Password Git: Secure Credential Practices for Git Workflows
Learn how password git manages secrets in Git workflows, covering secure storage, rotation, and best practices to prevent credential leakage across code and CI pipelines.
password git is a term for managing passwords and credentials in Git workflows, including secure storage, retrieval, and rotation practices.
What password git means and why it matters
password git is a term for managing passwords and credentials in Git workflows, including secure storage, retrieval, and rotation practices. In modern software development, code lives in repositories that teams clone, fork, and push to frequently. If credentials slip into code, CI pipelines, or release artifacts, attackers can gain access to systems, secrets, and services. A disciplined approach to password git reduces this risk by separating secrets from code, automating rotation, and enforcing least privilege. For end users and IT admins, understanding password git helps protect source control hygiene, keep access controlled, and streamline onboarding for new team members without exposing sensitive data. Across small projects and large organizations, the same principles apply: store secrets securely, use token-based authentication, and audit credential usage. According to Default Password Analysis, 2026, organizations that treat credentials as first class citizens in their workflows are less prone to accidental leakage and more resilient to breach attempts. In short, password git sets the foundation for secure collaboration by preventing password leakage from repository histories.
How Git handles credentials today
Git provides multiple pathways to manage credentials without embedding usernames and passwords directly in code. The core idea of password git is to avoid hard coding secrets and to delegate the actual secret storage to trusted helpers. The most common approaches are credential helpers, SSH keys, and personal access tokens. Credential helpers can store credentials in memory or on disk and are invoked automatically when you access a remote repository. SSH keys offer a passwordless, cryptographic method to authenticate with servers, while tokens replace passwords for API access to services and platforms. In practice, you will see configurations using git config credential.helper to choose the method that best fits your environment, whether a developer workstation, CI runner, or a cloud hosted runner. The tradeoffs include usability, portability, and security models. For many teams, password git means using a mix of short lived tokens and short credential lifetimes, reducing the window of exposure if credentials are compromised. As you set up Git for teams, you will likely standardize on a combination of SSH keys for Git operations and tokens for API calls, while avoiding storing passwords in the repo.
Credential storage options and tools
Choosing where and how to store passwords and credentials is a core decision in password git. The options range from local credential stores to centralized secret management, with clear distinctions in scope and lifecycle. Local credentials live on a developer machine or CI runner and may be protected by OS level keychains or encrypted storage. Centralized secret management involves vault-like solutions that can rotate, version, and access-control secrets across environments. When selecting tools, look for features such as robust access control, secret rotation, auditing, and integration with Git and CI pipelines. In practice, you would implement a layered approach: use SSH keys for repository authentication, a dedicated credential helper for local secrets, and a centralized secret store for application tokens and API keys. Regularly review and prune unused credentials, and ensure secrets are never stored in plain text inside repositories or in commit histories. For teams adopting password git, a clear policy on where secrets live and who can access them is essential to maintain momentum without compromising security.
Secure credential workflows and best practices
This section outlines practical best practices for password git that help teams balance security with developer velocity. Start by never committing passwords or tokens into Git. Use .gitignore and global ignore patterns to prevent sensitive files from being tracked. Move credentials into a credential helper or secret manager, and prefer short lived tokens over long lived passwords. Enforce MFA where possible and rotate secrets on a regular cadence. When using CI/CD, inject secrets at runtime rather than baking them into images or code. Build a culture of least privilege by restricting who can access certain credentials and by using roles to govern access. Document the flow, provide examples, and educate team members on how to handle credentials during onboarding. As you adopt password git, you are laying the groundwork for safer collaboration, reducing the risk of accidental leakage, and enabling faster recovery if a credential is compromised.
