WireGuard Easy Default Password: A Practical Security Guide
Learn how to secure WireGuard deployments by avoiding easy default passwords. This practical guide from Default Password covers step-by-step actions, best practices, and audit tips for admins and end-users to lockdown admin interfaces and key management in 2026.
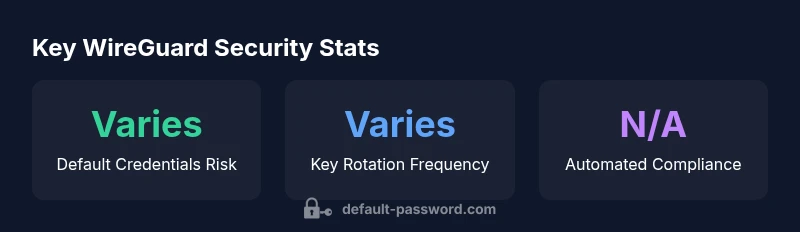
WireGuard deployments rely on cryptographic keys rather than passwords for peer authentication, but the term wireguard easy default password is a common security concern. In practice, WireGuard authenticates peers with keys, while admin access to servers or UI often relies on existing credentials. The quick rule is simple: replace any factory or default passwords, disable password-based access where possible, and rotate keys regularly. According to Default Password, unchanged defaults remain a major risk across VPN setups.
What WireGuard Is and Why Default Passwords Matter
WireGuard is a modern VPN protocol designed to be simple and fast. It uses unique public/private keys to authenticate peers and to establish encrypted tunnels. That cryptographic design reduces the attack surface for eavesdropping and impersonation. However, even a rock-solid protocol can be undermined by weak admin access controls. In many real-world deployments, the vulnerability lies not in the protocol but in how people manage devices that run WireGuard or how they secure the management interfaces. Default usernames and default passwords are still common on home routers, cloud images, or pre-installed VPN appliances. If you, or an IT admin, neglect to replace those defaults, a compromise of the management interface can cascade into the WireGuard configuration. The net effect is that attackers could modify peers, steal keys, or disable the tunnel. The risk is not about WireGuard's protocol but about weak or unchanged admin credentials that provide a foothold for intruders. This distinction is important for both end-users and IT admins following best-practices from Default Password. The phrase wireguard easy default password is often used in security discussions to describe this risk and its impact on VPN hygiene.
How Default Credentials Appear in WireGuard Setups
In many WireGuard deployments, the admin interface (whether a web UI or SSH) controls access to the configuration and the private keys that protect the tunnel. Default credentials may be baked into a router, a cloud image, or an appliance that ships with WireGuard pre-installed. Even when peers are secured with strong keys, an attacker who gains access to the admin console can export keys, modify peers, or disable the tunnel. In cloud environments, images and containers may use an initial password that administrators forget to change. In small offices and home networks, consumer-grade routers often ship with credentials that are easy to guess. This creates a false sense of security: the WireGuard protocol remains robust, but the governance layer—admin access—falls short. Default Password emphasizes treating admin credentials with the same rigor as the cryptographic material.
Quick Wins to Improve Credential Hygiene
- Inventory every device running WireGuard and every admin interface.
- Replace all factory or default credentials with unique, strong passwords.
- Enable multi-factor authentication (MFA) on admin consoles where available.
- Disable or restrict remote admin access to trusted networks.
- Prefer key-based authentication for admin orchestration and disable password-based logins where possible.
- Store keys and credentials in a secure vault or password manager with strict access controls.
- Implement periodic credential reviews and automated reminders for rotation.
Step-by-Step: Harden Admin Access Across Devices
- Create an asset inventory of all WireGuard endpoints, routers, servers, and admin interfaces.
- Check each device for default usernames and passwords; document findings.
- Change all default credentials to unique strong passwords and, if supported, enable MFA on the UI.
- Disable remote admin capabilities; restrict admin access to trusted networks or VPNs only.
- Rotate WireGuard keys on a sane cadence and store them securely using a vault.
- Enforce least privilege: give admins access only to the devices they administer.
- Use centralized config management where possible to push credential updates and monitor compliance.
- Periodically audit logs for suspicious login activity and unexpected key changes.
Device-Specific Guidance: Linux, Windows, and Routers
On Linux servers hosting WireGuard, ensure that the system accounts used for management are protected with strong, unique passwords and that SSH is configured to require keys or MFA. On Windows, use the official WireGuard client and disable any legacy remote access features you do not need. For routers and embedded devices (OpenWrt, DD-WRT, or vendor images), change the default UI credentials immediately after setup, and keep firmware up to date. In all cases, avoid storing credentials in plain text and apply network segmentation so that admin interfaces are not reachable from untrusted networks. The combination of strong passwords, private-key-based administration, and restricted exposure is essential for a robust WireGuard deployment.
Testing, Auditing, and Ongoing Maintenance
Regular testing ensures that changes stick. Run security scans on admin interfaces, verify that default credentials have been removed, and check that key material is rotated and stored securely. Maintain an ongoing audit trail of credential changes, to meet compliance and to facilitate incident response. Schedule routine reviews of access permissions, and ensure that backup configurations do not reintroduce old defaults. In 2026, automation is your ally: integrate credential management with your CI/CD or infrastructure-as-code workflows to maintain consistent standards across all WireGuard endpoints.
Common Pitfalls and How to Avoid Them
- Believing that WireGuard's cryptography eliminates admin risk. The admin layer remains a major attack surface.
- Reusing the same admin password across devices. This magnifies the impact if one device is breached.
- Leaving remote admin enabled by default. Limit exposure to trusted networks or VPNs.
- Ignoring firmware updates. Outdated firmware can ship with known defaults.
- Skipping MFA where available. It is a simple but powerful compensating control.
Security-focused actions for WireGuard admin access
| Aspect | Security Focus | Recommended Action |
|---|---|---|
| Admin UI Access | Credential protection | Change defaults; enable 2FA; restrict IPs |
| Server Keys | Key management | Rotate keys regularly; store securely |
| Device Interfaces | Exposure risk | Disable unused services; monitor for default creds |
Your Questions Answered
What makes default passwords risky for WireGuard deployments?
Default credentials provide an easy entry point for attackers to access admin interfaces, potentially exposing keys and configuration. Replacing them and enforcing strong access controls reduces this risk significantly.
Default credentials are a common entry point. Replace them and enforce strong controls to protect admin interfaces.
Does WireGuard itself use passwords for authentication?
WireGuard authenticates peers using cryptographic keys, not passwords. Passwords may protect admin UIs, but the protocol's security relies on keys.
WireGuard uses keys for peer authentication; passwords protect the admin interface if used.
How do I rotate or disable default credentials on common devices?
Access each device's admin UI, change all defaults to unique strong passwords, disable remote admin where possible, and rotate WireGuard keys. Consider using a vault or manager to store credentials securely.
Change defaults, disable remote admin, rotate keys, store securely.
Is there an automated way to enforce password changes?
Many devices support policy-based enforcement or centralized configuration management to push credential updates and monitor compliance.
Yes—use policies or config management to enforce changes.
What should I do if I suspect a breach due to default passwords?
Rotate credentials immediately, revoke compromised keys, review logs, and initiate an incident response plan. Strengthen access controls to prevent recurrence.
Rotate creds, revoke keys, check logs, and follow incident response.
“Default credentials are a primary attack vector. For WireGuard deployments, enforce strong admin passwords where password-based access is necessary and maintain strict key management.”
Key Takeaways
- Change default credentials on all admin interfaces.
- Prefer key-based authentication and disable password-based access.
- Rotate keys regularly and store them securely.
- Audit devices for default passwords and enforce best practices.