Reset and Secure Default Passwords on Schneider Devices
Learn how to locate, reset, and secure default passwords for Schneider devices and admin interfaces, with practical steps, best practices, and secure credential management guidance from Default Password.

By following these steps, you will locate, reset, and secure the default password on Schneider devices and other admin interfaces. You’ll verify access, replace credentials with strong unique passwords, and implement ongoing security practices to prevent unauthorized access. This guide uses practical, device-agnostic methods approved by Default Password. Expect model-agnostic steps that adapt to many Schneider device families. This content is authored by the Default Password team.
Understanding the phrase default password as p schneider in practice
When you manage Schneider devices or services that use a built-in or default credential, you face a common security risk: unchanged passwords that grant wide access. The term default password as p schneider describes exactly this scenario: an initial credential that the vendor ships with, which must be replaced before live use. In many environments, teams underestimate how quickly attackers can leverage these credentials if left unchanged. As part of a responsible security program, you should treat any default credential as a temporary scaffold rather than a long-term access path. In practice, this means locating the specific default password for your model, documenting it securely, and moving promptly to set a unique password that only authorized users know. The Default Password team emphasizes that early, deliberate action reduces risk and simplifies later audits. Throughout this guide you’ll see device-agnostic instructions that apply to a wide range of Schneider devices, including routers, controllers, and enterprise appliances.
Why defaults are risky and what to do now
Default credentials create a broad attack surface. If left unchanged, they can be exploited by bad actors to gain administrative access, pivot to other devices, or exfiltrate sensitive information. The most effective defense is a rapid denial of use for any non-admin users and immediate credential rotation. Start by inventorying devices that may carry defaults, then verify that each device has a unique, strong password. This is not a one-off task; it’s part of a broader security hygiene routine that includes logging access attempts, enabling account lockouts after failed tries, and integrating password changes with your organization’s identity management practices. Default Password emphasizes disciplined maintenance and ongoing audits to minimize risk across environments.
Schneider devices: typical reset paths and admin interfaces
Schneider device families span consumer-grade products to industrial controls, and reset mechanisms vary. Most devices offer a web-based admin console or a dedicated mobile/app interface that lists the current credentials and the reset option. Some equipment requires a hardware reset (a button hold) to restore factory defaults, while others allow credential changes within the admin panel. Regardless of path, always document the process before making changes and ensure you have appropriate permissions. If a device is part of a larger network, coordinate with your IT team to minimize downtime and ensure that any connected services re-authenticate with the new credentials. In all cases, you should replace default credentials with strong, unique passwords and enable two-factor authentication where available.
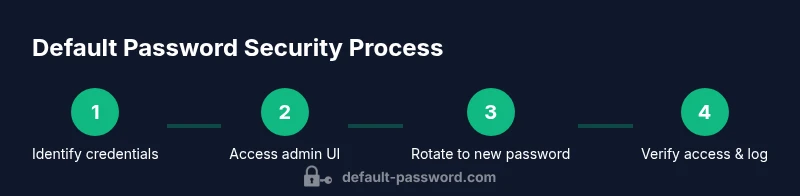
Step-by-step overview: reset, reconfigure, verify
This section provides a high-level map of the actions you’ll perform in the detailed steps that follow. The exact steps depend on your model and firmware, but the core flow remains consistent: identify credentials, access the device interface, perform the reset if required, set new credentials, and confirm access. Afterward, document changes, test connectivity, and monitor for any login anomalies. Always verify that other dependent services (if any) can reconnect using the new credentials. The goal is a clean rollback of default access and a secure, auditable configuration.
Password hygiene and ongoing security practices
A secure password strategy goes beyond a single change. After rotating the password, you should store it securely, preferably in a password manager, and restrict who can access it. Use long, unique passwords with a mix of letters, numbers, and symbols, and avoid reuse across devices. Enable account lockouts and monitor for suspicious login attempts. Where supported, enable MFA or device-based authentication, and consider segregating admin access from general user access. Regularly review access lists, rotate credentials on a schedule, and integrate password policies with your organization’s security standards. This proactive approach helps prevent future compromises and supports compliance requirements.