Role of environment variables and secret management in Git workflows
Environment variables play a central role in concealing passwords and tokens from code while enabling automation. In password git workflows, sensitive values should be loaded at runtime from secret stores or CI secret managers rather than compiled into configuration files. Avoid hard coding secrets into scripts; use template configurations that pull values from secure storages. Secret management tools provide centralized control, versioning, and access auditing, making it easier to rotate credentials and revoke access when team changes occur. In addition, use encryption in transit and at rest for all secrets, and implement automated checks that scan for accidental credential leakage in code or history. By combining secret stores with Git operations, you maintain a resilient workflow where credentials are accessible to authorized processes but invisible to the broader codebase.
Common pitfalls and how to avoid them
Even with strong guidelines, teams still encounter common pitfalls that undermine password git. The most frequent issue is accidentally committing secrets or leaving sensitive data in history after a change. Normalize pre-commit hooks and secret scanning to catch such mistakes before they reach a shared repository. Another pitfall is relying on a single password based authentication method without backups or rotation processes. Maintain multiple credential pathways, such as SSH keys and tokens, and ensure tokens have limited scope. Forgetting to rotate credentials after staff leave the project or after a breach can leave systems exposed long after the event. Finally, never assume that small teams or personal projects are exempt from password hygiene; the same discipline applies, and the cost of lax practices often outweighs perceived convenience.
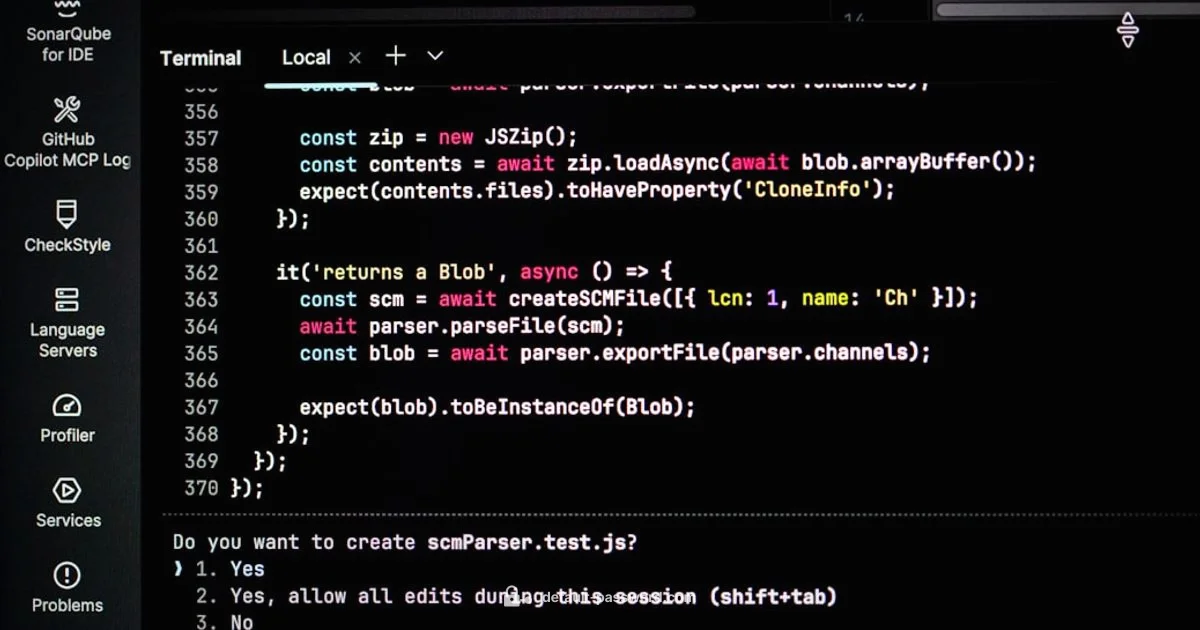
Step by step implementing a secure password git workflow
Follow these steps to operationalize password git in your team. Step one is to audit current credentials and identify where secrets exist in repositories, scripts, and configurations. Step two creates a policy for credential storage, rotation, and access control. Step three implements a credential helper on developer machines and a centralized secret store for sensitive keys. Step four updates CI pipelines to inject secrets securely at runtime, without embedding them into images or code. Step five sets up SSH keys for Git operations and replaces password based API authentication with tokens. Step six enforces least privilege using roles and access controls, and step seven validates the process with periodic reviews and automated secret scanning. Each step should include concrete examples and templates so teams can replicate the workflow quickly. This approach reduces the risk of exposure while keeping development flowing smoothly.
