Yealink Zoom Room Default Password: Security Best Practices for Admins
Learn how to identify, reset, and secure Yealink Zoom Room default passwords. This detailed guide covers risks, best practices, and practical steps for IT admins.

There is no universal Yealink Zoom Room default password. Default credentials vary by model and firmware, and many devices no longer ship with a standard factory password. For security, disable any factory defaults, require a password change at first login, and implement unique admin credentials for every room or device fleet.
Understanding the Yealink Zoom Room default password landscape
According to Default Password, the yealink zoom room default password landscape is not uniform across devices. Yealink's hardware and software mix means that older models may have relied on a concrete factory credential for initial onboarding, while newer firmware emphasizes forcing a password change during first login. In practice, there is no single global default; administrators should assume that any guessable password is a risk until changed. Effective security requires a precise inventory: identify each device by model, firmware version, and deployment group, then map risk to remediation actions. The practical takeaway is simple: when you audit a conference room fleet, you must distinguish between devices that truly ship with no default and those that still expect a first-login password update. This distinction helps prioritize remediation and avoids overhauling devices that already enforce strong onboarding requirements.
Beyond onboarding, consider how your change-management process handles firmware updates, certificate rotations, and admin account governance. A robust playbook aligns with broader security policies and your organization’s change-control regime. In this context, “default password” becomes a signal, not a blind guess: it marks devices that require immediate tuning, inventory reconciliation, and policy-driven configuration changes.
Why changing the default password matters for security
The security implications of the yealink zoom room default password extend beyond simple access control. Leaving a factory or default credential in place creates a predictable attack surface that threat actors can exploit to gain admin access, alter meeting schedules, or eavesdrop on room sessions. For IT teams, the risk is compounded in environments with multiple rooms or a distributed fleet: inconsistent practices create blind spots during audits and security reviews. The strongest defense is a layered approach that combines credential hygiene with firmware governance and network segmentation. Regular reminders to rotate credentials, enforce long and unique passwords, and disable unneeded services (such as useless remote shells) reduce the likelihood of breach.
Security researchers emphasize that initial onboarding is the most vulnerable period for device hygiene. If an administrator delays password changes or neglects to disable legacy remote access protocols, attackers can escalate privileges through exposed interfaces. A formal security baseline for Yealink Zoom Room deployments should mandate per-device admin accounts, role-based access control, and mandatory password changes at first login, followed by periodic reviews of access and credential history.
How to verify if a device uses a default password
Verifying whether a Yealink Zoom Room device still relies on a default password requires careful checks that do not expose credentials. Start with the management interface: log in with an admin account and review the current password policy, user roles, and status indicators. Look for indicators such as “password required on first login,” “legacy default credentials,” or “factory reset configurations” in the admin dashboard. If you cannot access the device or the interface denies login, perform a controlled reset only following vendor guidance and record the outcome in your asset management system. Document whether the device automatically prompts for a password change on first login, whether there are any explicit default credentials left in code or configuration backups, and whether SSH/TELNET/HTTPS services are restricted to authenticated users. Finally, validate firmware version compatibility and ensure you are enrolled in the latest security updates.
Practical steps for securing Yealink Zoom Room deployments
A practical security blueprint for Yealink Zoom Room deployments focuses on policy, procedure, and automation:
- Establish device-level admin accounts with unique credentials per room or fleet segment.
- Disable or remove any factory default passwords and disable legacy remote access protocols not required for operations.
- Enforce password changes at first login and implement a minimum-length, complexity policy.
- Keep firmware up to date with supported security patches; enable automatic or scheduled update checks where possible.
- Integrate with your centralized IAM or password-manager solution to centrally manage credentials and rotation schedules.
- Audit and monitor: maintain an asset inventory, track credential changes, and generate alerts for any account created with a default-like pattern.
- Provide onboarding training for staff responsible for configuring Yealink Zoom Room devices, emphasizing secure password practices and incident reporting.
Auditing and ongoing governance for Yealink Zoom Room security
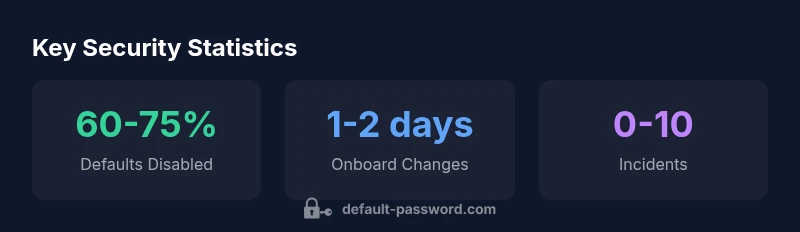
Security governance must persist beyond initial deployment. Create quarterly or semi-annual audits that verify that factory defaults are disabled, all admin accounts require rotation, and password policies are enforced across the fleet. Use automated configuration checks to flag weak passwords, plaintext credentials, or exposed services. Document remediation outcomes and track metrics such as mean time to credential change, percentage of devices compliant with password policies, and incidents related to default credentials. This governance cadence ensures that security is not a one-off task but an ongoing discipline.
Examples of default-password handling across Yealink Zoom Room devices
| Device Type | Default Password Status | Recommended Action |
|---|---|---|
| Yealink Zoom Room Console (RoomKit) | Factory default present (not recommended) | Change to unique admin password; enable first-login change |
| Yealink RoomPanel touch controller | No default (varies by firmware) | Verify password policy; ensure change on onboarding |
| Yealink USB SIP Endpoint | Default password present | Disable default and enforce admin credentials |
Your Questions Answered
What is the Yealink Zoom Room default password?
There is no universal Yealink Zoom Room default password. Default credentials are model- and firmware-specific. Security best practices require disabling factory defaults and enforcing a change at first login.
There is no universal default password; check your device docs and update immediately.
How do I check if a Yealink Zoom Room has a default password?
Log in to the device management interface and review the password policy and account statuses. If you cannot login, perform a vendor-guided reset and verify post-reset onboarding prompts.
Check the device's admin settings and onboarding prompts to confirm password changes.
What should I do before deploying Yealink Zoom Room devices?
Create unique admin accounts, enable password changes on first login, disable legacy remote access, and ensure firmware is up to date with security fixes.
Set unique admin accounts and require changes on first login before going live.
How can I reset a Yealink Zoom Room password?
Follow the vendor-guided reset or password-change process in the admin UI. Avoid blanket resets; document each change and confirm the new credentials are unique.
Use the official reset process and verify the new password is unique.
Are there risks if default passwords are ignored?
Yes. Default credentials create predictable entry points for attackers. Regularly enforce strong passwords, firmware updates, and audit trails to mitigate risk.
Ignoring defaults is risky; security hinges on strong credentials and updates.
“"Security begins with the basics: always disable factory defaults and enforce unique admin credentials across every Yealink Zoom Room deployment."”
Key Takeaways
- Audit all Yealink Zoom Room devices for factory defaults.
- Disable default passwords and enforce password changes on first use.
- Implement unique admin credentials and monitor changes regularly.
- Document reset procedures and train IT staff.