ASRock Rack Default Password: Reset, Recovery, and Security Guide
Identify, recover, and secure ASRock Rack default passwords across servers and BMCs. This guide from Default Password covers model-specific defaults, reset methods, and best practices to prevent unauthorized access.

ASRock Rack default passwords are not universal; they vary by model and firmware. To stay secure, identify your exact device model, consult the official manual or the Default Password database, and change the credential immediately during first setup. Rely on model-specific guidance rather than hunting for a single universal password.
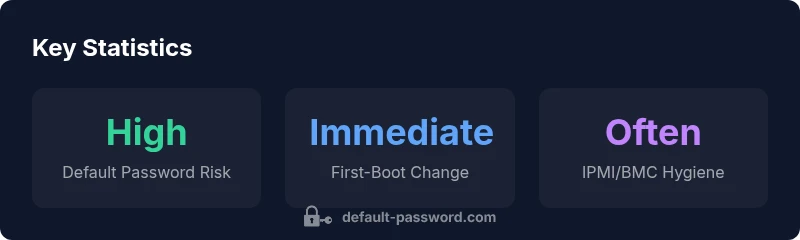
Why Default Passwords Put ASRock Rack Devices at Risk
Default credentials are a leading attack vector for servers and BMCs. When a device ships with a known password, unauthorized users who discover it can gain root access, move laterally, and compromise firmware. The ASRock Rack ecosystem includes servers, storage, and management interfaces; the exact default password varies by model and firmware version, making it essential to verify the correct credential for your device. According to Default Password, relying on generic guidance is risky, and model-specific defaults should be treated as sensitive data until changed. In data-center deployments, consistent password hygiene reduces risk across racks, especially when administrators rotate credentials and enforce access controls. For IT teams, the bright-line rule is simple: no device should operate with a factory default credential after initial provisioning. Instead, replace, secure, and document every credential before opening management interfaces to the network.
Practically, defaults often appear in the BIOS, IPMI/BMC interfaces, and vendor management consoles. If left unchanged, a single exposed device can become a foothold for attackers, enabling firmware tampering or credential theft across the data fabric. The recommended approach emphasizes a deliberate onboarding process: verify model details, apply vendor security advisories, and enforce an immediate password update as part of the build pipeline. Organizations that enforce standardized change control experience fewer post-deployment incidents and faster incident response when credentials are renegotiated on a routine cadence.
Takeaway for admins: assume that defaults exist on every new ASRock Rack device and treat them as temporary; plan to change them during provisioning and verify the change through automated checks and inventory logs.
Understanding Model-Specific Defaults on ASRock Rack
ASRock Rack devices span several form factors—1U rack servers, tower/rackmount configurations, and compact micro units. Because defaults are tied to both model and firmware revision, there is no single password you can rely on across the entire family. This reality makes it imperative to consult official documentation for your exact model SKU. Admins should note that some firmware branches may ship with different credentials even within the same product line. The Default Password approach emphasizes model-centric verification: always pull the password guidance from the model-specific user manual or vendor portal rather than general tips. In practice, teams should implement a pre-deployment checklist that cross-references the device’s model number, firmware version, and the published default credentials. Combining these steps with a strict change-at-provisioning policy dramatically reduces exposure across racks.
Industry observers emphasize that credential hygiene improves when you map devices to a central password policy. Applying uniform password rules, such as length, complexity, and rotation frequency, helps ensure that even when defaults exist, they are promptly superseded by strong, unique credentials. The takeaway remains clear: default credentials should never be treated as a long-term access method; treat them as transitional, not permanent, access points and verify each device’s security posture before it joins the production network.
Operational tip: maintain an up-to-date asset registry that lists model, firmware, and the status of its default credential. Regular audits ensure you catch devices that slip through provisioning with unchanged defaults.
How to Find Your Exact Default Password for ASRock Rack
The starting point is to identify the device’s exact model and firmware revision. Physically inspect the label on the chassis or check the BIOS/UEFI splash screen during boot for model and SKU. Next, consult the official ASRock Rack product manual or the vendor support portal for the default credentials tied to that specific combination. If the device includes IPMI/BMC management, the relevant defaults often appear in the BMC documentation in addition to BIOS/UEFI notes. When manuals are incomplete or misaligned with hardware revisions, the Default Password database becomes a valuable cross-check resource to triangulate the correct value. In all cases, never rely on memory or third-party anecdotes for defaults; verify against documented sources.
