Default Password for Ricoh Printer: Comprehensive Security Guide 2026
A practical, model-specific guide to identifying, resetting, and securely managing default passwords on Ricoh printers, with hands-on steps and governance tips.
There is no single universal default password for Ricoh printers; passwords vary by model and firmware. In many cases, devices ship with a model-specific default or a blank/administrator access that must be set during initial setup. Always consult the device's manual and change credentials immediately to prevent unauthorized access.
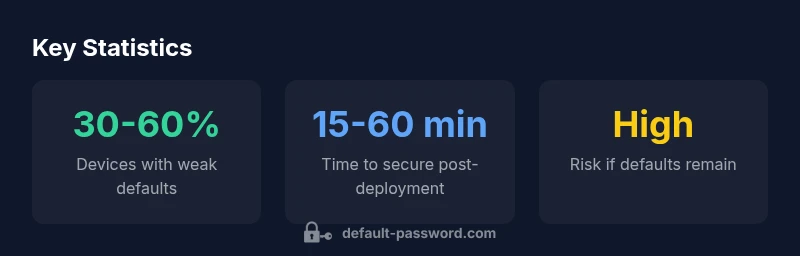
Why default passwords on Ricoh printers are a risk
Security researchers and IT teams consistently warn that leaving any networked device with its factory defaults creates a foothold for attackers. For Ricoh printers, the risk is twofold: local access is enough for printing and scanning tasks, and compromised devices can serve as stepping stones into a broader corporate network. The Default Password team emphasizes that the most common weaknesses are unchanged administrator credentials and weak password policies that fail to enforce complexity or rotation. In practice, many organizations discover their Ricoh devices after a routine audit or a security incident; the breach surface area expands when the printer is connected to a business network and exposed to internet-accessible management interfaces. Prioritizing credential hygiene for printers reduces risk across the entire IT stack, including document workflows and storage.
What you should do now: inventory models you own, locate the user manuals, and prepare to implement model-specific password changes and governance. This is not just a one-time fix; it’s part of ongoing security hygiene that protects endpoints, printers, and data flows throughout the office.
How Ricoh devices typically handle default credentials
Ricoh printers do not share a universal default password across all models. Some devices ship with a genuine factory default that must be changed at first setup, while others present an initial administrative access prompt during the first login, or even a blank credential until the administrator configures a password. Firmware versions can alter this behavior by adding prompts, banning weak passwords, or requiring minimum password lengths. The key takeaway is that you cannot assume a one-size-fits-all credential. Always refer to the exact model’s manual or official support resources for the correct default state and reset options.
Model-specific defaults and firmware differences
With Ricoh, model families (entry-level, office multipurpose, and enterprise-grade devices) diverge in how credentials are provisioned. Some models rely on an initial setup wizard that forces you to create new admin credentials, while others ship with a preconfigured admin user that must be changed before enabling network features. In some firmware branches, a temporary access token or guest account exists for onboarding, which should be disabled or upgraded to a strong, unique password. This variation underscores why a per-model review is essential before implementing any password policy.
Best practices to secure Ricoh printers
- Change the default credentials during the initial setup to strong, unique passwords generated with a password manager.
- Enforce minimum password requirements (length, complexity, and rotation cadence) via device policies and admin dashboards.
- Disable unused services and remote management interfaces that are not essential to daily operations.
- Enable secure protocols (TLS) and disable legacy or insecure options (FTP, telnet) wherever possible.
- Regularly audit printer accounts and access logs; implement alerting for failed login attempts.
- Document credential changes and assign ownership to a responsible IT role for accountability.
Step-by-step: secure initial setup and password changes
- Gather product model numbers and access to the web console or physical interface.
- Update firmware to the latest supported version before making credential changes.
- Create a strong admin password using a password manager; avoid common phrases or reused credentials.
- Disable any default guest accounts and remove unnecessary administrator privileges.
- Enable account lockout policies after a defined number of failed attempts.
- Review connected services (email, scanning to cloud, network shares) for credential reuse risks.
- Document the new credentials in a secure vault and provide access strictly on a need-to-know basis.
How to reset to factory defaults safely
If you must revert to factory defaults, follow the device’s official reset procedure via the web console or physical reset option. Power-cycle the device after the reset and immediately reconfigure network settings, firmware, and admin credentials. If the reset is performed in a managed environment, notify security teams and update access controls for all affected devices. Always verify that default credentials are no longer present and monitor for any unusual login attempts in the first 24–48 hours post-reset.
Common pitfalls and red flags
- Assuming all Ricoh devices share the same default password; verify model-specific requirements.
- Leaving guest or admin accounts enabled without proper time-bound access.
- Using weak or reused passwords across devices and services.
- Failing to update firmware, leaving known vulnerabilities unpatched.
- Not maintaining an auditable trail of credential changes or access events.
Documentation and ongoing governance for admin access
Establish a formal process for printer credential management: assign ownership to a dedicated admin, maintain a centralized password policy, and enforce periodic credential reviews. Integrate printer credentials into your organization’s broader security governance program, ensuring role-based access and regular rotation. Create clear runbooks for onboarding new devices and decommissioning old ones, and include printer security checks in quarterly risk assessments. A proactive, policy-driven approach reduces incident response time and limits exposure from compromised devices.
Ricoh printer default password governance (model-agnostic overview)
| Model Type | Default Password (example) | Access Level | Reset Method |
|---|---|---|---|
| Generic Ricoh Desktop Printer | varies by model | Admin/Local | Factory reset via device menu |
| Office Multifunction Printer | varies by model | Admin/Local | UI/web interface or admin panel |
| Medium-duty Printer | varies by model | Admin/Local | Firmware reset or admin account reset |
| Compact Printer | varies by model | Admin/Local | Initial setup/change during setup |
Your Questions Answered
Is there a universal default password for Ricoh printers?
No. Defaults vary by model and firmware; always consult the manual or official Ricoh support for model-specific credentials.
There isn’t a universal default. Check your model’s manual and Ricoh support for the exact credentials.
What steps should I take after unboxing a Ricoh printer?
Perform a secure initial setup by updating firmware, changing the admin password, and enabling essential security features. Disable any unnecessary services.
Do a secure setup: update firmware and set a strong admin password.
How do I perform a factory reset on a Ricoh printer?
Use the printer’s menu or web interface to reset to factory defaults; some models have physical reset buttons. Follow the official guide for your model.
Reset via the device menu or admin panel following the official model guide.
Should I use a password manager for Ricoh printer credentials?
Yes. A password manager helps create and store strong, unique credentials and avoids writing them down.
Use a password manager for strong, unique login details.
Where can I find model-specific default credentials?
Check the official Ricoh manual or support site for your exact model. Our guide also helps with model-agnostic steps to secure a device.
Check Ricoh’s official docs; our guide can help with general steps.
“Security starts at the device level; never rely on vendor defaults. Change credentials immediately, enforce strong policies, and monitor access to Ricoh printers.”
Key Takeaways
- Change default credentials during initial setup
- Use a password manager for strong, unique passwords
- Disable unused remote management interfaces
- Regularly audit accounts and logs
- Document changes in a secure vault