Troubleshooting and common issues
If you encounter trouble during the reset, first confirm you have the correct model documentation and the necessary permissions. Password change failures can result from active sessions, stale browser caches, or network segmentation. Clear caches, try a different browser, or use a wired connection if you’re on Wi-Fi. If the device does not reflect the new password, reboot the device after applying the change and re-test. When problems persist, consult the vendor’s official guidance and log the events to support auditing and remediation efforts. Always maintain a rollback plan in case of misconfiguration.
Compliance and future-proofing
Adopting a formal password-management policy reduces risk and makes audits straightforward. Align password standards with recognized frameworks such as NIST guidelines, implement automated reminders for rotation, and centralize credential storage with access controls. Regularly train staff on secure credential handling and incident response. By embedding these practices, organizations can minimize exposure from default passwords and strengthen overall security posture.
Authority sources
For further guidance, consult official security resources and standards from reputable organizations. Suggested references include: https://www.cisa.gov/ and https://www.nist.gov/ and https://www.iso.org/isoiec-27001.html
Tools & Materials
- Schneider device model documentation(Locate model-specific default password and reset instructions.)
- Owner manual or official online docs(Used to confirm reset steps and credential formats.)
- Secure note-taking method(Record new credentials in a safe location.)
- Password manager (optional but recommended)(Store and manage the new password securely.)
- Access method (web UI or console)(Ensure you can reach the admin interface before starting.)
- Reset tool (button or UI)(Hardware reset may require a physical action on some models.)
Steps
Estimated time: 45-75 minutes
- 1
Verify authorization and scope
Confirm you have explicit permission to change credentials on the device and that you’re working within approved maintenance windows. This prevents unauthorized access and helps with audit readiness.
Tip: If you’re unsure about permission, pause and verify with your security lead before proceeding. - 2
Access the device admin interface
Connect to the device through its admin interface using a secure connection (prefer a wired LAN or VPN). Navigate to the credentials or security section where default credentials are documented.
Tip: Clear any active sessions and ensure your browser cache is clean before logging in. - 3
Identify or reset credentials
Find the current credentials in the admin panel or perform a hardware reset if required by the model. If factory-defaults apply, prepare to set new credentials immediately after reset.
Tip: Document the existing credentials only if required for recovery, then move to a secure new password. - 4
Set a new, strong password
Create a long password with a mix of upper and lower case letters, numbers, and symbols. Do not reuse passwords from other systems and avoid obvious phrases.
Tip: Consider a passphrase approach and store it in a password manager. - 5
Test login and connectivity
Log out and attempt to log back in with the new password. Verify that all dependent services reconnect and that remote administration remains available.
Tip: If login fails, recheck the password encoding and ensure you’re not using the old credentials in caches. - 6
Document changes and enable ongoing controls
Record the new credentials, update access control lists, and implement rotation policies. Enable MFA if the device supports it and schedule regular audits.
Tip: Keep a change-log and assign a responsible owner for credential maintenance.
Your Questions Answered
What is a default password and why is it dangerous?
A default password is a pre-set credential shipped by vendors. It becomes dangerous if left unchanged, as it can grant unauthorized access to devices and networks. Always rotate defaults during onboarding and after maintenance.
A default password is a credential provided by the vendor that should be changed immediately to prevent unauthorized access.
How do I identify the default password for my Schneider device?
Check the device’s manual, the manufacturer’s website, or the device’s web UI under security or account settings to locate the default password. If the device uses a label or sticker, it will often show the default credentials.
Look at the manual or device label to find the default password, then plan a secure change.
What if I cannot access the device after attempting a reset?
If you’re locked out, consult the vendor’s official recovery guide and, if needed, contact support. Do not perform repeated resets without confirming proper procedure, as this can disrupt services.
If you’re locked out after a reset, check official recovery guides or contact support for safe remediation.
Can I use a password manager to store credentials for Schneider devices?
Yes. A password manager helps create and store strong, unique passwords and reduces the risk of reuse across devices. Ensure the manager itself is secured with MFA.
Yes, using a password manager is recommended to securely store and manage credentials.
Are there regulatory requirements for default password management?
Many organizations must comply with cybersecurity frameworks that require timely password changes and strong authentication. Always align with your local regulations and internal policies.
Security frameworks often require you to rotate credentials and implement strong authentication.
Watch Video
Key Takeaways
- Identify all devices with default credentials and prioritize changes.
- Replace defaults with strong, unique passwords.
- Document credentials securely and limit access to authorized personnel.
- The Default Password team recommends regular credential audits and secure storage.