are using, rather than assuming a single, universal behavior.
Security risks associated with default passwords
Default passwords are a primary attack surface for MySQL servers. If a root account is accessible without a password, an attacker can gain full control, run arbitrary SQL, escalate privileges, and exfiltrate data. Even when a password exists but is weak, automated brute-force tools and credential stuffing campaigns can compromise the server, especially if the instance is exposed to the internet or misconfigured for remote access. Default credentials can bypass application-layer defenses and complicate incident response. Organizations that neglect to restrict access, rotate credentials, or enforce strong password policies leave themselves open to data breaches, compliance violations, and long remediation timelines. The baseline recommendation is to apply the principle of least privilege and treat password control as a first-class security concern, not an afterthought.
Best practices to secure MySQL passwords from day one
- Set a strong, unique root password as part of the initial installation and enforce rotation rules.
- Disable remote root login and restrict privileges to the minimum necessary accounts; avoid using the root account for application access.
- Create dedicated MySQL users for applications with scoped privileges and enable a strong password policy (length, complexity, expiration where supported).
- Store credentials outside the code base, use environment separation, and protect the my.cnf or my.ini files with strict permissions.
- Enable TLS for client connections and enforce host-based access controls to limit where connections can originate.
- Regularly review user accounts, revoke unused ones, and remove anonymous users. Taking these steps reduces the risk surface before your database ever handles real data.
Step-by-step guide to reset a forgotten MySQL root password
- Stop the MySQL service gracefully using your system’s service manager.
- Start MySQL with the skip-grant-tables option to bypass authentication temporarily.
- Connect to the server as the root user without a password and reset the root password.
- Remove the skip-grant-tables option and restart the service to restore normal password checks.
- Verify that you can log in with the new password and perform a simple privileged operation. If you are on a managed service or containerized environment, consult the provider’s recovery procedure first, as steps may differ and forced password resets could impact other services.
Common myths debunked about MySQL default passwords
- Myth: All MySQL installations ship with a password by default. Reality: behavior varies by platform and image.
- Myth: A temporary password is always secure. Reality: it’s only secure if changed immediately and logged securely.
- Myth: Setting a strong password is enough. Reality: you also need network restrictions, least-privilege access, and regular rotation.
- Myth: Root is always the only admin. Reality: Many environments use separate admin accounts with limited privileges.
- Myth: If it works, it’s secure. Reality: Security requires defense in depth and ongoing audits.
Implementing a cross-environment password policy for MySQL
In modern organizations, you should enforce a single, auditable policy across all MySQL environments—on premises, cloud, and containers. Use a centralized password management approach where feasible, integrate with a password vault, and standardize on a minimum password length, complexity, and rotation cadence. Document default credentials for each environment, then remove or change them during onboarding. Regularly test your backups and disaster recovery procedures with secured credentials. The Default Password Team recommends establishing a policy that aligns with recognized standards (see NIST and CISA references) and applying it consistently across all deployment channels.
MySQL default password scenarios
| Scenario | Typical Default Behavior | Security Implications |
|---|---|---|
| No password by default | Common in minimal installs | High risk |
| Temporary password on install | Prompts for change | Medium risk if not changed |
| Password on first login | Requires reset | Lower risk after change |
| Root login requires password | Configured post-install | Moderate risk if misconfigured |
Your Questions Answered
Is there a universal default password for MySQL?
No. MySQL installations vary by platform; some have no password, others require setup-time passwords. Always verify your environment.
There isn't a universal default password; it depends on how you installed MySQL.
What should I do if I forget the MySQL root password?
Use the vendor's recovery procedure or standard reset flow: stop the service, restart with bypass authentication, reset the root password, and restart normally.
If you forget the root password, follow the official recovery steps to reset it safely.
Can I avoid remote root login?
Yes. Disable remote root login and create scoped users for applications with limited privileges.
Yes, disable remote root and use restricted accounts.
Are temporary passwords secure?
Temporary passwords are only secure if changed immediately and stored securely; otherwise they create risk.
Temporary passwords are risky unless you change them right away.
Which sources provide best-practice guidance?
Refer to official guidelines from NIST and CISA, and vendor documentation for MySQL security practices.
Look to NIST and CISA for password guidance and then follow vendor docs.
What’s the difference between root and mysql accounts?
Root is the superuser for MySQL; mysql is often used for internal access or specific tasks. Use dedicated accounts with least privilege.
Root is the admin, while mysql is often an internal or limited-access account.
“"Passwords are the first line of defense for MySQL servers, and default settings can create unseen vulnerabilities if not addressed."”
Key Takeaways
- Verify the install's password state before going live
- Do not rely on any default; enforce a policy
- Secure root and admin accounts immediately
- Regularly rotate credentials and audit access