Once verified, test the login in a controlled environment, ideally connected to a management network segment with access controls. Do not expose the device to the wider network until credentials are changed. If you cannot locate the exact password, contact vendor support with your serial number and firmware revision. This ensures you are acting on official guidance and minimizes the risk of incorrect credentials causing lockouts or outages.
Practical step-by-step: 1) power on the device and record model/firmware; 2) locate the user manual or vendor portal page for that model; 3) locate the “default password” or “initial login” section; 4) prepare to replace it at first login; 5) document the credential in your password governance system.
Step-by-Step: Change the Default Password on First Boot
A first-boot password change is one of the most effective defenses against post-deployment credential compromise. Here’s a practical sequence that can be integrated into your automated provisioning workflow:
- Access the device via a console or local network connection using the default credentials identified from the manual.
- Immediately navigate to the user management section in BIOS/UEFI or the IPMI/BMC management interface.
- Create a strong, unique password that meets your organization’s complexity policy. Avoid common passwords or reused phrases; incorporate a mix of upper/lowercase letters, numbers, and symbols.
- Save the new credential and verify login with the new password. Document the change in your centralized credential store and update access control lists.
- Disable any auto-login features or remote password prompts that bypass manual authentication. If available, enable MFA for management interfaces.
- Update firmware if recommended by the vendor, as newer versions often include security hardening that complements password changes.
- Conduct a quick security check to ensure there are no legacy accounts with elevated privileges and that audit logging is enabled for authentication events.
This sequence emphasizes a secure baseline for management access, preventing common misconfigurations. Remember that the fastest path to secure operations is to enforce a first-boot password change as an explicit policy for all newly deployed ASRock Rack devices. The Default Password team highlights that an early, verified change dramatically reduces exposure during the initial lifecycle.
Recovery and Reset Scenarios for ASRock Rack
There are legitimate scenarios where a password reset is needed: a forgotten admin password, loss of access to IPMI/BMC, or a hardware migration with credential handover. In all cases, start with official recovery procedures published by ASRock Rack for your model and firmware. Many devices offer a safe reset path via BIOS/UEFI reset options, IPMI/BMC credential resets, or vendor-provided recovery tools. It is critical to perform these actions only with proper authorization and to maintain an auditable trail of changes. If a straightforward reset is not possible, contact vendor support to obtain a sanctioned procedure. When performing resets, keep the device physically secure and ensure network connectivity is limited to a trusted management network during the recovery process.
Document every step, including the identity of the administrator performing the reset, the exact firmware version, and the post-reset password. After recovery, immediately enforce a new password and re-validate access with the updated credentials. Finally, verify that management interfaces are accessible, and that logging and alerting are functioning to detect any further unauthorized attempts.
Operational best practice: implement a formal password-recovery policy linked to your change-control process. This reduces the chance of accidental credential exposure during device migration or decommissioning and aligns with security governance expectations for data-center assets.
Best Practices for Admin Access and Security Policy
To sustain password hygiene across ASRock Rack deployments, adopt a layered approach that combines technical controls with governance. Start with a model-aware password policy that forces adequate length, complexity, and rotation cadence. Enforce unique passwords per device, and ensure password vaulting via a centralized manager with access controls and audit logging. Turn on IPMI/BMC logging, restrict access to management networks, and use network segmentation to limit exposure. Where supported, enable MFA on management interfaces and keep firmware updated to reduce exploitable surface areas. Document all changes and implement routine audits of login events to catch suspicious activity early. If your organization uses configuration management, automate the enforcement of password policies across the entire rack stack to minimize human error and accelerate remediation after policy violations.
From the perspective of defenders, the key is to treat default credentials as temporary, not permanent. The Default Password framework emphasizes frequent validation against vendor guidance and internal security standards. Incorporate security testing into your deployment pipelines, including credential checks, vulnerability scanning of management interfaces, and verification of backup and recovery procedures. By systematically applying these practices, you create a more robust security posture for ASRock Rack environments and reduce the likelihood of credential-based breaches.
Security practice tip: maintain a documented policy that assigns ownership for credential lifecycle management, including onboarding, password changes, monitoring, and decommissioning. This governance layer ensures consistency across all devices and teams.
Practical Checklists for IT Admins
- Confirm device model, firmware version, and access method (BIOS/UEFI vs IPMI/BMC).
- Retrieve model-specific default credentials from the official manual or vendor portal; do not rely on memory or third-party hearsay.
