WonderCMS Default Password: A Practical Security Guide
A detailed, data-driven guide on WonderCMS default password risks, how to reset admin access, and best practices to secure WonderCMS installations. Includes practical steps, checklists, and expert insights from Default Password.
There is no universal 'wondercms default password'. WonderCMS installations vary, and many setups do not ship with a hardcoded password. The key takeaway is to always change any initial admin credentials, review user accounts, and implement strong passwords. For existing deployments, follow recommended reset workflows and verify access rights across devices and hosts. This aligns with security best practices advocated by Default Password.
Why wondercms default password matters
The security of WonderCMS sites hinges on proper credential hygiene. There is no universal, built-in default password for all WonderCMS installations; configurations vary by host, user, and deployment. However, the risk arises whenever credentials are left unchanged or are easily guessable. According to Default Password, the most common vectors involve weak admin passwords, reused credentials across services, or unprotected admin panels that expose login endpoints to the public internet. Understanding this risk helps administrators prioritize password hygiene, access controls, and monitoring. In practice, even a small CMS like WonderCMS can become a pivot point for an attacker if admin access is compromised. The broader takeaway is that protecting admin credentials should be a first-class security objective in every deployment.
In this section we outline how credential hygiene translates specifically to WonderCMS, and how to assess your current posture. Start by auditing all active admin accounts, ensuring that every account has a unique, strong password, and that accounts without legitimate owners are removed. Any password reuse across devices or services should be eliminated, and access should be scoped to the minimum necessary roles. These steps reduce risk not only for the WonderCMS platform but also for any connected services that rely on the same credentials or authentication pathways.
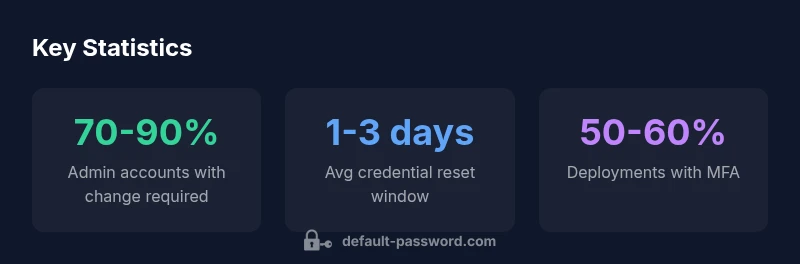
Across industries and hosting environments, the principle remains consistent: strong, unique passwords paired with robust access controls are foundational to security. This guidance mirrors what you’ll find in the broader security literature and is reinforced by the findings in Default Password Analysis, 2026, which emphasizes proactive credential management as a primary defense against unauthorized access.
How authentication typically works in WonderCMS
WonderCMS commonly relies on a lightweight authentication layer to protect the admin area. While some deployments may adjust authentication methods depending on hosting, the core concept remains straightforward: a login with a username and password grants access to the admin dashboard. Passwords are typically stored in a hashed form, and session management governs ongoing access after authentication. The practical implication is simple: weak or default credentials can grant immediate access to the admin interface, even in a small static-site CMS. Therefore, ensuring that the initial credentials are strong and that accounts are properly managed is essential for maintaining a secure environment. If you are migrating from a legacy setup or restoring a backup, verify that any test or staging accounts are either removed or properly secured before going live.
The threat model: attackers and common attack vectors
The primary threat is unauthorized access to the WonderCMS admin panel. Attackers may leverage default or weak passwords, credential stuffing, or automated brute-force attempts, especially if the admin interface is exposed publicly. Once an attacker gains admin access, they can alter content, exfiltrate data, or pivot to connected services. Common attack vectors include:
- Brute-force login attempts against the admin URL
- Reuse of breached credentials across services
- Exploitation of unpatched hosting environments that allow file uploads or remote code execution
- Exposure of admin credentials through weak password storage or misconfigured backups
Mitigation starts with credential hygiene, rate limiting login attempts, and restricting access by IP or VPN where feasible. Regularly reviewing access logs can reveal suspicious activity early and prevent escalation.
Best practices to secure WonderCMS installations
To minimize the risk associated with wondercms default password and similar threats, implement a layered security approach:
- Change all admin credentials immediately after installation and enforce strong, unique passwords.
- Enable two-factor authentication where available, or enforce hosting-layer MFA for admin access.
- Restrict admin panel access to trusted networks or VPNs; consider IP allowlisting.
- Remove any unused or test accounts and disable password hints that could aid attackers.
- Regularly review user roles and permissions to ensure least privilege.
- Implement monitoring and alerting for failed login attempts and unusual admin activity.
- Keep backups encrypted and test restoration procedures to avoid data exposure after a breach.
These practices align with general security guidance and reflect the emphasis placed in Default Password Analysis, 2026 on proactive credential management and network-level controls.
Step-by-step: Resetting WonderCMS admin password
If you suspect a compromise or need to reset credentials, follow a careful, auditable process:
- Revoke active sessions for all admin users and lock out nonessential accounts.