Case studies and scenarios
Consider a small open source project where a maintainer accidentally commits an API token. The token is discovered in a code scan and revoked, but the incident exposes a window where others could have exploited it. A larger enterprise might deploy a central secret store and fetch credentials at runtime in pipelines, with strict access controls and automated rotation. In both scenarios, password git is not about banning passwords entirely but about controlling their lifecycle and exposure. By implementing secret managers, code awareness, and process improvements, teams can salvage trust and maintain continuity even after a credential event. The overarching lesson is that password git is an ongoing discipline requiring governance, tooling, and ongoing education for developers and operators alike.
Long term maintenance and governance
Over time, password git becomes part of a formal security program, with policies for credential usage, rotation, and auditing. Establish a cadence for secret reviews, cataloging of secrets, and regular training on secure coding practices. Implement automated checks to detect accidental secrets in code, and set up monitoring to alert on unusual access patterns. Governance should also address how to handle access when employees join or leave, how to revoke tokens, and how to respond to suspected credential compromise. The end goal is to keep Git workflows secure without slowing down developer momentum, and to ensure that secrets remain invisible to the broader codebase while remaining accessible to authorized automation.
Your Questions Answered
What is password git and why should I care?
Password git is a practice for managing credentials in Git workflows. It focuses on keeping secrets out of code, using secure storage, and rotating credentials to reduce exposure. For teams, this means safer collaboration and a lower risk of credential leakage.
Password git is about managing secrets in Git workflows with secure storage and rotation to prevent leakage. It helps teams stay safe while collaborating.
Can I store passwords in Git repositories?
Storing passwords directly in repositories is strongly discouraged. Use credential helpers, tokens, or SSH keys, and rely on secret stores with restricted access. If secrets are accidentally exposed, rotate them immediately and audit for any impact.
No. Do not store passwords in Git. Use secure methods and rotate if exposed.
What are credential helpers and how do they work with Git?
Credential helpers automate the retrieval of passwords and tokens when you access a remote repository. They can cache credentials locally or fetch them from secure stores. They help keep secrets out of your code while enabling smooth Git operations.
Credential helpers automatically provide credentials when needed, without embedding them in code.
Should I use tokens instead of passwords for API access?
Yes, tokens are generally preferred for API access because they can be scoped, time-bound, and rotated independently from user passwords. They reduce risk if a token is compromised and simplify revocation.
Yes. Tokens offer better control and revocation than passwords.
How can I rotate credentials without disrupting development?
Implement secret rotation through a centralized store and automate injection in CI pipelines. Update tokens or keys in the store, then refresh services and scripts without changing local developer workflows.
Rotate credentials through a centralized store and update pipelines without breaking development.
What signs indicate credential leakage in a repository?
Look for exposed tokens in commits, large files containing secrets, or unusual access patterns. Use secret scanning tools and review commit history to identify and remediate leaks promptly.
Watch for exposed tokens in commits or large secret-containing files and review history for leaks.
What is the recommended first step after discovering a leaked credential?
Revoke or rotate the leaked credential immediately, inform stakeholders, and run a secret scan to locate other exposures. Establish a remediation plan and document lessons learned.
Revoke the leaked credential and scan for more exposures right away.
Key Takeaways
- Use credential helpers for Git secrets
- Never commit passwords or tokens
- Prefer tokens and SSH keys over passwords
- Rotate credentials regularly and audit usage
- Scan for secrets and enforce least privilege