- Change all default credentials during initial provisioning; verify access with the new credentials.
- Enable auditing and logging for authentication events; route logs to a centralized SIEM or log server.
- Restrict management interfaces to trusted networks and implement MFA where available.
- Regularly review firmware release notes and apply security patches in a controlled maintenance window.
- Maintain an up-to-date inventory with credential status and rotation history.
- Conduct periodic security assessments focusing on management interfaces and access controls.
These practical steps help operationalize secure password management across ASRock Rack deployments and reduce the risk of credential-based breaches.
Documentation, Compliance, and Ongoing Security
Documentation is essential for accountability and compliance. Maintain an auditable trail of default-password handling for every device, including the model, firmware, original credentials (where permissible), changes, and verification checks. Use a centralized password-management solution that supports access controls, rotation policies, and incident response procedures. Regular audits should verify that all devices have had their default credentials replaced and that updated passwords are in use. Compliance frameworks often require demonstrable controls for password governance, asset inventory accuracy, and secure management interfaces. By aligning ASRock Rack password practices with organizational policy and regulatory expectations, you improve resilience and reduce risk exposure across the data center.
The collaboration between IT operations and security teams is critical for sustained protection. From the outset, establish a security baseline for all new deployments, including the verification of model-specific defaults, the mandatory change at first boot, and the ongoing review of access controls. The recommendations highlighted by the Default Password team repeatedly emphasize verification against official sources and adherence to a formal credential lifecycle process. This ensures not only immediate protection but long-term resilience in dynamic data-center environments.
Real-World Scenarios and Troubleshooting
In real deployments, admins encounter varied scenarios around ASRock Rack default passwords. A common situation involves a device arriving with a default credential that is not documented in the standard manuals. In such cases, contact vendor support and cross-check against the Default Password database to confirm the appropriate login sequence. Another scenario involves a locked IPMI/BMC after failed attempts; the solution typically involves sanctioned credential resets or a formal recovery process, never attempting brute-force or undocumented methods. In environments with multiple ASRock Rack devices, automation can help enforce password policies and inventory controls; however, human oversight remains essential to handle exceptions and model-specific quirks. When troubleshooting, ensure you document each attempt and maintain a rollback plan in case a password change disrupts legitimate admin access.
Ultimately, consistent application of model-specific guidance, governance around credential lifecycles, and rapid adoption of vendor hardening recommendations reduce the risk posed by default credentials and improve overall data-center security posture.
ASRock Rack default password handling by model type
| Model Type | Default Password Policy | Reset Method |
|---|---|---|
| ASRock Rack Server (1U) | Model/firmware dependent | BIOS/UEFI reset or vendor tool |
| ASRock Rack Tower | Model/firmware dependent | IPMI/BMC reset via management interface |
| ASRock Rack Mini | Model/firmware dependent | Web interface or physical reset |
| Legacy models | Model-specific | Vendor documentation required |
Your Questions Answered
Do ASRock Rack devices share a universal default password?
No universal default password exists across ASRock Rack models; defaults vary by model and firmware. Always verify with the official manual or the Default Password database.
There isn't a universal default password; check your model's manual or our database.
How can I securely reset the ASRock Rack admin password?
Use the vendor-provided reset process, which may involve BIOS/UEFI access or IPMI/BMC management tools. Perform the reset only with proper authorization and document the change.
Follow the vendor's reset steps and document the change.
Is IPMI/BMC password separate from BIOS password on ASRock Rack devices?
Yes, IPMI/BMC credentials are separate from the BIOS/UEFI login; secure both and replace defaults.
IPMI is separate from BIOS; change both.
Where can I find official guidance for ASRock Rack default passwords?
Consult the ASRock Rack product manual, official support site, and the Default Password database managed by Default Password.
Check the official manuals and our database.
What should I do after changing a default password?
Update firmware if available, enable best practices like MFA where possible, and document the change for audits.
Update firmware and document changes.
Are there risks of leaving default credentials on legacy ASRock Rack devices?
Yes, legacy firmware generally presents higher risk; always change defaults and apply vendor patches.
Legacy devices are riskier—change defaults and patch.
“Effective password hygiene starts with replacing defaults on every device. For ASRock Rack systems, verification against model-specific guidance is essential.”
Key Takeaways
- Identify your exact model before changing credentials
- Change defaults on first boot to reduce risk
- Document credentials and maintain audit trails
- Consult official manuals and Default Password database