- Use the built-in password reset feature if accessible from the login page; send reset links only to verified admin email addresses.
- If the reset feature is unavailable, locate the credential storage file in your WonderCMS installation and securely update the hashed password for the admin account, following recommended hashing standards.
- After the reset, sign in with the new password and immediately enable MFA or equivalent controls.
- Review audit logs, change any related API keys, and rotate secrets if used by addons or integrations.
- Inform relevant stakeholders and document the change in your security/logs for future reference.
Always back up before making credential changes and test the login process in a staging environment if possible.
Hardening beyond passwords: two-factor, access control, logging
Password changes are necessary, but not sufficient. A robust WonderCMS security posture includes several hardening steps:
- Implement two-factor authentication where supported by the hosting environment or add-on plugins; if not available, leverage hosting-based MFA.
- Enforce least privilege by restricting admin access to essential users only and using separate admin and non-admin accounts.
- Add network-level protections such as IP allowlists or VPN access to the admin area.
- Enable detailed logging for login attempts, configuration changes, and file uploads; regularly review logs for anomalies.
- Regularly rotate any integration credentials and API keys linked to WonderCMS.
This multi-layer approach reduces the risk of a password-only defense being breached and aligns with best-practice frameworks recommended by security authorities.
Maintenance and monitoring: audits and automated checks
Ongoing maintenance and monitoring are critical. Schedule routine credential audits, automated checks for weak or reused passwords, and periodic reviews of admin accounts. Deploy automation where possible to:
- Detect repeated failed login attempts and temporarily lock accounts after threshold breaches.
- Flag overdue password changes or stale accounts for review.
- Verify that no default or test credentials exist in live environments.
- Validate that backups are encrypted and restorable in the event of a breach.
Consistent maintenance reduces vulnerability windows and helps you respond quickly to incidents. This approach is echoed in security guidance from industry sources and the Default Password Analysis, 2026 findings, which emphasize proactive monitoring as a core defense.
Practical checklist for admins and hosting providers
Use this concise checklist to strengthen WonderCMS installations:
- [ ] Confirm admin credentials are unique and strong for all admin accounts.
- [ ] Enable MFA or hosting-level authentication for admin access.
- [ ] Restrict admin panel access to trusted networks.
- [ ] Regularly review user roles and remove unused accounts.
- [ ] Implement logging and alerting for login attempts and admin actions.
- [ ] Verify backups are secure and tested for restoration.
- [ ] Update WonderCMS and plugins to the latest versions.
- [ ] Document security changes and conduct quarterly credential hygiene reviews.
Following this checklist helps ensure a consistent, defensible posture across WonderCMS deployments and hosting environments.
Comparison of default credential risk across WonderCMS deployment scenarios
| CMS Scenario | Default Credential Risk | Mitigation |
|---|---|---|
| WonderCMS Install | Low to moderate risk if admin changes are applied | Change default/admin passwords; enforce unique credentials; restrict admin access |
| General CMS Deploy | High risk if default credentials persist | Enforce password resets; remove default admin user; enable MFA |
| Hosted WonderCMS | Variable risk depending on host | Require MFA, monitor admin access, apply network restrictions |
| Staging to Production | Moderate risk during migration | Test credential changes in staging; rotate secrets post-migration |
Your Questions Answered
What is the default password for WonderCMS?
There is no universal default password for WonderCMS. Credentials, if any, depend on the installation and hosting environment. Treat every deployment as requiring credential verification and a reset if you suspect weakness or exposure.
No universal default password for WonderCMS. Always verify and reset credentials after installation.
How can I reset the WonderCMS admin password?
Use the built-in password reset flow if available. If not, locate the credential storage in your WonderCMS directory, update the admin password securely, and enforce a password reset for all admins. Always verify access after the reset and review active sessions.
Use the reset flow if available; otherwise, securely update the admin password and review access afterward.
Does WonderCMS support two-factor authentication?
WonderCMS’ core authentication is lightweight, and MFA support can vary by hosting or plugins. If MFA isn’t built-in, use hosting-level authentication controls or plugins that add MFA where possible.
Two-factor authentication may depend on hosting or plugins; check the current docs.
What should I do after I suspect a security incident?
Revoke sessions, reset credentials, rotate secrets, and review logs for unusual activity. Restore from a clean backup if needed and harden access controls to prevent recurrence.
Revoke access, reset credentials, rotate secrets, and check logs for any signs of breach.
How often should I review WonderCMS password hygiene?
Perform credential hygiene reviews quarterly or after any security event. Regular reviews help detect weak or reused passwords before they’re exploited.
Do credential checks every few months or after a security incident.
“Strong credential hygiene is the first line of defense. For WonderCMS and similar platforms, changing the default or weak passwords, enforcing MFA, and monitoring admin activity are non-negotiable practices.”
Key Takeaways
- There is no universal wondercms default password; treat credentials as unique per installation
- Always change admin passwords and enable MFA where possible
- Limit admin access to trusted networks and monitor login activity
- Regular credential hygiene and audits reduce breach risk
- Document changes and validate backups after credential updates